Kaiji is a Linux/IoT-focused Go-based botnet payload that gains access via exposed services (e.g., weak SSH, malicious PoC) and provides multi-protocol DDoS and proxying with rootkit-class stealth. The campaign uses distributed storage and HTTP file servers to host many architecture-specific binaries (e.g., amd64 MD5 fd05b94c016fd2eb7e26c406fa2266d0) and C2 domains such as else.su6s.su/#fd05b94c016fd2eb7e26c406fa2266d0 #su6s.su
Keypoints
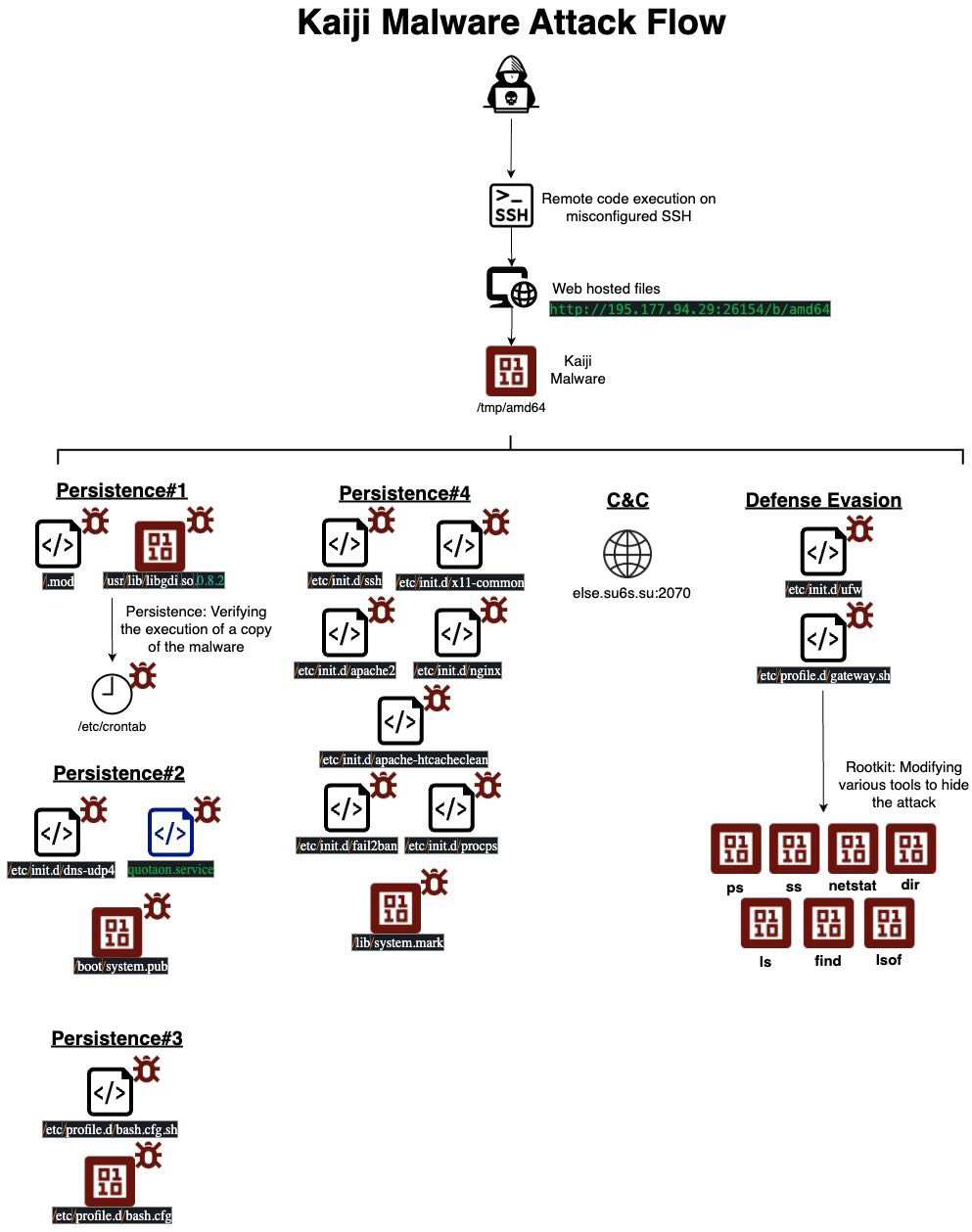
- Initial access observed via misconfigured SSH with weak credentials from IP 45.12.1.19 and via malicious CVE-2024-6387 PoC targeting researchers.
- Main payload is a large Go (1.21.0) ELF amd64 binary (MD5: fd05b94c016fd2eb7e26c406fa2266d0) implementing 24+ attack vectors, SOCKS5/HTTP proxies, and C2 over HTTP/HTTPS/WebSocket.
- Kaiji establishes persistence by copying binaries to multiple locations (/boot/system.pub, /usr/lib/libgdi.so.0.8.2, /etc/profile.d/bash.cfg, /lib/system.mark) and creating systemd/SysV services and cronjobs.
