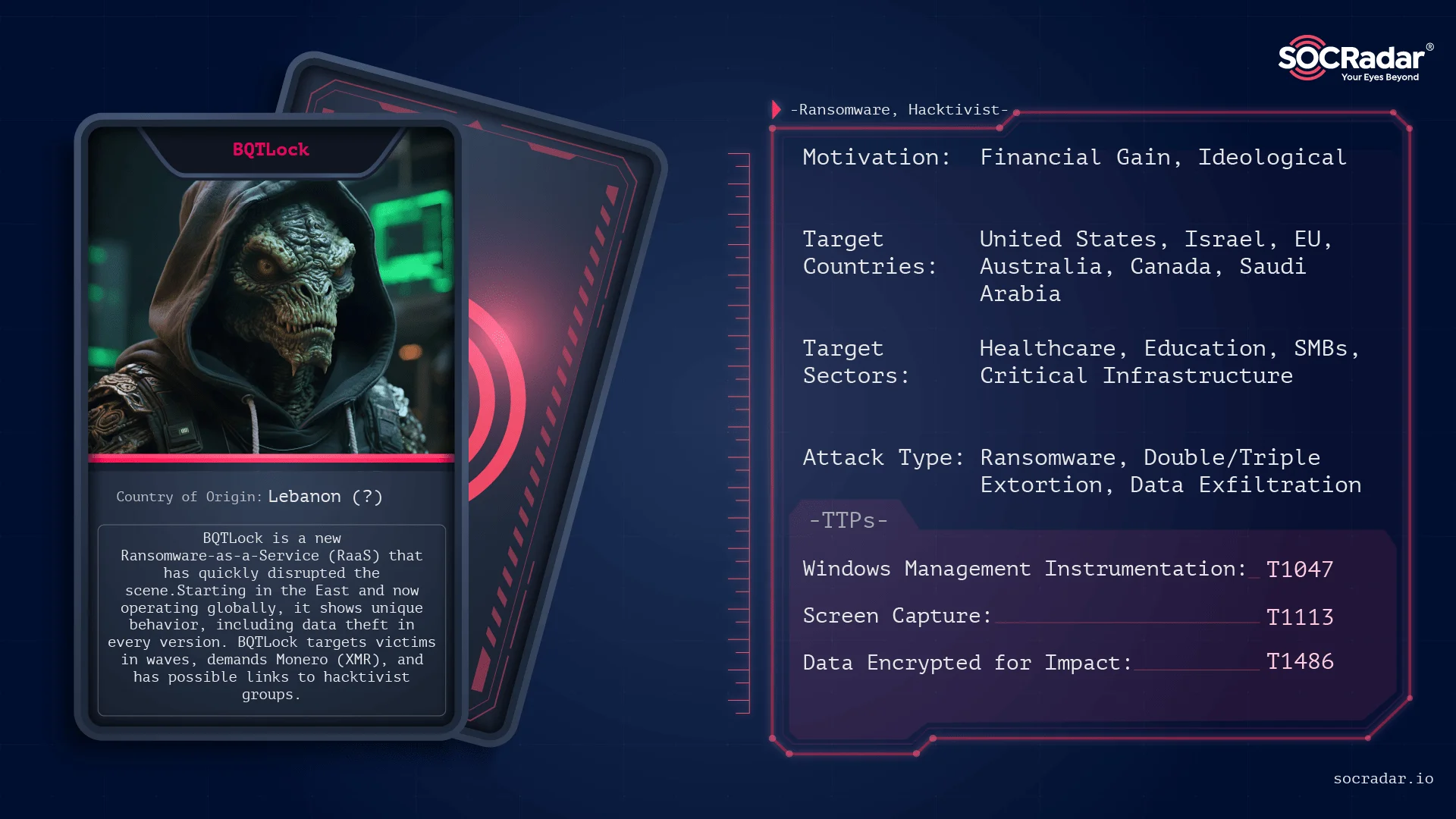
BQTLock is a rapidly evolving Ransomware-as-a-Service (RaaS) operation emerging from the Middle East that combines aggressive extortion, wave-based decryption pricing, and political propaganda to attract affiliates and victims worldwide. The group is led by Karim Fayad (aka ZeroDayX) with ties to pro-Palestinian hacktivist groups like Liwaa Mohammed and uses techniques such as AES-256/RSA-4096 encryption, process hollowing, UAC bypass, and C2 communication over Telegram/Discord. #BQTLock #ZeroDayX
Keypoints
- BQTLock is a RaaS run by a core team (notably Karim Fayad aka ZeroDayX and Fuch0u) that mixes financial motives with pro-Palestinian propaganda and recruits affiliates via Telegram and other social platforms.
- The group conducts wave-based campaigns with tiered decryption pricing (paid primarily in Monero), psychological pressure tactics (price doubling after 48 hours), and public data leak sites for extortion.
- Confirmed victims include a USA military alumni network, eFunda, Inc., and a European business server cluster with ransom demands totaling hundreds to thousands of XMR.
- Technical capabilities include Windows and Linux builders, multi-threaded encryption using OpenSSL (AES-256 + RSA-4096), bundled libraries for portability, and features like process termination, persistence, anti-VM/debug, UAC bypass, process hollowing, and data theft.
- Attack chain highlights: likely initial access via RDP/exposed services or phishing ZIPs, discovery and profiling of hosts, privilege escalation (admin account creation and UAC bypass), C2 registration (IPs and Telegram/Discord fallback), exfiltration (Discord/Telegram), and system-wide encryption with backup deletion.
