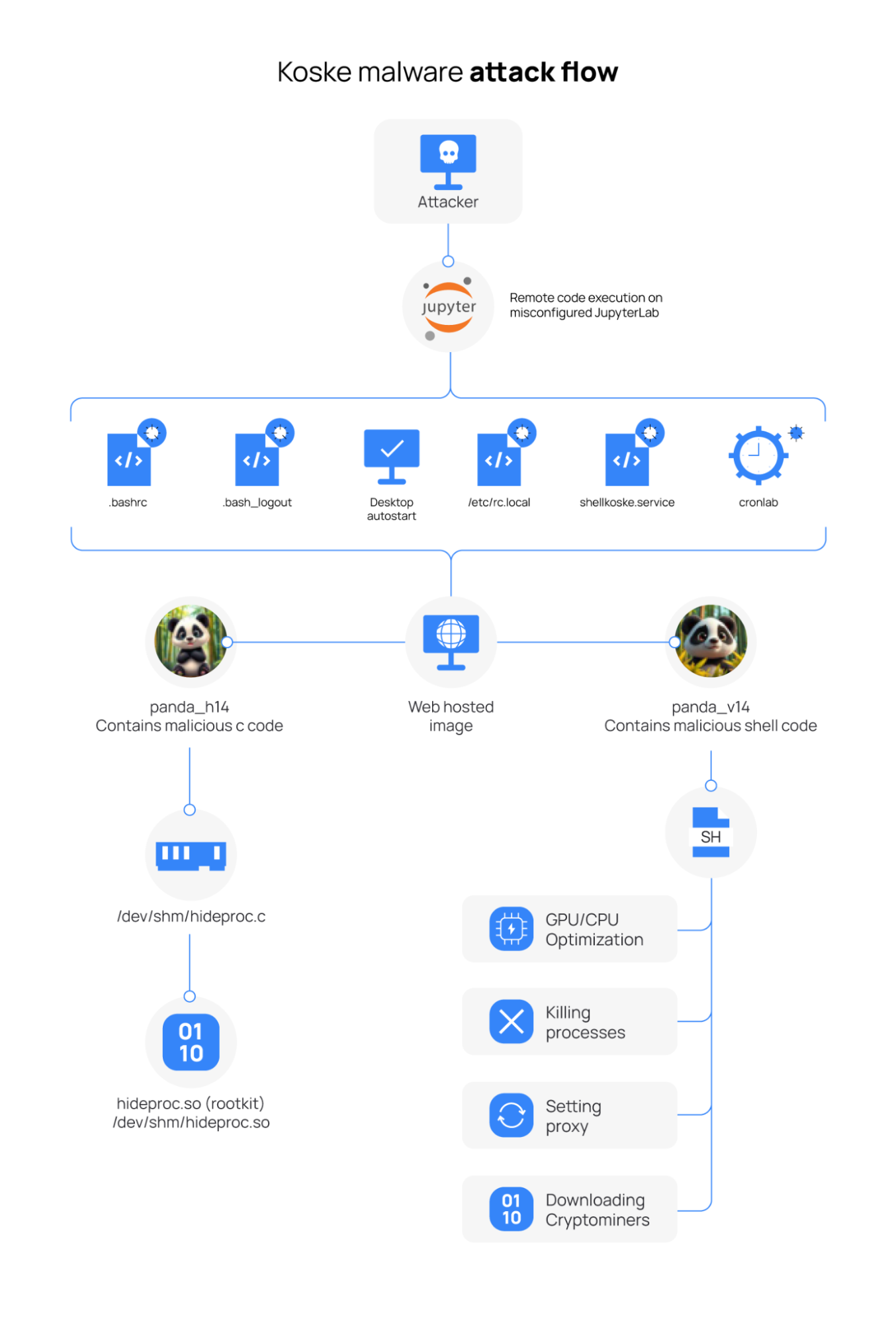
Koske is an AI-generated cryptocurrency-mining malware targeting Linux endpoints that was first identified by Aqua Nautilus in July 2025 and delivered via improperly configured JupyterLab instances using polyglot JPEGs with appended shellcode. It deploys rootkits, establishes persistence via .bashrc and systemd changes, downloads and runs multiple miners (.koske files) against mining…
Category: Threat Research

ASEC observed attacks against exposed MS-SQL servers that used weak credentials to install JuicyPotato for privilege escalation and deploy the XiebroC2 C2 framework, often alongside CoinMiner. The report includes specific IOCs and configuration details for XiebroC2 such as HostPort, Protocol, ListenerName, and AesKey. #XiebroC2 #JuicyPotato…
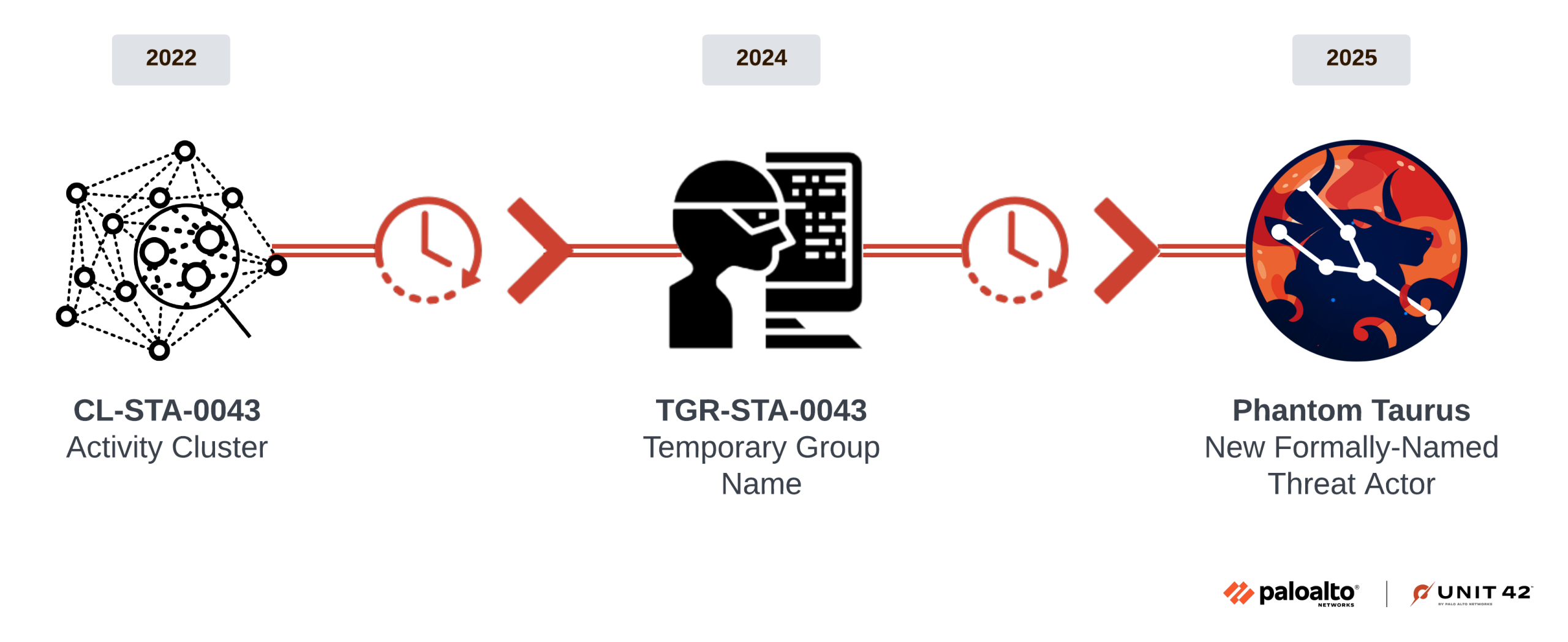
Phantom Taurus is a newly designated Chinese nation-state threat actor that conducts long-term espionage against government and telecommunications organizations across Africa, the Middle East, and Asia, using distinctive TTPs and custom tools. Researchers documented a new .NET IIS-targeting malware suite called NET-STAR (IIServerCore, AssemblyExecuter v1/v2) and a shift from email theft…

