XWorm resurfaced in 2025 as XWorm V6.0 with a modular plugin architecture enabling remote access, credential theft, ransomware, and persistence via multiple techniques including ResetConfig.xml. Trellix ARC analyzed the V6 campaign, identified C2 infrastructure (94[.]159[.]113[.]64:4411), numerous plugins (e.g., RemoteDesktop.dll, FileManager.dll, Ransomware.dll), and linked code overlap with NoCry and distribution via cracked builders. #XWorm #NoCry
Keypoints
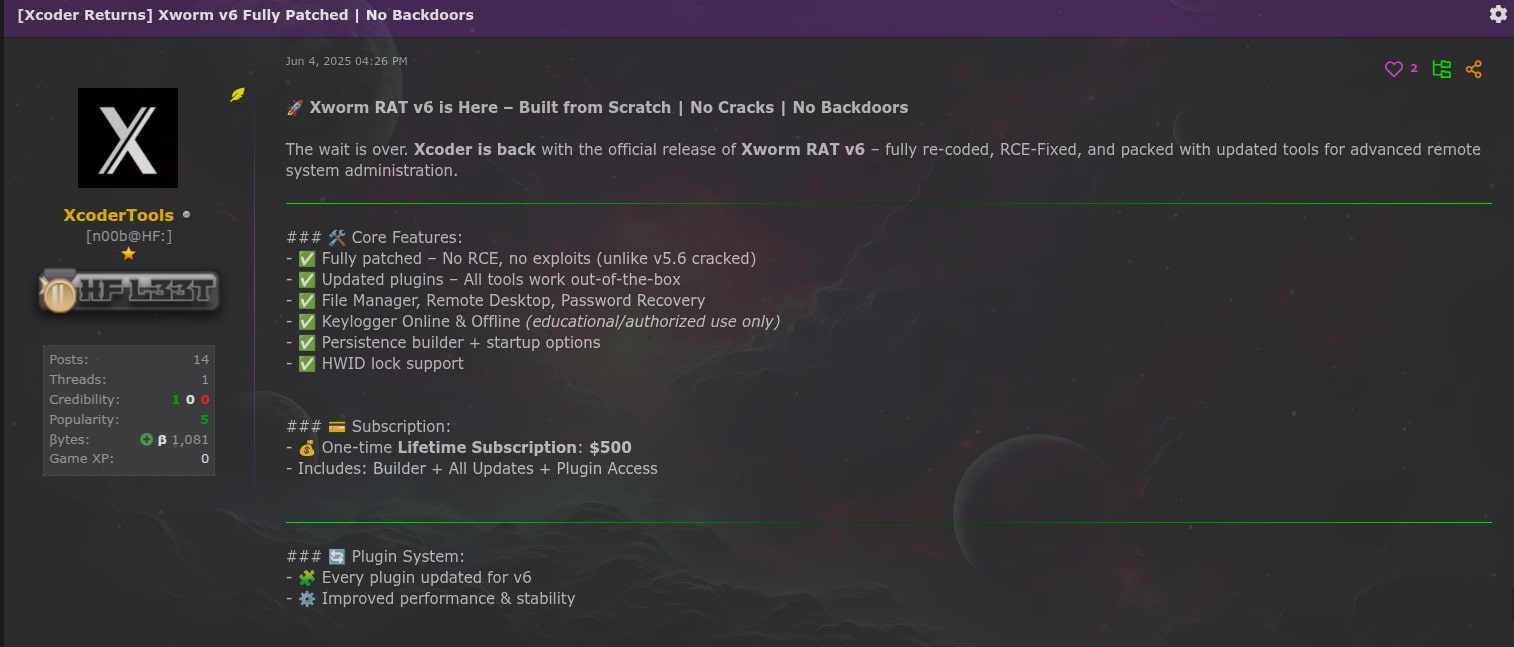
- XWorm was believed abandoned after XCoder deleted their account in 2024, but XWorm V6.0 was released (or rebranded) in June 2025, sparking rapid adoption and many samples on VirusTotal.
- The XWorm V6 infection chain commonly uses a malicious JavaScript that runs a PowerShell script, disables AMSI, uses a DLL injector (targeting legitimate processes like RegSvcs.exe), and deploys an XWorm client that contacts C2 (94[.]159[.]113[.]64:4411) using preset encryption keys.
- XWorm V6 implements a plugin system (plugins delivered as gzip/base64 and stored under HKCUSOFTWARE) enabling >35 capabilities including remote desktop, stealer, file manager, shell execution, TCP connection control, and ransomware.
- The ransomware plugin (Ransomware.dll) encrypts user files with AES-CBC derived from the ClientID, drops a ransom HTML, changes wallpaper, and shows code overlap with NoCry ransomware (including key/IV generation and anti-analysis checks).
- Multiple persistence methods are used by operators via a .wsf script: logon script, Run registry keys, persistent PowerShell loop, and ResetConfig.xml-based factory reset persistence (if elevated privileges exist).
