Sekoia.io analyzed an APT28 campaign that uses weaponized Office documents with malicious VBA to deploy a COM-hijack DLL which extracts shellcode hidden in PNG files to load a .NET Covenant Grunt stager communicating via Koofr, and (per CERT-UA) a subsequent BeardShell backdoor delivered via icedrive. The campaign also included SlimAgent keylogger/screenshooter and novel techniques such as PNG-based steganographic payloads and Covenant C2Bridge use of Koofr (and later Filen); #APT28 #Covenant #BeardShell #Koofr #icedrive
Keypoints
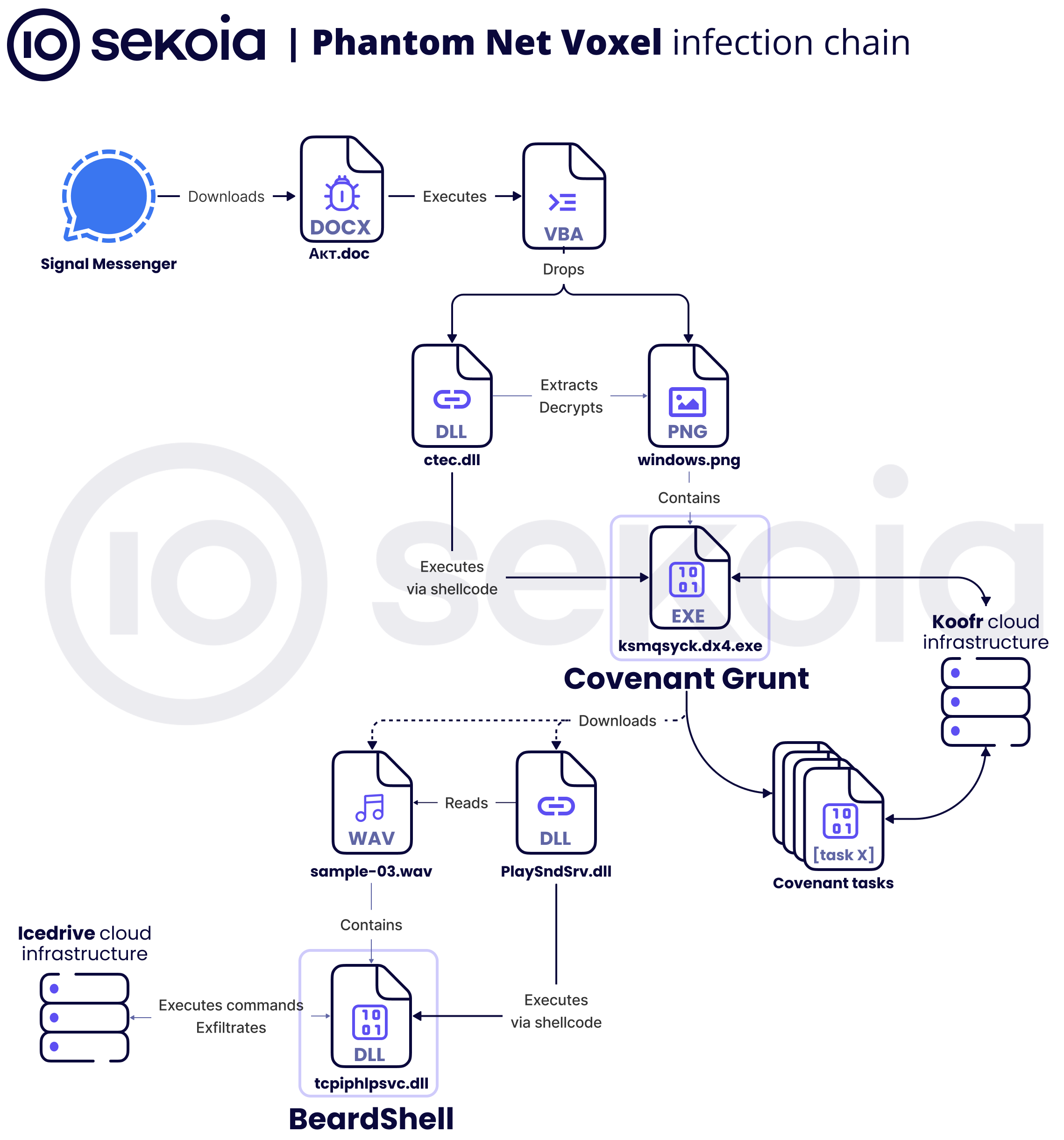
- Initial access via spearphishing: targeted Office documents (Ukrainian military-themed lures) delivered over private Signal chats containing malicious VBA macros.
- VBA macros drop a proxy COM DLL (prnfldr.dll) and a PNG (windows.png) then register the DLL for persistence via InProcServer32 CLSID hijack and regsvr32 /i.
- The malicious DLL extracts AES-encrypted shellcode from the LSBs of PNG pixels (steganography), decrypts it and uses the shellcode to host the CLR and load a .NET Covenant HTTP Grunt stager in-memory.
- Covenant was customized to use a Koofr-based C2Bridge: the implant creates folders, performs hybrid key exchange via uploaded files, polls for encrypted “Tasks”, executes them in-memory and uploads results to Koofr.
