Lazarus Group escalated its 2025 operations with campaigns that use fake IT workers, fraudulent job interviews, and hijacked open-source packages to steal credentials, crypto, and proprietary code. ANY.RUN’s Interactive Sandbox and Threat Intelligence Lookup are presented as tools SOC teams can use to detect malware families like InvisibleFerret, OtterCookie, and PyLangGhost and to collect IOCs for proactive defenses. #InvisibleFerret #OtterCookie #PyLangGhost
Keypoints
- Lazarus Group posed as remote IT workers since 2024 to gain insider access, compromising over 100 U.S. companies and causing direct financial losses such as a $900,000 cryptocurrency theft.
- Operation 99 (“Contagious Interview”) uses fake job/partnership interviews and malicious coding tests hosted on repositories to deliver malware and steal credentials and crypto.
- Lazarus has been hijacking open-source packages (GitHub, PyPI) since September 2024, with 230+ malicious packages identified in 2025 affecting approximately 36,000 firms globally.
- Supply chain attacks include high-profile incidents like the ByBit $1.5 billion theft that began with a compromised developer environment at Safe{Wallet} via a malicious Docker project.
- Notable Lazarus malware families in 2025: InvisibleFerret (keylogging, screen capture, C2 persistence), OtterCookie (token/session theft via malicious packages), and PyLangGhost RAT (remote access, long-term espionage).
- ANY.RUN’s Interactive Sandbox enables hands-on, fast detection of these threats, exposing behaviors, collecting IOCs, and reducing MTTR for SOC teams.
- Threat Intelligence Lookup offers free, fresh IOCs and sandbox reports attributed to Lazarus, helping refine SIEM/IDS/EDR detection rules and improve proactive defenses.
MITRE Techniques
- [T1586] Compromise Software Supply Chain – Lazarus “embedded malicious backdoors in cloned open-source software packages on repositories like GitHub and PyPI” [“embedded malicious backdoors in cloned open-source software packages on repositories like GitHub and PyPI”].
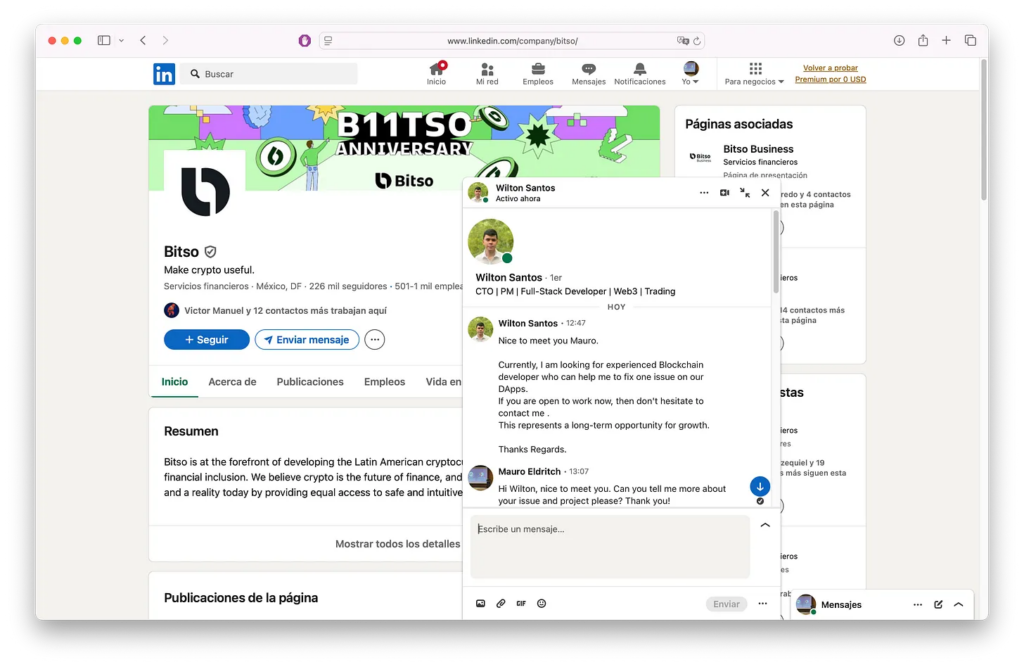
- [T1193] Spearphishing via Service – Use of fake job interviews and recruiter messages on LinkedIn/Telegram/Calendly to lure victims to malicious repos and executables [“posing as recruiters on LinkedIn, Telegram, or Calendly, Lazarus lures victims with fraudulent coding tests hosted on malicious GitLab repositories”].
- [T1204] User Execution – ClickFix tactic presenting fake pages or errors prompting victims to run commands or scripts (social engineering to execute malware) [“a fake page instructing them to run a malicious script… users were often asked to paste and run a command on their computer”].
- [T1059] Command and Scripting Interpreter – Attackers prompt victims to run commands/scripts that install malware (PyLangGhost and other RATs) [“a fake error, prompting the user to run a command… asked to paste and run a command on their computer”].
- [T1105] Ingress Tool Transfer – Downloading payloads from external servers to deploy OtterCookie and other malware [“payload being downloaded from an external server”].
- [T1078] Valid Accounts – Use of stolen or AI-enhanced identities and insider access by fake IT workers to infiltrate organizations [“deploying North Korean operatives posing as legitimate remote IT workers… using stolen or AI-enhanced identities”].
- [T1027] Obfuscated Files or Information – Use of evasion techniques like fake errors and try/catch blocks to hide malicious downloads and evade signature detection [“use a fake error and a try/catch block to download and run a piece of malicious code… may escape detection by signature-based solutions”].
Indicators of Compromise
- [Malicious Packages] Hijacked open-source repositories – examples: malicious PyPI/GitHub packages (230+ packages identified), affecting developers and downstream supply chains.
- [File Names / Executables] Fake installers and Zoom-like executables – examples: fake Zoom executables sent to C-suite targets, malicious Docker project used against Safe{Wallet}.
- [Network / Payload URLs] External payload download locations – example: payload downloaded from an external server used to deploy OtterCookie; sandbox reports include command-and-control endpoints (and other server URLs).
- [Sessions / Authentication Tokens] Stolen tokens and session data – examples: authentication tokens and session data exfiltrated by OtterCookie, leading to account takeover and bypassed authentication.
- [Campaign Artefacts] Social engineering lures and staging repos – examples: malicious GitLab repositories hosting fraudulent coding tests, Calendly/LinkedIn recruiter pages used in Contagious Interview campaign.
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/lazarus-group-attacks-2025/