- Cracked and leaked builders (including V6.0 and V6.4 variants) circulated publicly; modified builds added Rootkit.dll and ResetSurvival.dll to install a rootkit and abuse C:RecoveryOEM for survival.
- Trellix ARC captured numerous IOCs (file hashes, C2 IP/port, pastebin and download URLs), observed operators deploying additional malware (DarkCloud Stealer, Remcos, coin miners), and emphasized detection via EDR, email/web defenses, and network monitoring.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – JavaScript and PowerShell are used to download and execute subsequent stages: ‘a malicious JavaScript (JS) file initiates a PowerShell (PS1) script’ and the PowerShell disables AMSI and loads payloads.
- [T1112] Modify Registry – Plugins and persistence are stored/registered under HKCUSOFTWARE and persistence Run keys and UserInitMprLogonScript are created: “‘creates a registry entry in UserInitMprLogonScript’ … ‘creates a registry entry in HKCUSoftwareMicrosoftWindowsCurrentVersionRun’”.
- [T1140] Deobfuscate/Decode Files or Information – Plugins are delivered as base64-encoded gzip blobs and decoded by the client: “‘savePlugin’ along with a base64 encoded string containing the plugin…Upon receiving and decoding the plugin, the client loads the plugin into the memory.”
- [T1055] Process Injection – An injector DLL injects the XWorm client into legitimate processes like RegSvcs.exe by manipulating process memory: “‘inject the XWorm Client’s malicious code into a legitimate Windows program like RegSvcs.exe…by manipulating the program’s memory’”.
- [T1005] Data from Local System – Stealer plugins extract credentials and local artifacts (browser data, FileZilla, Telegram, Windows product key): “‘steals the following: FileZilla Login credentials, Wifi password, Discord credentials, Windows Product key, Telegram credentials, MetaMask credentials’”.
- [T1027] Obfuscated Files or Information – XWorm plugins are protected with ILProtector and unpacked with ILPUnpack: “‘plugins are protected using ILProtector which were unpacked using the tool ILPUnpack’”.
- [T1490] Inhibit System Recovery – Use of ResetConfig.xml to persist across factory reset by configuring Windows push-button reset to run attacker install.cmd: “‘creates ResetConfig.xml which is a configuration for Windows’ push-button reset feature…configured to run an install.cmd script during a factory reset’”.
- [T1486] Data Encrypted for Impact – Ransomware.dll encrypts user files with AES-CBC derived from ClientID and appends .ENC, then drops ransom instructions and changes wallpaper: “‘creates an encrypted file using the AES-CBC algorithm and permanently deletes the original…drops an HTML file named “How To Decrypt My Files.html”‘”.
- [T1071] Application Layer Protocol – C2 communication to IP and port (e.g., 94[.]159[.]113[.]64:4411) uses custom splitter and AES encryption for command/control and plugin retrieval: “‘connects to its Command and Control (C2) server (94[.]159[.]113[.]64 on port 4411), using an encryption key’”.
- [T1105] Ingress Tool Transfer – The RemoteDesktop.dll downloads and executes an additional XWorm instance from external URL (pastebin → hxxp://196[.]251[.]84[.]137:1337/RunShell[.]exe): “‘RemoteDesktop.dll contains the URL: hxxps://pastebin[.]com/raw/ZqAnzZcM, which contains the URL: hxxp://196[.]251[.]84[.]137:1337/RunShell[.]exe’”.
Indicators of Compromise
- [IP Address] C2 server – 94[.]159[.]113[.]64:4411 (XWorm V6 client C2 communication)
- [IP Address / URL] Downloader URL – hxxp://196[.]251[.]84[.]137:1337/RunShell[.]exe (observed in RemoteDesktop.dll via pastebin)
- [Domain/URL] Paste content – hxxps://pastebin[.]com/raw/ZqAnzZcM (contains download URL used by plugin)
- [File Hash (SHA256)] XWorm client and loaders – 570e4d52b259b460aa17e8e286be64d5bada804bd4757c2475c0e34a73aeb869 (XWormClient.exe), 000185a17254cd8863208d3828366ec25ddd01596f18e57301355d4a33eac242 (RunShell.exe)
- [File Hash (SHA256)] Plugins and artifacts – 31376631aec4800de046e1400e948936010d9bbedec91c45ae8013c1b87564d0 (RemoteDesktop.dll), 5314c7505002cda1e864eced654d132f773722fd621a04ffd84ae9bc0749b791 (TCPConnections.dll), 64cbbbf90fe84eda1a8c2f41a4d37b1d60610e7136a02472a72c28b6acadc2fc (Ransomware.dll)
- [File Name] Initial droppers and scripts – OSHA_Investigation_Case_0625OQI685837AW.pdf.js (malicious JS dropper) and payload_1.ps1 (PowerShell stage)
Read more: https://www.trellix.com/blogs/research/xworm-v6-exploring-pivotal-plugins/