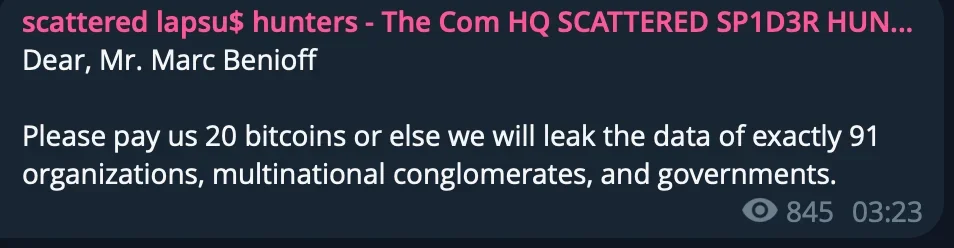
Scattered Lapsus$ Hunters — an alliance of Scattered Spider, LAPSUS$, and ShinyHunters — carried out coordinated social‑engineering intrusions into Salesforce environments of numerous major companies in mid‑2025, stealing data from at least 91 organizations without exploiting Salesforce vulnerabilities. The group scaled vishing and OAuth abuse (often via trojanized Data Loader apps and credential‑theft malware), leaked extortion demands on Telegram, and targeted high‑value sectors including technology, luxury retail, aviation, and insurance. #ScatteredSpider #ShinyHunters
Category: Threat Research

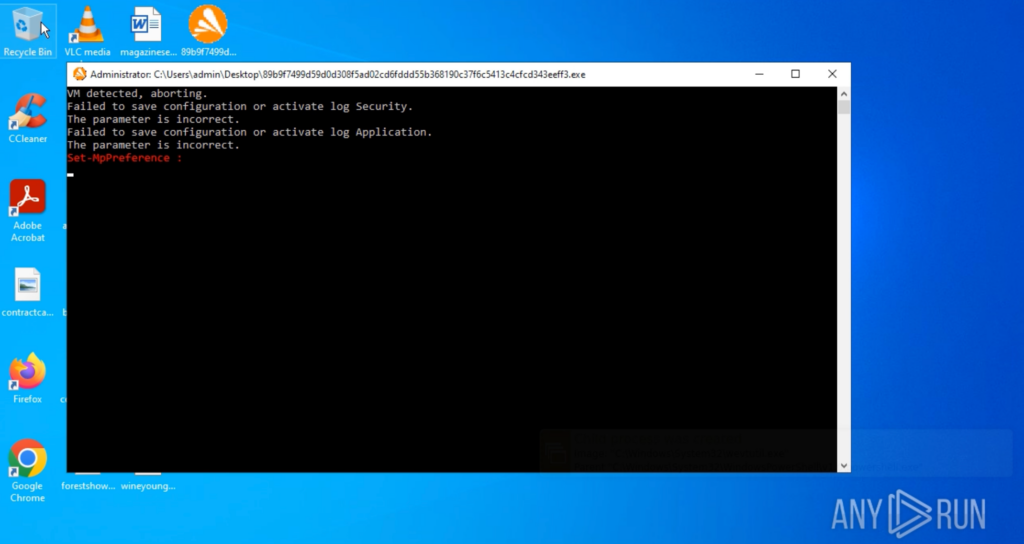
Yurei Ransomware is a Go-based, professional ransomware family that encrypts files with per-file ChaCha20 keys wrapped by ECIES, appends a .Yurei extension, and implements aggressive anti-forensics (shadow copy and log deletion, secure delete, memory wiping) while spreading via SMB, removable media, and credential-based remote execution. Ransom notes include Tor .onion contact channels and victim tracking for double-extortion; samples and artifacts include YureiRansomware.exe and related PowerShell scripts. #YureiRansomware #YureiSupp

Gunra is a double-extortion ransomware group active since April 2025 that primarily targets non‑US organizations across multiple industries, using phishing, DoNoT loader routines, and high‑speed stream ciphers (Salsa20/ChaCha20) to encrypt large data volumes and publish exfiltrated data on a dark‑web DLS. The group operates a WhatsApp‑themed negotiation portal (Slack backend), hosts a clearnet mirror (datapub.news), and uses tools like Lumma Stealer and ConnectWise‑like payloads while listing victims on multiple TOR domains. #Gunra #DoNoT #datapub.news

Confucius, a long-running espionage actor active primarily in South Asia, has evolved from using document stealers like WooperStealer to deploying Python-based backdoors such as AnonDoor, leveraging spear-phishing, malicious LNK files, OLE objects, DLL side-loading, and scheduled tasks for persistence. Recent campaigns targeted Microsoft Windows users in Pakistan and exfiltrated a wide range of files to domains including marshmellowflowerscar.info and bloomwpp.info. #WooperStealer #AnonDoor

