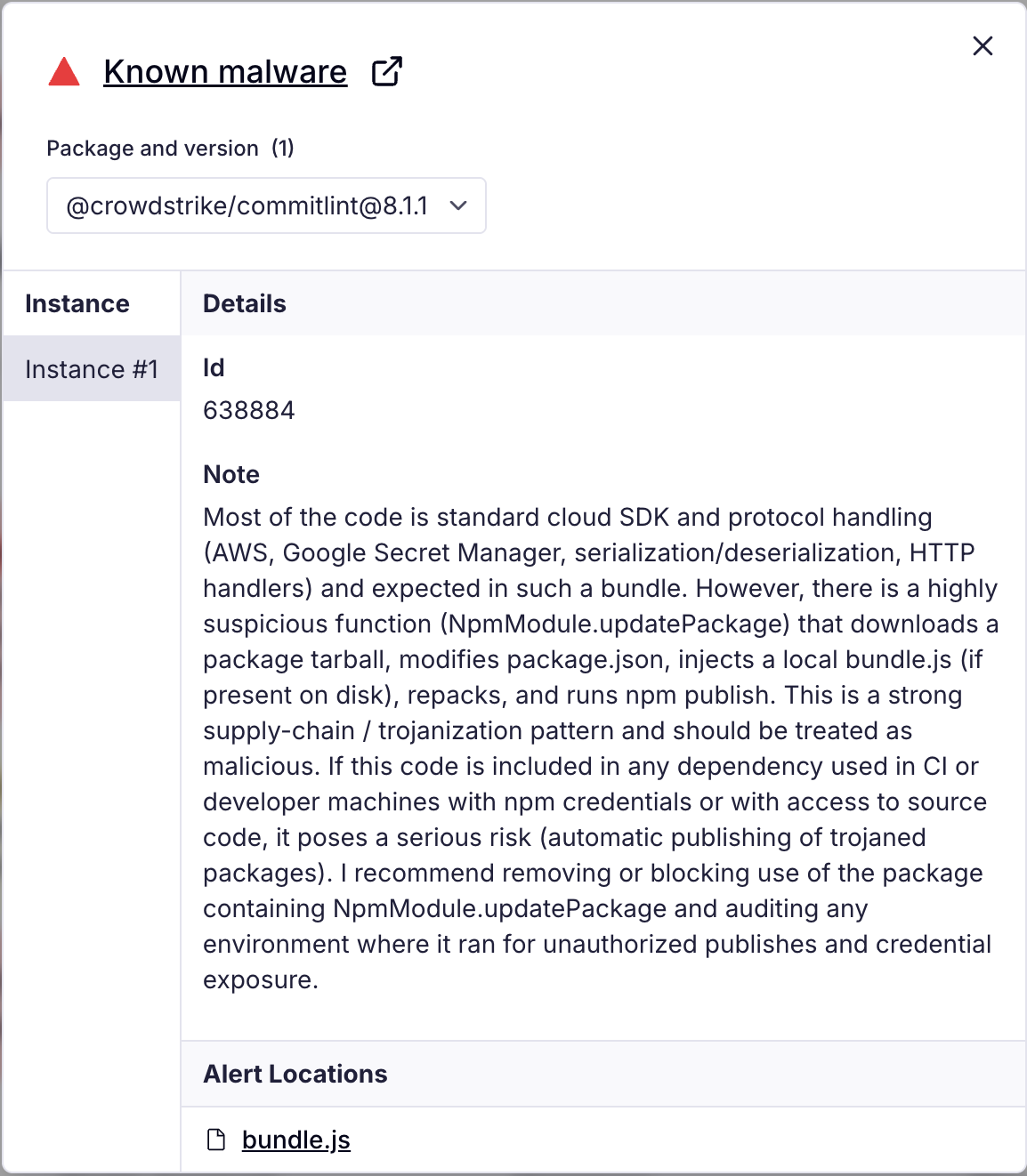
Multiple npm packages published by the crowdstrike-publisher account were compromised in a continuing “Shai-Halud” supply chain campaign that implants a bundle.js payload to scan for credentials, validate tokens, create GitHub Actions workflows, and exfiltrate sensitive data to a hardcoded webhook. The campaign affected over 100 packages (including many under @crowdstrike and other namespaces) and used workflow filenames like shai-hulud.yaml/shai-hulud-workflow.yml to persist exfiltration in CI pipelines. #Shai-Halud #TruffleHog #crowdstrike
Keypoints
- Multiple npm packages from the crowdstrike-publisher account were published with malicious payloads tied to the ongoing “Shai-Halud” campaign.
