Silent Push researched and compiled exports tracking ~70,000 domains that rent subdomains (Dynamic DNS providers), highlighting how these services are frequently abused by threat actors and can evade takedown efforts. The report urges enterprises to monitor or block connections to such providers and mentions specific providers like afraid[.]org and AttractSoft. #afraid_org #AttractSoft
Keypoints
- Silent Push created exclusive data exports to track roughly 70,000 domains that rent subdomains (Dynamic DNS providers) for enterprise monitoring and mitigation.
- Publicly rentable subdomain services are often low-regulation, accept anonymous payments, and can operate like mini-registrars with little oversight, making them attractive to threat actors.
- Dynamic DNS providers vary in capability: some allow full hosting and DNS control (e.g., afraid[.]org on paid plans), while others restrict DNS or content control.
- Many such providers ignore abuse/takedown requests and are not fully represented on the Public Suffix List, complicating tracking and remediation efforts.
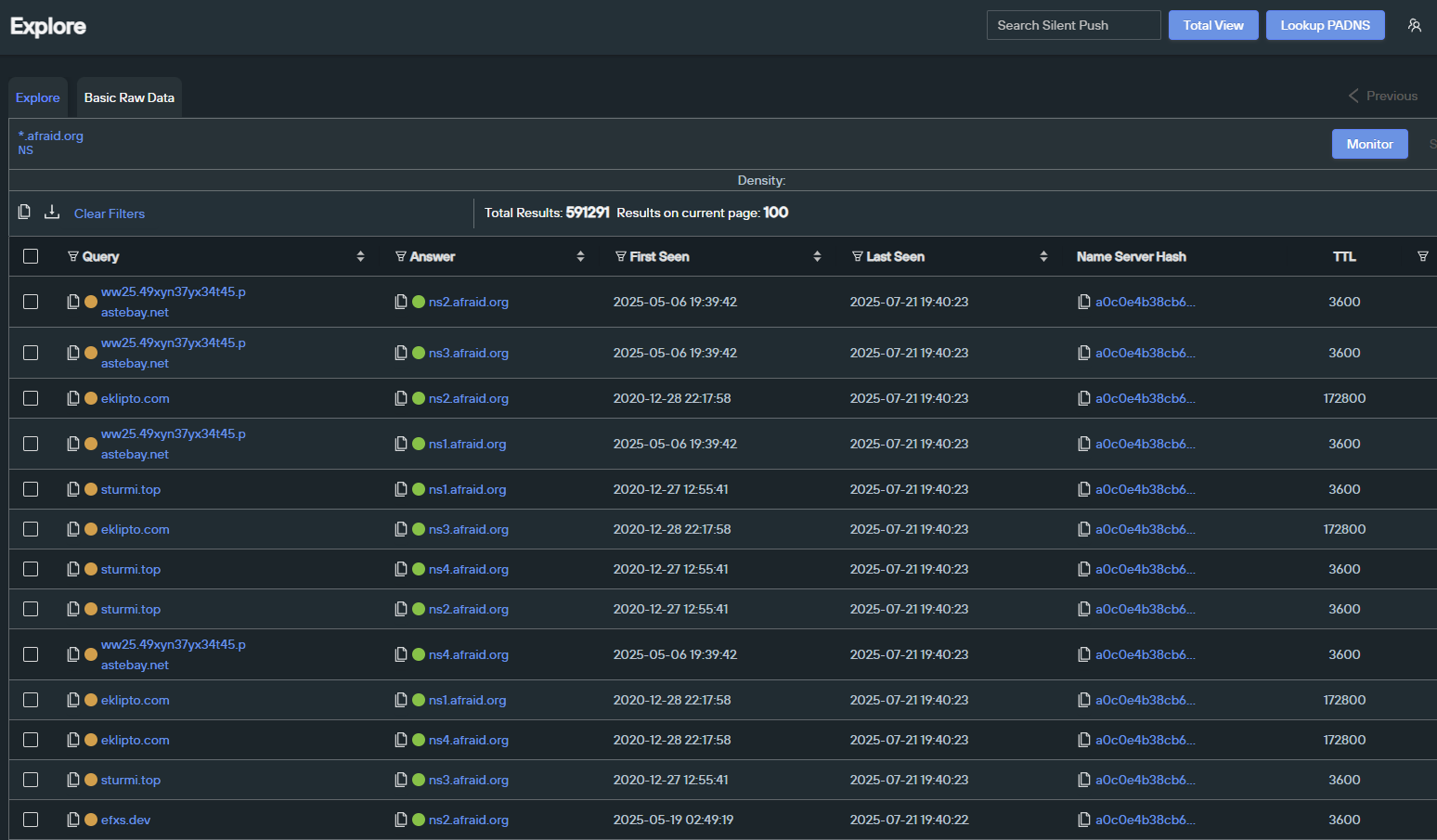
- Silent Push aggregates multiple data sources (PSL, scraped afraid[.]org listings, NS/PADNS lookups, and other DDNS providers) to build a comprehensive monitoring feed for enterprises.
- High-profile abuse of these services by threat actors is documented; Silent Push is tracking specific providers and created fingerprints (e.g., for AttractSoft) for customers.
- Enterprises are advised to set alerts or block connections to subdomains of tracked providers and ingest Silent Push IOFA™ feeds to improve detection and response.
MITRE Techniques
- [T1071 ] Application Layer Protocol – Used for command and control communications via subdomains on Dynamic DNS providers: ‘infrastructure becomes highly attractive for use as part of command and control (C2) communications and other dangerous network flows.’
- [T1591 ] Gather Victim Identity Information – Threat actors exploit lax registration and anonymous purchase flows to obtain infrastructure without identity verification: ‘many of these providers accept cryptocurrency payment methods… and never need to share credentials or provide “Know Your Customer” details.’
- [T1602 ] Data from Network Shared Drive (or alternate exfiltration) – Attackers leverage hosted content on rented subdomains to stage payloads or exfiltration endpoints: ‘allow anyone—malicious or otherwise—to register subdomains and host their own content on them.’
- [T1584 ] Compromise Infrastructure – Threat actors rent subdomains or use Dynamic DNS services to host malicious payloads and maintain persistence: ‘these services are effectively operating as “mini domain registrars” … allowing them to operate with far less red tape and regulation.’
- [T1588 ] Obtain Capabilities – Use of third-party Dynamic DNS providers to procure infrastructure and avoid takedown: ‘Many Dynamic DNS platforms… have abuse reporting channels; however, no organizations publicly track the takedown response times…’
Indicators of Compromise
- [Domain ] dynamic DNS providers used for hosting/malicious activity – afraid[.]org, attractsoft (AttractSoft) and mentions of changeip[.]com, duckdns[.]org
- [Domain ] enterprise/PSL-listed subdomain hosts – pages[.]dev, blogspot[.]com
- [DNS Records / NameServer ] stealth/NS-tracked subdomains – NameServer records for afraid[.]org produced many results (example: over 591,000 NS results) and “stealth” domains tracked via NS lookups
- [Service/Fingerprint ] provider-specific tracking context – AttractSoft fingerprint used in attacks targeting Ukraine (customer-only fingerprint available)