SafePay, a non-RaaS ransomware group, rapidly rose in 2025 by claiming hundreds of victims worldwide through discreet, in-house operations that emphasize strong OPSEC and rapid encryption within 24 hours. Their campaigns target mid-size and enterprise organizations—notably in manufacturing, healthcare, and construction—use tools like ShareFinder.ps1 and PsExec, and leave artifacts such as the .safepay extension and readme_safepay.txt ransom notes. #SafePay #ShareFinder.ps1
Keypoints
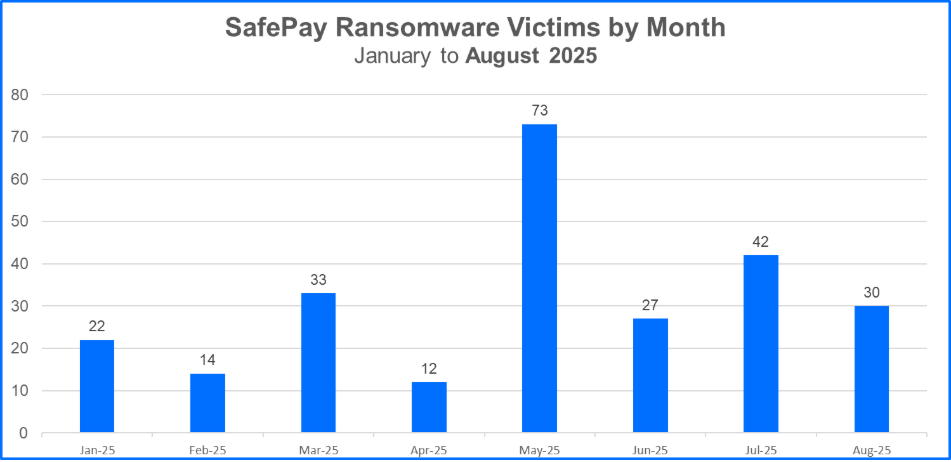
- SafePay claimed more than 270 victims in 2025, including 73 in June and 42 in July, marking a rapid escalation in activity.
- The group operates independently (non-RaaS), performs attacks in-house to preserve profits, and maintains strict operational secrecy aside from a data leak site.
- SafePay targets mid-size and enterprise organizations across the US, Germany, Great Britain, and Canada, focusing on industries prone to availability impacts such as manufacturing, healthcare, and construction.
- Attacks often move from initial access to encryption within 24 hours, with days where SafePay published 10+ victims and peaks of 29 victims in one day.
- Initial access methods include credential exposure, brute-force, VPN weaknesses, and social engineering to deploy tools like RMMs and ShareFinder.ps1 for discovery.
- Lateral movement and execution involve tools like PsExec; exfiltration uses WinRAR and FileZilla; encryption uses ChaCha20 and appends the .safepay extension while dropping readme_safepay.txt.
- Defense evasion includes debugger detection avoidance and terminating anti-malware processes; mitigation recommendations emphasize MFA, patching, complex passwords, and layered detection/response.
MITRE Techniques
- [T1078] Valid Accounts – SafePay gains initial access via credential exposure and brute-force password attacks (“SafePay typically establishes initial access to victim networks via credential exposure, brute-force password attacks…”).
- [T1190] Exploit Public-Facing Application – The group exploits weaknesses in VPN appliances and known vulnerabilities to gain access (“…exploiting weaknesses in VPN appliances…”).
- [T1598] Phishing for Information / T1593] Search Open Websites/Domains – Social engineering impersonation of IT staff to load tools like RMMs (“…engaged in social engineering tactics…to impersonate IT staff and load other tools like RMMs.”).
- [T1083] File and Directory Discovery – Use of ShareFinder.ps1 to hunt for network shares containing critical data (“…repurposed to hunt for shares that may contain critical data… ‘Invoke-ShareFinder’”).
- [T1021] Remote Services – Use of PsExec for lateral movement (“SafePay leverages tools like PsExec to establish lateral movement…”).
- [T1041] Exfiltration Over C2 Channel / T1560] Archive Collected Data – Use of WinRAR to archive and FileZilla to exfiltrate stolen data (“…using WinRAR…before exfiltration using FileZilla.”).
- [T1486] Data Encrypted for Impact – Ransomware encrypts files with ChaCha20, replaces extensions with .safepay, and drops readme_safepay.txt (“The .safepay extension replaces extensions on affected files. And, the ransom note named readme_safepay.txt is added…”).
- [T1497] Virtualization/Sandbox Evasion & [T1621] Debugger Evasion – Ransomware evades debugger detection and can terminate anti-malware processes (“…equipped with defense evasion capabilities, including the ability to evade debugger detection. It can also terminate processes associated with anti-malware functions.”).
Indicators of Compromise
- [File Hash] SafePay ransomware executable – SHA256: a0dc80a37eb7e2716c02a94adc8df9baedec192a77bde31669faed228d9ff526
- [File Hash] SafePay sample – SHA256: 327b8b61eb446cc4f710771e44484f62b804ae3d262b57a56575053e2df67917
- [File Name/Extension] Ransomware artifacts – readme_safepay.txt (ransom note), .safepay (file extension applied to encrypted files)
- [Tool/Script] Discovery utility repurposed – ShareFinder.ps1 (Invoke-ShareFinder) used to find network shares for pivoting or data discovery
Read more: https://www.bitdefender.com/en-us/blog/businessinsights/safepay-ransomware-attacks-ttps