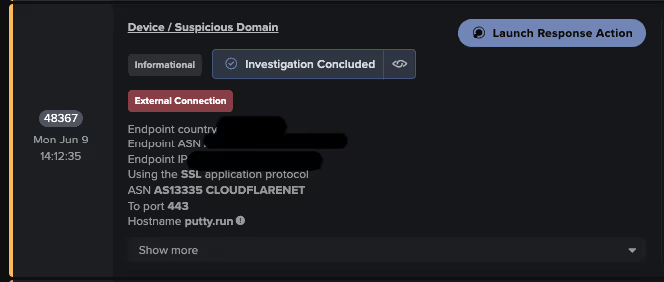
Attackers used SEO poisoning with typosquatted PuTTY download sites to deliver a trojanized installer that both installs PuTTY and deploys the Oyster (aka Broomstick/CleanUpLoader) backdoor, which establishes persistence via scheduled tasks and DLL side-loading and communicates with C2 endpoints using web-based URIs. Darktrace observed indicators including typosquatted domains (putty[.]run, putty-app[.]naymin[.]com), unusual user agents like “WordPressAgent”, and C2 URI patterns (/api/kcehc, /api/jgfnsfnuefcnegfnehjbfncejfh) tied to Oyster activity. #Oyster #putty[.]run
Keypoints
- Attackers leveraged SEO poisoning and typosquatted domains (e.g., putty[.]run) to present malicious PuTTY installers as legitimate downloads.
- The delivered trojanized installer installed a real copy of PuTTY while silently deploying the Oyster backdoor (also called Broomstick/CleanUpLoader).
- Oyster provides remote access, uses cmd.exe for command execution, supports file transfer, and frequently acts as an initial access vector for ransomware operators like Vanilla Tempest and Rhysida.
- Persistence mechanisms observed include Windows Scheduled Tasks and DLL side-loading (malicious twain_96.dll executed via rundll32.exe).
- Oyster C2 communications used web protocols with distinctive URI patterns (/api/kcehc, /api/jgfnsfnuefcnegfnehjbfncejfh, /reg, /secure) and spoofed user agents such as “WordPressAgent” or cryptic strings.
- Post-infection activity included downloading additional payloads (e.g., host[.]zip), HTTP POST-based exfiltration (/upload?dir=…), anomalous RDP sessions, and RDP scanning indicative of lateral movement.
- Darktrace’s anomaly-based detections and Autonomous Response capabilities identified and mitigated the campaign by detecting uncommon user agents, HTTP beaconing to rare destinations, and other model alerts.
MITRE Techniques
- [T1071.001] Command and Control – Web Protocols – Oyster used HTTP(S) URIs for C2 communications and beaconing to endpoints such as “…endpoints with URIs /api/kcehc and /api/jgfnsfnuefcnegfnehjbfncejfh…”
- [T1008] Command and Control – Fallback Channels – Multiple C2 endpoints and fallback callbacks were observed as the malware maintained communication with additional infrastructure: “…the malware continued communicating with additional infrastructure, maintaining its foothold…”
- [T0885] Command and Control – Commonly Used Port – C2 activity used standard web ports for HTTP/HTTPS requests to rare external IPs and URIs: “…device attempting outbound connectivity to rare external IP addresses, specifically requesting the ‘/secure’ endpoint…”
- [T1571] Command and Control – Non-Standard Port – Observed variations in network communication patterns and ports for persistence of C2 channels: “…continued communicating with additional infrastructure, maintaining its foothold and likely waiting for tasking instructions.”
- [T1176] Persistence – Browser Extensions – SEO poisoning leverages web delivery vectors and browser-based interactions to induce downloads from typosquatted landing pages: “…user lands on one of these fake pages… presented with what looks like a legitimate software download option.”
- [T1189] Initial Access – Drive-by Compromise – Users were redirected from SEO-poisoned landing pages to payload-hosting domains and downloaded trojanized installers via direct interaction: “…the user will be redirected to another separate domain that actually hosts the payload.”
- [T1566.002] Initial Access – Spearphishing Link – Malicious SEO and sponsored links (ads) were used to surface deceptive download links that entice users to click: “…backed by malicious Google ads, increasing the visibility when users search for download links.”
- [T1574.001] Persistence – DLL – Oyster employed DLL side-loading with a malicious DLL (e.g., ‘twain_96.dll’) executed via rundll32.exe: “…infection uses Dynamic Link Library (DLL) side loading, where a malicious DLL, often named ‘twain_96.dll’, is executed via the legitimate Windows utility ‘rundll32.exe’.”
Indicators of Compromise
- [IP Address] Observed C2 and payload hosts – 85.239.52[.]99, 185.28.119[.]113
- [IP/URI] IP with specific URI used for C2/exfiltration – 194.213.18[.]89/reg, 185.28.119[.]113/secure
- [Domain/Endpoint] Typosquatted or malicious landing sites – putty[.]run, putty-app[.]naymin[.]com
- [URI Paths] C2 and API endpoints – /api/jgfnsfnuefcnegfnehjbfncejfh, /api/kcehc, and /reg
- [File Name] Downloaded payloads and staging artifacts – host[.]zip (downloaded from /333/host[.]zip) and evidence of uploaded paths like /upload?dir=NAME_FOLDER/KEY_KEY_KEY/…
- [User Agent] Spoofed or cryptic user agents used in C2 traffic – “WordPressAgent”, “FingerPrint”, “FingerPrintpersistent”, and random Chinese-language strings