XWorm is a modular, builder-driven .NET Remote Access Trojan (RAT) sold as malware-as-a-service that enables operators to assemble bespoke payloads with features like keylogging, clipper, screen capture, credential theft, persistence, and optional ransomware modules. Campaigns use diverse delivery chains (LNK/HTA/VBS/PowerShell, steganography, TryCloudflare tunnels, ClickFix clipboard lures) and have been used by groups including Nullbulge, UAC-0184, TA558, and Kimsuky to scale infections rapidly. #XWorm #TA558 #Kimsuky
Category: Threat Research

Ransomware actors are increasingly targeting cloud control planes by using compromised AWS programmatic keys and tools like Pacu to enumerate, escalate, and exfiltrate data from cloud accounts. Rapid detection and response — including disabling keys, auditing activity, and monitoring cloud control plane telemetry — prevented greater impact in the investigated incident….
.png)
Cofense Intelligence tracked Lone None campaigns delivering Pure Logs Stealer and a new Lone None Stealer that use copyright-takedown email lures, Telegram bot profile pages for payload delivery, and obfuscated Python-based payloads to steal cryptocurrency via clipboard replacement. The campaign abuses legitimate programs (Haihaisoft PDF Reader, certutil.exe, WinRAR), installs a staged Python interpreter in C:UsersPublicWindows (svchost.exe), and reports clipboard replacements to a Telegram bot C2. #LoneNoneStealer #PureLogsStealer #TelegramBot
Indirect prompt injection abuses external data sources (emails, documents, web pages, API responses, images) by embedding hidden instructions that MCP-powered LLMs can execute, leading to stealthy data exfiltration or unauthorized actions. RUG Pull attacks replace trusted MCP tools via compromised registries or updates, turning vetted automations into backdoors. #RUGPull #ModelContextProtocol

Jaguar Land Rover experienced a major cyber incident on September 2, 2025, that disrupted global IT systems and halted manufacturing and retail operations, with leaked internal data and screenshots posted by a Telegram channel claiming ties to Scattered Spider, Lapsus$, and ShinyHunters. Earlier HELLCAT activity using Infostealer-harvested Jira credentials and subsequent data dumps increased risk of credential theft, IP exposure, and targeted follow-on attacks. #HELLCAT #ShinyHunters

