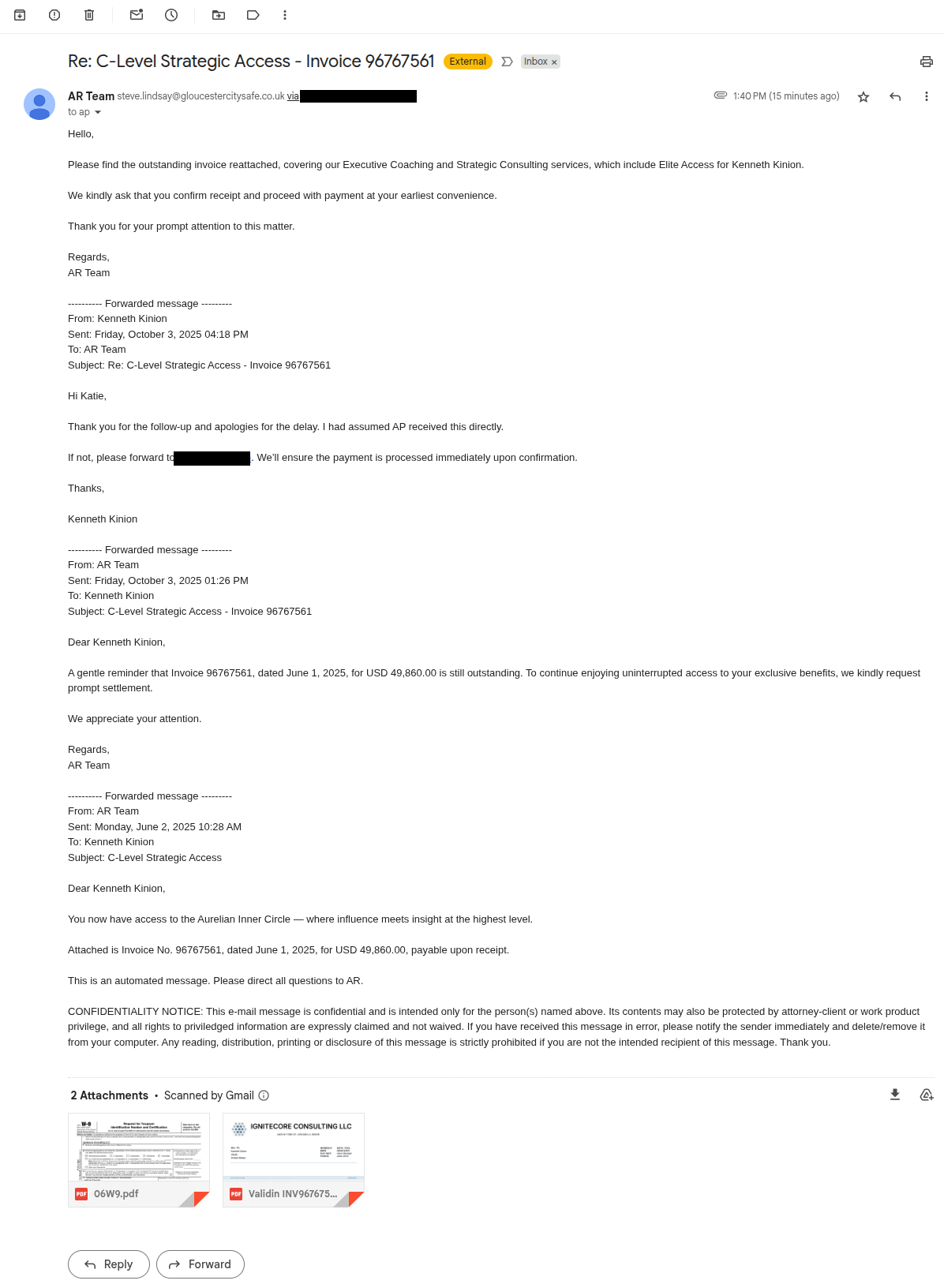
A highly convincing invoice-and-W9 phishing email targeted a Validin employee and used a realistic company identity (Ignitecore Consulting LLC) and reply-to domain to try to collect payments. Investigators pivoted on HTML/CSS template hashes, registration and hosting patterns, self-signed certificates, and Cloudflare origin IPs to identify ~40 related domains and multiple origin IP addresses to block. #ignitecoreconsulting #Cloudflare
Category: Threat Research

Nearly 70% of CVEs added to NVD between February and September 2024 were listed as “awaiting analysis,” leaving out crucial context like affected products and CVSS scores and creating widespread delays and inaccuracies that hinder patching decisions. This backlog and persistent data quality issues have real-world impacts on vendors, security tools, and administrators, prompting organizations to use alternative sources such as OSV.dev, VulnCheck, vendor advisories, and Kandji Vulnerability Management to obtain timely, accurate vulnerability intelligence. #CVE-2024-6604 #CVE-2025-6554
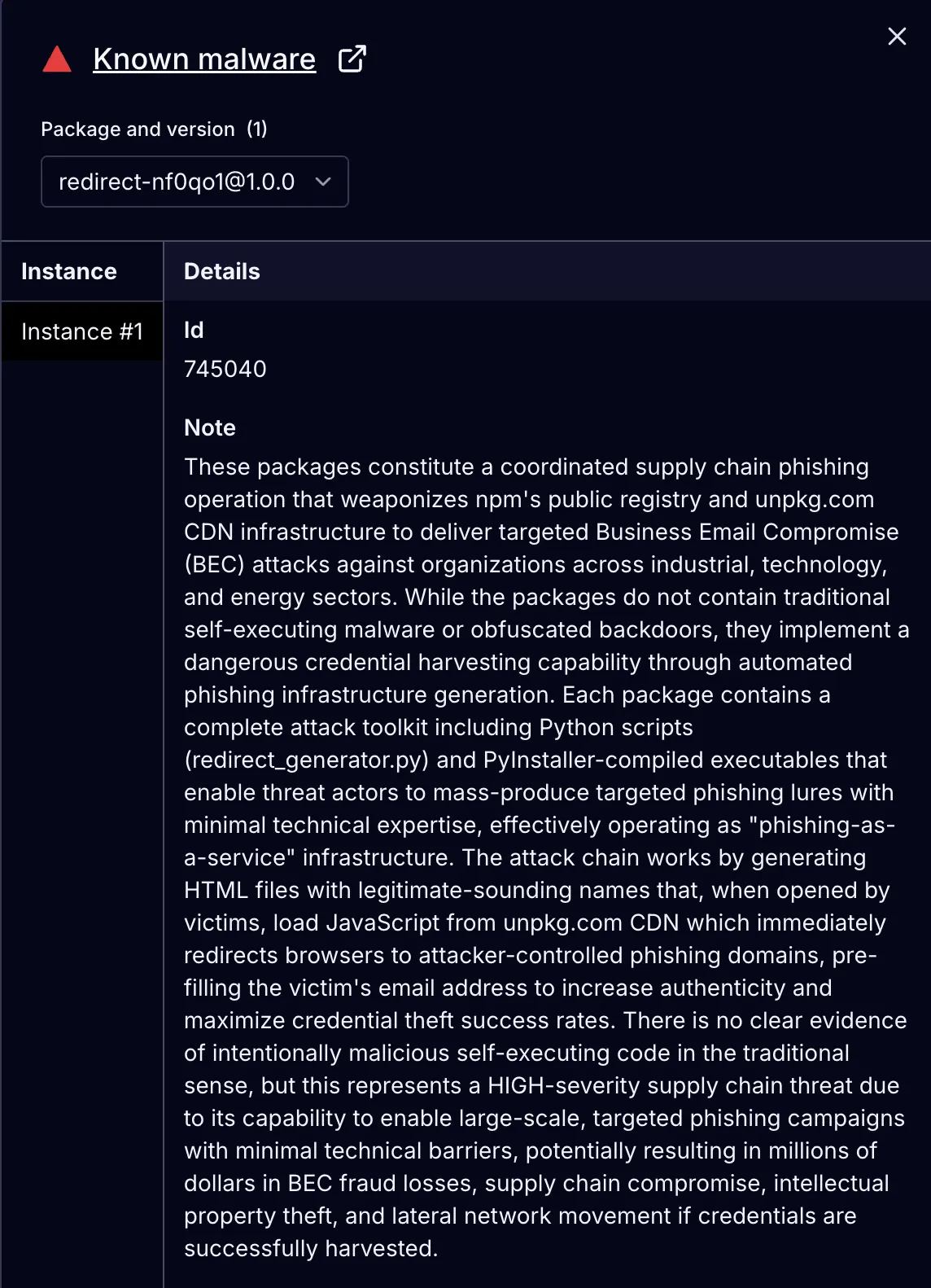