Sekoia.io observed attackers exploiting Milesight industrial cellular routers’ exposed APIs to send large-scale smishing campaigns, with a heavy focus on Belgian recipients impersonating CSAM and eBox services. The infrastructure and domains used trace to NameSilo-registered domains and hosting with Podaon SIA, and evidence shows unauthenticated SMS inbox/outbox APIs and campaigns active since at least February 2022. #Milesight #CSAM #eBox #PodaonSIA
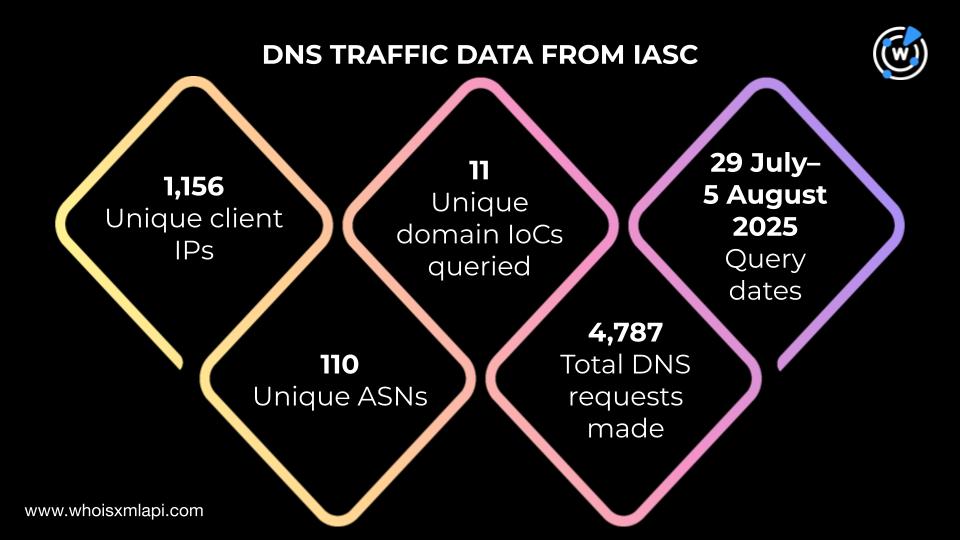
Guardio uncovered ClickFix, a browser-based stealer that used fake CAPTCHA pages to trick users into executing a malicious PowerShell command and exfiltrate credentials, and published 172 IoCs including 156 domains and 16 IPs. WhoisXML API’s analysis expanded those IoCs—finding thousands of related domains, IPs, registrant- and email-linked domains, and early warnings for 30 domains—and linked broad DNS and WHOIS artifacts to the campaign. #ClickFix #Guardio

