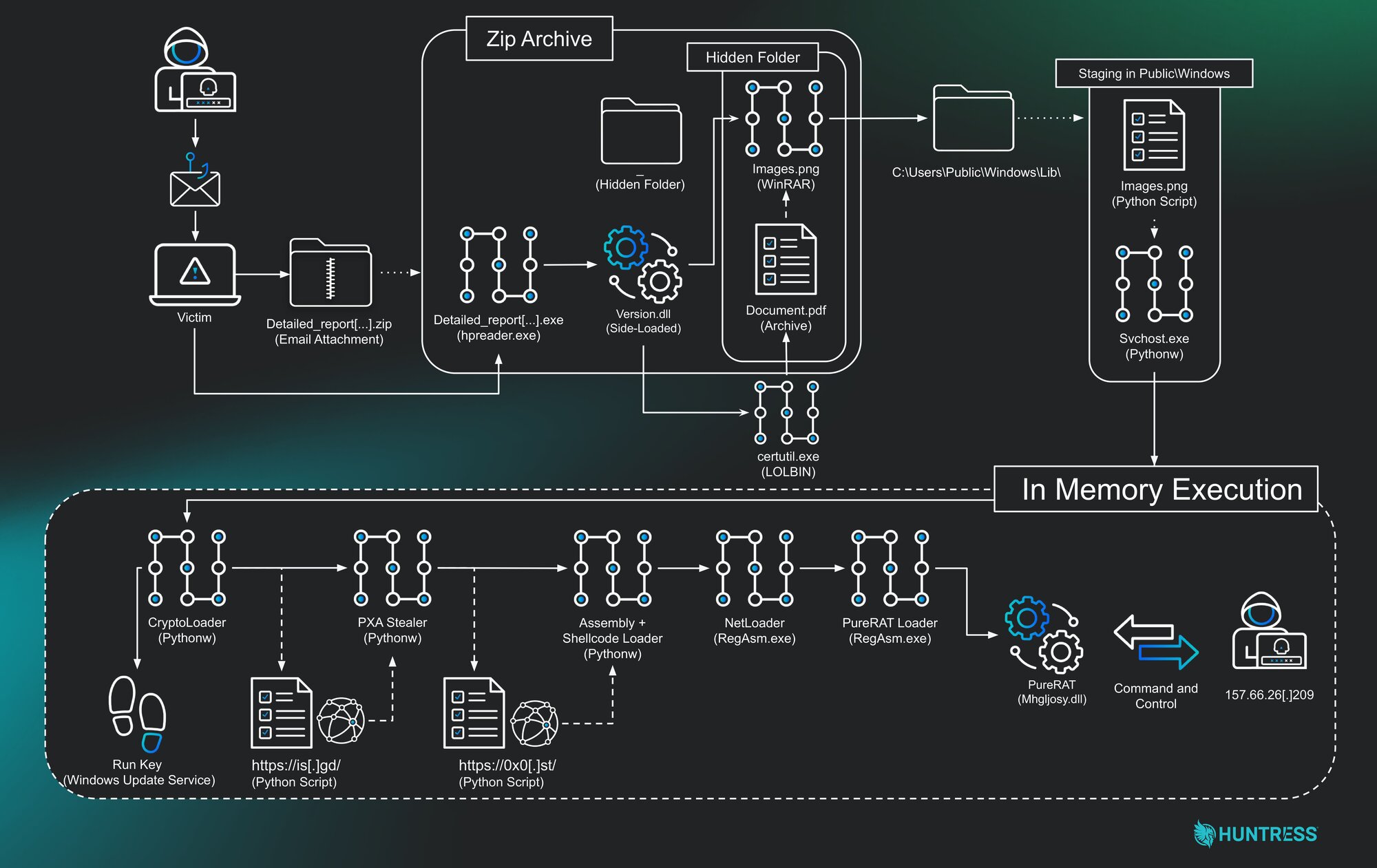
A multilayered intrusion began with a phishing ZIP that sideloaded a malicious DLL and progressed through multiple in-memory Python loaders and a .NET process-hollowing stage, ultimately delivering the commercial PureRAT backdoor. The campaign used Telegram-based exfiltration and hosted payloads on URL shorteners and file hosting services, with C2 infrastructure tied to IP 157.66.26.209 and attribution clues linking to @LoneNone and the PXA actor. #PureRAT #PXA #LoneNone #157.66.26.209
Keypoints
- Initial access via spearphishing: a ZIP archive containing a signed PDF reader executable and a malicious version.dll enabling DLL sideloading.
- Multi-stage, in-memory Python loaders used heavy obfuscation (Base85/Base64/RC4/AES/XOR) and registry Run key persistence disguised as “Windows Update Service”.
- Stage 2 deployed a Python-based information stealer that collected browser credentials, cookies, credit cards and exfiltrated data via the Telegram Bot API; metadata referenced Telegram handle @LoneNone.
- Stage 3 pivoted to .NET, using a hosted 3 MB payload that performed RC4/base64 decryption and process hollowing of RegAsm.exe to load additional .NET payloads in-memory.
