Attackers are commoditizing the ClickFix social-engineering technique into phishing kits like the IUAM ClickFix Generator to automate creation of spoofed browser-verification pages that trick victims into manually executing malware. Observed campaigns delivered DeerStealer and Odyssey infostealer using clipboard-injection and OS-detection features from hosted phishing pages. #IUAM_ClickFix_Generator #DeerStealer #Odyssey
Keypoints
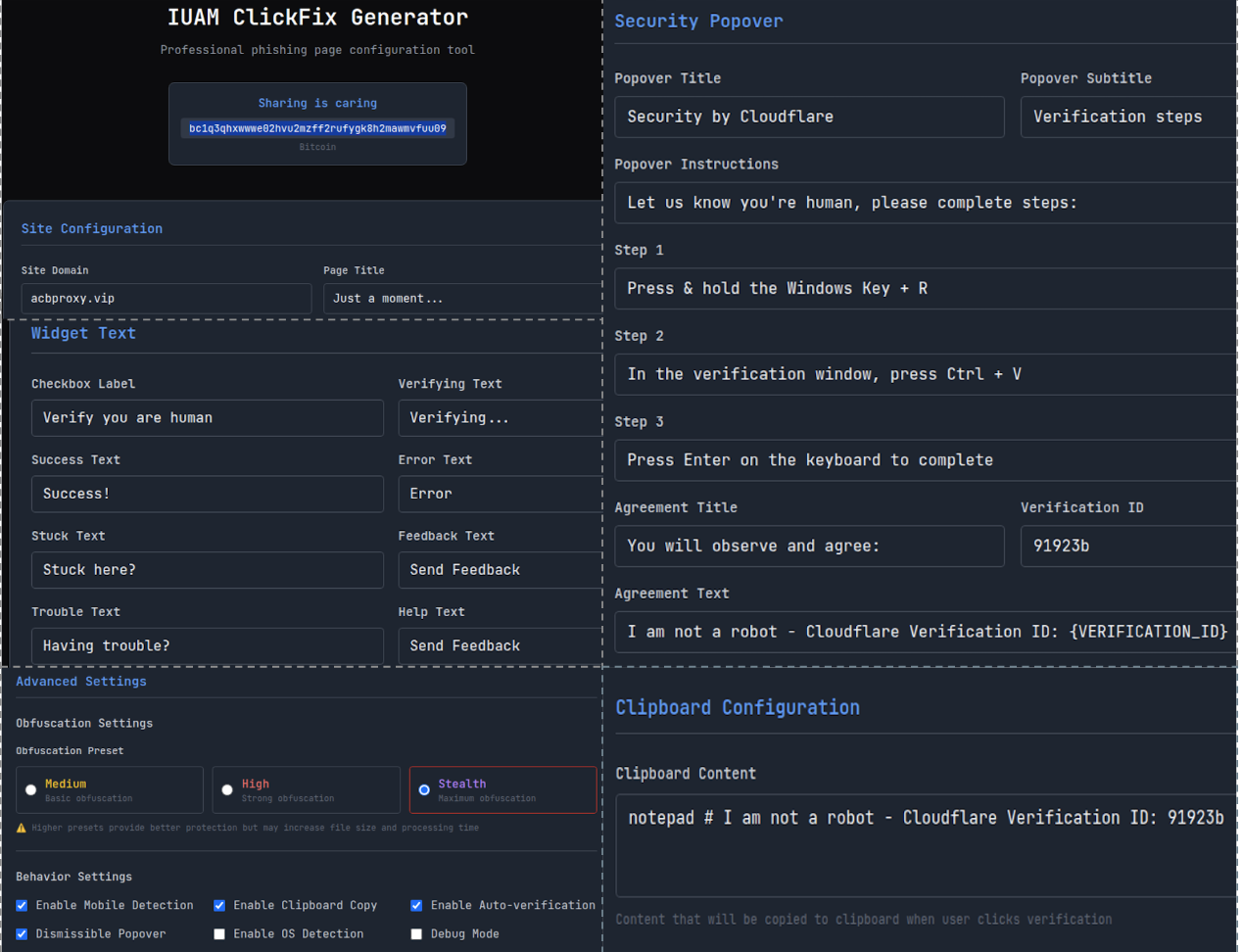
- Threat actors are using a publicly exposed phishing kit called IUAM ClickFix Generator to create customizable ClickFix-themed phishing pages that mimic CDN/browser verification challenges.