Socket Threat Research Team discovered 175 malicious npm packages used as hosting infrastructure for a coordinated phishing campaign that targeted 135+ industrial, technology, and energy organizations and delivered credential-harvesting redirects via unpkg.com CDN. The campaign identifier nb830r6x and the beamglea artifacts (beamglea.js, beamglea_template.js) link the infrastructure and automation to a single operation. #beamglea #nb830r6x
ClayRat is an evolving Android spyware campaign distributed via Telegram channels and phishing sites that impersonate popular apps to trick Russian users into sideloading malicious APKs. Once installed and granted default SMS handler privileges, it exfiltrates SMS, call logs, notifications, device info, takes front-camera photos, sends SMS/calls, and self-propagates by messaging all contacts. #ClayRat #GdeDPS
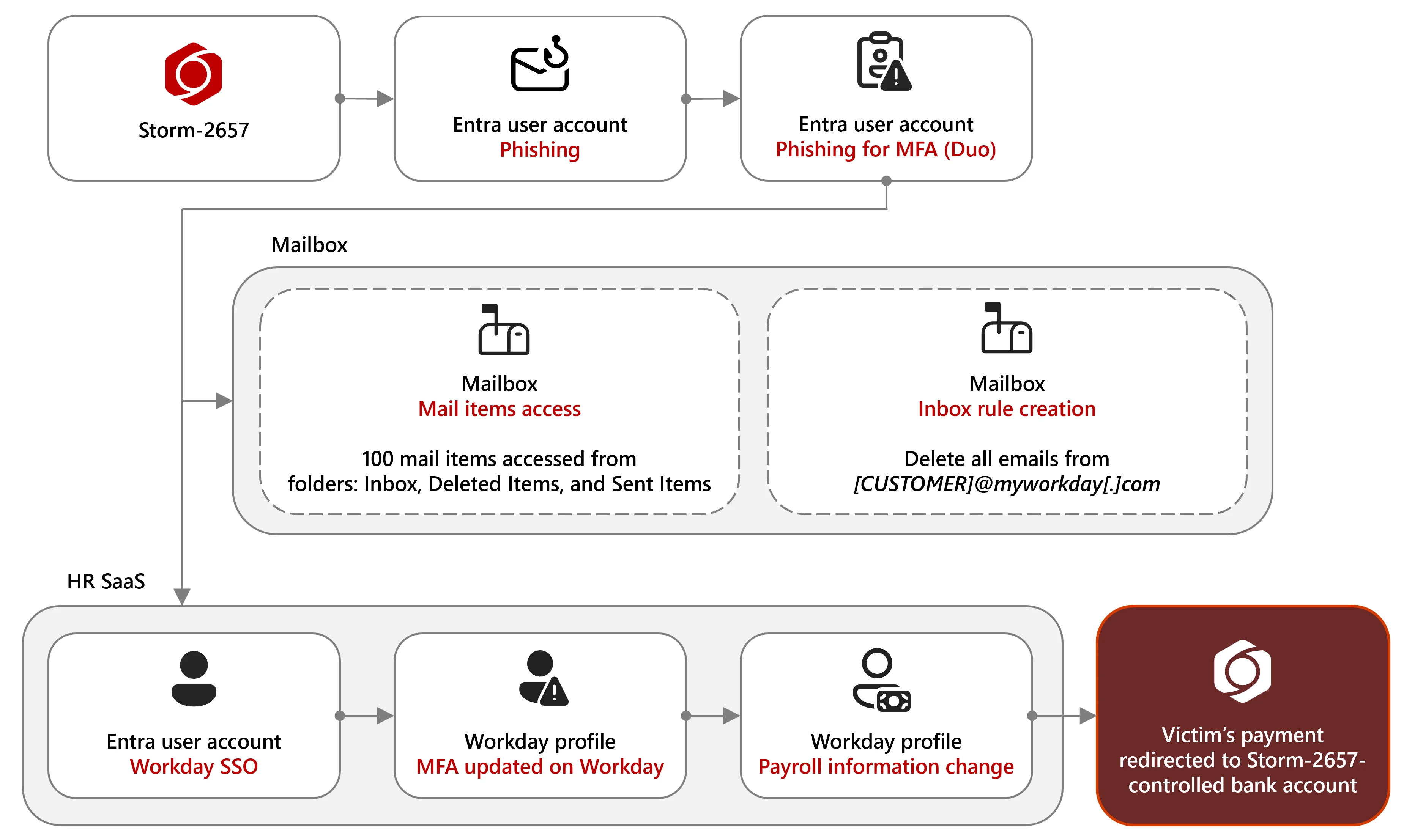
Microsoft observed a financially motivated group tracked as Storm-2657 using AITM phishing to steal MFA codes, compromise employee Exchange Online accounts, create inbox rules to hide Workday notifications, and redirect payroll to attacker-controlled bank accounts. The campaign targeted US universities and higher-education staff via tailored phishing themes and succeeded where phishing-resistant MFA was not enforced. #Storm-2657 #Workday

