On 19 August 2025 Arctic Wolf Labs disclosed a campaign where attackers used Google Ads and GitHub commit-specific pages to redirect victims to a trojanized GitHub Desktop installer that deploys a GPU-gated decryption loader dubbed “GPUGate.” The campaign delivers a 128 MB MSI with embedded modules and a GPU/OpenCL key-generation routine that prevents execution in many sandboxes and targets Western European IT workers. #GPUGate #AMOS_Stealer
Keypoints
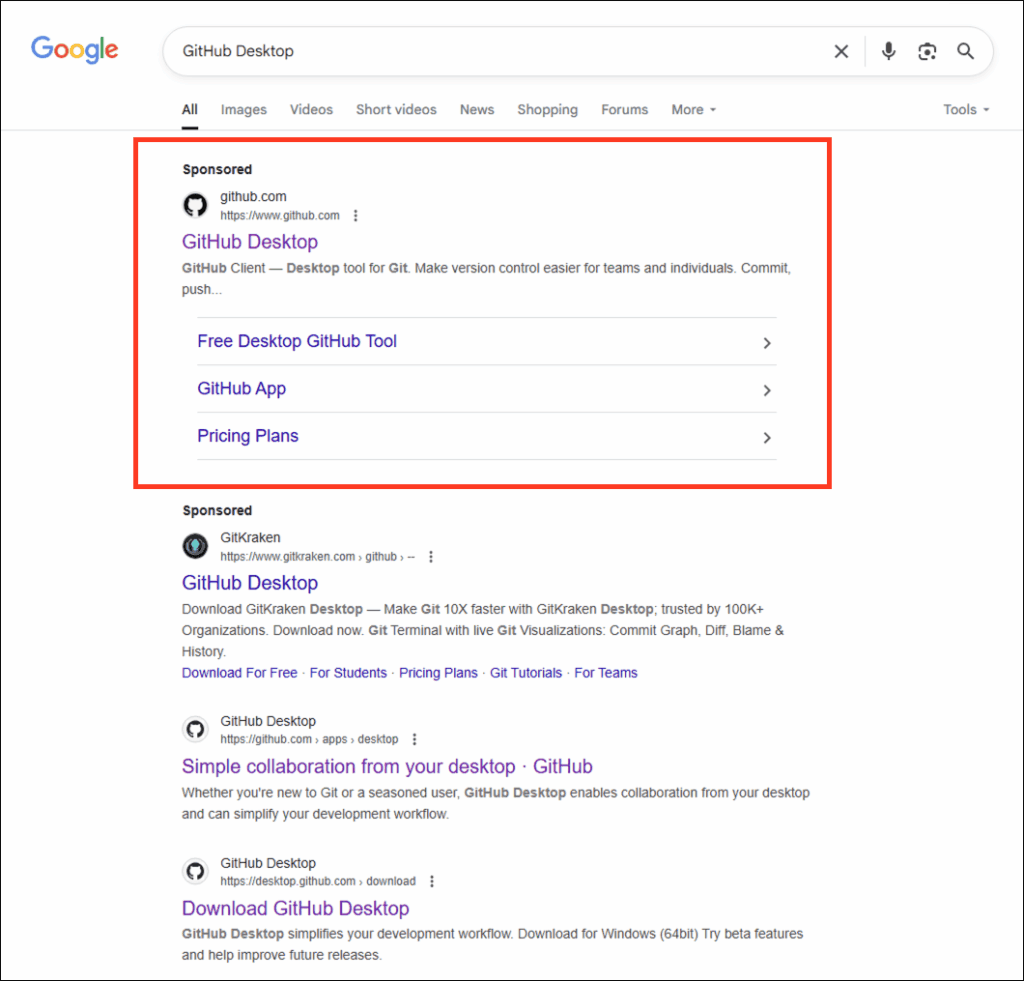
- Attackers purchased Google Ads targeted at GitHub Desktop searches to surface a sponsored result that led victims to a malicious commit page.
- The adversary abused GitHub commit pages by embedding commit-specific links and README modifications to present a trusted-source illusion while redirecting downloads to attacker-controlled domains (gitpage[.]app).