Attackers created fake Facebook groups targeting active seniors to distribute Android malware posing as event registration apps, sometimes asking for sign-up fees to phish card details. The primary malware observed was the Datzbro trojan (and occasionally the Zombinder dropper), delivered via links or messages and capable of audio/video recording, overlay phishing,…
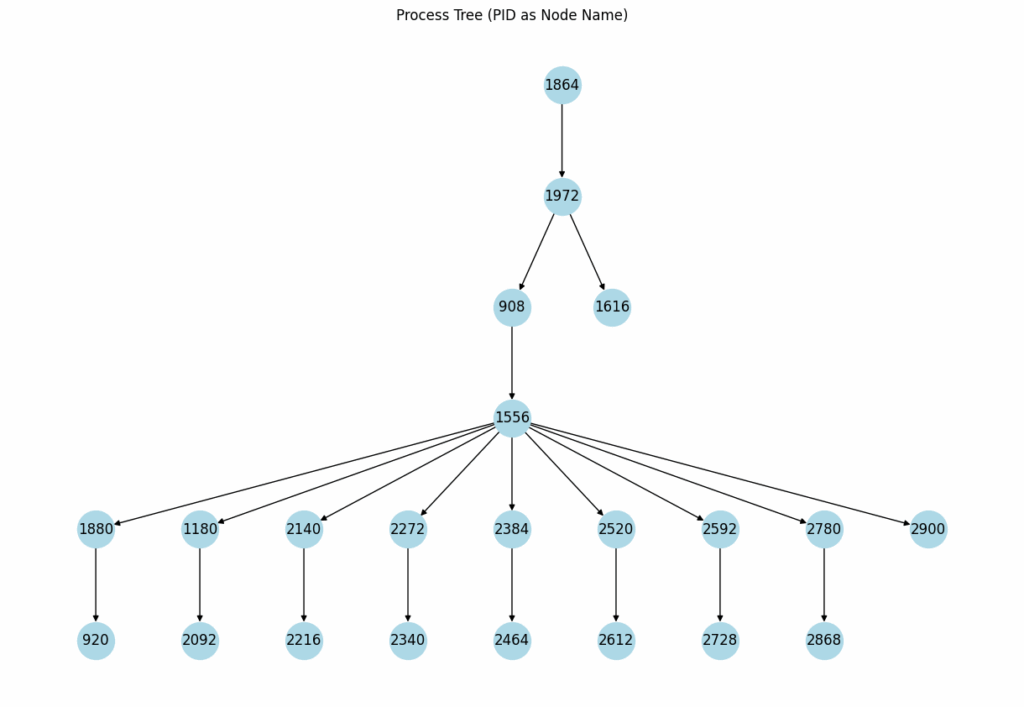
Lumma Stealer resurfaced in 2025 with new variants employing heavy obfuscation, AutoIt-based loaders, anti-analysis checks, DLL unhooking, and persistence via Startup shortcuts; Netskope detected a specific NSIS-signed sample (hash 87118baadfa7075d7b9d2aff75d8e730) using a transformer-based ML model on runtime process trees and behavioral features. #LummaStealer #AutoIt

TAG-150 has been deploying CastleLoader, CastleBot, and a newly identified CastleRAT (Python and C variants) since March 2025 using a multi-tiered infrastructure and phishing lures like Cloudflare-themed “ClickFix” and fake GitHub repositories. CastleRAT provides reconnaissance, command execution, and advanced capabilities (keylogging, screen capture) while leveraging services such as Kleenscan, temp.sh, and Steam Community for anti-detection and C2 operations. #CastleRAT #CastleLoader