A surge in Akira ransomware campaigns since July 2025 leverages CVE-2024-40766 in SonicWall SSL VPNs to harvest credentials and achieve rapid intrusions, sometimes completing post-compromise actions in under 55 minutes. Attacks use tools like Impacket, WinRAR, AnyDesk/RustDesk, and DPAPI-decrypting PowerShell scripts to perform discovery, lateral movement, data staging/exfiltration, and double-extortion. #Akira #CVE-2024-40766

eSentire’s TRU discovered a novel Rust-based backdoor named ChaosBot that uses Discord for command-and-control, leverages compromised VPN and over-privileged Active Directory credentials, and can side-load via msedge_elf.dll. Observed capabilities include remote command execution via PowerShell, file transfer, screenshots, FRP-based reverse proxying, VM/ETW evasion, and attempted VS Code Tunnel deployment. #ChaosBot #frp
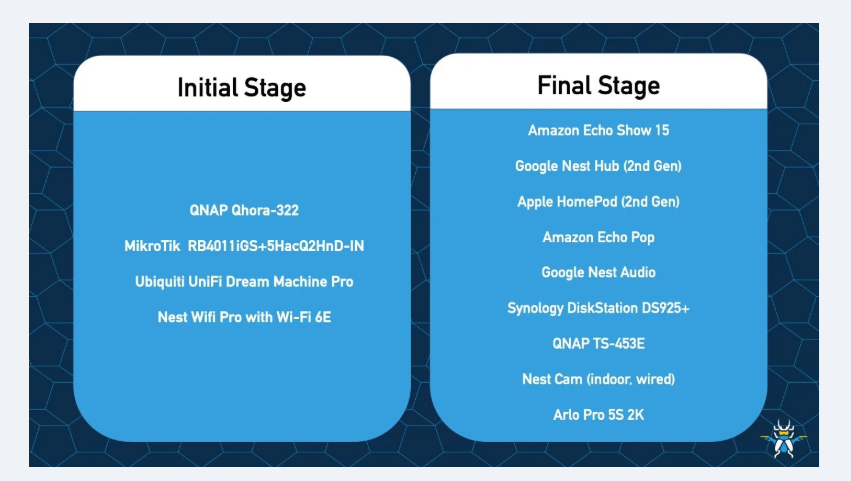