- The injected bundle.js downloads and executes TruffleHog, searches hosts for tokens and cloud credentials, validates discovered tokens, and exfiltrates data to a hardcoded webhook.
- The malware writes GitHub Actions workflow files (e.g., shai-hulud-workflow.yml / shai-hulud.yaml) into .github/workflows to persist and trigger exfiltration in CI runs.
- Nearly 700 public GitHub repositories named “Shai-Hulud Migration” appeared around the same time, likely artifacts of attacker automation for persistence or staging.
- Affected package list includes hundreds of package names and versions across many namespaces (examples: @crowdstrike/*, @ctrl/tinycolor, numerous @operato and @nativescript-community packages).
- Registry removed the affected packages quickly; recommended actions include uninstalling or pinning to known-good versions, auditing CI/dev environments, rotating exposed tokens, and monitoring for unusual npm publish events.
- Timeline analysis shows multiple bursts of malicious publishes across Sept 14–16, 2025 with reused payload hashes and several active SHA-256 hashes tied to different bursts.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – The bundle.js contains a bash block that executes commands to scan the host, validate tokens, and write workflows (“the bash block uses a GitHub personal access token if present, writes a GitHub Actions workflow into .github/workflows, and exfiltrates collected content to a webhook”).
- [T1592] Gather Victim Host Information – The script searches host systems for tokens and cloud credentials and probes cloud metadata (“Searches host systems for tokens and cloud credentials” and “attempts cloud metadata discovery that can leak short lived credentials inside cloud build agents”).
- [T1114] Email Collection (exfiltration variant of collecting secrets) – The payload exfiltrates collected sensitive data to a hardcoded webhook endpoint (“Exfiltrates sensitive data to a hardcoded webhook endpoint”).
- [T1574] Hijack Execution Flow (create or modify CI workflows) – The malware creates unauthorized GitHub Actions workflows in repositories to persist execution and trigger exfiltration from CI (“Creates unauthorized GitHub Actions workflows within repositories” and “The workflow that it writes to repositories persists beyond the initial host”).
- [T1086] PowerShell (scripting usage) – While not explicitly PowerShell, the campaign uses scripting to execute TruffleHog and orchestrate token validation and exfiltration (“Downloads and executes TruffleHog, a legitimate secret scanner” and “The script combines local scanning with service specific probing”).
- [T1609] Container and Resource Discovery (cloud metadata probing) – The script interacts with cloud metadata endpoints to discover short-lived credentials in build agents (“It also attempts cloud metadata discovery that can leak short lived credentials inside cloud build agents”).
- [T1190] Exploit Public-Facing Application (supply chain compromise) – The attacker compromised npm packages and used the package publication process as a vector to deliver malicious payloads to downstream consumers (“Multiple CrowdStrike npm packages published by the crowdstrike-publisher npm account were compromised” and insertion of bundle.js into packages).
Indicators of Compromise
- [File hash] Malicious bundle.js SHA-256 – 46faab8ab153fae6e80e7cca38eab363075bb524edd79e42269217a083628f09 (identified as the bundle.js payload).
- [URL / Domain] Exfiltration endpoint – hxxps://webhook[.]site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7de0e25a3e6c1e1e5998b306b7141b3dc4c0088da9d7bb47c1c00c91e6e4f85d681d2a004a1bca6ef87a1caf7d0e0b355ad1764238e40ff6d1b1cb77ad4f595c383a650ce44b2a9854802a7fb4c202877815274c129af49e6c2d1d5d5d55c501e4b2399646573bb737c4969563303d8ee2e9ddbd1b271f1ca9e35ea78062538dbdc67467a39b70d1cd4c1f7f7a459b35058163592f4a9e8fb4dffcbba98ef210c46faab8ab153fae6e80e7cca38eab363075bb524edd79e42269217a083628f09b74caeaa75e077c99f7d44f46daaf9796a3be43ecf24f2a1fd381844669da777 (hardcoded webhook used for exfiltration).
- [File name] GitHub Actions workflow filenames – shai-hulud-workflow.yml, shai-hulud.yaml – used to persist exfiltration in .github/workflows (observed written by the payload).
- [Package names] Compromised npm packages – examples: @crowdstrike/[email protected], @ctrl/[email protected], @operato/[email protected] (and many more across @crowdstrike, @operato, @nativescript-community, and other namespaces; see full list).
Read more: https://socket.dev/blog/ongoing-supply-chain-attack-targets-crowdstrike-npm-packages