Yurei is a newly observed ransomware group that launched operations on September 5, targeting organizations in Sri Lanka, India, and Nigeria and using a double-extortion model to encrypt files (adding a .Yurei extension) and exfiltrate data via a darknet blog and negotiation chat on an .onion site. Analysis shows Yurei’s binary is derived with minor modifications from the open‑source Prince‑Ransomware (written in Go), inherits flaws such as not deleting Volume Shadow Copies, and exhibits indicators linking some artifacts and uploads to Morocco. #Yurei #Prince-Ransomware
Category: Threat Research
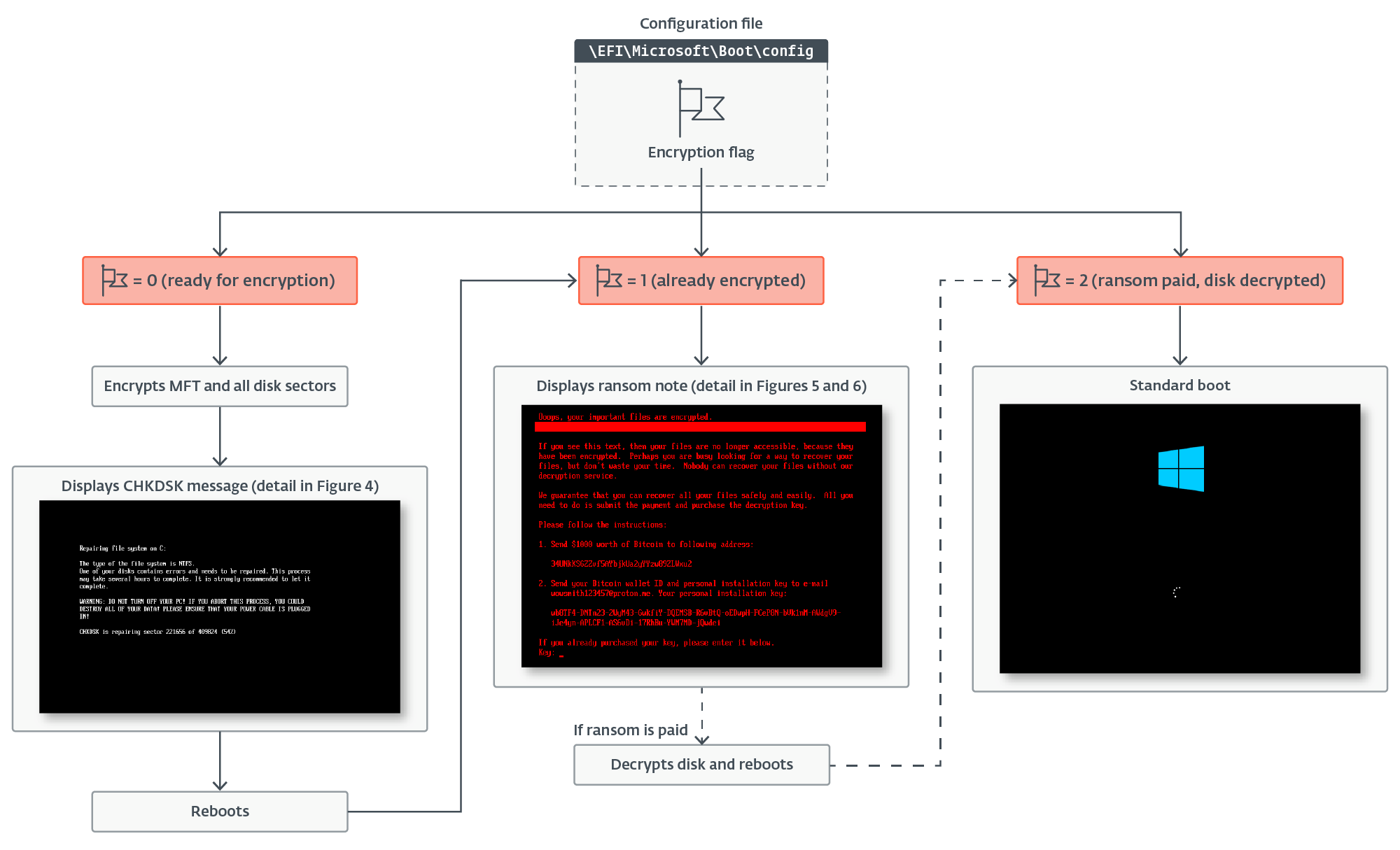
ESET Research discovered HybridPetya, a Petya/NotPetya copycat uploaded to VirusTotal in February 2025 that can install a UEFI bootkit to encrypt NTFS Master File Tables and, in one variant, weaponize CVE‑2024‑7344 (via a cloak.dat file) to bypass UEFI Secure Boot on vulnerable systems. ESET telemetry shows no active in-the-wild spread and the samples lack NotPetya’s aggressive network propagation. #HybridPetya #CVE-2024-7344
