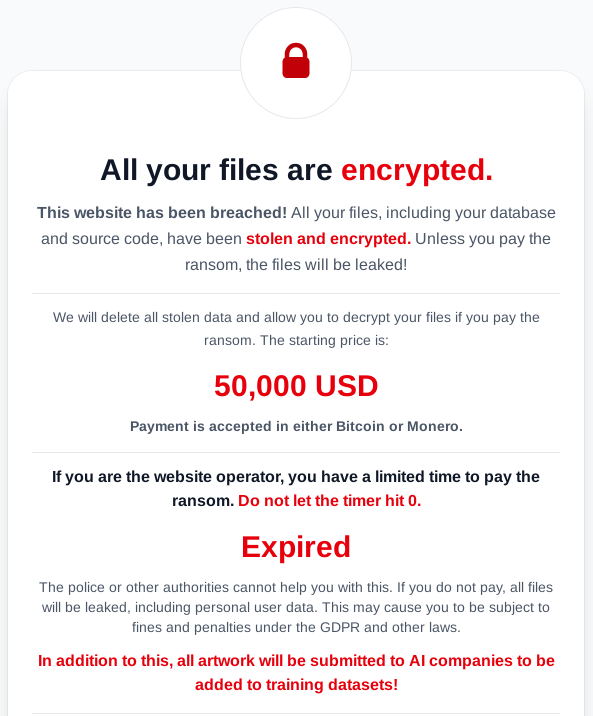
The LunaLock ransomware group claimed to have stolen and encrypted data from a freelance artist-client platform and threatened to publish the data if a ransom is not paid. They added a new extortion dimension by saying they would sell or hand over the stolen artworks to AI companies for model training if the victim does not pay. #LunaLock #AI
Category: Threat Research

Zscaler ThreatLabz uncovered a malware campaign from early May 2025 targeting Chinese-speaking users that delivers three RAT families: ValleyRAT, FatalRAT, and a newly identified kkRAT which combines features from Ghost RAT and Big Bad Wolf. The campaign uses phishing pages on GitHub Pages, multi-stage shellcode loaders, BYOVD to disable AV/EDR callbacks, and kkRAT capabilities such as clipboard crypto-hijacking and installing RMM tools like Sunlogin and GotoHTTP. #kkRAT #GhostRAT #BigBadWolf #ValleyRAT #FatalRAT #Sunlogin #GotoHTTP
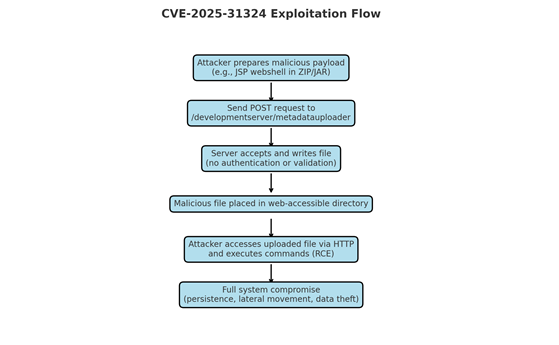
CVE-2025-31324 is a critical unauthenticated arbitrary file upload vulnerability in the SAP NetWeaver Development Server’s metadatauploader endpoint that allows attackers to upload ZIP/JAR payloads (application/octet-stream) which are parsed as trusted model metadata and lead to remote code execution. Active exploitation since March 2025 and a public exploit release in August 2025 resulted in widespread attacks deploying JSP web shells and a Linux backdoor named Auto-Color against exposed SAP NetWeaver Dev servers. #CVE-2025-31324 #Auto-Color #ScatteredLAPSUS$Hunters
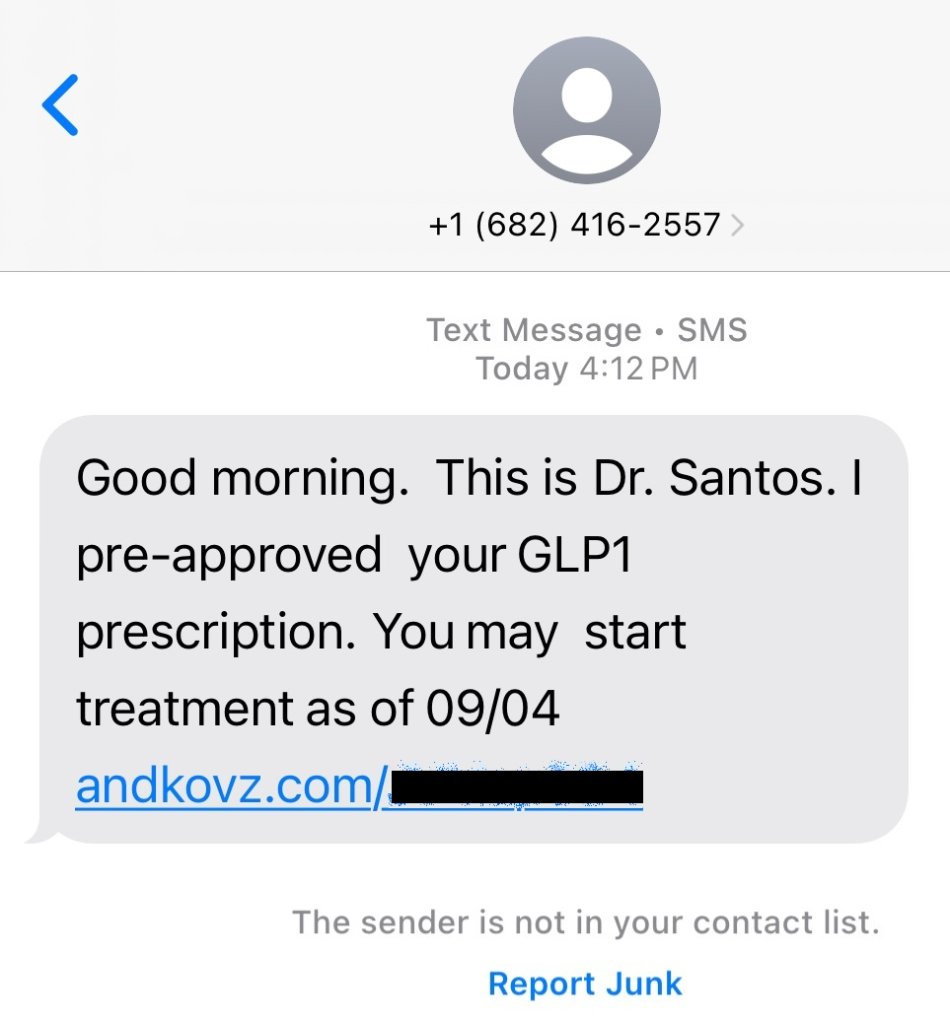
A phishing SMS impersonating a doctor offers pre-approved GLP-1 weight-loss prescriptions and links to a tracking subdomain that redirects to fraudulent pharmacy sites selling unapproved compounded GLP-1 products. Threat infrastructure included track.savezmeet[.]com and MyStartHealth.com; Malwarebytes telemetry shows track.savezmeet[.]com observed since August 2 and MyStartHealth.com blocked since March 2025. #track.savezmeet #MyStartHealth.com…
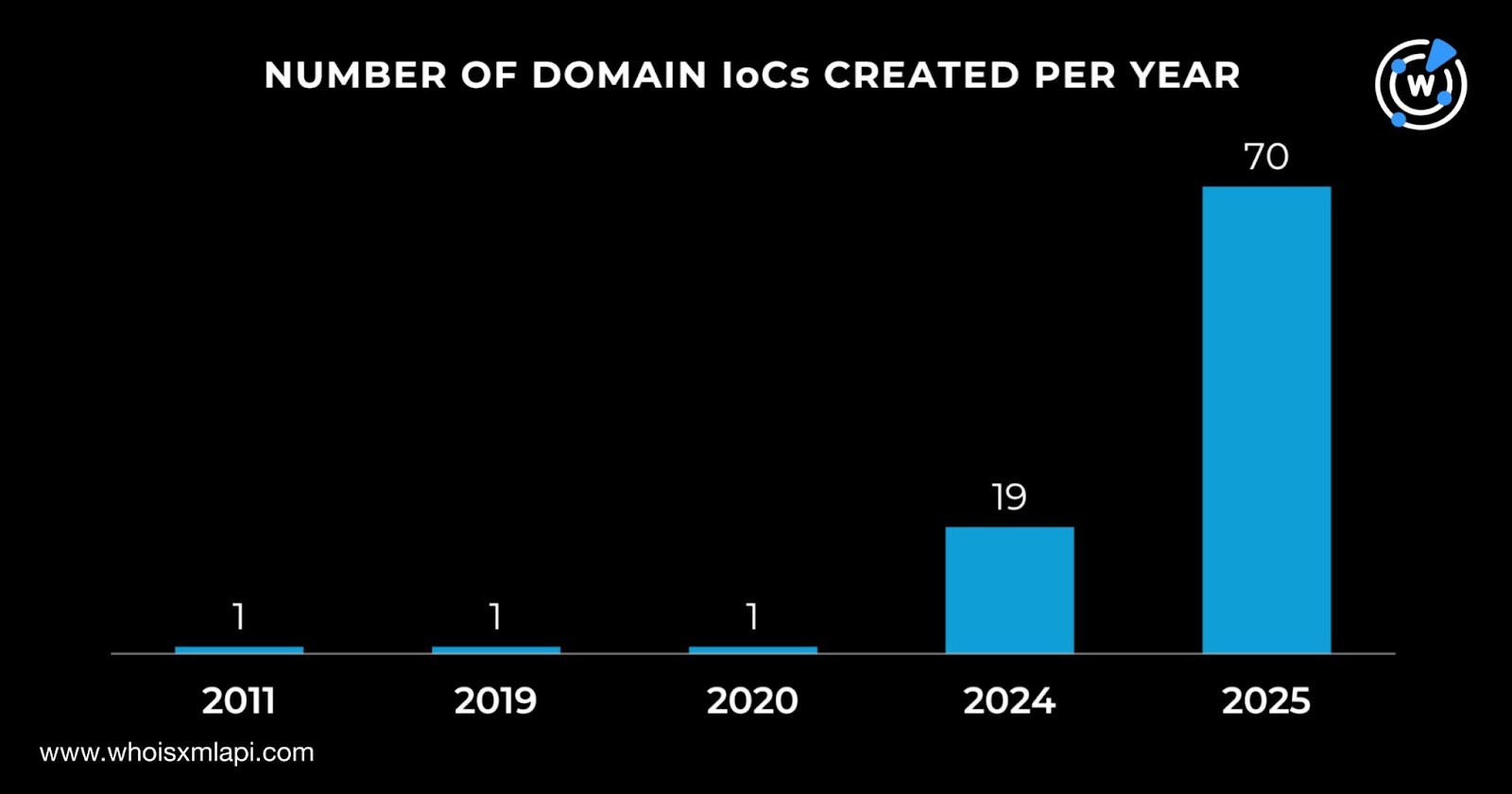
Check Point Research uncovered the JSCEAL campaign using malicious ads to distribute fake Node.js-based cryptocurrency trading apps, with about 35,000 malicious ads viewed millions of times in the EU during H1 2025. Researchers identified 94 domain IoCs and extensive DNS/WHOIS connections—highlighting mass registrations, typosquatting, and thousands of client IPs communicating with IoCs. #JSCEAL #CheckPointResearch
