Wazuh and Zeek can be integrated to provide unified, real-time network visibility by ingesting Zeek logs into Wazuh for enrichment, correlation, alerting, and automated response. The integration supports use cases such as detecting brute-force attempts, DoS, reconnaissance/port scans, suspicious DNS queries, and SSL/TLS certificate issues. #Wazuh #Zeek
Keypoints
- Wazuh is used as an open source SIEM/XDR platform to monitor, detect, and respond to threats across endpoints, networks, and cloud in real time.
- Zeek provides network visibility by analyzing traffic and producing structured logs (conn.log, dns.log, ssl.log, etc.), which are converted to JSON for easier ingestion.
- Integration steps include installing Zeek on an Ubuntu endpoint, enabling JSON logging, and configuring the Wazuh agent to monitor Zeek log files.
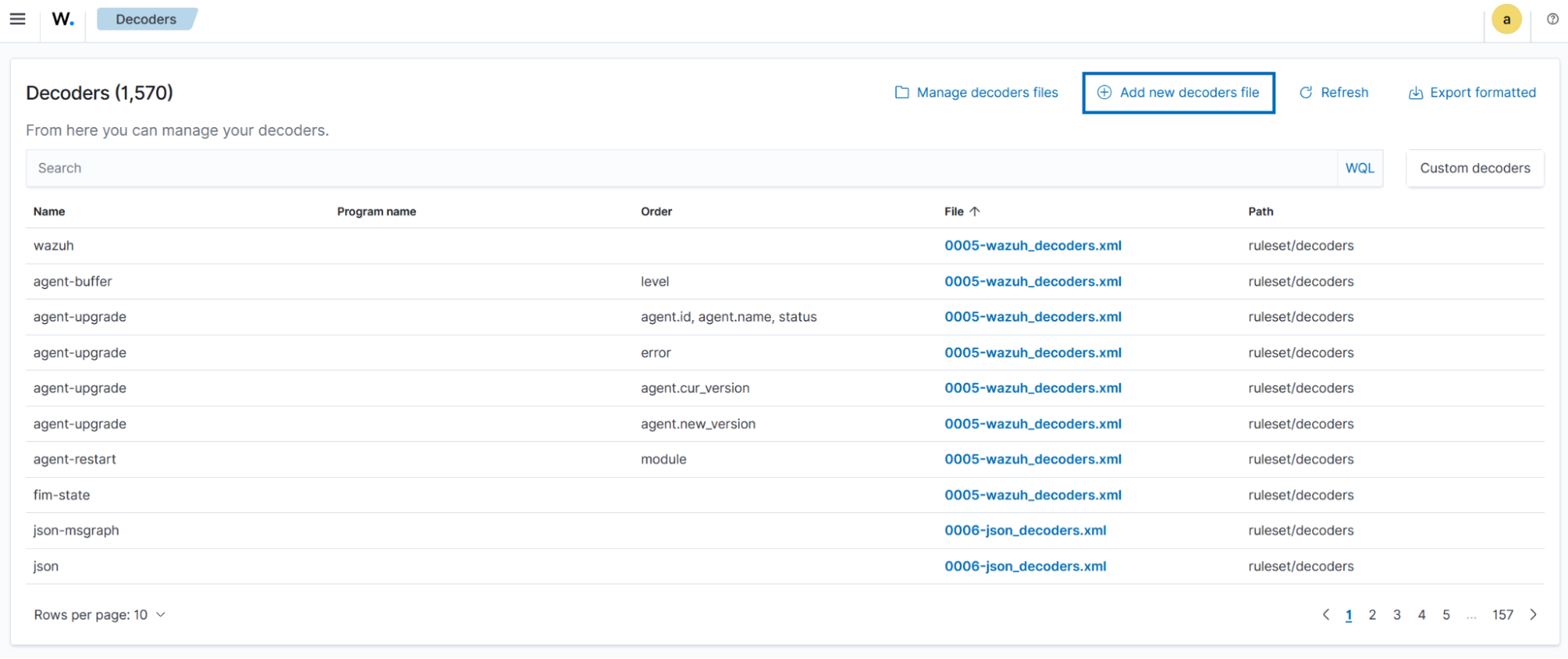
- Custom Wazuh decoders (zeek_decoders.xml) map Zeek JSON fields to standardized field names for parsing and correlation.
- Custom Wazuh rules (zeek_rules.xml) generate alerts for DNS queries, mDNS, rejected connections, repeated rejections (possible port scans), and SSL certificate validation issues.
- Testing procedures simulate DNS queries, port scans, and SSL certificate validation issues to validate detection and dashboard alerts using specific rule IDs.
- The integrated solution improves detection of network threats (brute-force, DoS, reconnaissance, malicious DNS, SSL/TLS issues) and provides actionable alerts via the Wazuh dashboard.
MITRE Techniques
- [T1046 ] Network Service Discovery – Used to detect reconnaissance/port scans by tracking repeated rejected connections and port probes: “Zeek: Multiple rejected connections from $(srcip) (5+ in 20s – possible port scan activity)”
- [T1071 ] Application Layer Protocol – DNS data exfiltration or suspicious DNS usage detected via DNS logs and rules: “Zeek: DNS Query $(dnsquery) attempted from source ip $(srcip) source port $(srcport) resolved to IP(s) $(resolved_by)”
- [T1499 ] Endpoint Denial of Service – Detection of potential DoS by identifying flooding traffic from a single source in conn.log (described as “Identifies flooding traffic from a single source.”)
- [T1110 ] Brute Force – Detection of repeated failed login attempts inferred from connection patterns in conn.log (“Detects repeated failed login attempts based on connection patterns.”)
- [T1553 ] Use Alternate Protocol – SSL/TLS anomalies and certificate issues flagged from ssl.log indicating possible man-in-the-middle or suspicious services: “Zeek: Client $(srcip) connected to a server with self-signed certificate $(dstip)” and “Zeek: Client $(srcip) connected to a server with expired certificate $(dstip)”
Indicators of Compromise
- [Domain ] Example DNS queries used in testing and detection – wazuh.com, virustotal.com
- [Log file paths ] Locations of Zeek JSON logs ingested by Wazuh – /opt/zeek/logs/current/*.log
- [Rule IDs ] Wazuh detection identifiers used to find alerts in the dashboard – 100901, 100903, 100904, 100906, 100907
- [Configuration artifacts ] Zeek and Wazuh configuration files referenced – /opt/zeek/etc/node.cfg, /opt/zeek/share/zeek/site/local.zeek, /var/ossec/etc/ossec.conf
- [Software versions ] Versions noted for reproducibility – Zeek 7.2.2, Wazuh 4.12.0
Read more: https://wazuh.com/blog/network-security-monitoring-with-wazuh-and-zeek/