Acronis TRU researchers documented an in-the-wild FileFix campaign that evolved from the FileFix proof-of-concept into a sophisticated, multilingual phishing operation using heavy JavaScript obfuscation, multistage PowerShell payloads, and steganography to hide a second-stage script and encrypted executables inside JPG images. The final payload is a Go-based loader that performs VM checks and decrypts shellcode to deploy the StealC infostealer, with C2 infrastructure including 77[.]90[.]153[.]225 and hosting on Bitbucket. #FileFix #StealC
Category: Threat Research
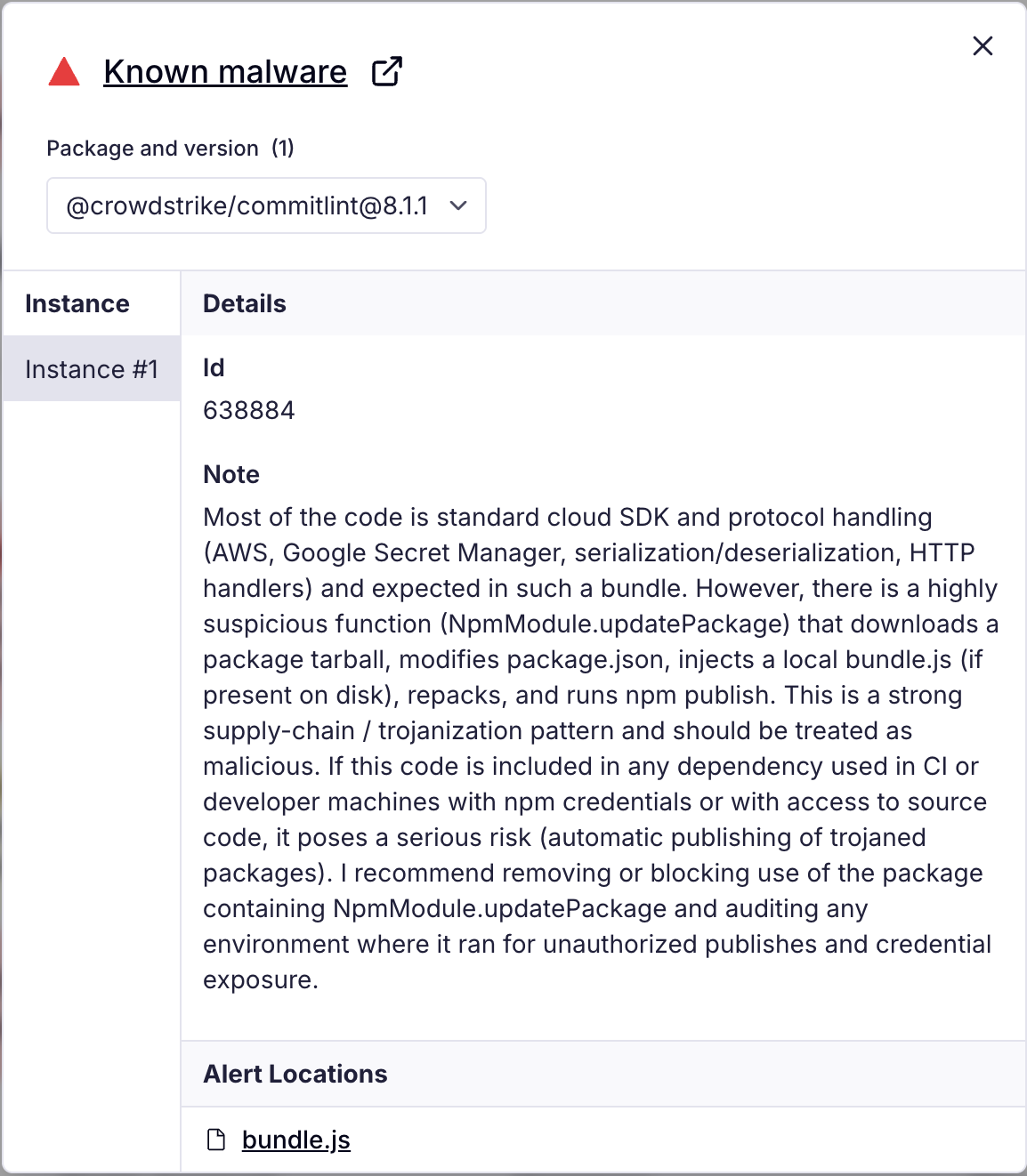
Multiple npm packages published by the crowdstrike-publisher account were compromised in a continuing “Shai-Halud” supply chain campaign that implants a bundle.js payload to scan for credentials, validate tokens, create GitHub Actions workflows, and exfiltrate sensitive data to a hardcoded webhook. The campaign affected over 100 packages (including many under @crowdstrike and other namespaces) and used workflow filenames like shai-hulud.yaml/shai-hulud-workflow.yml to persist exfiltration in CI pipelines. #Shai-Halud #TruffleHog #crowdstrike
Vane Viper — an adtech ecosystem centered on AdTech Holding and PropellerAds — operates a large, resilient malvertising and ad-fraud network using traffic distribution systems (TDS), push-notification abuse, service-worker script chaining, and thousands of short-lived domains to deliver malware, fraudulent downloads, and persistent unwanted notifications. Investigation links Vane Viper infrastructure to PropellerAds, URL Solutions/Pananames, Webzilla/XBT, and related actors, showing shared IP space, registrar bulk registrations, and organizational ties that enable plausible deniability and large-scale abuse. #VaneViper #PropellerAds

