VPS abuse by threat actors enables stealthy, scalable attacks by abusing VPS infrastructure to hide origin and mimic legitimate traffic, including phishing and mailbox manipulation. Darktrace’s May 2025 investigation links Hyonix, Host Universal, and other VPS providers to campaigns, highlighting the need for behavioral detection and autonomous response to block unusual VPS-based activity. #Hyonix #HostUniversal #Mevspace #Hivelocity #Darktrace
Keypoints
- VPS infrastructure is exploited to bypass geolocation-based defenses and IP reputation checks for stealthy campaigns.
- Attacks leverage credential misuse, session hijacking, and anomalous logins from rare endpoints to gain and maintain access.
- New inbox rules and obfuscated rule names help attackers persist and conceal malicious mailbox activity.
- Coordinated activity across multiple users and SaaS environments indicates a shared infrastructure and technique set.
- Behavioral detection and autonomous response are essential to detect rare logins, mailbox rule changes, and abrupt SaaS activity.
MITRE Techniques
- [T1566.001] Spearphishing Attachment – Initial access is described as likely achieved via phishing, with the article noting ‘initial access in this case was likely achieved through a similar phishing or account hijacking method.’
- [T1078] Valid Accounts – Credential misuse evidenced by logins from rare endpoints and session hijacking.
- [T1098] Account Manipulation – ‘attempts to modify account recovery settings’ observed on one account.
- [T1098.002] Exchange Email Rules – ‘creation of new email rules’ and ‘inbox rules with obfuscated names’ used to maintain access and evade review.
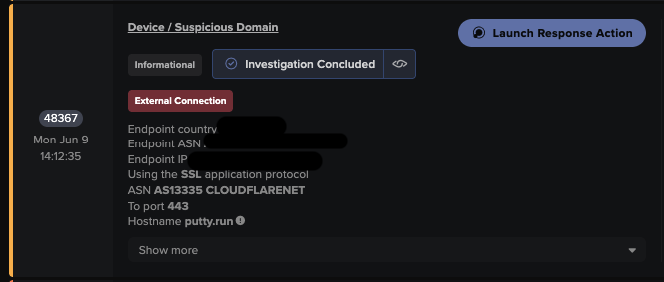
- [T1071.001] Web Protocols – ‘DNS requests from a device to a suspicious domain, which began prior the observed email compromise’ indicate use of web protocols for command and control or exfiltration.
- [T1036] Masquerading – ‘inbox rules with obfuscated names’ used to mask malicious activity.
- [T1562] Impair Defenses – ‘Autonomous Response capability was not enabled in either customer environment during these attacks. As a result, no automated containment actions were triggered’.
- [T1562.001] Disable or Modify Tools – Lack of automated containment suggests the potential to disable or modify defensive tooling.
- [T1556] Modify Authentication Process – ‘MFA bypass’ implications supported by ‘MFA satisfied via token claims, further indicating session hijacking’.
- [T1087] Account Discovery – Anomalous login patterns from rare endpoints imply discovery of affected accounts.
- [T1531] Account Access Removal – Deletion of emails to conceal phishing activity and maintain access.
Indicators of Compromise
- [IP] context – 38.240.42.160, 194.49.68.244
- [IPv6] context – 2a02:748:4000:18:0:1:170b:2524
- [File Name] context – SplashtopStreamer.exe