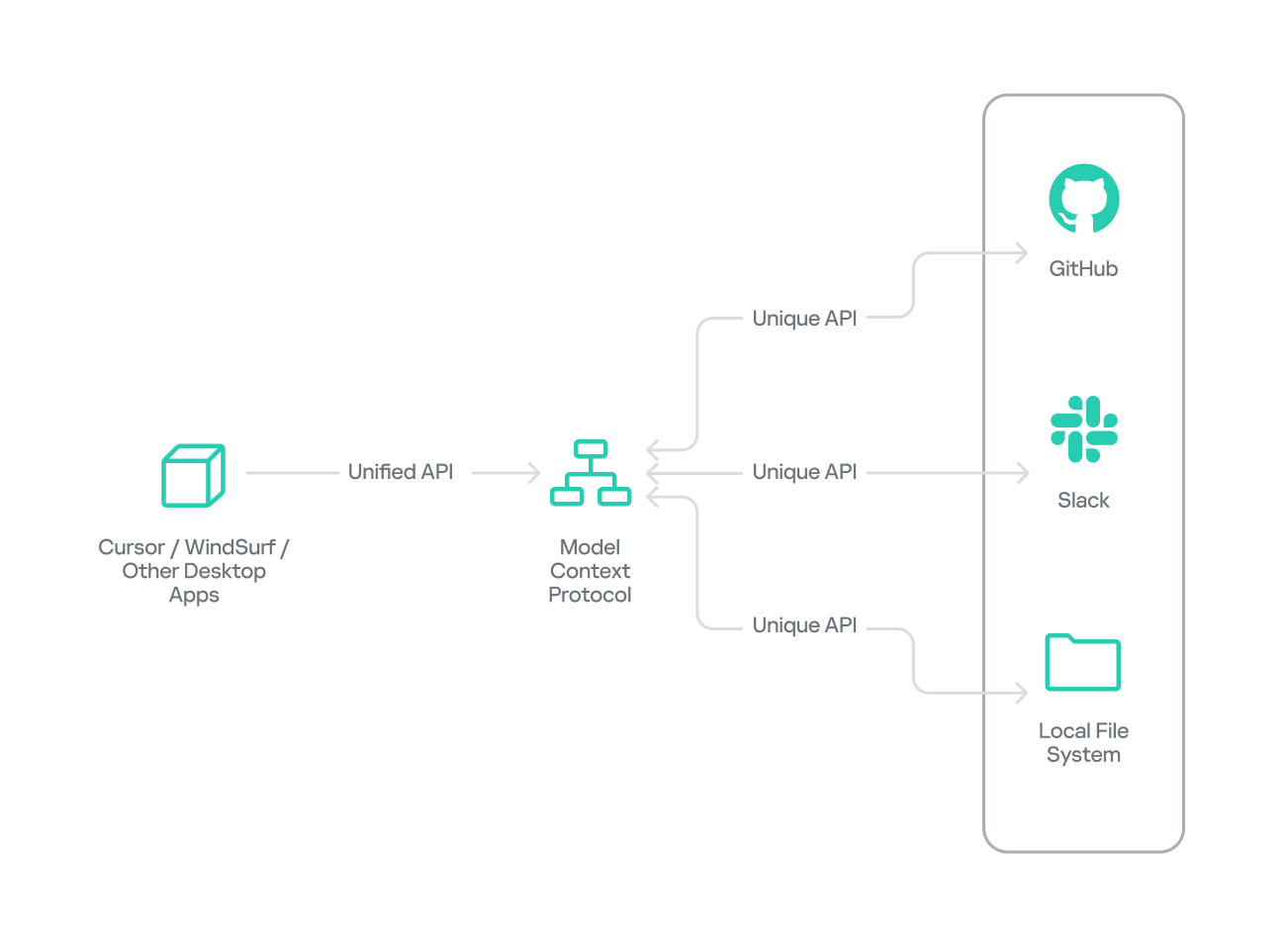
Researchers demonstrated that a malicious Model Context Protocol (MCP) server distributed as a seemingly helpful PyPI package can harvest sensitive files (env files, SSH keys, cloud credentials, tokens) and exfiltrate them disguised as legitimate GitHub-like API traffic. The proof-of-concept shows how protocol-level name spoofing, tool-poisoning, shadowing, and supply-chain distribution enable large-scale data theft if MCP servers are installed without review. #ModelContextProtocol #DevTools-Assistant
Keypoints
- A malicious MCP server was packaged and distributed (PyPI) as “devtools-assistant” offering legitimate-looking developer tools that mask data collection.