Lazarus Group escalated its 2025 operations with campaigns that use fake IT workers, fraudulent job interviews, and hijacked open-source packages to steal credentials, crypto, and proprietary code. ANY.RUN’s Interactive Sandbox and Threat Intelligence Lookup are presented as tools SOC teams can use to detect malware families like InvisibleFerret, OtterCookie, and PyLangGhost…
A malicious ISO named Servicenow-BNM-Verify.iso uploaded from Malaysia contains a benign Palo Alto executable that side-loads a hidden malicious DLL (libwaapi.dll) which injects and executes a compressed, obfuscated DLL that phones home to logsapi.azurewebsites[.]net. LNK metadata reveals creator machine and user details (desktop-rbg1pik, john.GIB) and points to a development path suggesting the actor tested the chain locally. #libwaapi.dll #logsapi.azurewebsites.net

A threat actor inadvertently installed the Huntress EDR agent on their primary operating machine, allowing Huntress to observe detailed browser history, tooling, and workflows—revealing use of AI, searches for Evilginx instances, residential proxies, and recon across banking and other sectors. Huntress used these telemetry and retroactive hunts to tie the host to known malicious activity, identify compromised identities, and produce high-confidence detections against the attack infrastructure. #Evilginx #Make.com
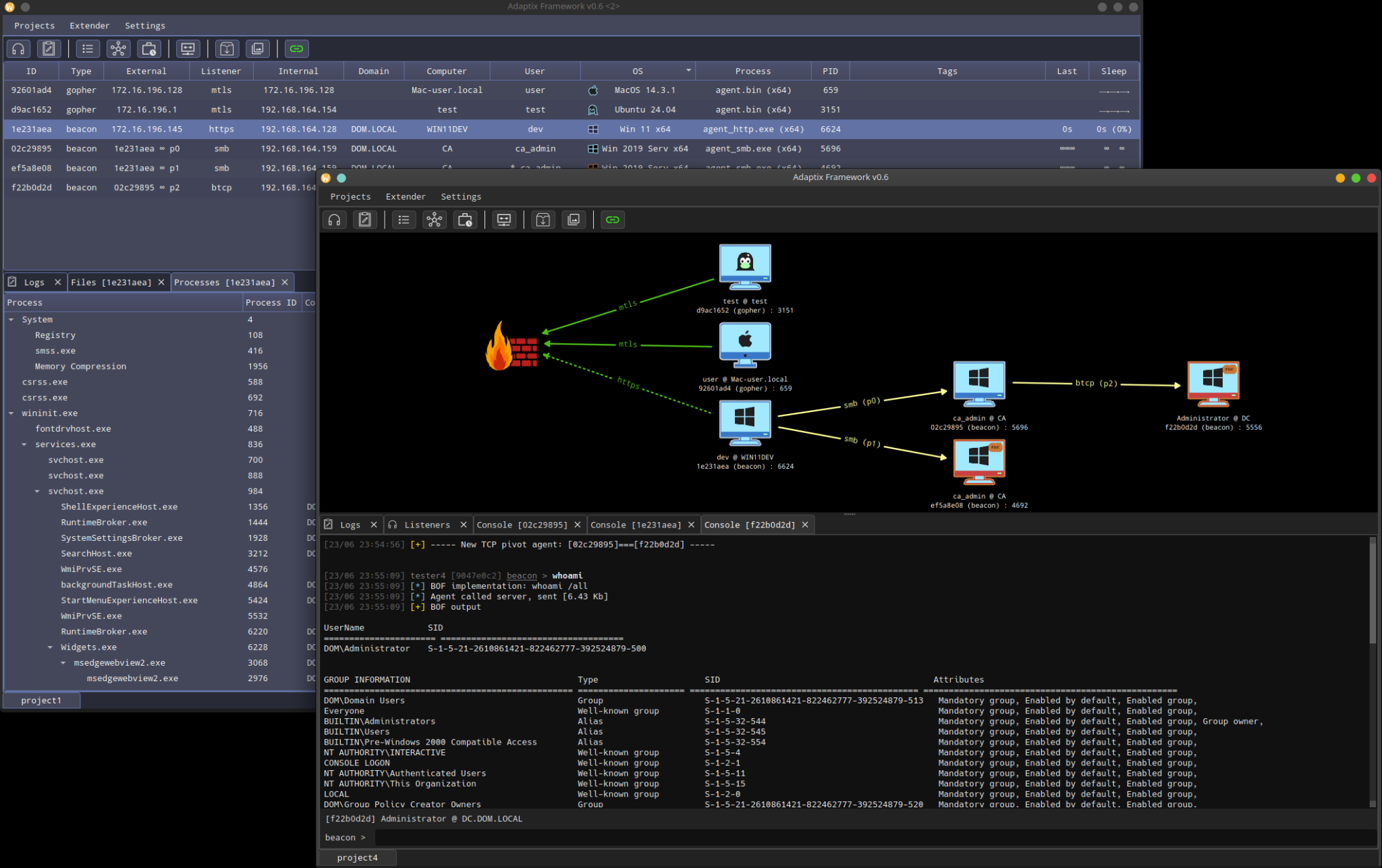
Unit 42 observed AdaptixC2—an open-source, modular post-exploitation framework—being used in the wild to execute commands, transfer files, exfiltrate data, and maintain persistence via in-memory shellcode and DLL hijacking. Key artifacts include multiple PowerShell loader hashes and numerous C2 domains such as tech-system[.]online, and the attacks show social engineering via Microsoft Teams…
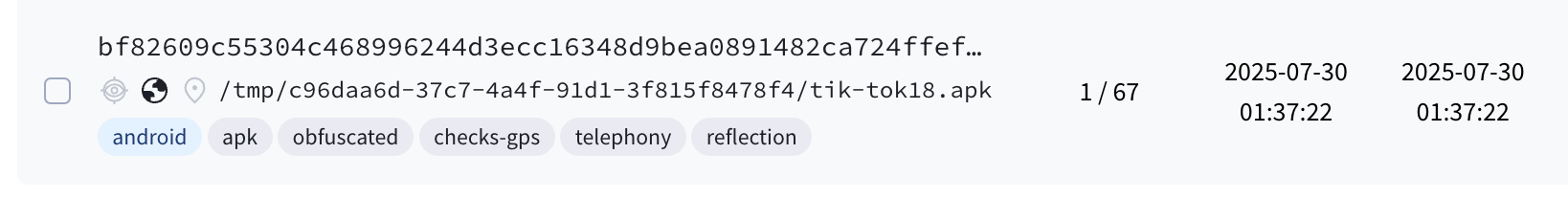
A newly discovered Android trojan named RatOn combines NFC relay attack capabilities (via NFSkate), remote access features, overlay-based ransom/deception pages, and automated money transfer (ATS) functionality targeting a Czech bank and several cryptocurrency wallets. The campaign used adult-themed domains to deliver a multi-stage dropper that abuses Accessibility and Device Admin privileges…
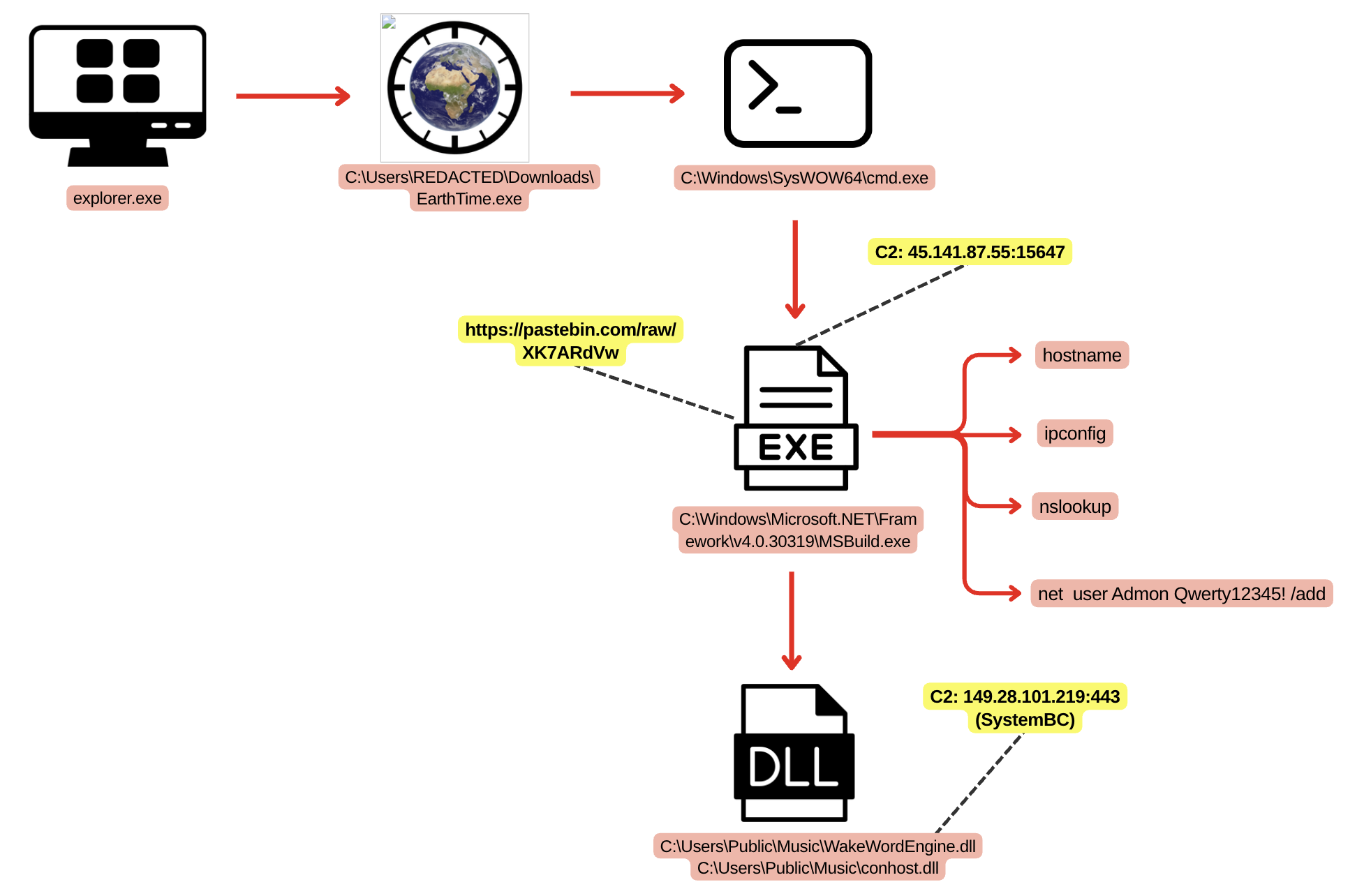
