CISA, FBI, NSA and partners released a joint CSA detailing TTPs linked to China-aligned activity overlapping with the actor industry calls Salt Typhoon (also reported as FamousSparrow, SparrowDoor, ShadowPad activity). AttackIQ updated its assessment templates and attack graphs to emulate these behaviors—covering execution, persistence, credential access, discovery, and C2—to help organizations…
Category: Threat Research
Cyble Research & Intelligence Labs discovered Maranhão Stealer, a Node.js–based credential stealer distributed via trojanized gaming sites and cloud-hosted social engineering pages that drops an Inno Setup installer executing a Node.js binary to harvest credentials, cookies, history, screenshots, and wallet data. The campaign uses reflective DLL injection into browsers, Run registry keys and scheduled tasks for persistence, and exfiltrates data to attacker infrastructure including maranhaogang[.]fun and 104.234.65.186. #MaranhãoStealer #maranhaogang.fun
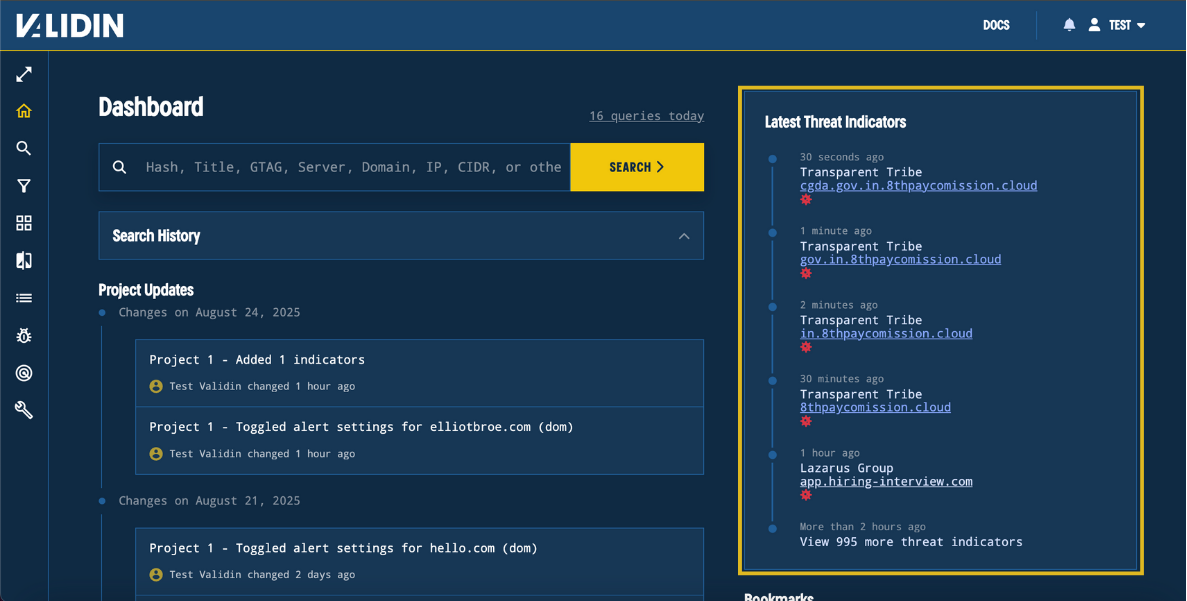
Validin introduced Dashboard Feeds (Threat Indicator Feed and Project Updates Feed) to surface newly reported IOCs and team activity directly on the homepage, improving analyst workflows and situational awareness. They also added daily PTR (reverse DNS) scanning across IPv4 to capture short-lived reverse DNS entries, illustrated by detection of rotating PTR records for 91.247.36[.]102, including free.friendhosting[.]net. #91.247.36.102 #free.friendhosting.net
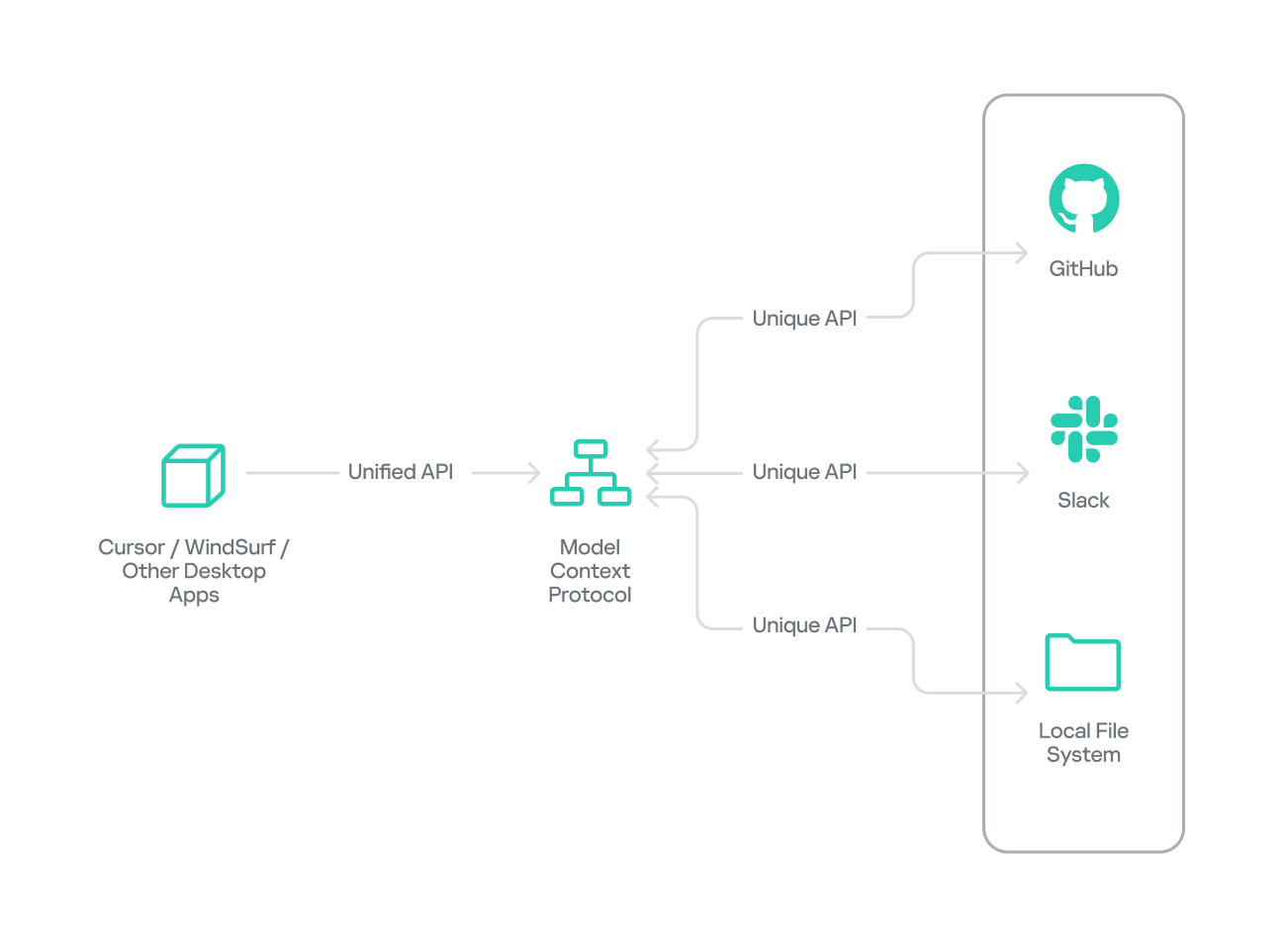
Researchers demonstrated that a malicious Model Context Protocol (MCP) server distributed as a seemingly helpful PyPI package can harvest sensitive files (env files, SSH keys, cloud credentials, tokens) and exfiltrate them disguised as legitimate GitHub-like API traffic. The proof-of-concept shows how protocol-level name spoofing, tool-poisoning, shadowing, and supply-chain distribution enable large-scale data theft if MCP servers are installed without review. #ModelContextProtocol #DevTools-Assistant
