Trend Research and ZDI Threat Hunters have identified a large-scale RondoDox botnet campaign using an “exploit shotgun” that targets over 50 vulnerabilities across more than 30 vendors to compromise internet-exposed routers, DVRs, NVRs, CCTV systems, and web servers. Active exploitation has been observed globally since mid-2025, leveraging vulnerabilities including CVE-2023-1389, CVE-2024-3721, and CVE-2024-12856, with several CVEs added to CISA’s KEV catalog. #CVE-2023-1389 #CVE-2024-3721 #CVE-2024-12856
Keypoints
- RondoDox is a large-scale botnet campaign observed since mid-2025 that exploits command-injection and other flaws in internet-facing infrastructure across over 30 vendors.
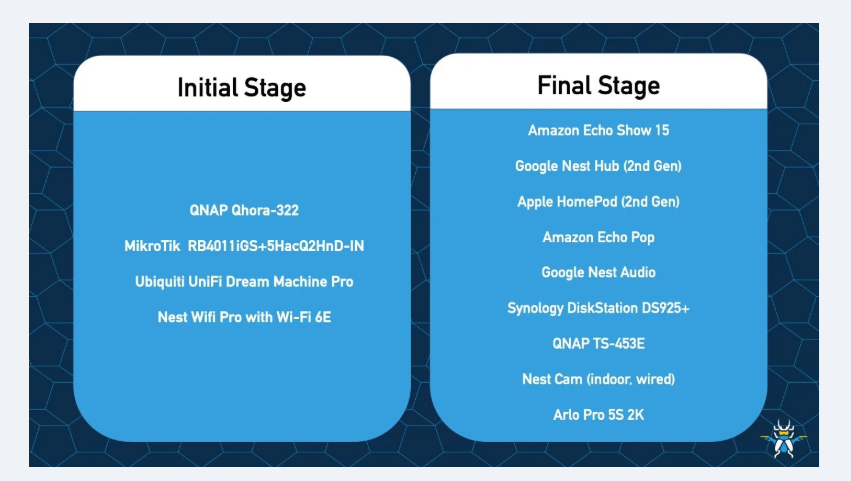
- The campaign uses an “exploit shotgun” approach with 56 identified vulnerabilities (38 CVE-assigned, 18 no-CVE) to maximize successful compromises.
- CVE-2023-1389 (TP-Link Archer AX21) was reused from a Pwn2Own disclosure and observed in RondoDox activity starting June 15, 2025.
- Notable exploited CVEs include CVE-2024-3721 (TBK DVR) and CVE-2024-12856 (Four-Faith routers); several were added to CISA’s KEV list, raising patching priority.
- RondoDox leverages loader-as-a-service infrastructure to distribute RondoDox alongside Mirai/Morte payloads, increasing scale and persistence.
- Post-exploitation actions include dropping multi-architecture payloads and shell commands (e.g., “#!/bin/sh”, “chmod 777”, “service apparmor stop”) to establish persistence.
- Mitigations recommended: prioritize patching (especially KEV entries), maintain asset inventories, network segmentation, continuous monitoring, and apply existing Trend Micro protections and detection rules.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – RondoDox exploited public-facing device vulnerabilities to gain shell access, described as “weaponizes longstanding command-injection flaws in internet-facing routers, DVRs, NVRs, CCTV systems, and other networking equipment to gain shell access.”
- [T1059 ] Command and Scripting Interpreter – Post-exploitation uses shell commands to deploy payloads and modify system state, evidenced by detection strings like “‘#!/bin/sh’ and ‘chmod 777’ and ‘service apparmor stop’”.
- [T1105 ] Ingress Tool Transfer – Loader-as-a-service co-packages and delivers RondoDox with other payloads (Mirai/Morte), described as “co-packages RondoDox with Mirai/Morte payloads”.
- [T1210 ] Exploitation of Remote Services – The campaign targets remote services on routers, DVRs, NVRs, and web servers using multiple CVEs (e.g., CVE-2023-1389, CVE-2024-3721, CVE-2024-12856) to achieve remote code execution (“command-injection flaws … to gain shell access”).
- [T1547 ] Boot or Logon Autostart Execution (persistence) – Dropped multi-architecture payloads and modifications (e.g., chmod 777) indicate efforts to ensure execution and persistence after exploitation (“to drop multiarchitecture payloads”).
Indicators of Compromise
- [Email Address ] Common proton/tutanota addresses used in samples – [email protected], [email protected]
- [Command Strings ] Post-exploitation payload indicators – “#!/bin/sh”, “chmod 777”, “service apparmor stop”
- [CVE Identifiers ] Vulnerabilities exploited as part of the campaign – CVE-2023-1389, CVE-2024-3721 (and 36 more CVE entries listed)
- [File/Process Pattern ] Loader/post-exploit hostname pattern – examples include domain pattern matching “rondo.” as in regex /brondo./ (used in detection rules)
- [Product/Device Names ] Affected device/product examples – TP-Link Archer AX21, TBK DVR, Four-Faith routers
Read more: https://www.trendmicro.com/en_us/research/25/j/rondodox.html