A user-executed malicious EarthTime installer led to deployment of SectopRAT, SystemBC, and later the Betruger backdoor, enabling reconnaissance, credential theft (including DCSync and Veeam credential dumping), lateral movement via RDP/Impacket, and cleartext exfiltration to an FTP host. Artifacts and tooling link the intrusion to multiple ransomware operations—Play, RansomHub, and DragonForce—suggesting a…

Cyble CRIL identified the Luno Linux botnet (LunoC2), a modular, actively evolving framework that combines crypto-mining (xmrig) and dozens of tunable DDoS attack methods with persistence, self-update, and strong anti-analysis features. Key infrastructure and artifacts include domains main.botnet[.]world, botnet[.]world, fallback IP 111[.]0.0.2, and a hardcoded Monero wallet 4B9gxLDjJP2ZNHm8R6k3hUTT9ozmArqUggecuyDntnWKYS9h3HLJAzs8TV2YP8P7VkMshJxtPnJJ5iZRQmncKWyVAwadHH2. #LunoC2 #main.botnet.world

This investigation links Clop ransomware infrastructure (pubstorm[.]com / pubstorm[.]net) to IPs hosted in AS209132 and AS209272 owned by Alviva Holding Limited, and traces Alviva to a Seychelles-registered shell company network connected to Alpha Consulting and a beneficial owner, Denis