Two high-profile npm maintainers — prolific author Qix and duckdb_admin (DuckDB-related packages) — were compromised in a coordinated supply-chain campaign that published malicious package versions containing the same obfuscated wallet-drainer payload. The malicious code hooks browser wallet APIs and network calls to rewrite transaction addresses across multiple chains, while on-chain analysis shows only minor attacker payouts so far. #Qix #duckdb_admin
Category: Threat Research

A sophisticated supply-chain phishing campaign in early September 2025 compromised as many as 20 popular npm packages, resulting in 2.67 billion weekly downloads and injecting JavaScript that intercepts and redirects multi-chain cryptocurrency transactions. The attack used a cleanly configured domain (npmjs.help) and AI-assisted phishing content to bypass conventional defenses and exfiltrate…
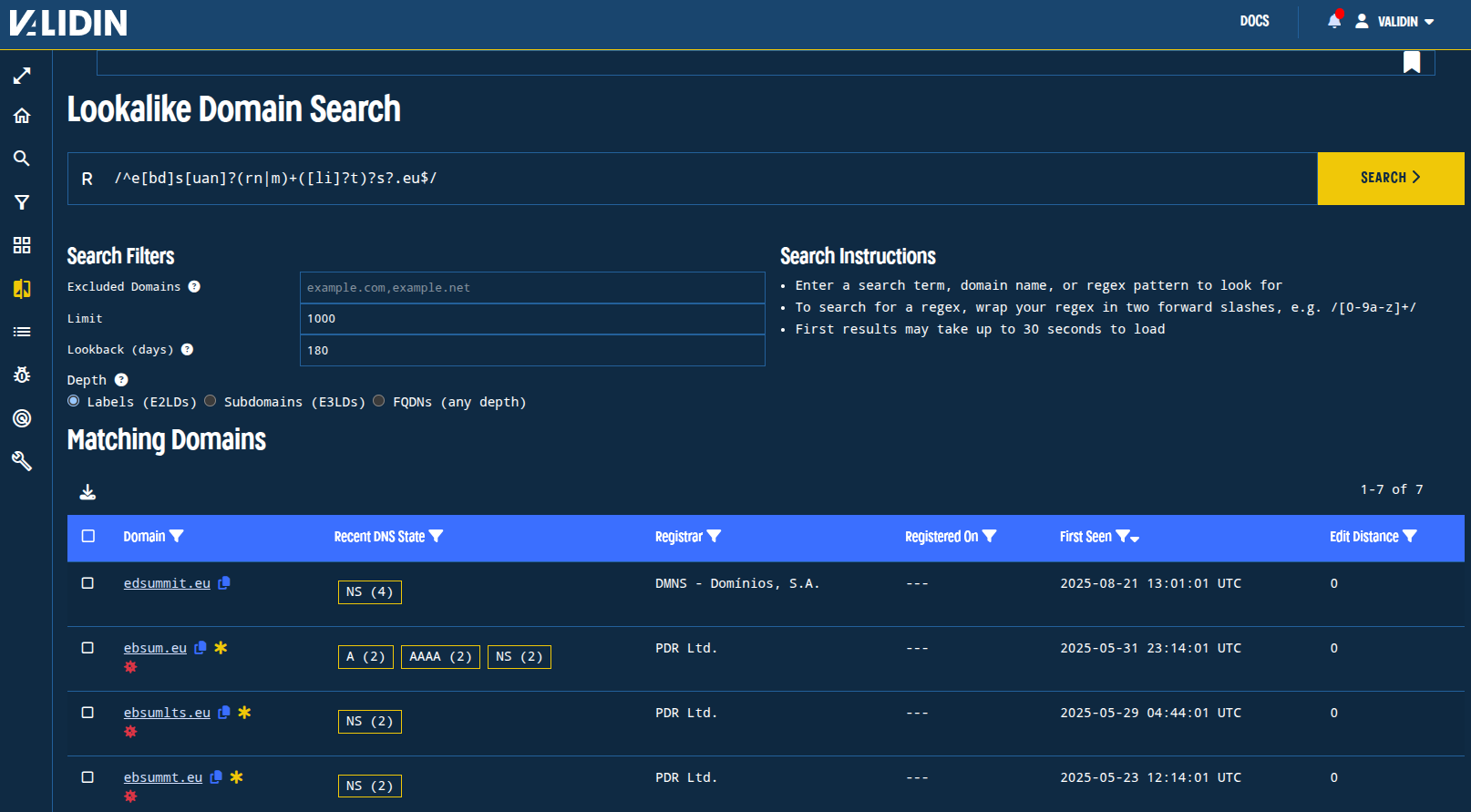
Validin re-tested pivoting and threat-hunting techniques from four recent blog posts (Laundry Bear, phishing/HTTP features, Transparent Tribe, and BlueNoroff) to see which methods still produce novel