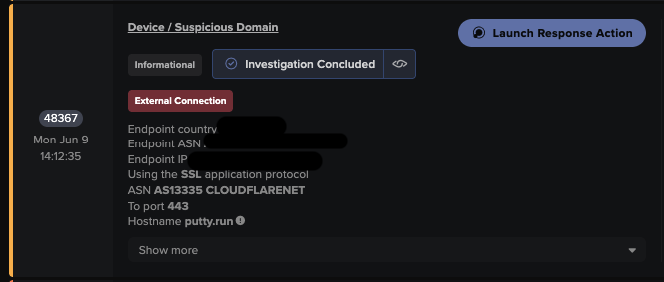
Attackers use SEO poisoning to promote typo‑squatted download sites (e.g., putty[.]run) that deliver a trojanized PuTTY which installs the Oyster (aka Broomstick/CleanUpLoader) backdoor. Darktrace observed TLS visits to typosquatted domains, redirects to payload hosts, C2 HTTP patterns (/secure, /api/kcehc, /api/jgfnsfnuefcnegfnehjbfncejfh), unusual user agents (e.g., “WordPressAgent”), scheduled task persistence, and DLL side‑loading via rundll32.exe. #Oyster #putty[.]run
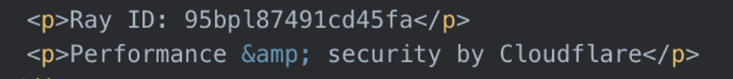
DomainTools found 21 domains registered since 01 June 2025 likely linked to the ecrime actor PoisonSeed that spoof SendGrid and use fake Cloudflare CAPTCHA interstitials to harvest enterprise credentials. Evidence suggests PoisonSeed’s TTPs resemble those of SCATTERED SPIDER, though a definitive operational link is unproven. #PoisonSeed #SCATTERED_SPIDER

Jamf Threat Labs analyzed a modular macOS backdoor named ChillyHell that remained notarized since 2021 and uses host profiling, multiple persistence mechanisms, DNS/HTTP C2 channels, and modular tasking including a brute-force module. The report links ChillyHell to prior Mandiant reporting (UNC4487 / MATANBUCHUS context), lists hardcoded C2 IPs and transport methods, and notes Apple revoked the associated developer certificates after disclosure. #ChillyHell #MATANBUCHUS
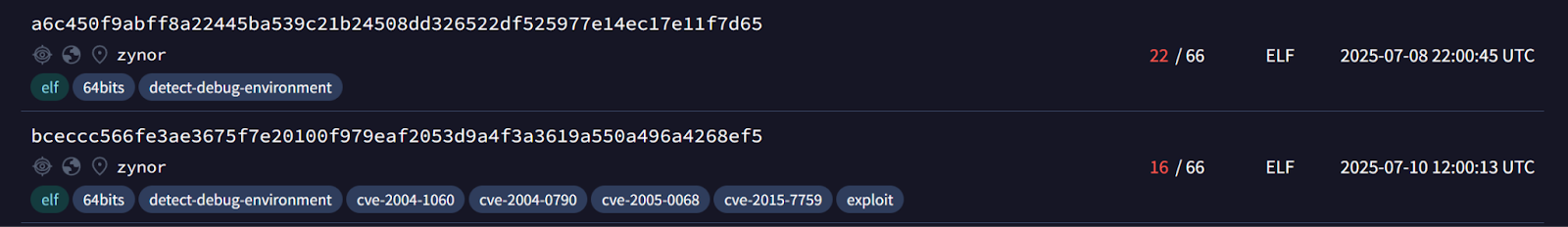
