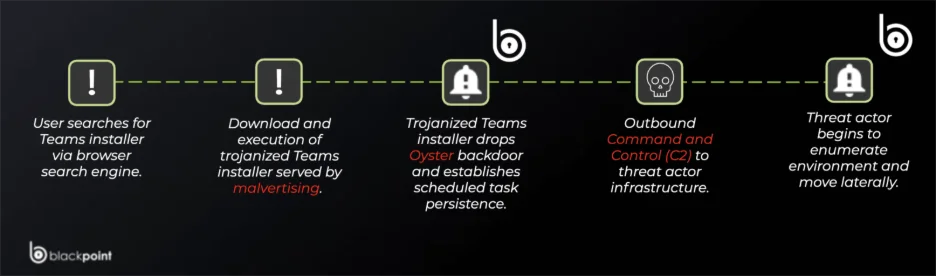
Attackers used SEO poisoning and malicious ads to distribute fake Microsoft Teams installers that drop the Oyster (Broomstick) backdoor, providing persistent C2 access via a malicious DLL, scheduled task CaptureService, and rundll32.exe execution. Key IOCs include domains like teams-install.icu and nickbush24.com, IPs such as 185.28.119.228, and multiple malicious file hashes. #Oyster #nickbush24.com
Keypoints
- Attackers manipulated search engine results and used poisoned ads to promote fake “Microsoft Teams” download links that hosted malicious installers.
- Downloaded installers placed a malicious DLL in AppData, created a scheduled task named CaptureService, and used rundll32.exe to execute the backdoor.
- The malware family is identified as Oyster (aka Broomstick), a persistent backdoor/loader capable of fetching additional payloads and enabling long-term access.
- C2 infrastructure includes domains such as nickbush24.com and teams-install.icu and IPs like 185.28.119.228, indicating a global SEO poisoning campaign.
- Detection and mitigation recommendations include monitoring for rundll32 executions, new scheduled tasks (Event ID 4698), blocking known IOCs, and enforcing installer download restrictions.
- Industries at elevated risk include healthcare, finance, and professional services, but any Teams user can be targeted via poisoned search results.
- SOCRadar modules suggested: IOC enrichment, DNS filtering, web proxy filtering, scheduled task monitoring, and brand protection/takedowns to reduce exposure.
MITRE Techniques
- [T1053.005] Scheduled Task – Malware creates a scheduled task named CaptureService to maintain persistence and run regularly. Quote: ‘it created a scheduled task called CaptureService.’
- [T1218.011] Rundll32 – Attackers used rundll32.exe to load and execute the malicious DLL from non-standard locations. Quote: ‘used rundll32.exe to stay on the computer.’
- [T1204.002] Malicious Installer – Fake Microsoft Teams installers were distributed via poisoned search results and ads to execute the backdoor. Quote: ‘people…downloaded installer files’ (fake Microsoft Teams installers).
- [T1606] Archive Collected Data / Exfiltration (implied) – Oyster backdoor links to attacker-controlled domains for C2 and potential data exfiltration. Quote: ‘The malware then linked up with domains that the attacker controlled, such as nickbush24.com and teams-install.icu.’
- [T1583] Acquire Infrastructure – Use of attacker-controlled domains and IPs (nickbush24.com, teams-install.icu, 185.28.119.228) to host C2 and malicious downloads. Quote: ‘linked up with domains that the attacker controlled, such as nickbush24.com and teams-install.icu.’
Indicators of Compromise
- [Domain] Malicious download/C2 domains – teams-install[.]icu, nickbush24[.]com
- [IP Address] C2 / hosting – 185.28.119.228, 45.66.248.112
- [File Hash – SHA256] Malicious installer/backdoor samples – 90b633cacfa185dd912a945f370e14191644ecff1300dbce72e2477171753396, 9dc86863e3188912c3816e8ba21eda939107b8823f1afc190c466a7d5ca708d1 (and other hashes)
- [File Hash – MD5/SHA1] Additional sample identifiers – MD5: d28b4136a7e6148de5c26a055c711f4f, SHA1: 8d8ceba1b31f4ace5a9c44225014d3947fbf205a
- [Hostname] Related hostnames observed – server-na-qc2.farsafe.net, team.frywow.com
Read more: https://socradar.io/fake-microsoft-teams-installers-oyster-backdoor/