indicators and active infrastructure. Host response, header/body/hash, DNS/IP, and registration pivots remained fruitful in many cases, producing new domains, IPs, and certificate-based links, while some specific pivots (favicons, title tags, wildcard subdomains) aged out faster. #LaundryBear #TransparentTribe #BlueNoroff

Threat actors use PhantomRAT/PhantomRShell and related tools to download and execute remote-access and credential-stealing tools (MeshAgent, OpenSSH, RSocx, PhantomStealer, XenArmor) from multiple staging servers and compromised sites, then persist via scheduled Windows tasks and reverse SSH or SOCKS5 tunnels. Infrastructure includes many domains and IPs such as 188.127.254.234, 195.133.32.213, and mgfoms.org. #PhantomRAT #MeshAgent
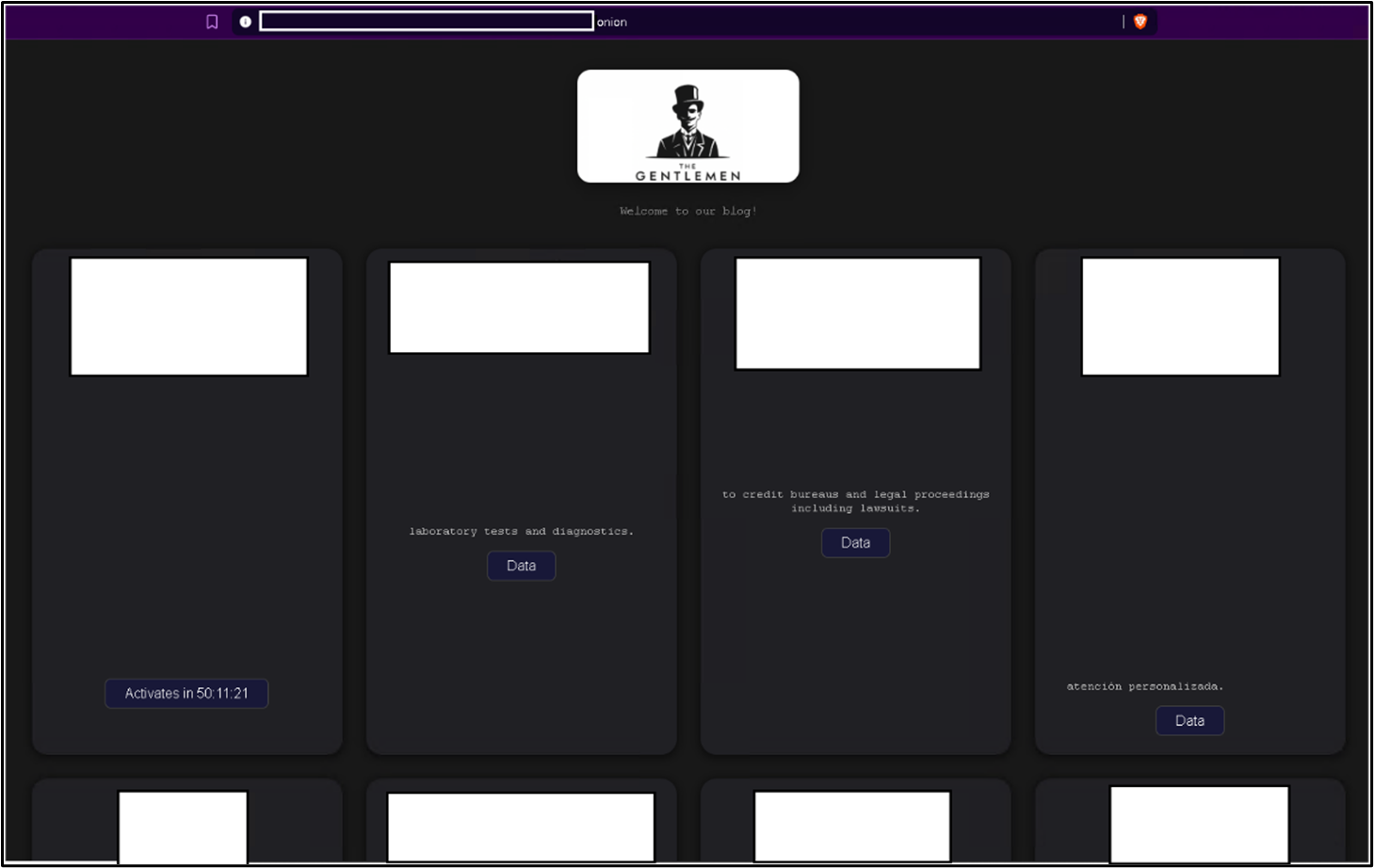
The Gentlemen ransomware group ran a highly tailored campaign using legitimate driver abuse, custom anti-AV tools, Group Policy manipulation, privileged account compromise, and encrypted exfiltration to bypass enterprise defenses and deploy ransomware domain-wide. Victims spanned critical sectors in at least 17 countries, with specific tooling and IOCs including ThrottleBlood.sys, PowerRun.exe, AnyDesk,…