Security teams face rising ransomware threats, increasing use of zero-days, and operational overload from too many tools and alert fatigue, making contextualized, prioritized threat intelligence essential. Automation, enrichment, and vendor partnerships that align with standards like STIX and MITRE ATT&CK help teams scale, focus on what matters, and respond faster. #Ransomware #Zero-day
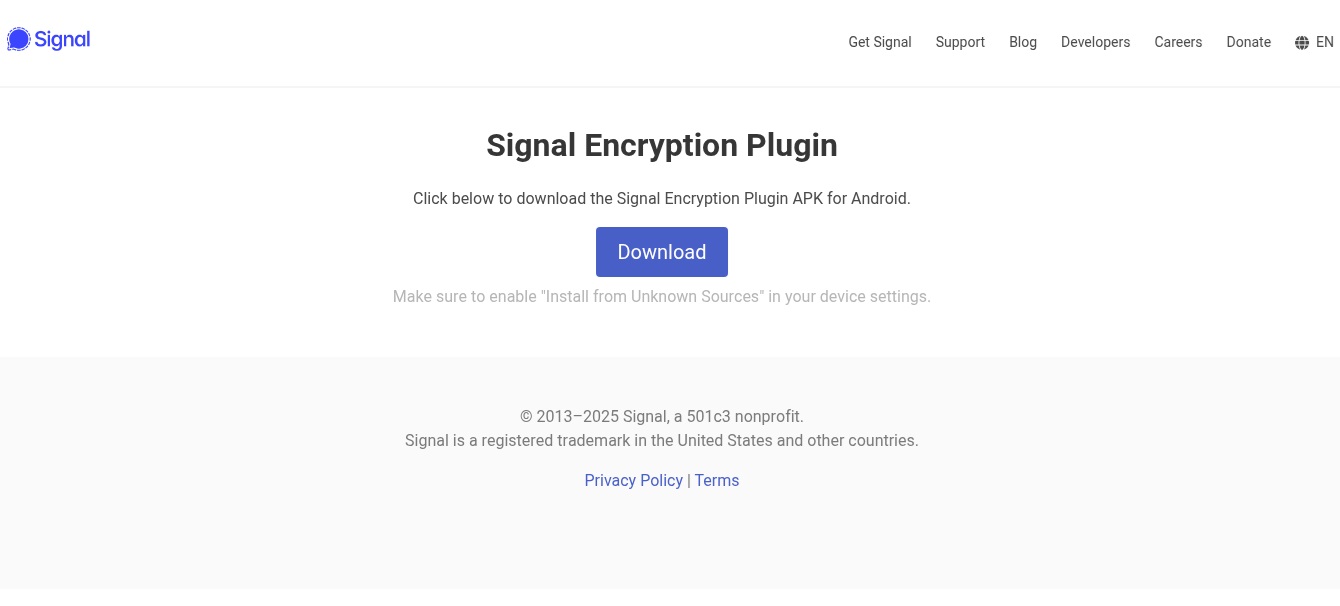
ESET researchers discovered two undocumented Android spyware families—Android/Spy.ProSpy and Android/Spy.ToSpy—that impersonate Signal and ToTok to trick users into manually installing malicious APKs from deceptive websites, with confirmed targeting of users in the United Arab Emirates. Both families persist on devices and exfiltrate sensitive data (including ToTok .ttkmbackup files) to active C2 servers, and known samples/domains and hashes have been shared. #Android/Spy.ProSpy #Android/Spy.ToSpy

Elastic Security Labs reports continued active development and distribution of the WARMCOOKIE backdoor, including new handlers (PE, DLL, PowerShell, DLL Start export), a campaign ID field for clustering, and reuse of a distinctive SSL certificate linked to C2 infrastructure. Observed indicators include numerous C2 IPs/domains and multiple SHA-256 sample hashes; Elastic notes CASTLEBOT as a MaaS loader distributing WARMCOOKIE. #WARMCOOKIE #CASTLEBOT
Arctic Wolf observed an active campaign beginning July 21, 2025 that abused SonicWall SSL VPN access—often bypassing OTP MFA—to rapidly perform internal scanning, Impacket SMB discovery, extract Veeam credentials, and deploy Akira ransomware within hours. Early indicators included VPN logins from hosting-related ASNs, SMBv2 session requests consistent with Impacket use, and use of tools like rclone and WinRAR for exfiltration. #CVE-2024-40766 #Akira

Nimbus Manticore, an Iran-linked APT, has escalated cyberespionage using spear-phishing, fake career portals, and DLL sideloading to deliver MiniJunk backdoors and MiniBrowse stealers against defense, aerospace, and telecom targets in Western Europe and the Middle East. The actors employ heavy compiler-level obfuscation, Cloudflare/Azure-backed resilient C2 hosting, and stolen certificates to maintain stealth and persistence. #NimbusManticore #MiniJunk #MiniBrowse
FunkLocker is a FunkSec ransomware strain showing signs of AI-assisted development (snippet-style coding) that leads to many inconsistent builds but predictable destructive behavior, including forceful termination of processes and local-only encryption using the .funksec extension. Avast Labs produced a decryptor after researchers found reused BTC wallets and locally derived or hardcoded…
Rhadamanthys v0.9.2 introduces significant format and behavior changes — new XS1_B/XS2_B custom executable formats, updated config decoding (0xBEEF marker, LZO), PNG-based stage delivery, new mutex and Bot ID generation, and unpacking/evasion improvements — which break older analysis tools and require updated scripts. Check Point Research released updated converters, a string deobfuscator (for RC4 in XS2_B), and an unpacker; observed IOCs include multiple SHA256 sample hashes and C2 URL hxxps://193.84.71.81/gateway/wcm6paht.htbq1. #Rhadamanthys #ClickFix
A threat actor dubbed Detour Dog has used DNS-based server-side TXT records to conditionally redirect compromised websites and, more recently, to deliver remote-executed payloads by returning Base64-encoded “down” URLs that instruct infected sites to curl and relay staged malware from Strela/StarFish infrastructure. This campaign has been tied to distribution chains involving REM Proxy, Tofsee, Help TDS, Monetizer, and Los Pollos affiliate IDs and persisted across thousands of sites and many registrars despite sinkholing efforts. #DetourDog #StrelaStealer