Linux kernel 6.9 replaced the old sys_call_table direct dispatch with a switch-statement-based dispatcher, rendering traditional syscall hooking ineffective. The FlipSwitch technique bypasses this by locating the unique call instruction in x64_sys_call that targets an original syscall (e.g., sys_kill), disabling write protection, and patching the call offset to redirect execution to a malicious handler before restoring changes on unload. #FlipSwitch #x64_sys_call
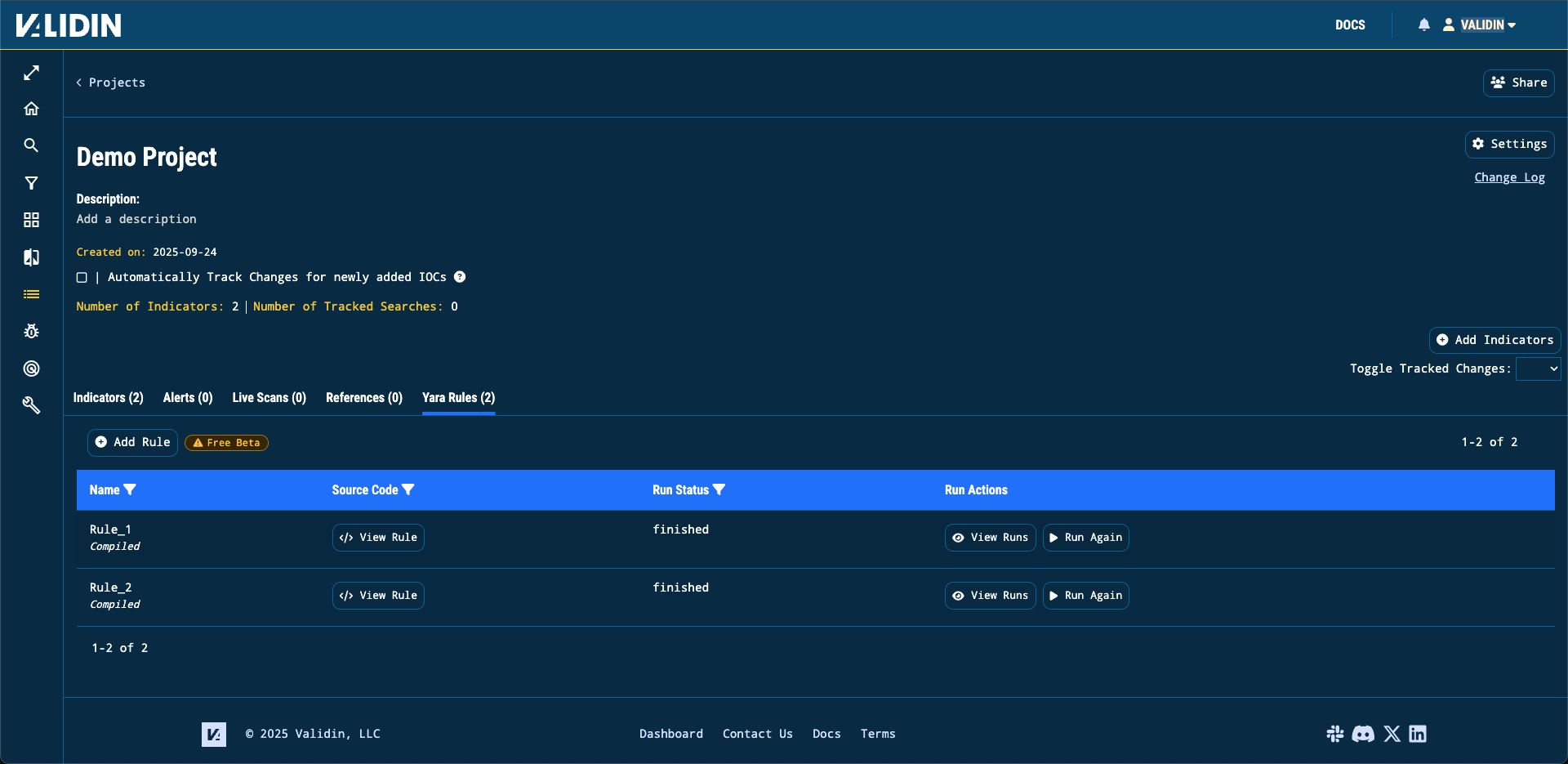
Validin added YARA retro hunting across its large archive of virtual host responses, allowing enterprise users to write, run, and view matches from custom YARA rules to discover and track indicators in historical web artifacts. A demonstrated use case found over 5,000 exposed OpenAI API keys in one week by searching for the OpenAI key substring. #Validin #OpenAI_api_keys

MatrixPDF is a toolkit that transforms legitimate PDF files into interactive phishing and malware delivery tools by adding overlays, clickable prompts, and embedded JavaScript that redirect victims to attacker-controlled payloads. The toolkit exploits email PDF preview behavior and PDF scripting (e.g., app.launchURL) to bypass scanning and initiate downloads, often using short…