Silent Push identified 45 previously unreported domains and associated infrastructure patterns used by Chinese APT group Salt Typhoon and a related actor UNC4841, linking them via ProtonMail registrant emails, fake US personas, SOA records, and shared name servers. The report highlights historical C2 domains tied to Demodex, Snappybee, and Ghostspider malware…

Mr Hamza is a Telegram-based hacktivist collective active since late 2024 that combines politically motivated campaigns—primarily anti-Israel/pro-Palestinian—with commercial operations selling DDoS tools and botnets. The group was a top source of DDoS claims during the June 2025 Iran–Israel conflict and promotes bespoke Layer 7 flooding tools like HTTP Spectral Phantom V1 and HTTPS Flood V1. #MrHamza #HTTPSpectralPhantomV1
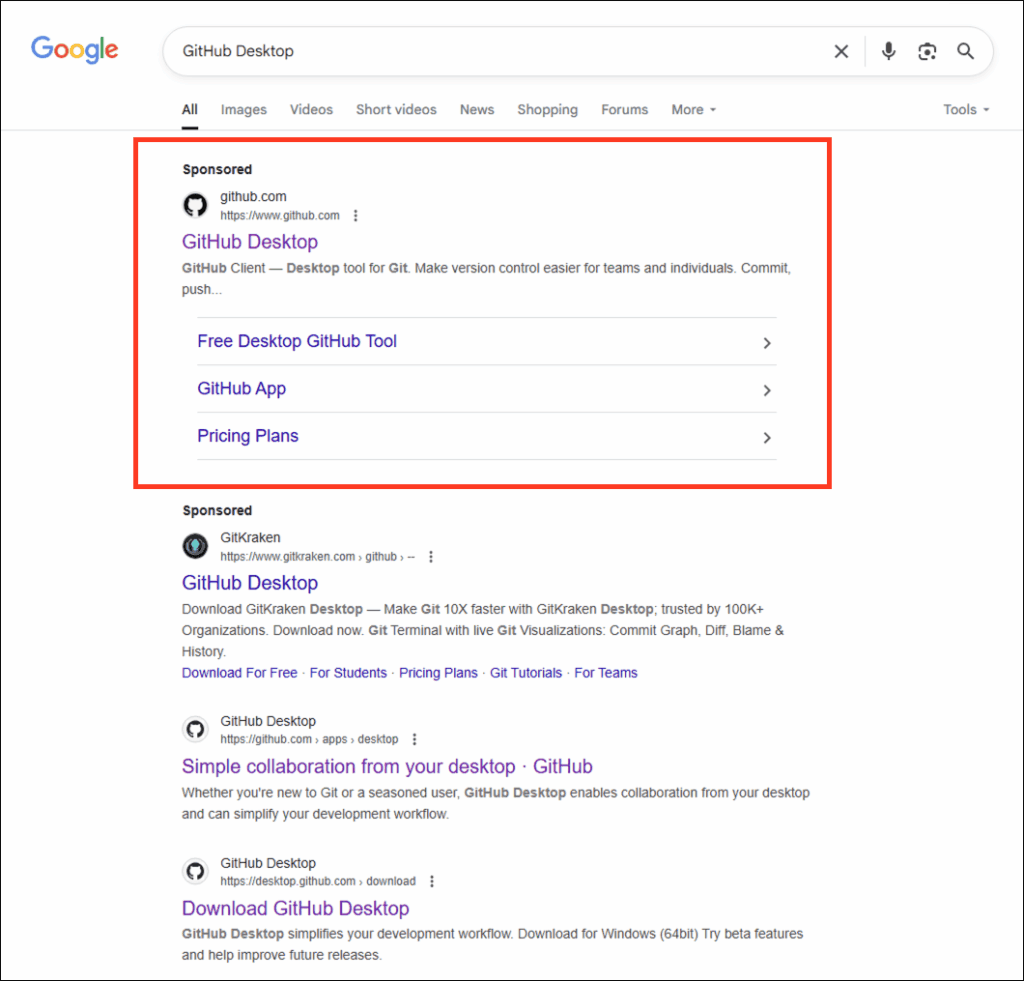
On 19 August 2025 Arctic Wolf Labs disclosed a campaign where attackers used Google Ads and GitHub commit-specific pages to redirect victims to a trojanized GitHub Desktop installer that deploys a GPU-gated