Nachaev. Evidence includes WHOIS, VT records, ASN peer relationships (Verdina Ltd, FOP Gubina Lubov Petrivna), Pandora Papers/ICIJ leak references, and historical abuse tied to Cobalt Strike and other criminal services. #Clop #AlvivaHoldingLimited
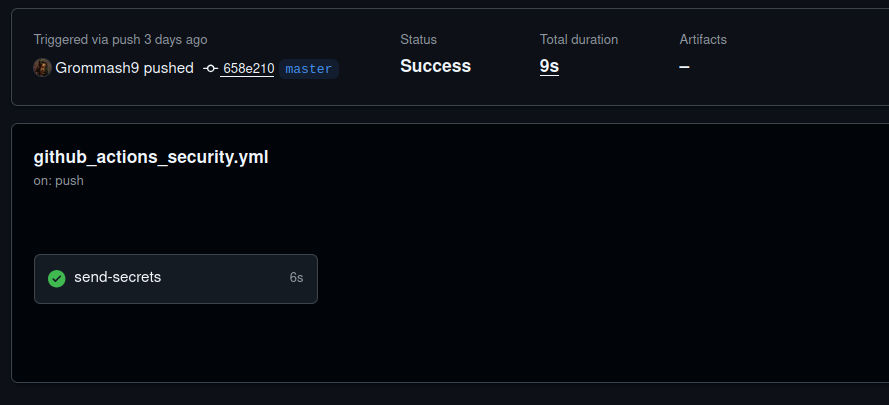
On September 2, 2025, an attacker compromised multiple GitHub accounts to inject malicious GitHub Actions workflows that exfiltrated CI/CD secrets (e.g., PyPI, NPM, DockerHub, GitHub tokens) to hxxps://bold-dhawan.45-139-104-115.plesk.page leading to 3,325 leaked secrets across hundreds of repositories. Rapid disclosure and remediation by GitGuardian, affected maintainers, and registries (PyPI read-only action, reports to GitHub/NPM/PyPI) limited impact with no evidence of malicious PyPI releases; affected keywords include #FastUUID #bold-dhawan

Recent weeks have seen escalating data theft targeting Salesforce instances through supply chain attacks such as the Salesloft Drift incident attributed to UNC6395, with threat actors focused on exfiltrating Account, Contact, Case, and Opportunity records for financial gain. Telegram channels linked to groups like Muddled Libra/Scattered Spider and Bling Libra have…