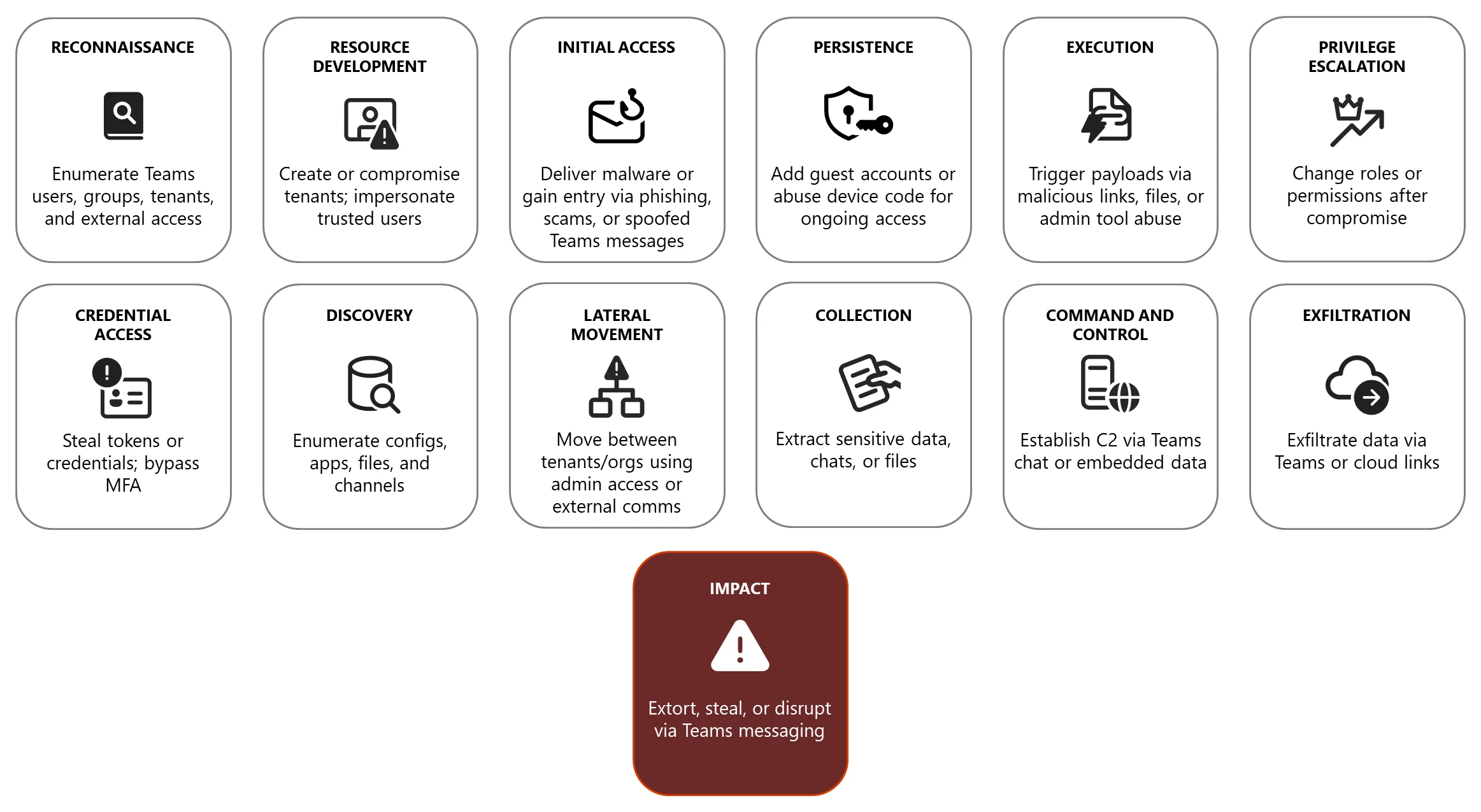
Microsoft Teams’ widespread use and rich collaboration features make it a frequent target for both criminal and state-sponsored actors who abuse chat, calls, meetings, and screen-sharing across the attack chain to gain initial access, persist, move laterally, exfiltrate data, and pressure victims for ransom or theft. #Storm-1811 #TeamsPhisher
Keypoints
- Teams identities are backed by Microsoft Entra ID and can be enumerated via Graph API and open-source tools (e.g., ROADtools, TeamsEnum) to perform reconnaissance and map privileges.
- Threat actors use resource development (fake tenants, branding, purchased tenants) and social engineering (tech support scams, deepfakes) to lure victims into installing RMM tools or divulging credentials.
- Notable actors and techniques: Storm-1811, Storm-1674, Storm-2372, Storm-0324, Midnight Blizzard, Octo Tempest, and tools like TeamsPhisher, DarkGate, ReedBed, JSSloader, AnyDesk, AADInternals for token/credential theft and persistence.
- Attack chain abuses include phishing via Teams, device code phishing to capture tokens, malicious files and links, C2 via Teams messages (ConvoC2, BRc4), and exfiltration through cloud storage and Graph API.