Trend Research and ZDI Threat Hunters have identified a large-scale RondoDox botnet campaign using an “exploit shotgun” that targets over 50 vulnerabilities across more than 30 vendors to compromise internet-exposed routers, DVRs, NVRs, CCTV systems, and web servers. Active exploitation has been observed globally since mid-2025, leveraging vulnerabilities including CVE-2023-1389, CVE-2024-3721,…
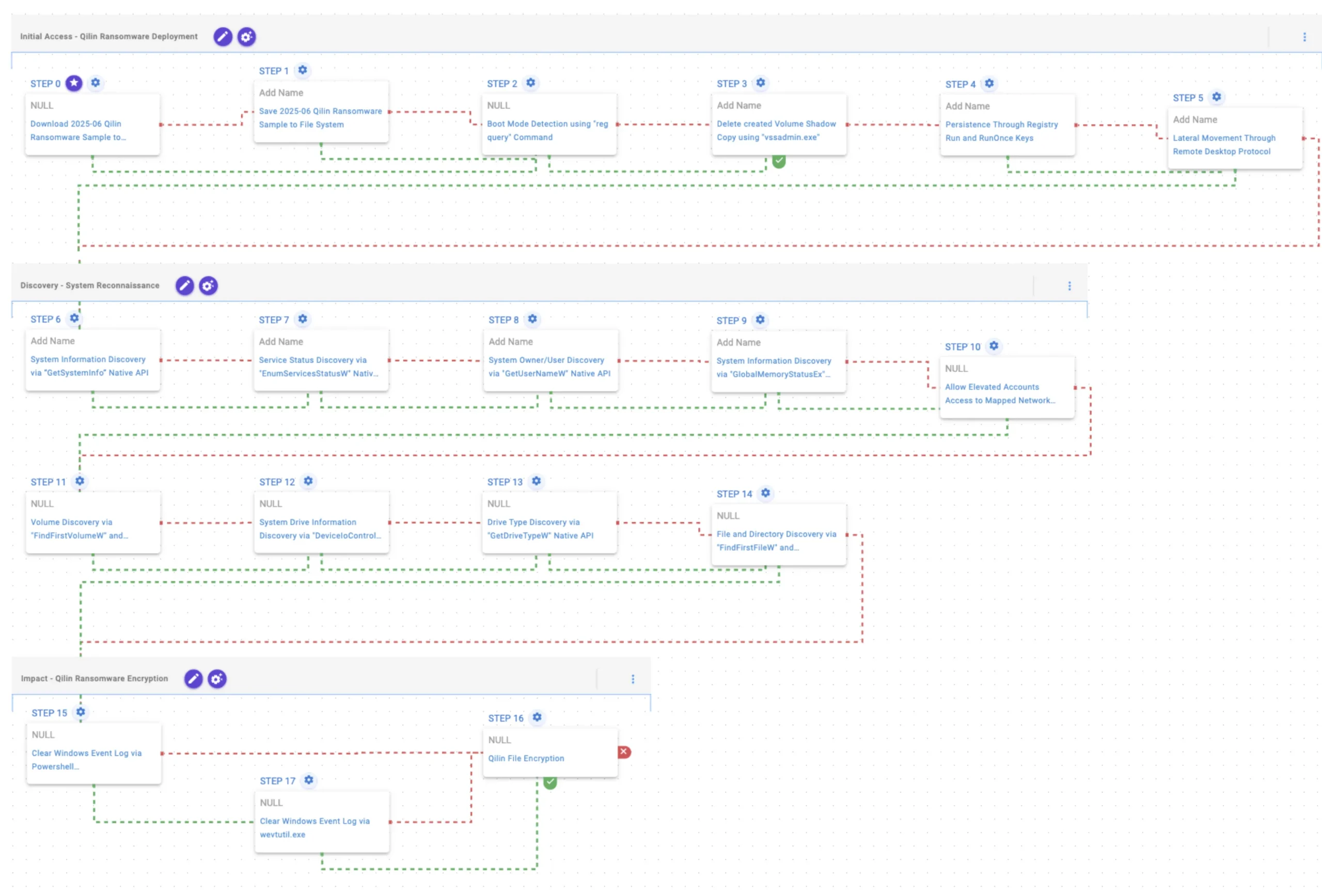
Qilin is a RaaS strain that evolved from Agenda (Go) into a Rust-based, cross-platform ransomware family targeting Windows, Linux, and ESXi with advanced evasion including BYOVD, Safe Mode detection, and shadow copy deletion, using AES-256 and RSA-2048 for encryption. AttackIQ published an emulation/attack graph to validate defenses against Qilin TTPs and…

Researchers warn that widespread use of AI agents in Cyber Threat Intelligence (CTI) boosts productivity but raises concerns about reliability, transparency, and the ability to trust another analyst’s prompts or workflows. A case study using an LLM-driven agentic system to analyze Russian internet leaks demonstrates both practical benefits and the need for adapted research methodology and clear communication of AI-assisted judgments. #Dreadnode #LABScon25

