Trend Research analyzed LockBit 5.0 source binaries and confirmed Windows, Linux, and ESXi variants that use heavy obfuscation, in-memory DLL reflection loading, anti-analysis/anti-forensics (ETW patching, service termination, event log clearing), randomized 16-character file extensions, and Russian-language/geolocation avoidance. The ESXi variant targets VMware virtualization to encrypt multiple VMs at once while Linux and Windows variants share command-line interfaces and features for targeted, configurable encryption. #LockBit5.0 #ESXi
Keypoints
- Trend Research recovered and analyzed LockBit 5.0 binaries and confirmed distinct Windows, Linux, and ESXi variants, indicating continued cross-platform capability.
- Windows variant uses heavy obfuscation/packing and acts as a loader that decrypts a PE in memory and loads it via DLL reflection, complicating static analysis.
- All variants implement anti-analysis and anti-forensics techniques including ETW patching (overwriting EtwEventWrite), terminating security services by hashed names, and clearing event logs via EvtClearLog.
- Ransomware appends randomized 16-character extensions to encrypted files and embeds original file size in encrypted file footer; it omits typical infection markers at file endings.
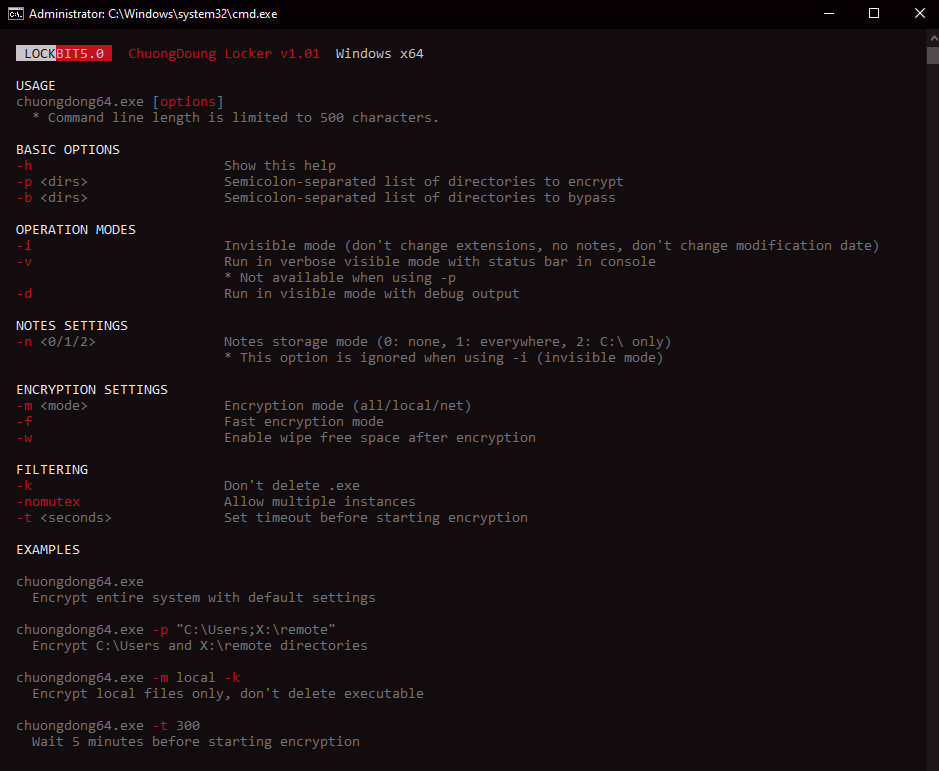
- Command-line interfaces across Windows, Linux, and ESXi provide extensive options (target/bypass directories, modes like invisible/verbose, filtering, and encryption scopes) giving attackers flexible operation.
- ESXi-specific variant targets VMware virtualization hosts to maximize impact by encrypting multiple virtual machines from a single host compromise.
- LockBit 5.0 reuses core code elements from LockBit 4.0 (identical hashing algorithms and dynamic API resolution), indicating evolutionary development rather than a new actor or imitation.
MITRE Techniques
- [T1082] System Information Discovery – The malware checks system language and geolocation and terminates if Russian language/geolocation is detected (“This code terminates if the language is Russian” / “This code terminates if the geolocation is Russia”).
- [T1055] Process Injection – Windows sample functions as a binary loader decrypting a PE in memory and loading it via DLL reflection (“decrypting a PE binary in memory and loading it via DLL reflection methods”).
- [T1218] System Binary Proxy Execution – Use of DLL reflection to load payloads in-memory acts as a living-off-the-land style technique to execute code without writing a persistent drop (“loads its payload through DLL reflection while implementing anti-analysis techniques”).
- [T1562.001] Impair Defenses: Disable or Modify Event Logs – The malware patches EtwEventWrite to immediately return and calls EvtClearLog to erase event logs (“overwriting it with a 0xC3 (return) instruction” and “clears all event logs using the EvtClearLog API”).
- [T1489] Impact: Service Stop – The ransomware terminates security-related services by hashing service names and comparing them to a hardcoded list, then stopping matching services (“terminates security-related services by comparing hashed service names against a hardcoded list of 63 values”).
- [T1486] Data Encrypted for Impact – The variants encrypt files and append randomized 16-character extensions to encrypted files to prevent recovery (“encryption process appends randomized 16-character extensions to files”).
- [T1083] File and Directory Discovery – Command-line options and logging reveal enumeration and selection of directories/files to include or exclude from encryption (“detailed logging of its activities, displaying files targeted for encryption and folders designated for exclusion”).
Indicators of Compromise
- [File Extension] Encrypted file marker – randomized 16-character hexadecimal-like extensions appended to encrypted files (example pattern: .[a-f0-9]{16}); hunting query: objectFilePath: /.[a-f0-9]{16}$/
- [File Name] Ransom note – standard ransom note filename ReadMeForDecrypt.txt referenced in detections and hunting queries (example: ReadMeForDecrypt.txt)
- [API/Function Behavior] Anti-forensics indicators – ETW patching and use of EvtClearLog observed in samples (context: EtwEventWrite overwritten with 0xC3; EvtClearLog called to clear logs)
- [Service Hashes] Hardcoded hashed service identifiers – list of hashed service name values used to identify and terminate security services (examples: FEF56F15, BEC3470B, 9757464D, and many others)
- [Command-line Options] CLI parameters used by samples – examples of options observed: -h (help), -d (directories to encrypt), -b (bypass directories), -i (invisible mode), -n (note storage mode)
Read more: https://www.trendmicro.com/en_us/research/25/i/lockbit-5-targets-windows-linux-esxi.html