Qilin (also known as Agenda) emerged in Q2 2025 as the most active ransomware targeting U.S. State, Local, Tribal, and Territorial (SLTT) government entities, responsible for roughly 24% of reported incidents and leveraging double-extortion tactics including data theft and public leak sites. Qilin operates as a Ransomware-as-a-Service (RaaS) with affiliates using…

XillenStealer is an open-source, Python-based information stealer with a GUI builder that harvests system metadata, browser credentials, cryptocurrency wallet files, messaging sessions, and screenshots, then exfiltrates data via a Telegram bot. The builder lowers the barrier for abuse by enabling rapid configuration and compilation of customized builds and is linked to Russian-speaking actors and an ecosystem at xillenkillers[.]ru. #XillenStealer #Telegram

Ransomware activity in August 2025 showed global expansion by the Qilin group, continued emergence of new groups, and increased targeting of critical infrastructure and the Asia-Pacific region. The AhnLab TIP report provides statistics on affected industries, regional trends, top ransomware groups, and DLS/detection trends over the past three years. #Qilin #AhnLab…

TA415 conducted July–August 2025 spearphishing campaigns against U.S. government, think tank, and academic targets on U.S.-China economic topics, impersonating the Select Committee Chair and the US-China Business Council to distribute password-protected archives that executed an obfuscated Python loader (WhirlCoil) to install VS Code Remote Tunnels for persistent remote access. The actor…
