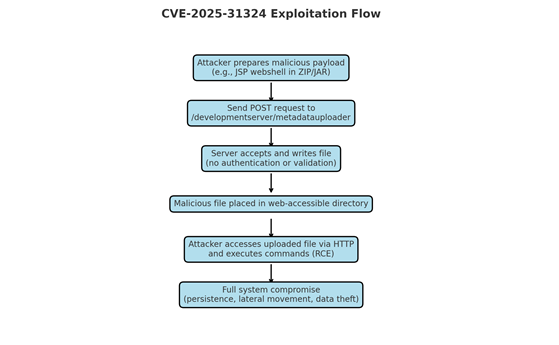
CVE-2025-31324 is a critical unauthenticated arbitrary file upload vulnerability in the SAP NetWeaver Development Server’s metadatauploader endpoint that allows attackers to upload ZIP/JAR payloads (application/octet-stream) which are parsed as trusted model metadata and lead to remote code execution. Active exploitation since March 2025 and a public exploit release in August 2025 resulted in widespread attacks deploying JSP web shells and a Linux backdoor named Auto-Color against exposed SAP NetWeaver Dev servers. #CVE-2025-31324 #Auto-Color #ScatteredLAPSUS$Hunters
Keypoints
- CVE-2025-31324 enables unauthenticated arbitrary file upload via the /developmentserver/metadatauploader endpoint, leading to remote code execution in SAP NetWeaver Development Server.
- The vulnerability arises from improper validation of uploaded model files and trusting Content-Type: application/octet-stream, allowing PK-prefixed ZIP/JAR payloads to be processed as model metadata.
- Active exploitation observed March–April 2025 with JSP web shells (helper.jsp, cache.jsp, random .jsp names) and Linux backdoor Auto-Color; public exploit release in August 2025 increased automated attacks.
- Confirmed impacts include persistent footholds, reverse shells, file manipulation, data exfiltration, and lateral movement across multiple sectors (manufacturing, retail, telecom) with at least 8 large enterprise intrusions.
- Indicators include POST requests to /developmentserver/metadatauploader with application/octet-stream bodies beginning with PK, specific JSP webshell hashes, and modified .properties files in upload paths.
- Mitigations: apply SAP September 2025 security updates, restrict development server exposure, deploy IPS/IDS rules matching CONTENTTYPE=MODEL and PK-prefixed binaries, and monitor SAP processes for unexpected child processes.
- Over 1,200 exposed SAP NetWeaver Dev servers showed exploit attempts on Shodan, highlighting the scale and urgency for patching and monitoring.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – The metadatauploader endpoint was exploited to upload malicious model files: ‘POST /developmentserver/metadatauploader requests’ and server accepted application/octet-stream payloads beginning with PK.
- [T1059] Command Execution – Uploaded web shells (helper.jsp, cache.jsp, random .jsp files) and backdoors (Auto-Color) enabled command execution and reverse shells: ‘attackers uploading web shells like helper.jsp, cache.jsp, or randomly-named .jsp files’.
- [T1105] Ingress Tool Transfer – Attackers transferred malicious ZIP/JAR payloads containing bytecode and model definitions into SAP servers: ‘Begin with PK (ZIP header), embedding .properties + compiled bytecode’.
- [T1071.001] Application Layer Protocol: Web Protocols – Exploitation used HTTP POST to the metadatauploader endpoint with Content-Type: application/octet-stream: ‘Content-Type: application/octet-stream with PK-prefixed binary content’.
Indicators of Compromise
- [File Hash] Webshell file hashes – 1f72bd2643995fab4ecf7150b6367fa1b3fab17afd2abed30a98f075e4913087 (helper.jsp), 794cb0a92f51e1387a6b316b8b5ff83d33a51ecf9bf7cc8e88a619ecb64f1dcf (cache.jsp).
- [File Hash] Additional webshell examples – 0a866f60537e9decc2d32cbdc7e4dcef9c5929b84f1b26b776d9c2a307c7e36e (rrr141.jsp), 4d4f6ea7ebdc0fbf237a7e385885d51434fd2e115d6ea62baa218073729f5249 (rrxx1.jsp).
- [HTTP URI] Exploit URI and header pattern – POST to /developmentserver/metadatauploader?CONTENTTYPE=MODEL&CLIENT=1 with Content-Type: application/octet-stream.
- [Network Artifact] Malicious HTTP body pattern – Binary HTTP bodies beginning with PK (ZIP header) indicating ZIP/JAR payloads in POST requests.
- [File/FS] Suspicious files and modifications – Unexpected ZIP/JARs and modified .properties files in SAP model upload directories found after exploitation.
- [Process] Process behavior – SAP NetWeaver spawning unexpected system binaries (e.g., cmd.exe, powershell) consistent with post-exploitation activity.
Read more: https://www.seqrite.com/blog/cve-2025-31324-sap-vulnerability-protection/