Sysdig TRT discovered a new Go-based remote access trojan named ZynorRAT that uses a Telegram bot as its command-and-control channel to perform file exfiltration, system enumeration, screenshots, persistence via systemd, process control, and arbitrary shell execution on Linux (with an incomplete Windows build). Analysis of binaries, Telegram chats, VirusTotal submissions, and network telemetry suggests the developer is Turkish, actively refining the RAT, and likely preparing it for sale on underground markets. #ZynorRAT #lraterrorsbot

Darktrace observed increased use of AI (notably LLMs) by threat actors to scale and sophisticate phishing and social‑engineering campaigns, alongside continued exploitation of internet‑facing systems and rapid ransomware activity driven by Ransomware‑as‑a‑Service affiliates. Notable threats and IOCs included LameHug, ClickFix campaigns, SimpleHelp CVE exploitation, ransomware families like Qilin/RansomHub/Lynx, and persistent malware such as Raspberry Robin and Auto-Color. #LameHug #ClickFix
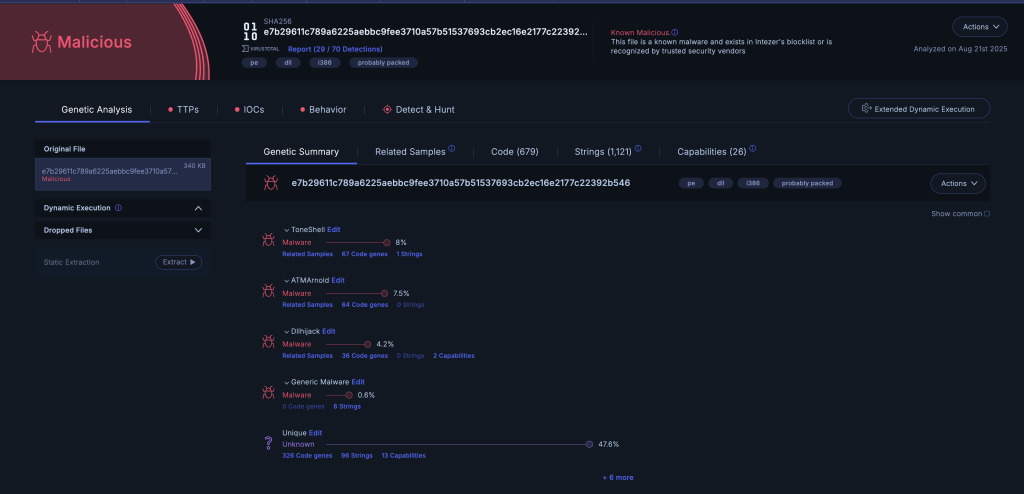
A new ToneShell backdoor variant tied to Mustang Panda was delivered via DLL sideloading inside ZIP archives and uses anti-analysis stalling, GUID-based host IDs, a rolling-XOR C2 scheme, and a minimal command set while targeting Myanmar. New indicators include DLL and archive hashes and a C2 at 146.70.29[.]229:443 that can aid…

A Chinese APT compromised a Philippine military company using a new fileless malware framework called EggStreme that injects payloads into memory and abuses DLL sideloading for persistent espionage. The core EggStremeAgent backdoor (with an injected EggStremeKeylogger) supports 58 commands for reconnaissance, lateral movement, and data exfiltration. #EggStreme #EggStremeAgent…
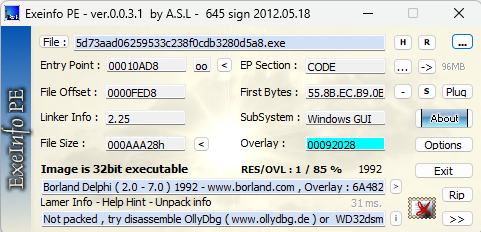
The article analyzes the Backdoor.Win32.Buterat sample, detailing its persistence, obfuscated strings and API usage (notably SetThreadContext and ResumeThread), dropped files, hashes, and C2 infrastructure. It also provides technical controls and remediation steps including indicators like file hashes and the C2 domain. #Backdoor.Win32.Buterat #ginomp3.mooo.com
