CERT-AGID analyzed a targeted email campaign impersonating Politecnico di Milano that delivered FormBook via a malicious JS inside a ZIP attachment which launched a PowerShell downloader. The campaign targeted construction-sector operators with convincing bid invitations; CERT-AGID shared IoCs with accredited organizations and advised caution including verifying senders, avoiding compressed attachments, and reporting to [email protected]. #FormBook #PolitecnicodiMilano
Keypoints
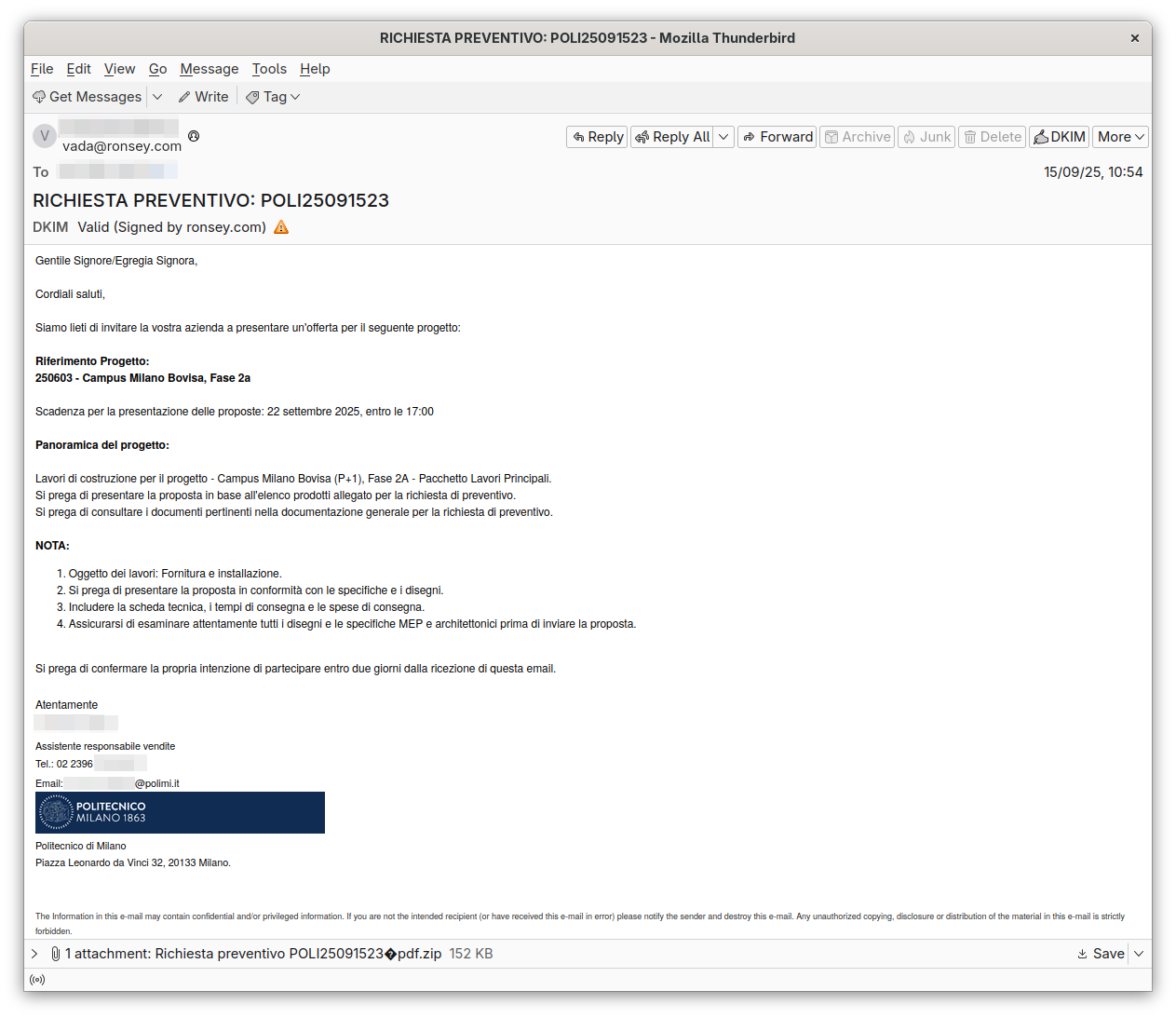
- The campaign impersonated an office of Politecnico di Milano to invite bids, increasing credibility and likelihood of engagement.
- Malicious emails contained a ZIP attachment that concealed a JavaScript (.js) script rather than legitimate documents.
- The obfuscated JavaScript launched a PowerShell script that downloaded and executed additional components.
- Final payload was the FormBook trojan, designed to steal credentials and sensitive data.
- Targets were likely operators in the construction sector, leveraging realistic corporate workflows to bypass suspicion.
- CERT-AGID notified Politecnico di Milano and shared Indicators of Compromise with accredited organizations.
- Recommended mitigations include verifying sender domains, avoiding compressed attachments from unknown senders, not opening scripts/executables, and reporting suspicious messages to [email protected].
MITRE Techniques
- [T1566] Phishing – The threat used deceptive emails impersonating Politecnico di Milano to trick recipients into opening an attachment (“the message… simulates coming from an office of Politecnico di Milano”).
- [T1204] User Execution – The attack relied on recipients opening the ZIP and executing the contained JavaScript (“invites the recipient to consult the attached documentation… open the ZIP file attached, which instead… hides a malicious JS script”).
- [T1218] Signed Binary Proxy Execution (PowerShell) – The obfuscated JavaScript launched a PowerShell script to download and run additional components (“The JavaScript… starts a PowerShell script that downloads and executes further components”).
- [T1105] Ingress Tool Transfer – The PowerShell downloader retrieved further components from external sources to install FormBook (“…downloads and executes further components. In the final phase, these components install the FormBook trojan”).
- [T1086] PowerShell – PowerShell was used as the execution environment for downloading and launching payloads (“…starts a PowerShell script that downloads and executes further components”).
- [T1059.005] JavaScript – A malicious JavaScript file inside a ZIP archive served as the initial script to trigger subsequent actions (“the ZIP… hides a malicious JS script”).
Indicators of Compromise
- [Attachment/File name] Malicious archive and script – ZIP attachment containing a .js script that launches PowerShell (example: archived bid_document.zip containing payload.js).
- [File type/Technique] Scripts and executables used – JavaScript that spawns PowerShell and PowerShell downloader scripts (example: payload.js, and follow-up PowerShell script), and other items shared with accredited organizations.
- [Affected organization] Impersonated sender context – Emails purporting to come from Politecnico di Milano (example: spoofed addresses/domains mimicking politecnico.it), and related communications reported to CERT-AGID.