- The kit offers features such as clipboard injection, OS detection, editable messaging, obfuscation, and UI configuration to maximize social engineering effectiveness across platforms.
- At least one campaign delivered DeerStealer on Windows by copying a malicious PowerShell command to the clipboard that executed a multi-stage batch script and MSI payload.
- Multiple variants of phishing pages were observed delivering Odyssey infostealer to macOS users and other unidentified malware to Windows users, indicating a shared codebase or builder tool and affiliate customization.
- IOCs include 18 Odyssey and 8 DeerStealer SHA256 hashes, multiple Odyssey C2 IP addresses, and a long list of malicious or lookalike domains used to host the phishing pages.
- Developer artifacts and Russian-language comments in some pages suggest shared origins and possible Russian-speaking developer involvement or leftover code from the builder.
- Palo Alto Networks products (Advanced URL Filtering, Advanced DNS Security, WildFire, Cortex XDR, XSIAM) are noted as protective and mitigation measures and Unit 42 is available for incident response.
MITRE Techniques
- [T1204] User Execution – Victims are socially engineered to manually paste and run copied commands from their clipboard (“…a popover appears, instructing them to open the Windows Run dialog… paste the content from their clipboard and run the command.”).
- [T1059] Command and Scripting Interpreter – Phishing pages place PowerShell, batch, or Base64-encoded shell commands into the clipboard to be executed by victims (“…this action triggers a background JavaScript to copy a malicious PowerShell command to their clipboard…”).
- [T1490] Ingress Tool Transfer – Multi-stage download and execution observed (batch script downloads MSI) to transfer and install malware (“…downloads a batch script cv.bat…that ultimately installs the DeerStealer infostealer.”).
- [T1078] Valid Accounts (decoy behavior) – Pages sometimes present benign-looking or decoy commands for certain OSes to maintain lure credibility (“…Windows users receive a PowerShell command as a benign decoy intended to complete the social engineering lure without delivering a payload.”).
- [T1203] Exploitation for Client Execution – Use of crafted commands and OS-specific payload delivery to cause execution on victim endpoints (“…macOS users receive a Base64-encoded command to deliver Odyssey… PowerShell command designed to download and execute an unidentified malware strain.”).
- [T1588] Obtain Capabilities – Use and distribution of phishing kit (IUAM ClickFix Generator) and MaaS (Odyssey) to lower barrier and provide tooling to affiliates (“…Odyssey is a malware-as-a-service (MaaS) offering… actor has allegedly supplied ClickFix-style lure pages to affiliates…”).
Indicators of Compromise
- [File Hash ] Malware samples – DeerStealer example: ead6b1f0add059261ac56e9453131184bc0ae2869f983b6a41a1abb167edf151, cv.bat batch script: 2b74674587a65cfc9c2c47865ca8128b4f7e47142bd4f53ed6f3cb5cf37f7a6 (and 24 more hashes).
- [Domain ] Hosting/phishing pages and C2 – Examples: tradingview.connect-app.us[.]com (hosting), Odyssey1[.]to (Odyssey C2/malware hosting), and many others like cloudlare-lndex[.]com and Emailreddit[.]com.
- [IP Address ] Odyssey C2 servers – Examples: 45.146.130[.]129, 185.93.89[.]62 (and other IPs listed for Odyssey C2 infrastructure).
- [File Name ] Downloaded artifacts – cv.bat (batch script used in DeerStealer delivery), MSI payload (DeerStealer MSI SHA256: ead6b1f0add0…), and other multi-stage download filenames referenced in campaigns.
- [URL/Host Variation ] Typosquatted or lookalike domains – Examples: cloudlare-lndex[.]com (looks like Cloudflare), treadingveew.last-desk[.]org (looks like tradingview variants) used to increase credibility.
Read more: https://unit42.paloaltonetworks.com/clickfix-generator-first-of-its-kind/