- The delivered installer is a bloated 127.7 MB MSI containing 171 embedded executables (chaff) and at least one malicious module to evade sandboxes and analysis.
- GPUGate implements an OpenCL GPU-gated decryption routine that generates the AES key only on systems with real GPUs (device name length >= 10), preventing payload decryption in headless or VM analysis environments.
- Post-execution behavior includes UAC elevation, persistence via scheduled task “WinSvcUpd,” Windows Defender exclusion additions, detached PowerShell execution, DLL sideloading, and modular payload retrieval.
- Campaign targeted Western European IT sector users and delivered macOS AMOS Stealer variants for Apple platforms from the same infrastructure.
- Network infrastructure includes multiple attacker domains and IPs (e.g., gitpage[.]app 107.189.17[.]89) and observable file hashes for detection and YARA rules provided by Arctic Wolf.
MITRE Techniques
- [T1566.002] Phishing: Spearphishing Link – Adversaries purchased Google Ads to position malicious results for “GitHub Desktop” searches, sending users to compromised commit pages (“Google search results showing sponsored malicious advertisements directing users to compromised repositories”).
- [T1189] Drive-by Compromise – Malicious README links on GitHub commit pages redirected users to attacker-controlled domains hosting trojanized installers (“GitHub repository with modified content showing download links redirecting to external domains instead of GitHub releases”).
- [T1059.001] Command and Scripting Interpreter: PowerShell – PowerShell launched with stealth parameters to execute payloads and bypass policies (“powershell.exe -WindowStyle Hidden -ExecutionPolicy Bypass -File …”).
- [T1059.005] Command and Scripting Interpreter: Visual Basic – VBScript used to create shell objects that launch PowerShell stealthily (“Set shell = CreateObject(“WScript.Shell”)” and shell.Run usage).
- [T1053.005] Scheduled Task/Job: Scheduled Task – Persistence via scheduled task “WinSvcUpd” configured to run at logon with highest privileges (schtasks.exe /create … /RL HIGHEST).
- [T1547.009] Boot or Logon Autostart Execution: Shortcut Modification – Script copies itself to AppData for persistence (C:Users[user]AppDataRoaming… .ps1 file creation).
- [T1548.002] Abuse Elevation Control Mechanism: Bypass User Account Control – Script requests UAC elevation once to obtain admin rights (“Если не админ, запрашиваем один раз UAC и выходим” / “If not admin, request UAC once and exit”).
- [T1562.001] Impair Defenses: Disable or Modify Tools – Adds Windows Defender exclusions for AppData, LocalAppData, and ProgramData to evade detection (Add-MpPreference -ExclusionPath …).
- [T1036.004] Masquerading: Masquerade Task or Service – Scheduled task named “WinSvcUpd” to blend with legitimate service naming (task name chosen to mimic legitimate Windows Update tasks).
- [T1027.002] Obfuscated Files or Information: Software Packing – MSI contains 171 executables with chaff to inflate size and complicate analysis (large installer with embedded garbage files).
- [T1140] Deobfuscate/Decode Files or Information – GPU-based OpenCL decryption routine generates AES key conditionally, preventing decryption on systems without suitable GPUs (OpenCL kernel device name length check and key selection).
- [T1055.012] Process Injection: Process Hollowing – Malware restarts in a detached process to break parent-child relationships and hinder analysis (“Перезапуск в оторванном процессе” indicated in script comments).
- [T1218.005] Signed Binary Proxy Execution: Mshta – Use of legitimate scripting hosts (wscript.exe) to execute VBScript and proxy execution of malicious code (wscript.exe launching VBScript from temp directories).
- [T1564.001] Hide Artifacts: Hidden Files and Directories – Creation of adm_marker.tmp to manage execution state and hide repeated initialization activities (marker file creation in AppData/TEMP).
- [T1082] System Information Discovery – Enumeration of GPU device name via OpenCL to determine suitability for payload decryption (OpenCL kernel checks device_name length and sets suspicious_flag).
