Unit 42 observed AdaptixC2—an open-source, modular post-exploitation framework—being used in the wild to execute commands, transfer files, exfiltrate data, and maintain persistence via in-memory shellcode and DLL hijacking. Key artifacts include multiple PowerShell loader hashes and numerous C2 domains such as tech-system[.]online, and the attacks show social engineering via Microsoft Teams and probable AI-generated scripts. #AdaptixC2 #tech-system.online
Keypoints
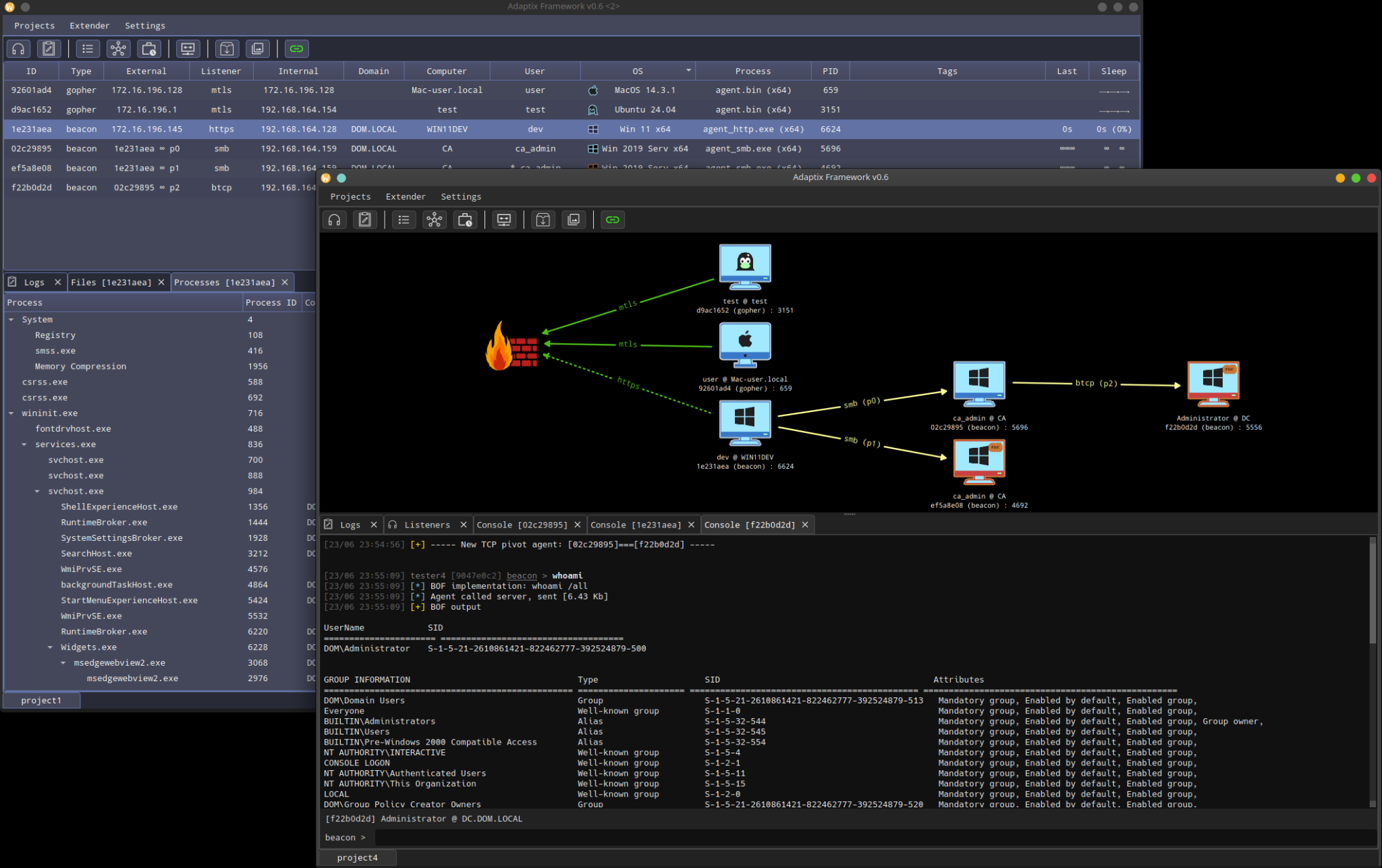
- AdaptixC2, an open-source post-exploitation/adversarial emulation framework, was observed in real-world attacks in May 2025.
- Attackers used social engineering (Microsoft Teams phishing impersonating IT support) and AI-assisted code generation to deploy AdaptixC2 beacons.
- Deployment methods included PowerShell loaders that decode and execute shellcode in memory (fileless execution) and DLL hijacking for persistence.
- AdaptixC2 supports modular “extenders,” BOFs, SOCKS4/5 tunneling, port forwarding, and multiple beacon profiles (HTTP, SMB, TCP) to evade detection and maintain covert communications.