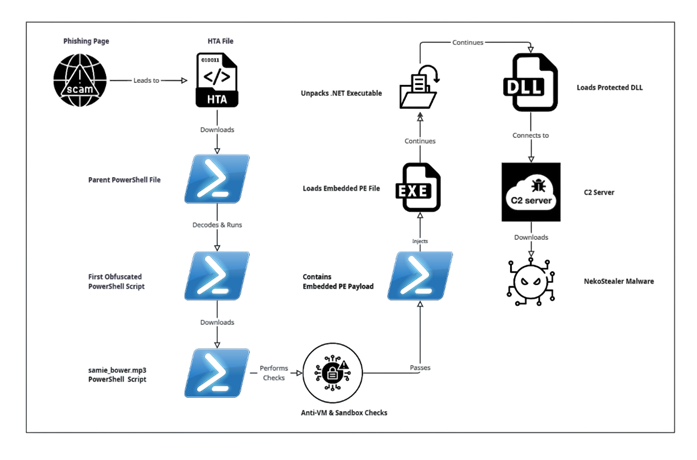
Attackers are using HijackLoader—distributed via CAPTCHA-based phishing pages, fake installers, malvertising and pirated sites—to deliver multi-stage obfuscated PowerShell loaders that unpack and inject a packed .NET PE which downloads info-stealers such as NekoStealer, DeerStealer, and Lumma. Observed techniques include process doppelgänging, unhooking system DLLs, direct syscalls under WOW64, call-stack spoofing and extensive anti-VM checks. #HijackLoader #NekoStealer
EvilAI is an active global campaign that disguises Node.js-based trojans as legitimate AI or productivity applications—using professional UIs and code-signing—to steal browser credentials, maintain AES-encrypted C2 communications, and persist via scheduled tasks, registry Run keys, and Start Menu shortcuts. Telemetry shows rapid, widespread infections across Europe, the Americas, and AMEA, heavily…