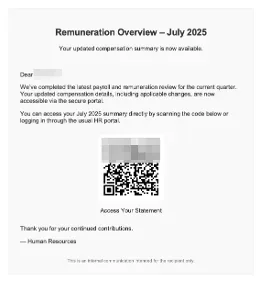
ReliaQuest observed a 241% surge in activity using the Axios user agent between June and August 2025, with campaigns pairing Axios and Microsoft Direct Send achieving up to a 70% credential-theft success rate and broadening from high-profile targets to everyday users. The report highlights abuse of Axios for automating phishing, MFA/session token interception, and API exploitation—often delivered via QR-coded phishing and short-lived domains like .es and Firebase links—calling for tightened Direct Send controls and enhanced detection. #Axios #DirectSend

FortiGuard Labs identified an SEO poisoning campaign targeting Chinese-speaking users that used manipulated search rankings and lookalike domains to distribute malware, notably Hiddengh0st and Winos variants. The campaign delivered malicious MSI installers (impersonating DeepL) that included EnumW.dll and vstdlib.dll, used extensive anti-analysis checks, persistence via TypeLib hijacking or Startup redirection, and a C2-capable payload for data theft and plugins. #Hiddengh0st #Winos

Yurei is a newly observed ransomware group that launched operations on September 5, targeting organizations in Sri Lanka, India, and Nigeria and using a double-extortion model to encrypt files (adding a .Yurei extension) and exfiltrate data via a darknet blog and negotiation chat on an .onion site. Analysis shows Yurei’s binary is derived with minor modifications from the open‑source Prince‑Ransomware (written in Go), inherits flaws such as not deleting Volume Shadow Copies, and exhibits indicators linking some artifacts and uploads to Morocco. #Yurei #Prince-Ransomware