Kaspersky integrated a machine-learning model for detecting DLL-hijacking (DLL sideloading) into its SIEM (Kaspersky SIEM), which analyzes loaded libraries with local attributes and Kaspersky Security Network validation to improve detection and reduce false positives. During pilot MDR testing the model detected multiple real incidents — including ToddyCat using Cobalt Strike via DLL sideloading, an infostealer masquerading as policymanager.dll, and a malicious loader (wsc.dll) on a USB drive — and flagged related IOCs. #ToddyCat #CobaltStrike #SystemSettings.dll #policymanager.dll #wsc.dll
Keypoints
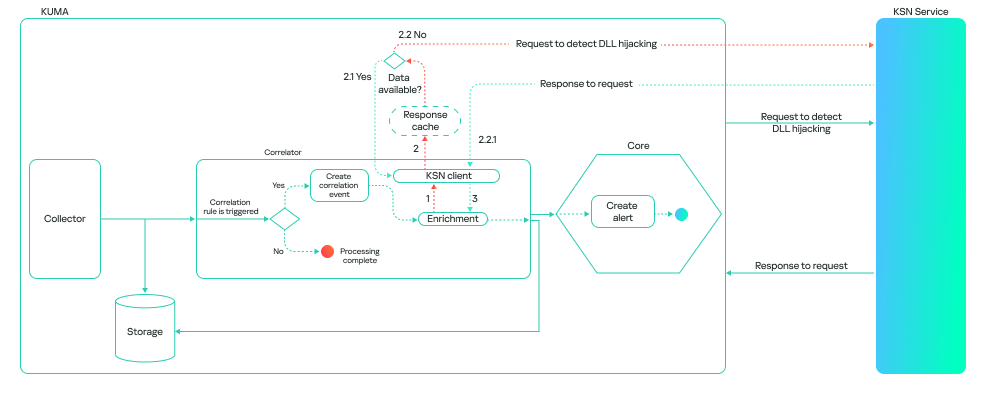
- The ML model inspects DLL libraries loaded by processes and validates attributes (path, process name, hashes) with Kaspersky Security Network (KSN) to improve detection and reduce false positives.
- The model can run on a correlator (checks events that triggered rules) or a collector (processes all qualifying events), trading resource use for coverage and retrospective hunting capability.
- Verdicts are confidence-ranked (0 data processing, 1 not malicious, 2 suspicious, 3 malicious), enabling flexible SOC use and correlation with other telemetry.
- Pilot MDR deployment detected real-world DLL sideloading incidents, confirming model robustness beyond lab environments.
- Incident 1: ToddyCat exploited CVE-2021-27076 in SharePoint/IIS, sideloaded a malicious SystemSettings.dll (Cobalt Strike) and established persistence via a scheduled task.
- Incident 2: A relocated SettingSyncHost.exe loaded policymanager.dll, which was an infostealer accessing Chrome user data and matched entries in the HijackLibs list.
- Incident 3: A USB-borne attack used shortcuts to launch CEFHelper.exe that sideloaded wsc.dll (malicious loader) which decrypted and executed an AvastAuth.dat backdoor.
MITRE Techniques
- [T1574.001] Hijack Execution Flow: DLL – Attackers used DLL sideloading to execute malicious code by placing a malicious DLL next to a legitimate executable and having the legitimate process load it: ‘…DLL sideloading technique…’
- [T1210] Exploitation of Client Execution Vulnerability (CVE-2021-27076) – Exploitation of a SharePoint service using IIS allowed execution of commands that led to malicious DLL deployment: ‘…leveraged the vulnerability CVE-2021-27076 to exploit a SharePoint service that used IIS as a web server.’
- [T1053.005] Scheduled Task/Job: Scheduled Task – Persistence was achieved by creating a scheduled task disguised as an Edge update to run the malicious SystemSettings.exe daily: ‘…Schtasks /create /ru “SYSTEM” /tn “MicrosoftWindowsEdgeEdgeupdates” /sc DAILY /tr “C:ProgramDataSystemSettings.exe” /F’
- [T1105] Ingress Tool Transfer (USB) – Attackers used a removable USB drive with shortcuts that executed an executable which then sideloaded a malicious DLL: ‘…connected a removable USB drive… the shortcut opened the corresponding hidden folder and ran an executable…’
- [T1041] Exfiltration Over C2 Channel / Command and Control – After loading malicious DLLs (e.g., Cobalt Strike implant, backdoor), the malware connected to remote C2 servers for reconnaissance and further commands: ‘…attempted to connect to the attackers’ command-and-control server.’
Indicators of Compromise
- [File path] Suspicious/malicious file locations – C:ProgramDataSystemSettings.exe, C:ProgramDataSystemSettings.dll; C:Program FilesChiniksSettingSyncHost.exe, C:Program FilesChinikspolicymanager.dll; D:RECYCLER.BIN1CEFHelper.exe, D:RECYCLER.BIN1wsc.dll
- [File hash] Malicious library hashes – EA2882B05F8C11A285426F90859F23C6 (SystemSettings.dll), E83F331BD1EC115524EBFF7043795BBE (policymanager.dll), 831252E7FA9BD6FA174715647EBCE516 (wsc.dll)
- [File hash] Legitimate files used for hijacking – E0E092D4EFC15F25FD9C0923C52C33D6 (loads SystemSettings.dll), 09CD396C8F4B4989A83ED7A1F33F5503 (loads policymanager.dll), A72036F635CECF0DCB1E9C6F49A8FA5B (loads wsc.dll)
- [Domain / IP] C2 domain and IP observed – connect-microsoft[.]com resolving to 8.219.1[.]155; 8.219.1[.]155:8443 (used by Cobalt Strike implant)
- [File name] Executables and DLL names used in attacks – SystemSettings.dll, policymanager.dll, wsc.dll, CEFHelper.exe (and other Avast-related files); hijack library names listed in HijackLibs project
Read more: https://securelist.com/detecting-dll-hijacking-with-machine-learning-in-kaspersky-siem/117567/