APT-C-24 (响尾蛇) uses malicious LNK files inside zip archives to deliver MSHTA-executed obfuscated HTA/JS scripts that memory-load C# loaders and remote payloads, targeting government, military, and energy sectors in South Asia. The campaigns use distinctive URL patterns ending in yui=0/1/2 and domains such as mail163cn.info, with rapid C2 rotation and strong code-obfuscation and evasion techniques. #APT-C-24 #mail163cn.info
RevengeHotels (TA558) runs targeted phishing campaigns against hotels—primarily in Brazil—using invoice- and job-themed lures to deliver multi-stage loaders that ultimately deploy VenomRAT and other RAT families. The group increasingly leverages LLM-generated code for initial loaders and abuses legitimate hosting and Portuguese-themed domains for payload delivery. #RevengeHotels #VenomRAT
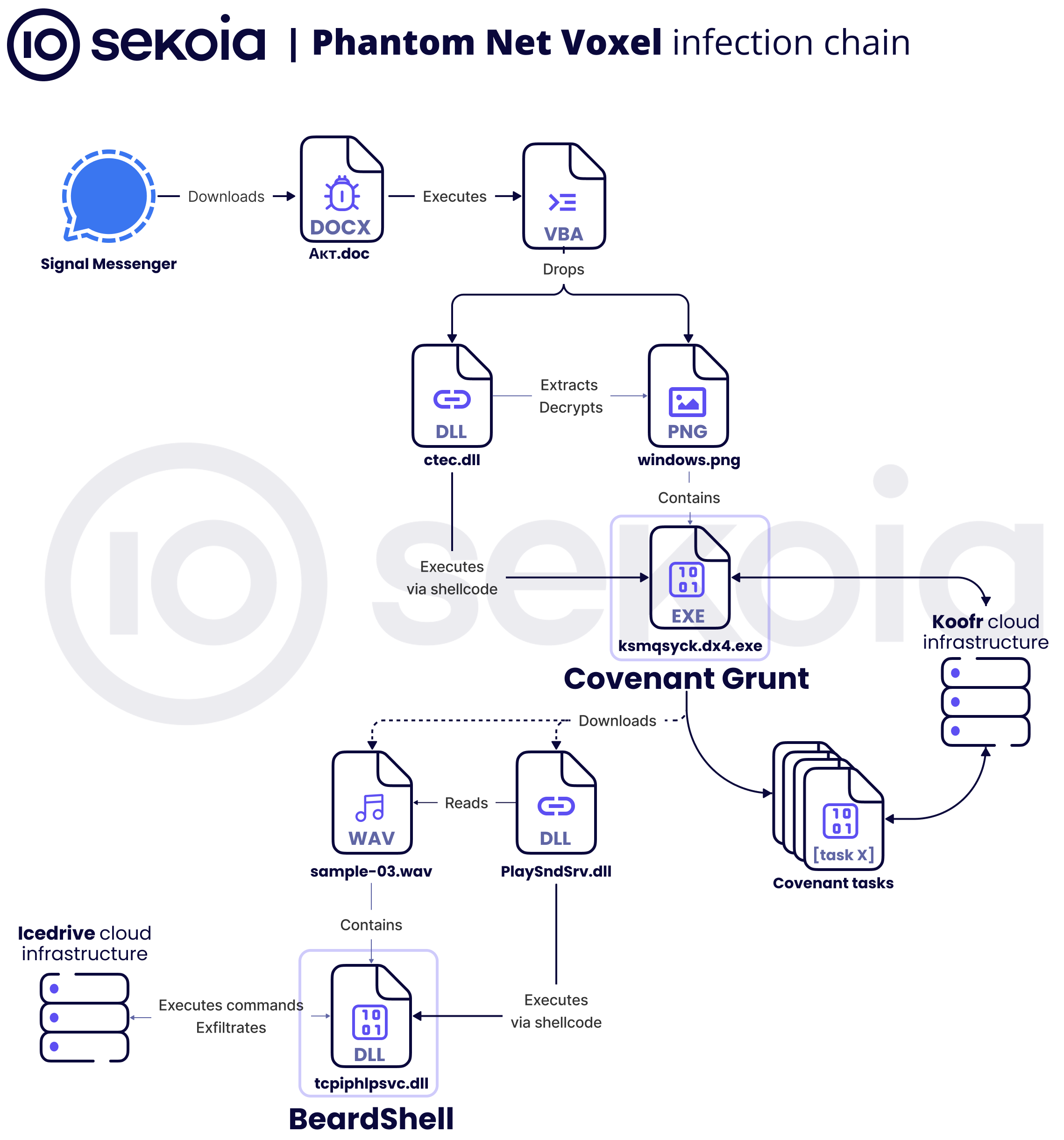
Sekoia.io analyzed an APT28 campaign that uses weaponized Office documents with malicious VBA to deploy a COM-hijack DLL which extracts shellcode hidden in PNG files to load a .NET Covenant Grunt stager communicating via Koofr, and (per CERT-UA) a subsequent BeardShell backdoor delivered via icedrive. The campaign also included SlimAgent keylogger/screenshooter and novel techniques such as PNG-based steganographic payloads and Covenant C2Bridge use of Koofr (and later Filen); #APT28 #Covenant #BeardShell #Koofr #icedrive

