North Korea-aligned actors behind the Contagious Interview cluster used cyber threat intelligence platforms (Validin, VirusTotal, Maltrail) and coordinated team workflows (likely Slack) to monitor, scout, and rapidly replace exposed infrastructure while conducting ClickFix social engineering against job seekers in the crypto sector. SentinelLABS recovered ContagiousDrop server logs showing over 230 victims and numerous IOCs including domains, IPs, email addresses, and SHA-1 hashes. #ContagiousInterview #ClickFix
Category: Threat Research
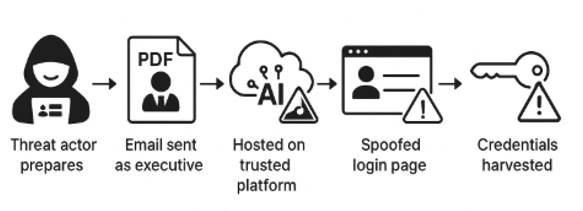
Threat actors hosted a phishing page on the legitimate Simplified AI platform and used a password-protected PDF that redirected victims to a spoofed Microsoft 365 login to harvest credentials. The campaign targeted US organizations, was detected and contained by Cato MDR in July 2025, and leveraged app.simplified.com to bypass defenses. #SimplifiedAI #Microsoft365
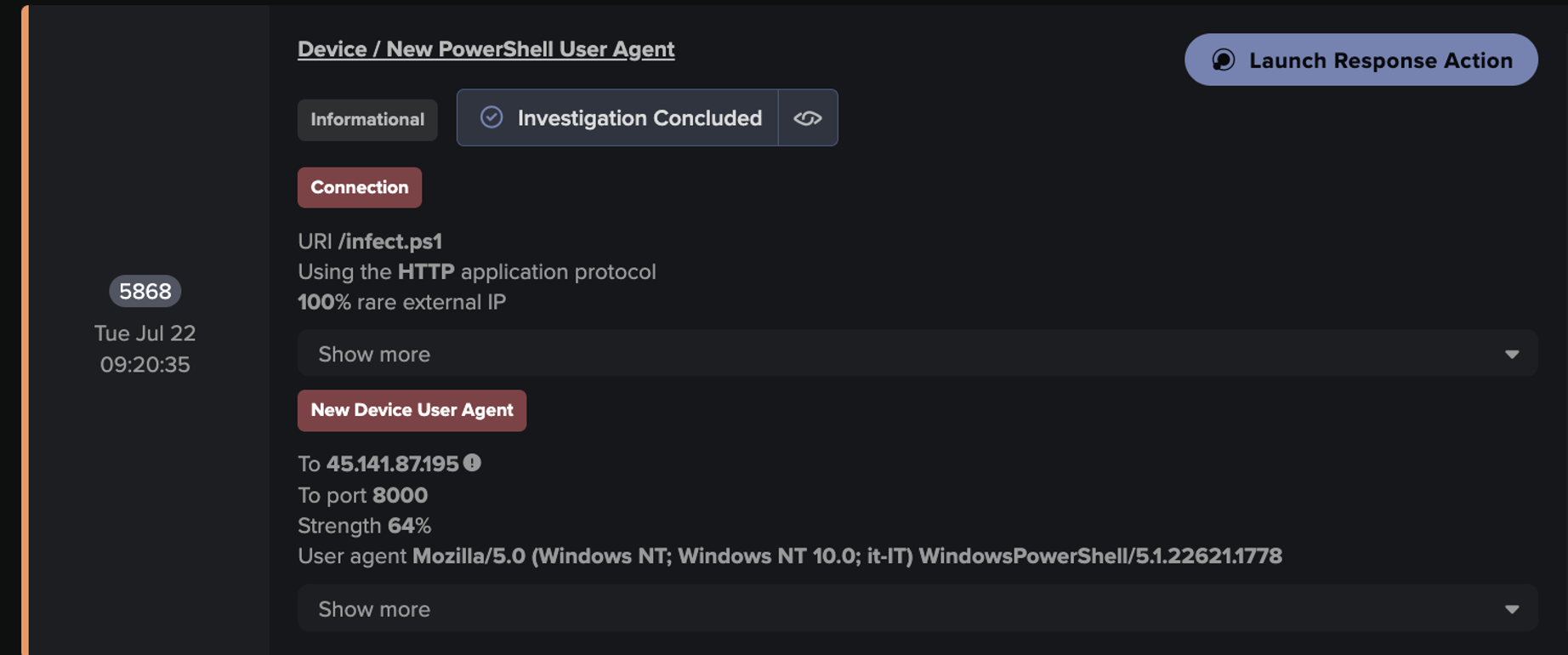
Darktrace detected and autonomously contained a PowerShell-based cryptojacking campaign that used an obfuscated PowerShell dropper (infect.ps1) to deploy an AutoIt loader which injected and executed NBMiner in memory. The attack contacted mining infrastructure including gulf.moneroocean[.]stream, monerooceans[.]stream and IPs such as 152.53.121[.]6, and was halted by Darktrace Autonomous Response. #NBMiner #infect.ps1