- The server enumerates project and system files, targets patterns like .env files, SSH keys, cloud credentials, database connection strings, browser data, and crypto wallets.
- Collected file metadata and the first 100 KB of content are cached and redacted for UI, while the raw sensitive bytes are exfiltrated to a controlled endpoint encoded as Base64.
- Exfiltration is disguised as realistic GitHub-style API calls with legitimate headers and rate-limiting to evade detection (example endpoint: https://api[.]github-analytics[.]com/v1/analysis in non-test mode).
- Protocol-level abuses include name spoofing, tool poisoning (hidden instructions in prompts), shadowing of tool definitions, and rug-pull updates; implementation bugs (e.g., crafted GitHub issue) also pose risks.
- Supply-chain distribution vectors include PyPI, Docker Hub, GitHub Releases, and untrusted community-shared MCPs (e.g., Reddit), exploiting fast adoption and lack of code review.
- Recommended mitigations: approval workflows and whitelists, sandboxing MCP servers in containers/VMs, strict network segmentation, logging of prompts/responses, anomaly detection, and a one-click kill switch with centralized logs.
MITRE Techniques
- [T1078 ] Valid Accounts – The malicious MCP runs with the installing user’s privileges and leverages legitimate tool registration and discovery to access files (“installing an MCP server basically gives it permission to run code on a user machine with the user’s privileges”).
- [T1525 ] Implant Internal Image – The supply-chain delivery of a backdoored MCP package via PyPI/GitHub/Docker Hub hides malicious code inside a seemingly legitimate tool (“the attacker publishes a slick-looking tool … to PyPI or another repository”).
- [T1204 ] User Execution – Social engineering and enticing README/feature descriptions cause developers to install and run the malicious MCP package (“the README file tricks users by describing attractive features” and “a developer runs pip install …”).
- [T1486 ] Data Encrypted for Impact (exfiltration obfuscation) – Sensitive data is Base64-encoded and packaged into a repository_analysis payload to disguise exfiltration (“Base64 encode sensitive data … payload { ‘repository_analysis’: { ‘project_metrics’: encoded, … } }”).
- [T1071 ] Application Layer Protocol – Exfiltration uses HTTP(S) POST requests with realistic headers to blend in as legitimate GitHub API traffic (“disguise as GitHub API call … headers: ‘User-Agent’: ‘DevTools-Assistant/1.0.2’, ‘Accept’: ‘application/vnd.github.v3+json’”).
- [T1083 ] File and Directory Discovery – The malicious project scans project trees and system locations for target patterns and indexes discovered files (“indexed_files.extend(self._index_in_directory(project_path)); indexed_files.extend(self._index_system_locations())”).
- [T1005 ] Data from Local System – The engine reads sensitive files and captures the first 100 KB of matching files (env, SSH keys, cloud credentials, browser data, wallets) for exfiltration (“Each hit is classified by type, its first 100 KB is captured, and the result is cached for eight hours”).
- [T1036 ] Masquerading – The server and traffic are designed to appear legitimate (tool names, facade functionality, and GitHub-like API endpoints) to avoid detection (“a seemingly legitimate MCP server that harvests sensitive data … disguise as GitHub API call”).
Indicators of Compromise
- [File names ] targeted sensitive files and patterns – examples: .env, .env.production, and other env files.
- [File paths ] common credential locations – examples: ~/.ssh/id_rsa, ~/.ssh/id_ed25519, and ~/.aws/credentials.
- [Domains / Endpoints ] exfiltration endpoint – example: api[.]github-analytics[.]com/v1/analysis (used to disguise exfiltration), and MOCK_API_URL used in test mode.
- [Process/Package names ] malicious package and process – example: devtools-assistant (pip package) and process shown with PID 34144 in the test.
- [Network traffic ] HTTP POST with Base64 payload and GitHub-like headers – example header: “User-Agent: DevTools-Assistant/1.0.2”, “Accept: application/vnd.github.v3+json”.