A Lunar Spider-linked Latrodectus JavaScript dropper (masquerading as a tax form) installed an MSI that deployed Brute Ratel, which in turn injected Latrodectus and enabled BackConnect VNC, leading to extensive discovery, credential theft (including from an unattend.xml and LSASS), lateral movement with Cobalt Strike, and data exfiltration via Rclone/FTP. The intrusion persisted nearly two months, leveraged tools like Zerologon exploits, Metasploit, and a custom .NET backdoor (lsassa.exe), and used domains/IPs such as workspacin.cloud, cloudmeri.com, and 45.129.199.214. #Latrodectus #BruteRatel #CobaltStrike #Rclone #cloudmeri.com
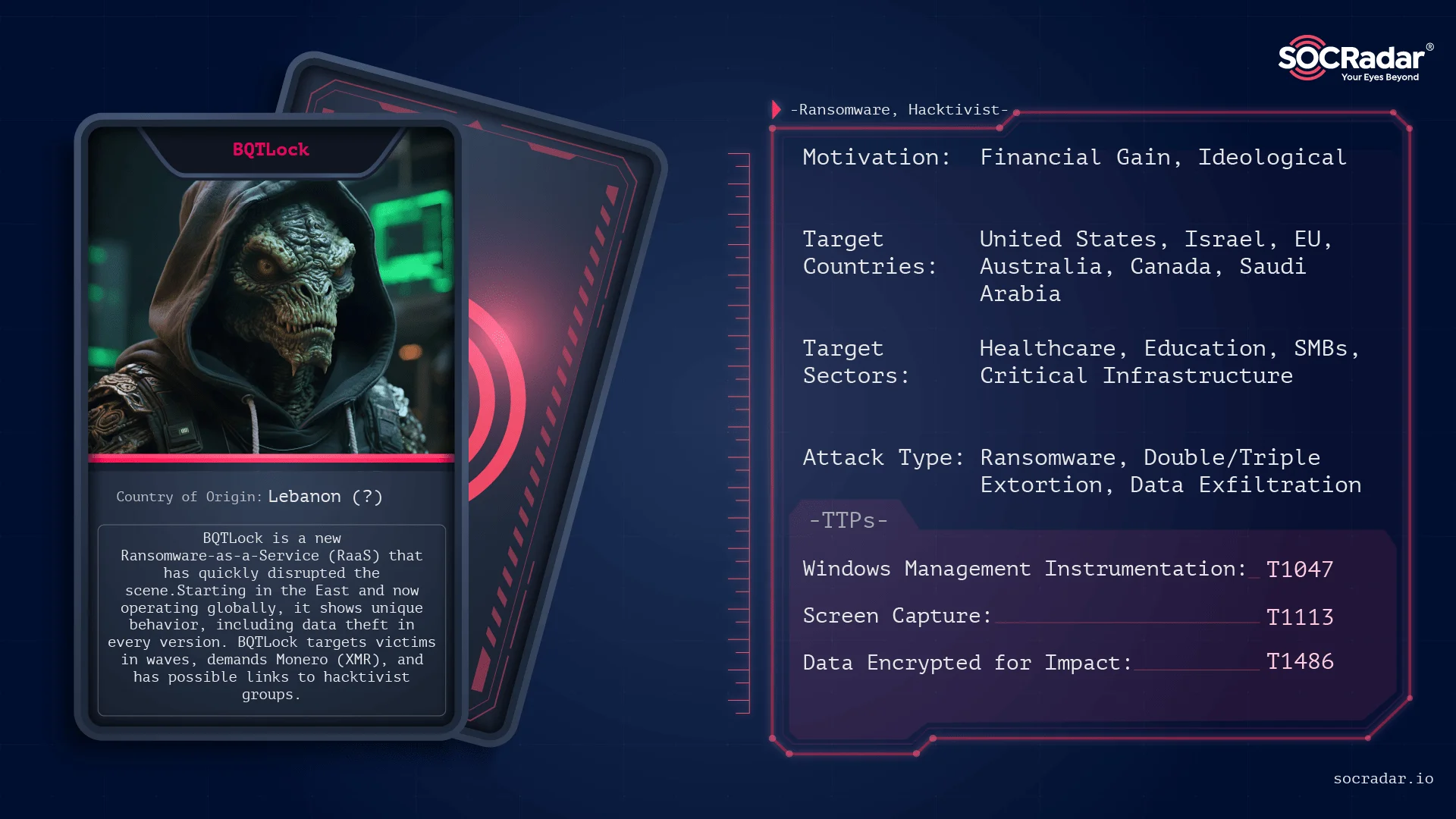
BQTLock is a rapidly evolving Ransomware-as-a-Service (RaaS) operation emerging from the Middle East that combines aggressive extortion, wave-based decryption pricing, and political propaganda to attract affiliates and victims worldwide. The group is led by Karim Fayad (aka ZeroDayX) with ties to pro-Palestinian hacktivist groups like Liwaa Mohammed and uses techniques such as AES-256/RSA-4096 encryption, process hollowing, UAC bypass, and C2 communication over Telegram/Discord. #BQTLock #ZeroDayX