- [T1518.001] Software Discovery: Security Software Discovery – Targeted manipulation of Windows Defender exclusions shows reconnaissance of installed security products (Add-MpPreference commands targeting Defender paths).
- [T1083] File and Directory Discovery – PowerShell searches and creates directories in AppData and ProgramData for deployment and persistence (file system operations targeting AppData locations).
- [T1071.001] Application Layer Protocol: Web Protocols – Use of HTTPS to download ZIP payloads and communicate with C2 infrastructure (downloads from kololjrdtgted[.]click/zip.php and other domains over port 443).
- [T1105] Ingress Tool Transfer – PowerShell downloads ZIP archives containing secondary modules and extracts executables for local execution (download and extraction flow to TEMP folder).
- [T1573.002] Encrypted Channel: Asymmetric Cryptography – Use of HTTPS encrypted channels for C2 and payload retrieval to blend with legitimate traffic (network traffic to C2 domains over port 443).
- [T1008] Fallback Channels – Multiple domains and IPs across hosting providers used for redundancy (infrastructure spanning 107.189.x.x, 45.59.125.x, 104.194.x.x ranges).
- [T1102.001] Web Service: Dead Drop Resolver – PHP-based endpoints (zip.php) act as simple web services for payload delivery and command retrieval (PHP scripts serving ZIP payloads).
- [T1555.003] Credentials from Password Stores: Credentials from Web Browsers – Malware capability to harvest browser-stored credentials enabled by persistence and elevated privileges (credential theft described in capabilities).
- [T1552.001] Unsecured Credentials: Credentials In Files – File system access allows harvesting plaintext credentials from configuration files and scripts (enumeration of app config and script locations).
- [T1005] Data from Local System – Collection of documents and application data via persistent malware access (local file system collection described).
- [T1115] Clipboard Data – Potential clipboard monitoring to capture copied sensitive data during user activity (clipboard capture capability noted).
- [T1041] Exfiltration Over C2 Channel – Exfiltration of collected data over HTTPS to attacker-controlled infrastructure (C2 channels used for data transfer).
- [T1020] Automated Exfiltration – Scheduled tasks and persistent execution enable automated periodic exfiltration without manual operator involvement (scheduled task-driven automation).
- [T1486] Data Encrypted for Impact – Code similarities to known ransomware and potential for ransomware deployment via modular payloads (shared debug paths and function similarities to ransomware samples).
- [T1489] Service Stop – Administrative privileges enable stopping security services to prepare for destructive actions (capability to terminate security services noted).
- [T1490] Inhibit System Recovery – Administrative access and destructive modules could delete backups and recovery artifacts to prevent restoration after impact (capability to remove backups and recovery options).
Indicators of Compromise
- [Domain] Payload hosting and C2 – gitpage[.]app (107.189.17[.]89), gitpage[.]app/git/mac (serves AMOS Stealer)
- [Domain/IP] Additional payload domains – fileisuwaiquw[.]icu (107.189.16[.]41), poiwerpolymersinc[.]online (107.189.25[.]128), git-freqtrade[.]com (107.189.20[.]254) and many other listed domains across 107.189.x.x, 104.194.x.x, 45.59.125.x ranges (see report for full list).
- [File Hash – PE] Primary Windows installer – SHA-256: ad07ffab86a42b4befaf7858318480a556a2e7c272604c3f1dcae0782339482e (GitHubDesktopSetup-x64.exe / MSI, ~127.7 MB).
- [File Hash – Stage2] Embedded/loader module – SHA-256: 3746217c25d96bb7efe790fa78a73c6a61d4a99a8e51ae4c613efbb5be18c7b4 (second-stage GPUGate module; also noted SHA-256 e4d63c9aefed1b16830fdfce831f27b8e5b904c58b9172496125ba9920c7405b related).
- [File Hash – macOS] macOS payload – SHA-256: b13d2ecb8b7fe2db43b641c30a7ca0f8b66f4fadb92401582ac2f8cc3f21a470 (GithubDesktopMacOS.dmg delivering AMOS Stealer).
- [Filename] Deceptive installer filename – GitHubDesktopSetup-x64.exe used to lure victims (ITW filename matched to malicious MSI).