- CERT-UA links the chain to BeardShell (C++ backdoor) using icedrive for C2, which polls a per-host folder, executes JSON commands to run PowerShell sessions and uploads results; Sekoia also observed SlimAgent on the same server (keylogger/screenshooter) though direct linkage is unconfirmed.
- Novel techniques include PNG LSB-based payload embedding, DLL proxying to preserve legitimate functionality, and leveraging legitimate cloud-storage APIs (Koofr, icedrive, later Filen) as covert C2 transport.
- Sekoia recovered multiple weaponized documents, Koofr account credentials and numerous uploaded files suggesting ~42 distinct compromised GUIDs; detections (YARA) and Python tooling were provided for extraction/decryption.
MITRE Techniques
- [T1566] Phishing – Initial delivery via spearphishing messages over Signal containing malicious Office documents (“the infection chain begins with the Office document being delivered via a private Signal chat”).
- [T1204] User Execution – Malicious VBA macros require user to open document and enable macros to trigger the payload (“these exchanges … urges the recipient to open and complete the malicious Office document”).
- [T1219] System Binary Proxy Execution – Abuse of regsvr32.exe to run DllInstall and trigger DLL installation (“the accompanying VBA macro immediately invokes regsvr32.exe with the /i switch, triggering the DLL’s installation routine”).
- [T1546] Event Triggered Execution: COM Hijacking – Persistence via InProcServer32 CLSID registration causing explorer.exe to load the malicious DLL (“reg.exe is used to add an InProcServer32 registry key … thereafter, at each user logon, explorer.exe automatically loads this server”).
- [T1027] Obfuscated Files or Information – Payloads and strings are encrypted/obfuscated (single-byte XOR, embedded AES blobs, randomized .NET names) (“strings are encrypted using a ten-character XOR key” and “uses a basic single-byte XOR cipher”).
- [T1005] Data from Local System (steganography) – Payload hidden inside PNG LSBs used to store encrypted shellcode (“the LSB of each value is used to create the next payload … The data is an AES-CBC encrypted blob”).
- [T1573] Encrypted Channel – Use of hybrid encryption (hybrid key exchange + AES session keys) for Covenant communication via cloud files (“Grunt uses hybrid encryption to perform a secure key exchange”).
- [T1105] Ingress Tool Transfer – Download of additional modules and tasks from Koofr/icedrive storage (implant polls Transfering folder for new modules and downloads them) (“the implant polls the Tansfering folder for new ‘modules’ … the implant downloads that file, decrypts … and loads it into memory”).
- [T1210] Exploitation of Remote Services (Cloud Abuse) – Abuse of legitimate cloud storage APIs (Koofr, icedrive, Filen) as covert C2 channels (“attacker implemented a custom C2Bridge leveraging the Koofr API as a C2, relying entirely on file upload and download”).
- [T1056] Input Capture – Keylogging and screenshots by SlimAgent (“this malware … has for main functionality keylogging and screenshooting”).
- [T1059] Command and Scripting Interpreter – BeardShell executes PowerShell commands by hosting the CLR and using System.Management.Automation to run cmdlets/scripts (“BeardShell … loads the System.Management.Automation assembly … to create PowerShell instances”).
Indicators of Compromise
- [File Hash ] second-stage DLL (steganography loader) – sha256: 2338f420d66ef191c5a419353da2c12b… (long hash listed), and other related hash fragments (multiple listed in report).
- [File Hash ] Covenant Grunt stager (in-memory .NET) – sha256: f442db1753a7475842607307a439870e and c60991effda994e4…, and additional in-memory module hashes.
- [File Hash ] BeardShell backdoor – sha256: d802290cb9e5c3fed1ba1a8daf827882 (short hash shown in report).
- [File Hash ] SlimAgent DLL – md5: 889b83d375a0fb00670af5276816080e (source: CERT-UA) – keylogger/screenshooter proxy DLL.
- [Document Files ] Weaponized Office documents – examples include СЛУЖБОВА ХАРАКТЕРИСТИКА.doc (MD5: 608877a9e11101da53bce99b0effc75b), lorem.doc (f21b63dd…), and multiple other MD5s listed in the attachments.
- [Cloud Accounts / C2 ] Koofr credentials and storage container IDs – examples: jakub2233@tutamail[.]com storage container ID 133bd1da-4d2b-454f-9029-87f46ab30ca7; Alan_Smith2304@outlook[.]com container ID 90af1701-2aff-461d-b962-b32dec0f1a13.
- [Files ] PNGs used to hide shellcode and stage payloads – examples: windows.png (hashes: 5ddc34c5a9a2a1dc97c79d8777d54f14 and 50199e69c6a23ce935267be72372de0a), Koala.png (bef42c5c079fe43c8353b24c607d9e4d).
- [Cloud Service Endpoints ] Legitimate services abused as C2 – Koofr API endpoint app.koofr.net; icedrive API api.icedrive.net; Filen gateways (gateway.filen.io, gateway.filen.net, etc.).
Read more: https://blog.sekoia.io/apt28-operation-phantom-net-voxel/