Goffee conducts stealthy, long-term intrusion campaigns primarily against Russian organizations, using a mix of older tools (owowa, PowerTaskel) and newly discovered later-stage tools (DQuic, MiRat, BindSycler, Sauropsida rootkit) to maintain persistence and minimize visibility. The group favors Russian IP addresses and hosting providers to blend with internal traffic and deliver/tunnel malware, enabling confident attribution through consistent packaging, network profile, and encrypted traffic patterns. #Goffee #DQuic

Bad actors are using AI, vibe coding tools, SEO poisoning, and malvertising to spin up near‑perfect clones of the FBI’s IC3 site and other spoofed pages, tricking users into submitting sensitive reports and PII. Security teams are urged to combine domain/link analysis, computer vision, phishing sandboxes, and advanced browser protections to…

FortiGuard Labs observed a phishing campaign impersonating Ukrainian government agencies that used malicious SVG attachments to deliver a CHM → HTA loader (CountLoader) which fetched and executed fileless payloads Amatera Stealer and PureMiner. The campaign enabled data exfiltration (credentials, browser and wallet files, system info) and resource hijacking for cryptomining via techniques like process hollowing, .NET AOT execution, and in-memory Python loading. #Amatera #PureMiner
Bitdefender researchers tracked a global malvertising campaign that impersonated TradingView across Facebook, YouTube, and Google Ads to deliver a large multi-stage downloader and stealer (detected as Variant.DenoSnoop.Marte.1 and Trojan.Agent.GOSL) that hijacks accounts, steals credentials and crypto data, and persists via scheduled tasks and Defender exclusions. The campaign used hijacked Google advertiser…
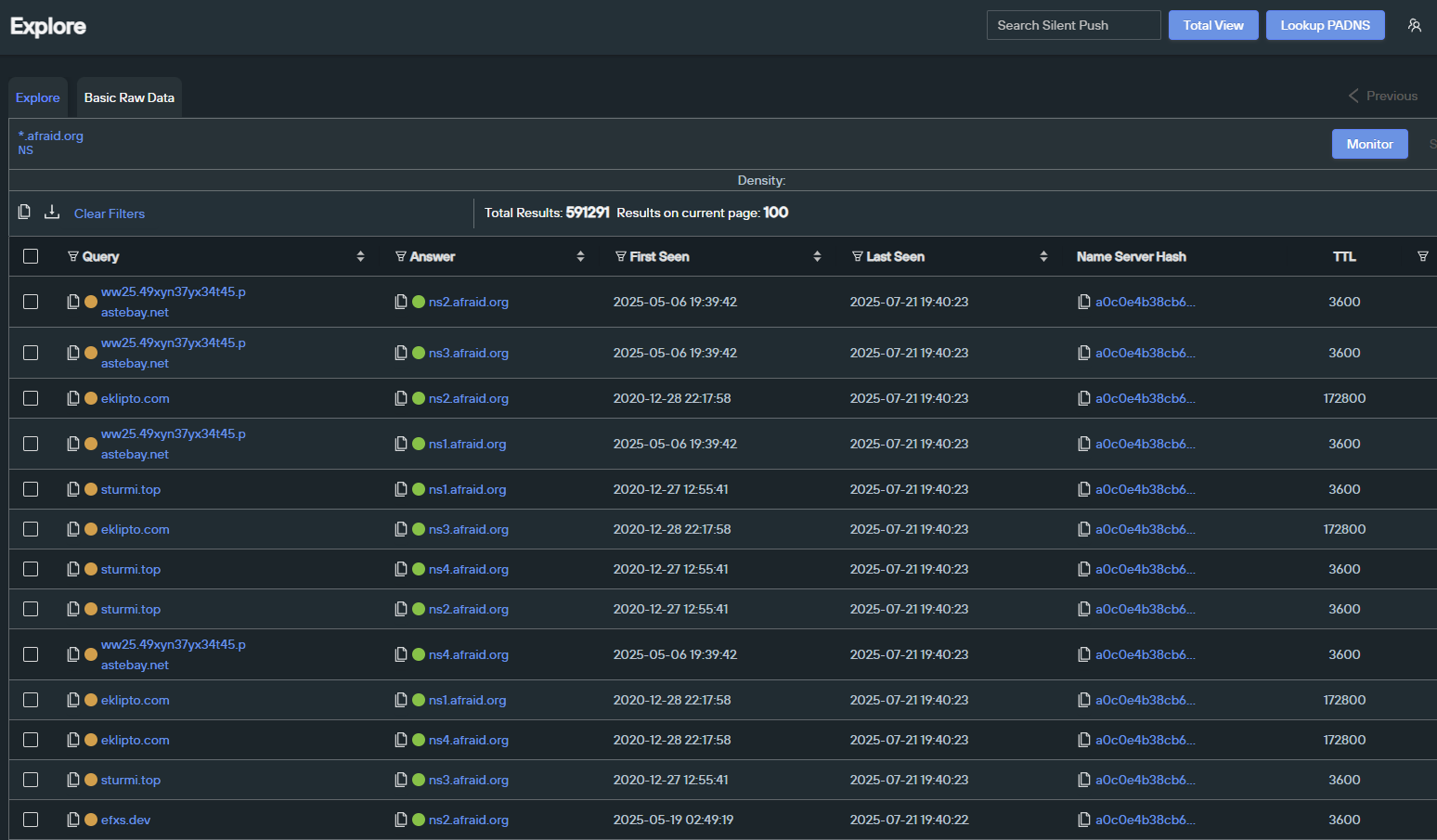
Silent Push researched and compiled exports tracking ~70,000 domains that rent subdomains (Dynamic DNS providers), highlighting how these services are frequently abused by threat actors and can evade takedown efforts. The report urges enterprises to monitor or block connections to such providers and mentions specific providers like afraid[.]org and AttractSoft. #afraid_org…