- The .NET loader patched AMSI and unhooked ETW for defense evasion and used reflective loading to deliver a final DLL (Mhgljosy.dll) which was deobfuscated to reveal PureRAT.
- PureRAT used Base64→GZip→Protobuf to store its config, contained TLS pinning with an embedded X.509 cert, and connected to C2 at 157.66.26.209 on ports 56001–56003.
- Evidence (Telegram metadata, code strings referencing PureHVNC and PureCoder) links the campaign to the PXA actor and demonstrates use of commodity malware to scale capabilities.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – The campaign begins with a phishing email containing a malicious ZIP archive (“The campaign begins with a phishing email containing a malicious ZIP archive.”).
- [T1204.002 ] User Execution: Malicious File – The user is tricked into executing an .exe disguised as a document (“The user is tricked into executing an .exe file disguised as a document.”).
- [T1059.006 ] Python – Stages 1 and 2 executed via a renamed Python interpreter (“Stages 1 and 2 are executed via a renamed Python interpreter.”).
- [T1547.001 ] Registry Run Keys / Startup Folder – Persistence created by adding a Run key labeled Windows Update Service (“payload 4 establishes persistence by creating a ‘Windows Update Service’ Run key.”).
- [T1574.001 ] DLL Side-Loading – A legitimate PDF reader executable loads a malicious version.dll from the same directory (“A legitimate PDF reader executable is used to load a malicious version.dll.”).
- [T1027 ] Obfuscated Files or Information – Multiple stages use Base85, Base64, RC4, AES, and XOR to hide payloads (“Multiple stages use Base85, Base64, RC4, AES, and XOR to hide payloads.”).
- [T1055.012 ] Process Hollowing – Loader injects a .NET payload into suspended RegAsm.exe and resumes it (“The payload 7 .NET loader is injected into a suspended RegAsm.exe process.”).
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – Payload 7 patches AMSI to prevent runtime inspection (“It patches the AmsiScanBuffer function in amsi.dll to prevent the Antimalware Scan Interface from inspecting dynamically loaded code.”).
- [T1562.006 ] Impair Defenses: Indicator Blocking – Payload 7 unhooks ETW to blind Event Tracing for Windows (“It patches EtwEventWrite in ntdll.dll to blind Event Tracing for Windows, a common source of telemetry for EDR products.”).
- [T1082 ] System Information Discovery – PureRAT enumerates OS version, architecture, and privileges during fingerprinting (“PureRAT fingerprints the OS version, architecture, and user privileges.”).
- [T1518.001 ] Security Software Discovery – The malware queries WMI for installed antivirus product names (“Queries WMI (rootSecurityCenter) for the displayName of all installed antivirus products.”).
- [T1560.001 ] Archive Collected Data: Archive via Utility – Stolen data is compressed into a ZIP before exfiltration (“Stolen data is compressed into a ZIP archive before exfiltration.”).
- [T1071.001 ] Web Protocols – Stage 2 exfiltrates data via HTTP POST to the Telegram API (“The stage 2 stealer exfiltrates data via HTTP POST requests to the Telegram API.”).
- [T1573.002 ] Encrypted Channel: Asymmetric Cryptography – PureRAT uses TLS with pinned X.509 certificate for C2 communications (“PureRAT uses TLS with a pinned X.509 certificate for C2 communications.”).
Indicators of Compromise
- [File Hash ] Payloads on disk/memory – e0e724c40dd350c67f9840d29fdb54282f1b24471c5d6abb1dca3584d8bacaa (Payload 9 PureRAT), 06fc70aa08756a752546198ceb9770068a2776c5b898e5ff24af9ed4a823fd9d (Payload 8 loader).
- [File Hash ] Loader artifacts – f5e9e24886ec4c60f45690a0e34bae71d8a38d1c35eb04d02148cdb650dd2601 (Payload 7 loader), f6ed084aaa8ecf1b1e20dfa859e8f34c4c18b7ad7ac14dc189bc1fc4be1bd709 (obfuscated Python script images.png).
- [File Path ] Renamed Python interpreter and script – C:UsersPublicWindowssvchost.exe (renamed Python), C:UsersPublicWindowsLibimages.png (obfuscated Python script).
- [Registry ] Persistence – HKCUSOFTWAREMicrosoftWindowsCurrentVersionRunWindows Update Service (Run key that re-executes svchost.exe and images.png).
- [IP Address ] C2 server – 157.66.26.209 (PureRAT command-and-control server located in Vietnam).
- [Ports ] C2 ports – 56001, 56002, 56003 (PureRAT C2 listening ports).
- [URL ] Payload hosting – https://0x0.st/8WBr.py (stage 3 payload host), https://is[.]gd/s5xknuj2 and https://paste[.]rs/fVmzS (stage 2 payload hosts).
- [Account ] Threat actor handle – @LoneNone (Telegram handle found in stealer ZIP metadata linked to PXA Stealer).
Read more: https://www.huntress.com/blog/purerat-threat-actor-evolution