decryption loader dubbed “GPUGate.” The campaign delivers a 128 MB MSI with embedded modules and a GPU/OpenCL key-generation routine that prevents execution in many sandboxes and targets Western European IT workers. #GPUGate #AMOS_Stealer
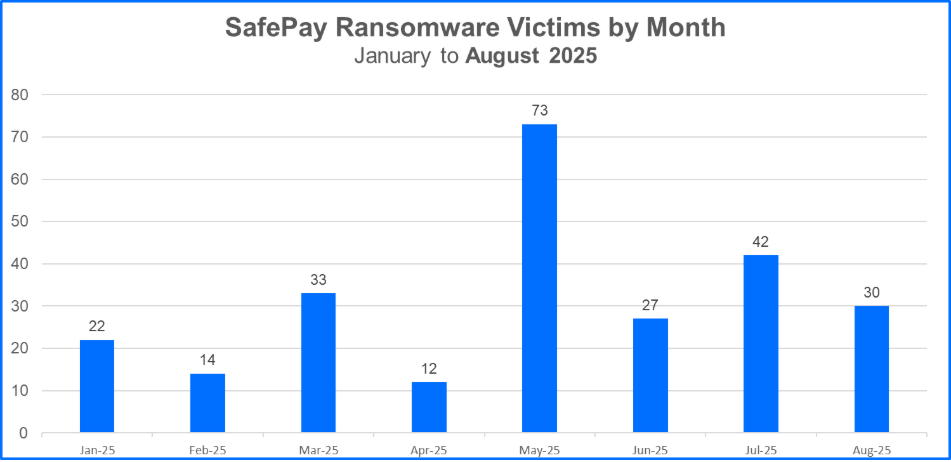
SafePay, a non-RaaS ransomware group, rapidly rose in 2025 by claiming hundreds of victims worldwide through discreet, in-house operations that emphasize strong OPSEC and rapid encryption within 24 hours. Their campaigns target mid-size and enterprise organizations—notably in manufacturing, healthcare, and construction—use tools like ShareFinder.ps1 and PsExec, and leave artifacts such as the .safepay extension and readme_safepay.txt ransom notes. #SafePay #ShareFinder.ps1

FortiGuard Labs identified a phishing campaign targeting Japanese users that deploys a multi-stage Remote Access Trojan called MostereRAT, which leverages Easy Programming Language (EPL), service and scheduled task persistence, and deployment of legitimate remote-access tools to achieve full system control. The malware uses advanced evasion including AV/EDR traffic blocking via Windows Filtering Platform, running as TrustedInstaller, and mTLS-protected C2 communications. #MostereRAT #EPL

