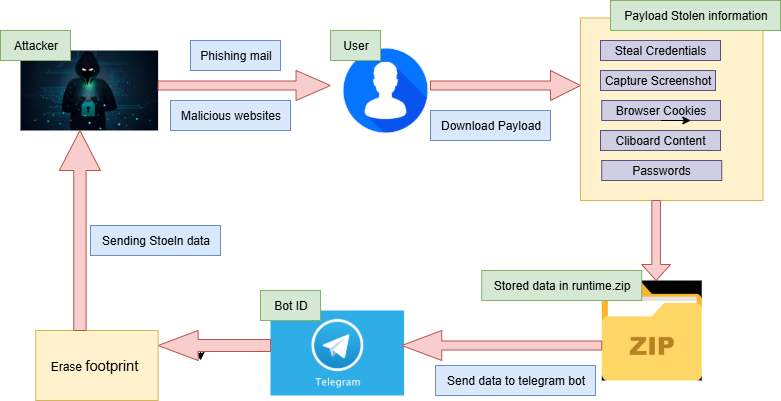
Shuyal Stealer is an infostealer that targets 19 different browsers to harvest browser-stored credentials, Discord tokens, clipboard contents, screenshots, and extensive system hardware/configuration details before exfiltrating data via a hardcoded Telegram bot. It uses WMI for system profiling, disables Task Manager and adds persistence through the Startup folder, then compresses stolen data to runtime.zip, sends it to a Telegram chat, and attempts self-deletion. #Shuyal #TelegramBot
Keypoints
- Shuyal Stealer targets an unusually large set of 19 browsers (including Chrome, Edge, Tor, Brave, Opera, Vivaldi, Yandex, Waterfox, and others) to extract saved credentials via the browser “Login Data” SQLite database.
- The malware performs deep system reconnaissance using WMI commands to collect disk drive models/serials, keyboard and display information, and other hardware identifiers for precise fingerprinting.
- Shuyal captures clipboard contents and screenshots (saved as clipboard.txt and ss.png) and extracts Discord tokens from Discord, Discord Canary, and Discord PTB installations.
- For evasion, it locates and terminates taskmgr.exe using TerminateProcess and sets the DisableTaskMgr registry value to 1 to prevent Task Manager use after reboot.
- Persistence is achieved by copying the executable into the Windows Startup folder via CopyFileA to ensure execution on reboot.
- Collected artifacts are placed in a runtime directory, compressed with PowerShell into runtime.zip, and exfiltrated using a hardcoded Telegram bot token and chat ID to the Telegram Bot API.
- After exfiltration Shuyal runs a batch self-deletion script (util.bat) to remove the archive and residual files, reducing forensic traces.
MITRE Techniques
- [T1033 ] System Owner/User Discovery – Uses WMI queries (e.g., “wmic diskdrive get model, serial number” and “wmic path Win32_Keyboard get Description, DeviceID”) to enumerate hardware and input device identifiers and build a detailed fingerprint.
- [T1055 ] Process Injection / Manipulation – Scans for taskmgr.exe and forcefully terminates Task Manager using the TerminateProcess method to disrupt user and investigator mitigation efforts (“stopping Task Manager”).
- [T1112 ] Modify Registry – Sets the registry value DisableTaskMgr to 1 to permanently disable Task Manager and maintain concealment across reboots (“Task Manager disabled by Registry value”).
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Copies itself into the Windows Startup folder using CopyFileA to achieve persistence and automatic execution on reboot (“replicate itself into the Windows Startup folder”).
- [T1005 ] Data from Local System – Reads browser SQLite “Login Data” and executes SQL query “SELECT origin_url, username_value, password_value FROM logins” to harvest stored credentials from a wide range of browsers.
- [T1113 ] Screen Capture – Captures screenshots using GdiplusStartup, BitBlt, and GdipSaveImageToFile APIs and saves images as ‘ss.png’.
- [T1115 ] Clipboard Data – Retrieves clipboard content using OpenClipboard and GetClipboardData APIs and stores it in clipboard.txt.
- [T1074.001 ] Data Staged – Aggregates stolen files into a runtime directory and compresses them into runtime.zip using PowerShell before exfiltration (“PowerShell to compress the ‘runtime’ directory into runtime.zip”).
- [T1041 ] Exfiltration Over C2 Channel – Exfiltrates compressed data via a hardcoded Telegram Bot API endpoint to send the archive to an attacker-controlled chat (“api.telegram[.]org/[bot]…/sendDocument?chat_id=-1002503889864”).
- [T1070.004 ] File Deletion – Executes a batch script util.bat to remove runtime files and erase forensic traces after data exfiltration (“generating and executing a batch file designed to remove the malware and its related components”).
Indicators of Compromise
- [File Hash ] Sample hashes for the analyzed sample – MD5: 9523086ab1c3ab505f3dfd170672af1e, SHA-256: 8bbeafcc91a43936ae8a91de31795842cd93d2d8be3f72ce5c6ed27a08cdc092
- [File Paths ] Artifacts and staged data locations – C:UsersAppDataLocalTempruntimebrowsertokens.txt; C:UsersAppDataLocalTempruntimeclipboardclipboard.txt
- [Files ] Exfiltration and staging filenames – runtime.zip (compressed archive), util.bat (self-deletion batch script), ss.png (screenshot), saved_passwords.txt (decrypted credentials)
- [Network / URL ] Exfiltration endpoint – Telegram Bot API URL: hxxps[:]//api.telegram[.]org/[bot]7522684505:AAEODeii83B_nlpLi0bUQTnOtVdjc8yHfjQ/sendDocument?chat_id=-1002503889864
- [Detection Name ] AV detection label used in remediation guidance – UltraAV detection: Trojan.W64.100925.Shuyal.YR