- Configurations are RC4-encrypted and stored in PE .rdata; Unit 42 developed an extractor to recover beacon configurations (e.g., servers, URIs, parameters, timing).
- Observed post-exploitation activity included reconnaissance commands (nltest.exe, whoami.exe, ipconfig.exe) and potential pairing with other tools like Fog ransomware in at least one incident.
- Unit 42 published YARA rules, hunting queries, and IOCs (file hashes and domains) to help defenders detect AdaptixC2 activity.
MITRE Techniques
- [T1566] Phishing – Threat actors used Microsoft Teams phishing impersonating IT support to convince employees to start remote assistance sessions (“…impersonate IT support personnel (using subject lines like ‘Help Desk (External) | Microsoft Teams’)”).
- [T1218.011] Signed Binary Proxy Execution: PowerShell – Attackers used PowerShell loaders and .NET dynamic invocation (GetDelegateForFunctionPointer) to execute shellcode in memory (“…the script leverages .NET capabilities to allocate memory… uses GetDelegateForFunctionPointer… executing the shellcode without writing an executable file to disk”).
- [T1055.001] Process Injection: Dynamic-link Library Injection / Shellcode Injection – Adversaries copied shellcode into allocated memory and executed it via delegate invocation (“…copies the decrypted payload, which is actually shellcode, into this allocated memory region…create a delegate… effectively executing the shellcode”).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Persistence was established by creating a shortcut in the startup folder and adding a Run key named “Updater” to execute loader.ps1 on login (“…creates a shortcut in the startup folder” and “creates a registry entry in the run key named ‘Updater’”).
- [T1573] Encrypted Channel / Tunneling – AdaptixC2 supports SOCKS4/5 proxy functionality and port forwarding to facilitate covert communications and bypass network restrictions (“…supports sophisticated tunneling capabilities, including SOCKS4/5 proxy functionality and port forwarding”).
- [T1071.001] Application Layer Protocol: Web Protocols – The BEACON_HTTP profile uses HTTPS POSTs with configurable URIs, headers, and parameters to communicate with C2 (“…default HTTP profile targets 172.16.196.1:4443 using HTTPS communication, with a POST method to the /uri.php endpoint and the X-Beacon-Id parameter”).
- [T1090] Proxy – Beacon agents can create proxy functionality (SOCKS) enabling lateral movement and covert channeling (“…including SOCKS4/5 proxy functionality and port forwarding”).
- [T1036.005] Masquerading: Binary Padding / Legitimate Resource Abuse – Attackers downloaded payloads from legitimate services and used legitimate admin/remote tools (Quick Assist RMM) to blend in (“…downloads an encoded and encrypted payload from a link to a legitimate service” and “leveraged trust in Microsoft Teams… to initiate legitimate remote assistance sessions”).
- [T1608] Stage Capabilities: Adversary-in-the-Middle / Extensible Modules – AdaptixC2 modular “extenders” and BOFs enable custom payloads and on-process execution to evade analysis (“…modular, using ‘extenders’… supports Beacon Object Files (BOFs), which let attackers run small, custom programs written in C directly within the agent’s process to evade detection”).
Indicators of Compromise
- [SHA256] PowerShell installers / loaders – bdb1b9e37f6467b5f98d151a43f280f319bacf18198b22f55722292a832933ab, 83AC38FB389A56A6BD5EB39ABF2AD81FAB84A7382DA296A855F62F3CDD9D629D (PowerShell scripts that install AdaptixC2 beacons).
- [SHA256] AdaptixC2 beacon binaries – b81aa37867f0ec772951ac30a5616db4d23ea49f7fd1a07bb1f1f45e304fc625 (DLL beacon), df0d4ba2e0799f337daac2b0ad7a64d80b7bcd68b7b57d2a26e47b2f520cc260 (EXE beacon), and AD96A3DAB7F201DD7C9938DCF70D6921849F92C1A20A84A28B28D11F40F0FB06 (shellcode).
- [Domain] Command-and-control domains used by AdaptixC2 – tech-system[.]online (observed in a beacon configuration), protoflint[.]com, novelumbsasa[.]art (and many other domains listed such as picasosoftai[.]shop, dtt.alux[.]cc).
- [File names / Persistence] Persistence artifacts and target paths – loader.ps1, update.ps1, Run key named “Updater”, and use of APPDATAMicrosoftWindowsTemplatesmsimg32.dll for DLL hijacking.
- [YARA Rules] Detection signatures – provided YARA rules such as u42_hacktool_beacon_adaptixC2 (generic beacon), u42_hacktool_beaconGo_adaptixC2 (Go beacon), and u42_hacktool_adaptixC2_loader (shellcode loader) to detect related binaries and loaders.
Read more: https://unit42.paloaltonetworks.com/adaptixc2-post-exploitation-framework/