SmokeLoader has resurfaced with two updated variants — version 2025 alpha and version 2025 — that fix long-standing bugs (notably a recurring injection/mutex issue), add evasion and obfuscation changes, and modify network protocol details. ThreatLabz observed these versions in the wild, provided detection/cleanup tooling (SmokeBuster), and published IOCs including file hashes and C2 domains/IPs. #SmokeLoader #SmokeBuster

In August 2025 phishing-themed attachments accounted for 63% of threats, with actors using HTML scripts, embedded hyperlinks in documents, and compressed executables to harvest credentials or deliver malware. Exploit-based documents (CVE-2017-11882) deploying Purecrypter and ZIP-distributed PE files were observed, along with C2 communications and credential-stealing fake pages. #Purecrypter #CVE-2017-11882…
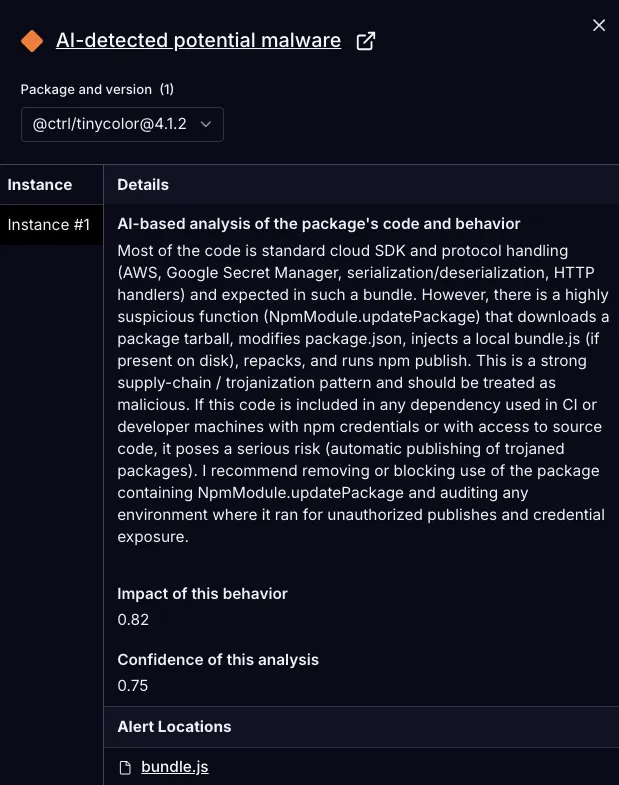
A malicious update to @ctrl/tinycolor and over 40 other npm packages injected a trojanized installer that modifies package archives to include a bundled script (bundle.js) which runs on install to scan for secrets, validate tokens, create GitHub Actions workflows, and exfiltrate findings to a hardcoded webhook. The campaign uses an automated repack-and-publish routine (NpmModule.updatePackage) to propagate across downstream packages and has been flagged by researchers and automated detection systems. #TruffleHog #@ctrl/tinycolor

The Kimsuky group used generative AI (ChatGPT) to create deepfake images of South Korean military ID cards and incorporated them into spear-phishing campaigns that deployed obfuscated scripts and AutoIt-based payloads to contact C2 servers. Affected targets include South Korean military agencies and portal companies, highlighting the need for EDR adoption and improved endpoint detection to counter obfuscated multi-stage attacks. #Kimsuky #ChatGPT
CISA, FBI, NSA and partners released a joint CSA detailing TTPs linked to China-aligned activity overlapping with the actor industry calls Salt Typhoon (also reported as FamousSparrow, SparrowDoor, ShadowPad activity). AttackIQ updated its assessment templates and attack graphs to emulate these behaviors—covering execution, persistence, credential access, discovery, and C2—to help organizations…