The report details multiple cyber incidents affecting financial organizations, including a 90 GB database leak from an offshore services firm, an 845 GB ransomware claim by D4RK 4RMY against a Japanese financial group, and DDoS-related activity involving hacktivist group Keymous targeting Iraqi banks. It also highlights recommended defensive measures and provides…

Vladimir Putin’s foreign policy is driven by a reactive worldview shaped by his life experiences, prioritizing centralized power, strategic flexibility, and the restoration of a Russian sphere of influence using a mix of diplomatic, covert, cyber, and kinetic tools. Western and allied organizations should monitor Kremlin rhetoric and Western policy actions to anticipate escalations and adopt heightened cyber, physical, and personnel protections. #WhisperGate #Sandworm

CyberVolk is a pro‑Russia ransomware group that emerged in May 2024 and has targeted public institutions and critical infrastructure in countries such as Japan, France, and the UK, using Telegram for communication. The ransomware uses AES‑256 GCM and ChaCha20‑Poly1305 with a per‑file nonce that is not stored, making decryption impossible; #CyberVolk…

Scammers are sending SMS messages impersonating state vehicle agencies (BMVs/DMVs) claiming outstanding traffic tickets and urging immediate payment via malicious links that harvest payment and identity data. Affected states include Ohio, Indiana, Colorado, West Virginia, Hawaii, Arizona, and New Hampshire, with rapidly rotating scam domains used to host lookalike payment pages….
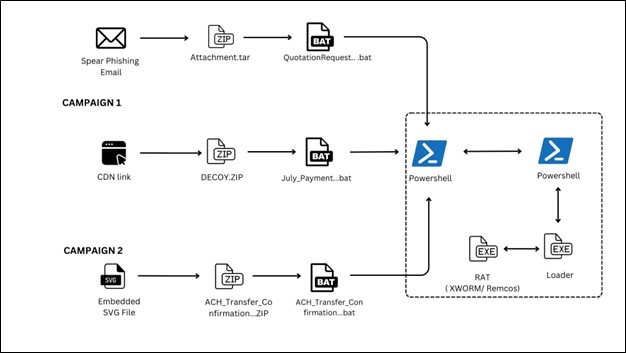
Recent campaigns use obfuscated BAT-based loaders and SVG-embedded JavaScript to deliver in-memory Remote Access Trojans, notably XWorm and Remcos, often via ZIP archives hosted on platforms like ImageKit. The attacks rely on PowerShell decoding, AMSI/ETW disabling, and encrypted .NET/shellcode loaders to achieve fileless execution and persistence. #XWorm #Remcos

VirusTotal Code Insight added support for SWF and SVG and immediately uncovered an undetected malware campaign using SVG files that impersonated the Colombian justice system by executing embedded JavaScript to deliver a phishing page and a malicious ZIP dropper. A retrohunt using a simple YARA signature based on Spanish comments found 523 related SVG samples dating back to August 14, 2025, all previously undetected by antivirus engines. #SVG #ColombianFiscalia

Healthcare organizations faced a sustained surge of ransomware attacks in 2025 that disrupted operations, forced patient-care delays, and exposed millions of records. Prominent families like INC, INTERLOCK, Akira, Qilin, RansomHub, and Warlock targeted hospitals worldwide, using phishing, exploited CVEs, Cobalt Strike, Mimikatz, and Rclone to persist, steal, and extort data. #INC #INTERLOCK

The ACSC warns that CVE-2024-40766 is being actively exploited in SonicWall SSL VPN appliances, enabling unauthorized access and in some cases causing firewall crashes across Gen 5–7 devices. Immediate actions recommended include applying SonicWall firmware updates, resetting local SSLVPN passwords (especially after migrations), enabling MFA, and blocking identified malicious IPs. #CVE-2024-40766 #Akira

BlackNevas is a ransomware group active since November 2024 that targets organizations across Asia-Pacific, Europe, and North America, using AES to encrypt files and then encrypting the AES key with RSA, rendering files practically undecryptable without breaking RSA. The group uses distinctive filename patterns (including a “trial-recovery” prefix for some file…

Eighteen widely used npm packages were pushed with malicious updates that inject obfuscated JavaScript into clients, intercepting browser network calls and wallet APIs to rewrite crypto payment destinations and transaction data to attacker-controlled addresses. The compromise originated from a phishing domain (npmjs.help) used against maintainers, and remediation includes checking versions, reinstalling packages, and using tools like Aikido SafeChain. #npmjs.help #simple-swizzle

A cluster of phishing attacks targeting Pakistan used MSC files with GrimResource to execute obfuscated JavaScript and deliver Mythic-based remote access trojans, with indicators linking the activity to Patchwork using a Dark Samurai/OceanLotus false-flag. Key artifacts include DismCore.dll (Mythic RAT), MSC/HTML lure files, and multiple malicious domains/C2 URLs. #Patchwork #Mythic
