Electron CVE-2025-55305 is a framework-level bypass that allows attackers to backdoor Chromium-based applications by tampering with V8 heap snapshot files, enabling unsigned JavaScript to run despite integrity checks. Proofs of concept showed backdoors in Signal, 1Password (patched in v8.11.8-40), Slack, and Chrome derivatives by overwriting snapshots to clobber builtins like Array.isArray. #CVE-2025-55305 #V8_heap_snapshot
Keypoints
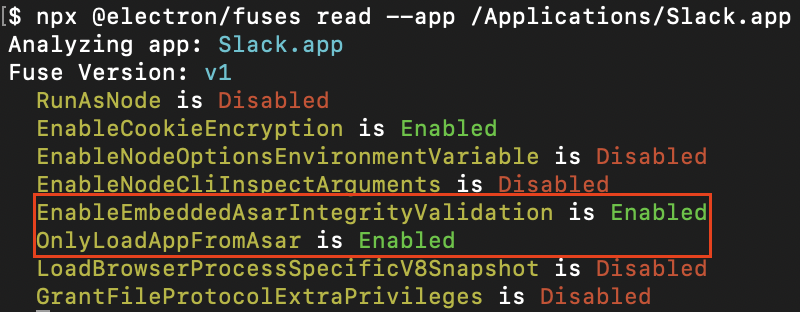
- Electron’s integrity fuses (EnableEmbeddedAsarIntegrityValidation and OnlyLoadAppFromAsar) did not consider V8 heap snapshots as executable content, leaving snapshots unchecked.
- V8 heap snapshots are deserialized into isolates and can contain builtins that, when clobbered, allow execution of attacker-controlled JavaScript without breaking OS code-signing.
- Tampering with snapshots is especially dangerous for applications installed to user-writable locations (e.g., %AppData%Local, /Applications), enabling local persistence without privilege escalation.
- A practical gadget approach using builtins (e.g., Array.isArray) was demonstrated to run payloads in multiple isolates and selectively access Node.js capabilities in the main process.
- Proofs of concept showed backdoors for Slack, 1Password, and Signal; 1Password patched the issue in v8.11.8-40 after responsible disclosure.
- The issue affects not only Electron but any Chromium-based application using V8 snapshots; similar local backdooring of Chrome derivatives was demonstrated.
- Electron maintainers assigned CVE-2025-55305 and coordinated fixes; developers are advised to enable and extend integrity checks to include heap snapshots.
MITRE Techniques
- [T1218.015 ] Signed Binary Proxy Execution: Loki C2 technique – “Loki C2 … uses backdoored versions of trusted applications (VS Code, Cursor, GitHub Desktop, Tidal, and more) to evade endpoint detection and response (EDR) software” — described as abuse of applications that appear signed but include tampered content.
- [T1553 ] Create or Modify System Process: Overwrite V8 heap snapshot files to inject malicious builtins – “tampering with executable content outside of their code integrity checks” (translated quote: “tampering with executable content outside of their code integrity checks”).
- [T1609 ] Container and Resource Discovery (contextual technique): Use V8 isolate-specific builtins to discover environment and capabilities (Node.js presence, process.pid) – “Different builtins can be discovered in different V8 isolates, which allows gadgets to forensically discover which isolate they are running in.”
- [T1055 ] Process Injection (conceptual analog): Load unsigned JavaScript into V8 isolates via snapshots to run code in targeted processes – “we deserialize a previously-prepared snapshot directly into the heap to get an initialized context,” enabling unsigned code to run via clobbered builtins.
Indicators of Compromise
- [File Name ] tampered V8 heap snapshot – v8_context_snapshot.bin (overwritten with attacker snapshot)
- [Software Version ] vulnerable or patched app versions – 1Password v8.11.8-40 (patched), Electron versions prior to CVE-2025-55305 fixes
- [Function/Method ] abused builtins used as gadgets – Array.isArray (gadget to execute payload), other V8 builtins used to fingerprint isolates
- [Domain ] exfiltration/command callback example – attacker.tld (used in PoC keylogger fetch), and example callbacks to HTTP endpoints