A new ToneShell backdoor variant tied to Mustang Panda was delivered via DLL sideloading inside ZIP archives and uses anti-analysis stalling, GUID-based host IDs, a rolling-XOR C2 scheme, and a minimal command set while targeting Myanmar. New indicators include DLL and archive hashes and a C2 at 146.70.29[.]229:443 that can aid threat hunting. #ToneShell #MustangPanda #146.70.29.229
Keypoints
- The backdoor is delivered via DLL sideloading inside signed executables bundled in ZIP archives (example archive names include update.zip and a Burmese-named ZIP referencing TNLA).
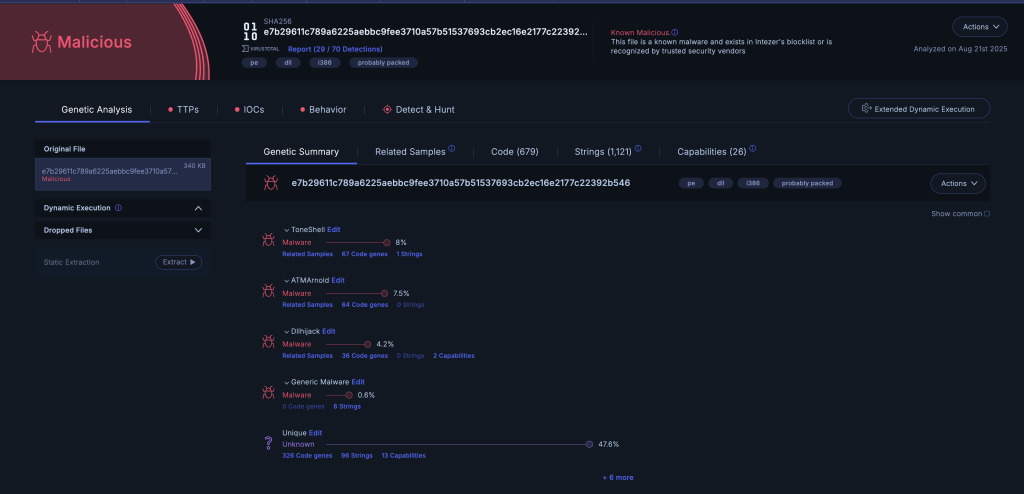
- Samples: SkinH.dll (sha256 e7b29611c789a6225aebbc9fee3710a57b51537693cb2ec16e2177c22392b546) and node.dll variant (sha256 a58868b3d50b775de99278eeb14da8b7409b165aa45313c6d9fa35ac30d2cda2).
- Persistence via copying to %APPDATA%svchosts.exe and registering a Task Scheduler task named dokanctl that runs every minute.
- Anti-analysis techniques include repeated file churn, randomized sleep loops, tick-count checks, opaque string comparisons (large filler strings copied from OpenAI and Pega AI sites), junk arithmetic, and decoy API use to frustrate sandboxes and analysts.
- Networking uses a TLS-like 5-byte header (17 03 03 + 2-byte length with only low byte honored) and a 256-byte rolling XOR for payload obfuscation; observed C2: 146.70.29[.]229:443.
- GUID-based host ID generation: attempts to read 16 bytes from C:ProgramDataSystemRuntimeLag.inc, else generates via CoCreateGuid or LCG fallback and persists the seed to that file.
- Code reuse and hybrid characteristics align this sample with prior ToneShell variants (mixing elements from both first and second versions) and reflect Mustang Panda’s continued targeting of Myanmar for geopolitical objectives.
MITRE Techniques
- [T1055 ] Process Injection – The backdoor checks parent process image paths (e.g., GoogleDrive) and performs execution control checks to avoid infecting certain processes; “it enumerates processes to identify the parent process, retrieves its image path, and verifies whether it contains GoogleDrive.”
- [T1547.001 ] Registry Run Keys / Startup Folder (Task Scheduler persistence) – Registers a scheduled task named dokanctl to execute svchosts.exe every minute for persistence: “the task is registered in the root folder with the name dokanctl” and set to run %APPDATA%svchosts.exe.
- [T1095 ] Non-Standard Port / Protocol – Uses a TLS-like record header and a rolling-XOR obfuscation over TCP to blend C2 traffic: “Each packet begins with the fixed bytes 17 03 03 … the malware XOR-decodes it in place with a 256-byte rolling key.”
- [T1070.004 ] Indicator Removal on Host (File deletion loops as anti-analysis) – Repeatedly creates, writes, closes, and deletes temporary files to consume time and confuse sandbox artifacts: “creating, writing, closing, and deleting a temporary file in a loop with Sleep(100) delays.”
- [T1497.001 ] Time-of-Day Checks – Uses GetTickCount64 and jittered sleeps to wait until at least 10 seconds of wall-clock time have elapsed to evade short-lived sandboxes: “waiting until at least 10 seconds of wall-clock time has elapsed.”
- [T1027 ] Obfuscated Files or Information – Employs API function hashing (rolling hash) and embedded filler strings to obscure intent and impede static analysis: “uses a custom API-resolving scheme based on a simple rolling hash” and “large embedded string buffers … serve as filler to inflate the binary.”
Indicators of Compromise
- [File Hash ] ToneShell DLL samples – e7b29611c789a6225aebbc9fee3710a57b51537693cb2ec16e2177c22392b546 (SkinH.dll), a58868b3d50b775de99278eeb14da8b7409b165aa45313c6d9fa35ac30d2cda2 (node.dll)
- [Archive Hash ] Malicious ZIP archives – 543024edc9f160cc1cedcffc3de52bfa656daa0ec9ed351331d97faaa67d0d99 (update.zip), 1272a0853651069ed4dc505007e8525f99e1454f9e033bcc2e58d60fdafa4f0 (Burmese-named ZIP)
- [Domain/IP ] Command-and-control address – 146.70.29[.]229:443 (observed C2 endpoint used with TLS-like header and rolling-XOR payloads)
- [File Path ] GUID persistence file – C:ProgramDataSystemRuntimeLag.inc used to store 16-byte GUID seed for host identification
- [File Name ] Installed persistence executable – %APPDATA%svchosts.exe and auxiliary DLLs msvcr100.dll, msvcp100.dll, mfc100.dll (copied into the AppData folder)
Read more: https://intezer.com/blog/frankenstein-variant-of-the-toneshell-backdoor-targeting-myanmar