- Defenders should harden identity, endpoints, apps, and network: enable Conditional Access, CAE, EDR in block mode, tamper protection, cloud-delivered protection, and enforce device compliance via Intune/Defender for Endpoint.
- Monitoring and detection recommendations include auditing Teams activity in Microsoft Purview, using Defender for Cloud Apps and Defender XDR alerts, populating advanced hunting tables (MessageEvents, CloudAppEvents), and integrating with Microsoft Sentinel data lake.
- Provide user awareness and training (attack simulations, QR code phishing, deepfake awareness), secure Teams apps and developer practices (Graph API best practices), and configure detection policies to find anomalous behavior and illicit consent grants.
MITRE Techniques
- [T1598] Drive-by Compromise – Threat actors may use Teams to direct users to malicious websites or spoofed installers (e.g., “malvertising campaign delivering credential-stealing malware through a fake Microsoft Teams for Mac installer”).
- [T1190] Exploit Public-Facing Application – Actors exploit or spoof Teams apps and app installers (including fake or cracked installers) to gain initial access (“fake Microsoft Teams for Mac installer”).
- [T1586] Compromise Infrastructure – Use of purchased or weakly configured legitimate tenants and trial subscriptions to impersonate trusted organizations and stage operations (“purchasing legitimate ones … build a persona for social engineering”).
- [T1595] Active Scanning – Enumeration of Teams objects and tenant configuration via Microsoft Graph API and DNS using tools like ROADtools, TeamFiltration, TeamsEnum (“enumerating teams, members of teams and channels, tenant IDs and enabled domains”).
- [T1078] Valid Accounts – Actors obtain and reuse compromised or purchased accounts including admin roles to access Teams and escalate privileges (“obtain Teams admin access … could potentially leverage external communication settings …”).
- [T1110] Brute Force – Password spraying and other credential attacks targeting Teams accounts to request OAuth tokens and access services (“password spraying … request OAuth tokens for Teams”).
- [T1204] User Execution – Social engineering via Teams chats, calls, and meetings persuading users to click links, open files, or install remote access tools (e.g., AnyDesk) (“impersonated a client during a Teams call to persuade a target to install AnyDesk”).
- [T1531] Account Discovery – Using tools like AzureHound and AADInternals to enumerate Microsoft Entra ID configuration, users, roles, groups, and applications (“Void Blizzard has used AzureHound to enumerate … Microsoft Entra ID configuration”).
- [T1091] Replication Through Removable Media and External Services – Exfiltration via cloud storage and shared links in Teams to attacker-controlled cloud storage (“use Teams messages or shared links to direct data exfiltration to cloud storage under their control”).
- [T1105] Ingress Tool Transfer – Distribution of malware and loaders (DarkGate, ReedBed, JSSloader) over Teams to deploy payloads (“TeamsPhisher … distribute DarkGate malware and other malicious payloads over Teams”).
- [T1136] Create Account – Creation of guest users or adding credentials in target tenants to maintain persistence (“try to create guest users in target tenants or add their own credentials to a Teams account to maintain access”).
- [T1071] Application Layer Protocol – Use of Teams messaging protocols and Adaptive Cards for C2 (ConvoC2, BRc4 features) to send commands and exfiltrate data (“ConvoC2 to send commands through Microsoft Teams messages using the Adaptive Card framework”).
- [T1530] Data from Cloud Storage – Accessing OneDrive/SharePoint via Graph API or tools like GraphRunner and TeamFiltration to collect or exfiltrate chats and files (“GraphRunner … search all chats and channels and export Teams conversations”).
- [T1588] Obtain Capabilities – Use or abuse of admin tools (AADInternals, AADInternals-federation) and legitimate remote management tools to forge tokens or take over MFA (“AADInternals … federate existing domains … forge tokens”).
- [T1589] Gather Victim Host Information – Using presence and directory enumeration to identify user availability and misconfigurations for targeting (“Presence indicates a user’s current availability … could then be exploited if the admin has not disabled external meetings and chat”).
Indicators of Compromise
- [Tool/Threat Actor ] reported misuse examples – Storm-1811 (ReedBed loader, RMM delivery), Storm-1674 (TeamsPhisher distributing DarkGate)
- [Malicious Files/Loaders ] examples observed – DarkGate, ReedBed, JSSloader, and other payloads (“DarkGate”, “ReedBed”)
- [Utility/Tooling ] admin/attack tools repurposed – AADInternals, TeamsPhisher, TeamFiltration, AzureHound, GraphRunner, ConvoC2 (used for token theft, enumeration, C2, exfiltration)
- [Spoofed App/Installer ] malicious installer examples – fake Microsoft Teams for Mac installer (malvertising campaign delivering credential-stealing malware)
- [Techniques/Artifacts ] campaign behaviors – mail bombing preceding tech support scams; device code phishing to capture authentication tokens (Storm-2372 used device code authentication flows)