RedNovember (formerly TAG-100) is a Chinese state‑sponsored threat activity group that has conducted widespread reconnaissance and likely compromises of internet‑facing edge devices and services worldwide using open‑source tools such as the Go-based backdoor Pantegana, LESLIELOADER to load SparkRAT and Cobalt Strike, and targeted appliances like SonicWall, Fortinet, Palo Alto GlobalProtect, Ivanti Connect Secure, and Check Point VPNs. The group expanded targeting across government, intergovernmental, defense, aerospace, law firms, media, and technology sectors between June 2024 and July 2025 and has leveraged published proof‑of‑concept exploits and spearphishing lures to lower the bar for large‑scale intrusions. #Pantegana #LESLIELOADER
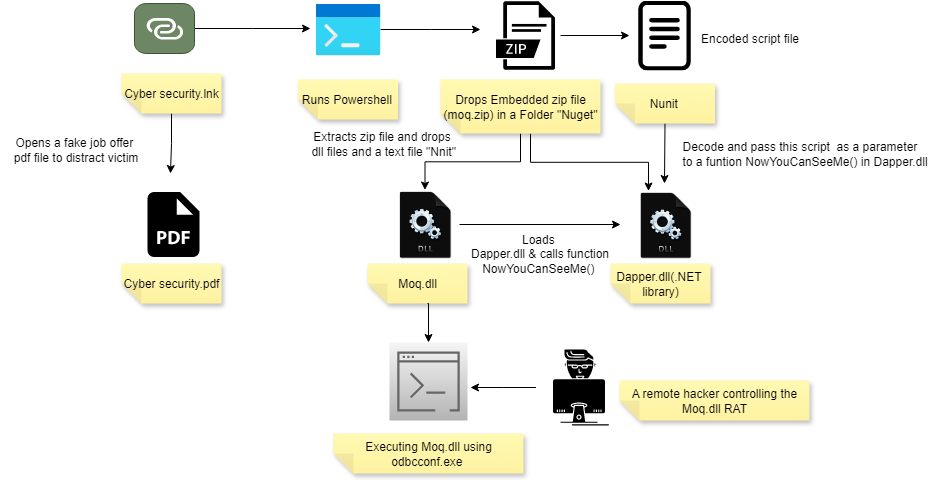
A Windows shortcut (.LNK) distributed via Discord drops a ZIP containing a malicious DLL (Moq.dll) that is executed using the legitimate binary odbcconf.exe, enabling a multi-functional RAT to run stealthily. The RAT disables AMSI and ETW, collects system and antivirus info, captures screenshots, persists via Winlogon Shell modification, and communicates with C2 servers such as hotchichenfly.info. #Moq.dll #odbcconf.exe
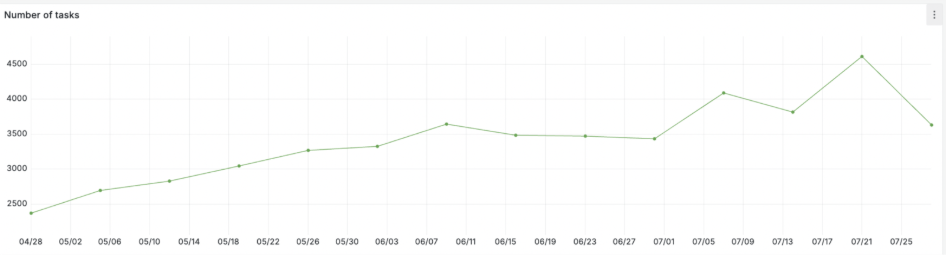
Telecom-targeted phishing campaigns surged in May–July 2025, with attackers abusing brand impersonation, DGA-like domains, and the Tycoon2FA phishing kit to harvest Microsoft credentials and bypass 2FA. ANY.RUN’s Interactive Sandbox, YARA searches, and Threat Intelligence Lookup enabled detection of malicious PDFs, phishing redirects (xjrsel.ywnhwmard[.]es), and recurring sender patterns to produce actionable IOCs…
Microsoft Threat Intelligence detected and blocked a credential-phishing campaign that used an SVG attachment with AI-like, business-term–based obfuscation to hide a JavaScript payload that redirected users to a phishing landing page. Microsoft Defender for Office 365’s AI-powered protections identified infrastructure, behavioral, and message-context signals to block the campaign. #SVG #SecurityCopilot
Based on frontline intelligence from over 7,000 incident investigations, Cybereason and partners identified 11 Essential Cybersecurity Controls that most effectively reduce likelihood, dwell time, and impact of attacks while enabling faster incident response and recovery. The guidance highlights common implementation pitfalls, DFIR-specific benefits, and mappings to major compliance frameworks to help…
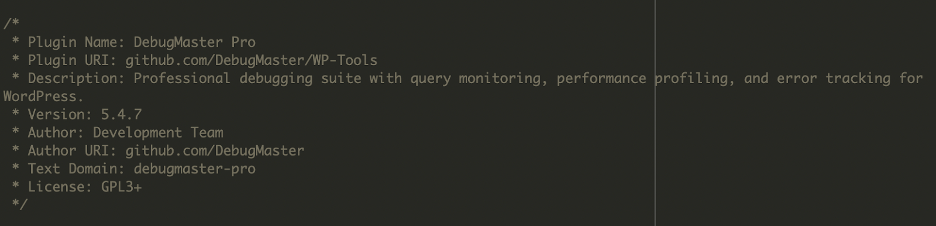
Two malicious backdoors were found on a compromised WordPress site: a disguised plugin at ./wp-content/plugins/DebugMaster/DebugMaster.php that created a hidden admin, exfiltrated credentials to a C2, hid itself, and injected visitor scripts; and a root-level ./wp-user.php that ensured a hardcoded admin account named “help” was always present by recreating it if removed. These files provided layered persistence, data exfiltration, and visitor-script injection, enabling long-term attacker access and control. #DebugMaster #kickstar-xbloom

Zscaler ThreatLabz identified a new backdoor family named YiBackdoor in June 2025 that can collect system information, capture screenshots, execute commands, and load plugins, and shows significant code overlap with IcedID and Latrodectus. The malware includes anti-analysis checks, injects into svchost.exe, persists via Run registry entries using regsvr32.exe, and communicates with C2 servers using dynamic TripleDES keys. #YiBackdoor #IcedID #Latrodectus

CISA investigated a multi-week compromise of a U.S. federal civilian executive branch agency where threat actors exploited CVE-2024-36401 in public-facing GeoServer instances to gain RCE, upload web shells (including China Chopper), establish C2 using Stowaway, move laterally to a web and SQL server, and persist using cron jobs, BITS abuse, and…

North Korean operators used ClickFix lures on a fake hiring site to distribute compiled BeaverTail and InvisibleFerret payloads beginning in May 2025, shifting targeting toward marketing and trading roles and delivering binaries bundled with pkg and PyInstaller. The campaign used infrastructure including businesshire[.]top, nvidiasdk.fly[.]dev, and C2 172.86.93.139 and shows testing artifacts and low-scale deployment to date. #BeaverTail #InvisibleFerret

Cisco Talos identified a multi-year campaign (since 2022) targeting telecommunications and manufacturing organizations in Central and South Asia that delivered a new variant of PlugX which shares significant code, keys, and execution techniques with RainyDay and Turian. The overlaps in configuration format, RC4 keys, XOR-RC4-RtlDecompressBuffer payload handling, and DLL sideloading lead…