APT37 (aka ScarCruft, Ruby Sleet, Velvet Chollima) used a unified C2 server to orchestrate Rustonotto (Rust backdoor), Chinotto (PowerShell backdoor), and FadeStealer (surveillance/stealer) in campaigns targeting South Korean individuals linked to North Korean interests, employing spear phishing, CHM/shortcut delivery, and TxF-based Process Doppelgänging. The group leveraged Rust for a lightweight backdoor, Python-based loaders, and password-protected RAR exfiltration to maintain persistence and stealth. #Rustonotto #Chinotto #FadeStealer
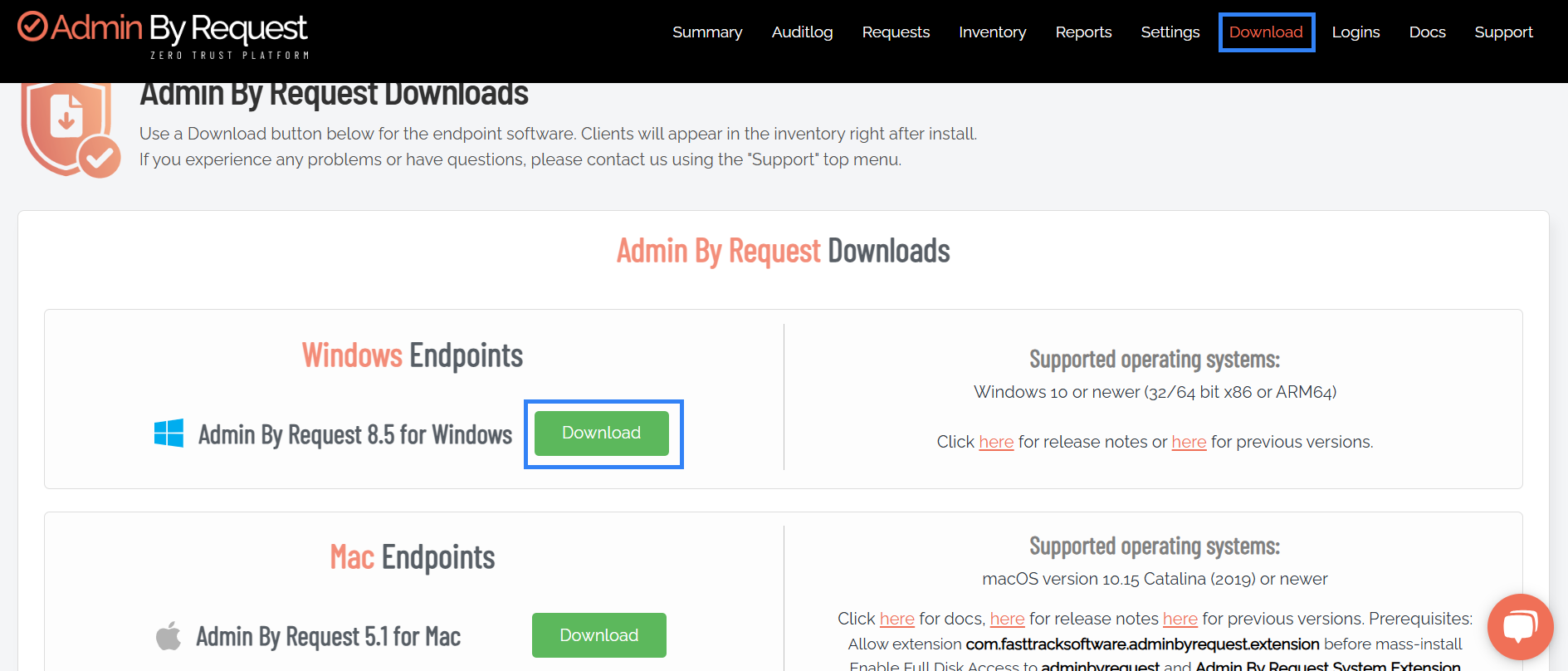
Admin By Request (ABR) provides temporary, audited local administrator access to enforce least privilege, and integrating it with Wazuh centralizes privilege elevation events for faster detection and response. This integration uses Wazuh custom rules to detect denied elevations, repeated requests, and changes to local admin membership, improving visibility into risky privilege…
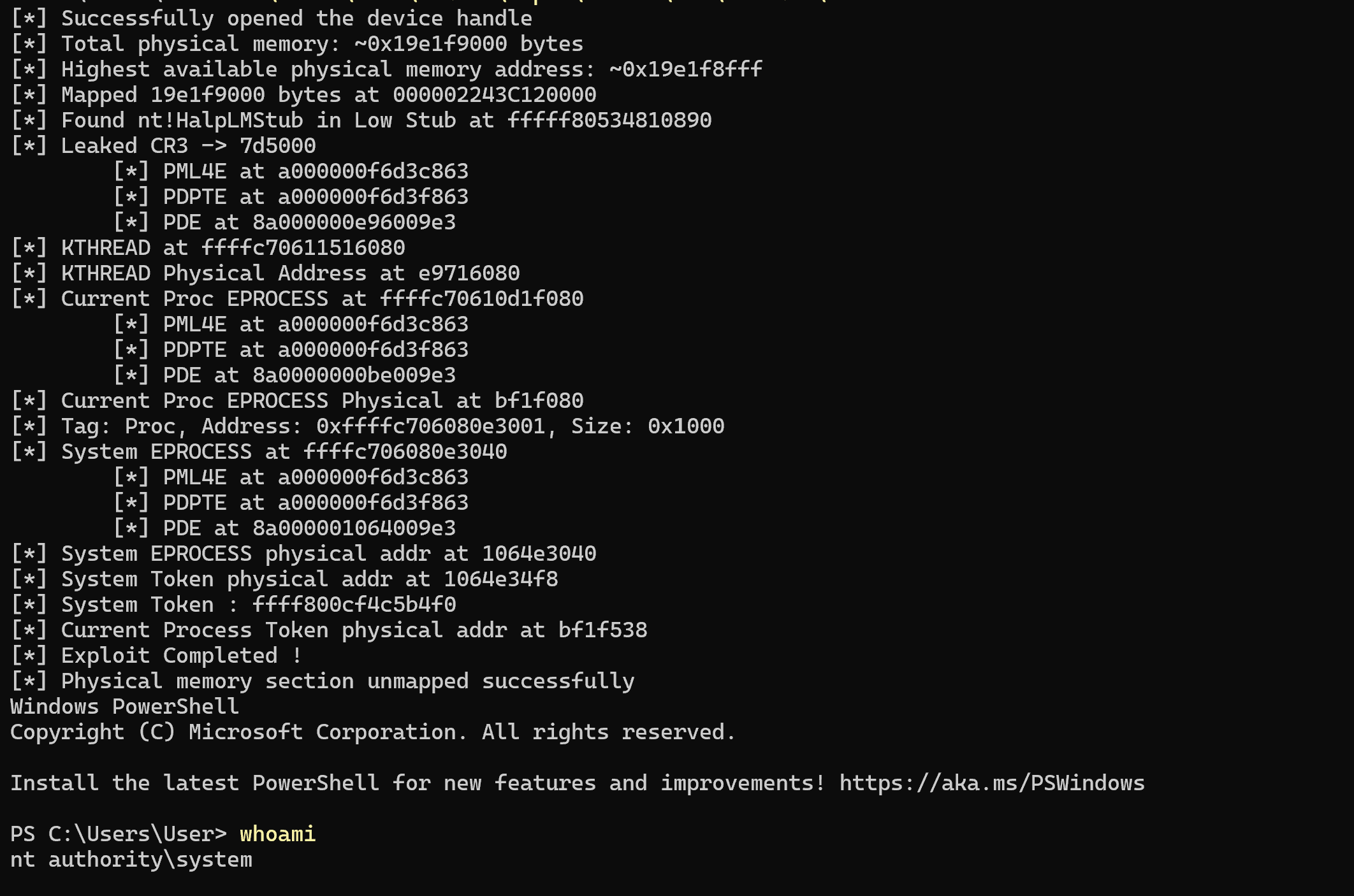
This article walks through a proof-of-concept exploit for CVE-2020-12446 in the eneio64.sys driver (Trident Z Lighting Control v1.00.08), which exposes primitives to map, read and write physical memory and can be loaded on Windows 11 with HVCI enabled. The write-up details obtaining CR3 from the Low Stub, performing virtual-to-physical translations via…

A Windows 10 kernel-only crash dump (build 19041) shows a 0xD1 DRIVER_IRQL_NOT_LESS_OR_EQUAL caused by tunnel.sys (Teredo) dereferencing a NULL previous pointer while unlinking a flow list entry, triggered during concurrent TCP/IP cleanup and a user thread closing a UDP endpoint. The analyst concludes the root cause is a race condition between…

Mandiant investigated a ViewState deserialization attack exploiting an exposed ASP.NET machine key in Sitecore deployments (CVE-2025-53690) that enabled remote code execution and deployment of reconnaissance and tunneling tools. The actor used WEEPSTEEL, EARTHWORM, DWAGENT, SHARPHOUND, and attempted GoTokenTheft to escalate privileges, perform AD reconnaissance, and exfiltrate data. #WEEPSTEEL #EARTHWORM