Cybercriminals operated a coordinated scam infrastructure hosting fake cryptocurrency sites, a malicious browser-extension-based wallet-connect phishing flow, and an iPhone configuration-profile phishing “app” that together enabled wallet drains and credential theft. Key infrastructure included domains medaigenesis[.]cc, novacrypt[.]net, and zzztd[.]com all hosted on 8.221.100[.]222, with related artifacts like Novacrypt.mobileconfig and Android APKs linking to C2 domains such as anedhaude[.]xyz. #medaigenesis[.]cc #novacrypt[.]net

Attackers created multiple spoofed Homebrew installer sites that copied brew.sh but forced users to use a page Copy button which injects a hidden malicious shell command into the clipboard, leading to parallel download and execution of payloads like Odyssey Stealer. Kandji observed the infrastructure, Russian-language code comments suggesting payload-as-a-service and exfiltration to Telegram, and listed domains and a malicious curl command used in the campaign. #OdysseyStealer #HomebrewOnline

GhostSocks is a Malware-as-a-Service that converts compromised devices into residential SOCKS5 proxies, leveraging partnerships (notably with LummaStealer) to monetize infected hosts and bypass anti-fraud measures. The service provides obfuscated Golang binaries, uses a pool of relay servers for back-connect, and continues active development despite forum disruptions and law enforcement actions. #GhostSocks #LummaStealer

A user executed a malicious JavaScript disguised as a browser update that led to a multi-stage intrusion tied to RansomHub affiliates using SocGhoulish, resulting in rapid credential theft, privilege escalation to Domain Admin, and mass data exfiltration via AzCopy. Varonis intervened within 48 hours, contained and remediated the threat with zero…

Elastic Security Labs’ 2025 Global Threat Report highlights AI-driven shifts in adversary behavior, including increased execution techniques on Windows, widespread use of infostealers targeting browser credentials, and concentrated cloud attacks focused on Initial Access, Persistence, and Credential Access. The report names specific threats and campaigns such as BANSHEE, EDDIESTEALER, ARECHCLIENT2, REF7707 (FINALDRAFT, PATHLOADER, GUIDLOADER) and calls out delivery methods like ClickFix and abuse of Microsoft GraphAPI. #BANSHEE #EDDIESTEALER #ARECHCLIENT2 #REF7707 #FINALDRAFT #PATHLOADER #GUIDLOADER