- Defense evasion includes SELinux policy modification via audit2allow/semodule, bind-mounting over /proc/[pid] to hide process info, and overriding common userland commands via /etc/profile.d/gateway.sh to filter outputs.
- Infrastructure: download server at 195.177.94.29:26154 hosting many architecture-specific binaries with tens of thousands of downloads; C2 domain su6s.su (else.su6s.su → 198.251.81.61).
- Observed behaviors focus on long-term relay/proxy abuse and volumetric/protocol-specific DDoS rather than one-off compromise, with features for respawn, watchdogs, and process-name spoofing.
- Detection and mitigation recommendations include runtime protection and policy enforcement to detect unusual network bindings, proxy activity, and fileless/container drift behavior.
MITRE Techniques
- [T1110] Brute Force – Initial access from misconfigured SSH with weak password exploited on the honeypot: “Our honeypot has an exposed misconfigured SSH access, with weak password. The threat actors exploited our honeypot and infected it with Kaiji malware.”
- [T1204] User Execution – Malicious PoC exploitation: “this threat actor is targeting security researchers by hiding a malicious backdoor in CVE-2024-6387 proof of concept code, and when running the PoC it will lead to infection of the server with Kaiji malware.”
- [T1569] System Services – Service creation for persistence: “creates a system service … ExecStart=/boot/system.pub” and SysV init scripts (/etc/init.d/dns-udp4) to execute malware at startup.
- [T1053] Scheduled Task/Job – Cron-based persistence: “*/1 * * * * root /.mod >> /etc/crontab” which runs /.mod that calls /usr/lib/libgdi.so.0.8.2.
- [T1543] Create or Modify System Process – Installing init scripts and services across system locations: copies to /lib/system.mark and creates /etc/init.d/x11-common and other init scripts to ensure execution.
- [T1497] Virtualization/Sandbox Evasion (Environment Fingerprinting) – Runtime CPU/environment fingerprinting to adapt behavior: “At runtime it performs CPU/environment fingerprinting.”
- [T1105] Ingress Tool Transfer – Downloading payloads from HTTP file server: “The main payload was downloaded from an Http File Server at 195.177.94.29:26154.”
- [T1071] Application Layer Protocol – C2 over HTTP/HTTPS and WebSocket: “C2 channels over HTTP/HTTPS and WebSocket (TLS-capable).”
- [T1620] Reflective Code Loading / Fileless Techniques – Fileless/stealthy execution patterns and respawn helpers: includes “respawn logic, and dropper helpers such as gateway.sh/system.pub” and techniques to hide artifacts.
- [T1562] Impair Defenses – Modifying SELinux policies to allow malware actions: “ausearch -c ‘system.pub’ –raw | audit2allow -M my-Systemmod; semodule -X 300 -i my-Systemmod.pp” to weaken SELinux.
- [T1036] Masquerading – Use of innocuous-looking filenames for persistence: copies to names like /usr/lib/libgdi.so.0.8.2 and /boot/system.pub to blend in with benign files.
- [T1201] Traffic Signaling – Use of embedded proxies and relays (SOCKS5/HTTP) to proxy malicious traffic: “embedded SOCKS5 and HTTP proxy” used to relay traffic.
- [T1499] Endpoint Denial of Service – DDoS capabilities: “implements a multi-protocol network-attack platform” and “volumetric and protocol-specific DDoS.”
- [T1564] Hide Artifacts – Bind-mounting /tmp over /proc/[pid] to hide process metadata: “mount -o bind /tmp/ /proc/55” to obfuscate process details.
- [T1222] File and Directory Permissions Modification – Dropping executable files into profile.d and altering login scripts to execute malware at login: “/etc/profile.d/bash.cfg … will run at login and execute /etc/profile.d/bash.cfg.”
- [T1592] Gather Victim Network Information – Use of network modules and custom networking for high-throughput traffic and fingerprinting: “custom http/websocket/TLS networking modules” and traffic encoding/buffering.
Indicators of Compromise
- [IP Address] initial access & infrastructure – 45.12.1.19 (attacker IP observed), 195.177.94.29:26154 (payload download server), 198.251.81.61 (else.su6s.su)
- [Domains] C2 and infrastructure – su6s.su (C2 registration), else.su6s.su → 198.251.81.61
- [File Hashes] main and architecture binaries – fd05b94c016fd2eb7e26c406fa2266d0 (amd64), 2964bf18cd6050068e73ccff0c848e48 (386), and other hashes such as 3a7ae1ecb3df725b8e5adfef4a2216ba (aarch64) and 10+ more
- [File Paths / Filenames] persistence & scripts – /boot/system.pub, /usr/lib/libgdi.so.0.8.2, /etc/profile.d/bash.cfg, /.mod, /etc/profile.d/gateway.sh
- [Files on Download Server] additional payloads and tools – linux (SSHscan worm) MD5 138ba58259d3c64b34a2b9c5d0b8b178, systeme (Mayday/elknot) MD5 b93915ef006606b4720dc566845575a2
Read more: https://www.aquasec.com/blog/kaiji-malware-anatomy-persistence-detection/