- Operational artifacts include scheduled tasks for persistence, usage of legitimate services (e.g., icanhazip[.]com) for reconnaissance, and public demonstrations of a decryptor to advertise capabilities to affiliates.
- Detection and mitigation guidance emphasizes monitoring for suspicious account creation, use of vssadmin/bcdedit/schtasks, outbound Telegram/Discord traffic, isolating infected hosts, forensic collection, blocking known C2 addresses, and maintaining segmented immutable backups.
MITRE Techniques
- [T1047 ] Windows Management Instrumentation – Remote execution and deletion of shadow copies using WMI (example: “Remote execution of the binary, as well as deletion of ShadowCopies by abusing WMI (process call create)”)
- [T1055.012 ] Process Hollowing – Injects and runs code in explorer.exe via CreateProcess (suspended) + WriteProcessMemory + SetThreadContext + ResumeThread to evade detection (“Process hollowing”)
- [T1053 ] Scheduled Task/Job – Persistence via schtasks creating tasks named like SystemHealthCheck or BQTLock_Startup_[ID] to run malware on logon (“schtasks /create /tn “” /tr “” /sc ONLOGON /rl HIGHEST /f”)
- [T1136.001 ] Create Account: Local Account – Creates new administrator accounts (e.g., BQTLockAdmin or Guest_[ID]) to retain elevated access (“Create a new admin user”)
- [T1548.002 ] Bypass User Account Control – UAC bypass using CMSTP on Windows 11, fodhelper on Windows 10, or eventvwr on Windows 7/8 to auto-elevate payloads (“UAC abuse to execute legitimate binaries (CMSTP, fodhelper, & eventvwr)”)
- [T1112 ] Modify Registry – Alters registry keys for persistence and UAC bypass (e.g., HKCU SoftwareClasses modifications to hijack auto-elevation mechanisms) (“Modification of the registry”)
- [T1562.001 ] Impair Defenses: Disable Tools – Kills security and monitoring processes (e.g., Sysmon) to impair defenses (“Kill security processes (e.g., Sysmon)”)
- [T1070.004 ] File Deletion – Deletes files and originals (cmd.exe /C timeout /t 3 /nobreak > NUL & del /f /q “”) and removes shadow copies (vssadmin/wmic) to inhibit recovery (“Auto-delete file …”)
- [T1078 ] Valid Accounts – Checks and leverages administrative privileges and created local accounts for further operations (“Check admin privileges”)
- [T1555.003 ] Credentials from Web Browsers – Extracts saved browser credentials and stores them for exfiltration (“Collect saved passwords from browsers”)
- [T1074 ] Data Staged – Writes stolen credentials and data to temp files (e.g., C:WindowsTemp_passwords.txt) before exfiltration (“Saved passwords written to C:WindowsTemp_passwords.txt”)
- [T1082 ] System Information Discovery – Gathers OS details, hostname, BIOS and motherboard serials, disk sizes and free space to profile victims (“System information discovery”)
- [T1622 ] Debugger Evasion – Detects debugging environments using IsDebuggerPresent and CheckRemoteDebuggerPresent to alter behavior and hinder analysis (“Anti-debug checks”)
- [T1113 ] Screen Capture – Takes screenshots of the victim desktop and saves them (e.g., bqt_screenshot in Windows Temp) for exfiltration or evidence (“Take screenshots”)
- [T1071.001 ] Application Layer Protocol: Web – Uses HTTP/HTTPS (WinInet) and common platforms for C2 and reconnaissance (e.g., icanhazip[.]com to get public IP) (“Get public IP via WinInet”)
- [T1041 ] Exfiltration Over C2 Channel – Exfiltrates stolen data to C2 or platforms like Discord and Telegram webhooks (“Extract info collected to C2”)
- [T1486 ] Data Encrypted for Impact – Performs file encryption across disks using AES-256 per-file with RSA-4096-wrapped keys to render data inaccessible (“File encryption”)
- [T1490 ] Inhibit System Recovery – Deletes backups and disables recovery using vssadmin, wmic, and bcdedit to prevent restoration (“Delete backups (VSS, Shadow Copies, Volume Snapshots)”)
Indicators of Compromise
- [File Hash ] malware sample hashes – 425b2f283b71237276f84d941d9c2982c7f61a9aff12ece10e15065b73b7165e, b211537ea626fae4ad2ef5ee2652633dc68aaf20da6eb953a44f266c4106b367 (and many more hashes listed)
- [IP Address ] C2 servers – 92[.]113[.]146[.]56, 208[.]99[.]44[.]55 (observed as command-and-control endpoints)
- [Domain ] payment/exfiltration infrastructure – bcoins[.]online (associated service/wallet/payment infrastructure)
- [Onion Domain ] ransom site – yywhylvqeqynzik6ibocb53o2nat7lmzn5ynjpar3stndzcgmy6dkgid.onion (ransom onion site)
- [Telegram/X ] threat actor social channels – https://t.me/BQTlock_raas, https://t.me/Fuch0u, https://t.me/liwaamohammad, https://t.me/BQTlock, https://x.com/zerodayx1 (used for propaganda, affiliate liaison, and victim listings)
- [Email ] extortion contact – [email protected] (ransom/communication email in victim notes)
- [Wallet ] Monero payment address – 89RQN2EUmiX6vL7nTv3viqUAgbDpN4ab329zPCEgbceQJuS233uye4eXtYk3MXAtVoKNMmzgVrxXphLZbJPtearY7QVuApr (example payment wallet)
Read more: https://socradar.io/dark-web-profile-bqtlock-ransomware/