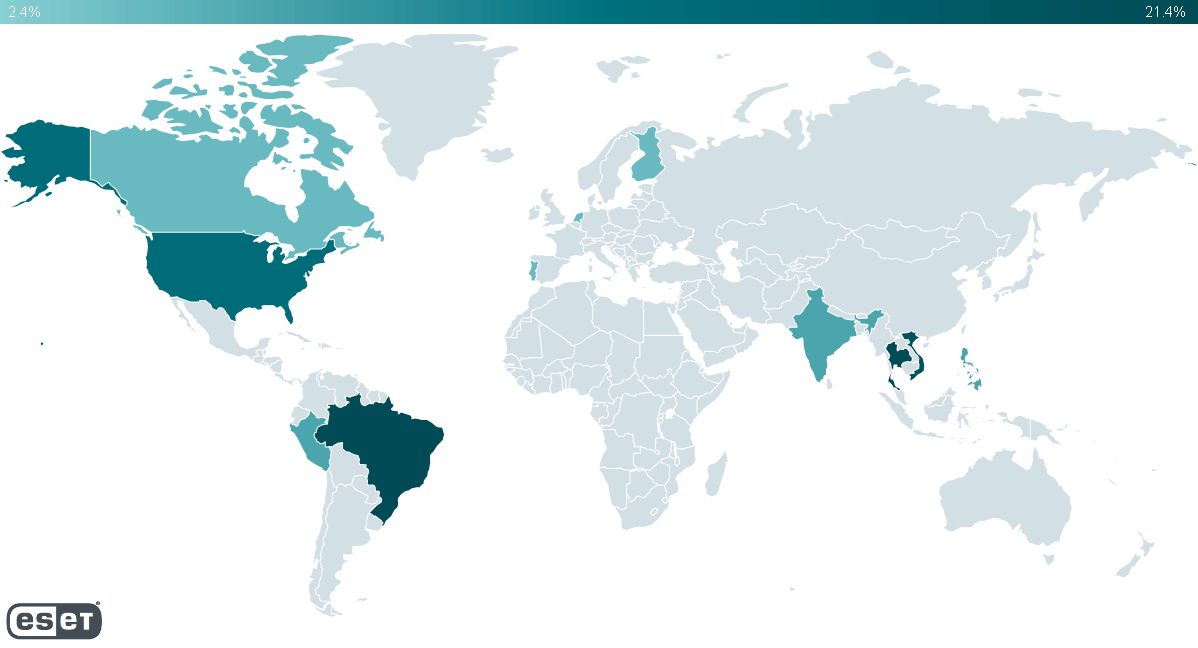
Proofpoint observed an uptick in campaigns delivering Stealerium-based info-stealers between May and July 2025, with multiple low-sophistication cybercrime actors (e.g., TA2715, TA2536) using varied lures and delivery types to deploy the open-source Stealerium and related variants. The malware exfiltrates a wide range of data (browser credentials, cookies, crypto wallets, Wi‑Fi profiles,…
ESET identified a previously unknown, China-aligned threat actor named GhostRedirector that compromised at least 65 Windows servers and deployed custom tools Rungan (a C++ backdoor) and Gamshen (a malicious native IIS module for SEO fraud). The campaign used public exploits (EfsPotato, BadPotato), multiple custom utilities, and staging domains such as 868id[.]com to manipulate Google search results and promote third-party gambling sites. #GhostRedirector #Rungan #Gamshen #868id

A spear-phishing campaign targeting organizations in India used weaponized Linux .desktop files to deliver a MeshAgent payload through a multi-stage, heavily obfuscated Go-based dropper chain possibly linked to APT36 (Transparent Tribe). The campaign used decoy PDFs, ELF magic-byte restoration, AES/DES decryptors, anti-VM checks, and C2 infrastructure at indianbosssystems.ddns[.]net resolving to 54.144.107.42. #APT36 #MeshAgent

A Lazarus subgroup targeting financial and cryptocurrency organizations used social engineering and likely a Chrome zero-day to deploy multiple RATs — PondRAT, ThemeForestRAT and RemotePE — progressing from initial loaders to a more advanced in-memory RAT. The actor used phantom DLL persistence via PerfhLoader, extensive discovery tools, and cleaned up artifacts before deploying RemotePE, linking activity to AppleJeus, POOLRAT, Citrine Sleet and Gleaming Pisces. #PondRAT #ThemeForestRAT
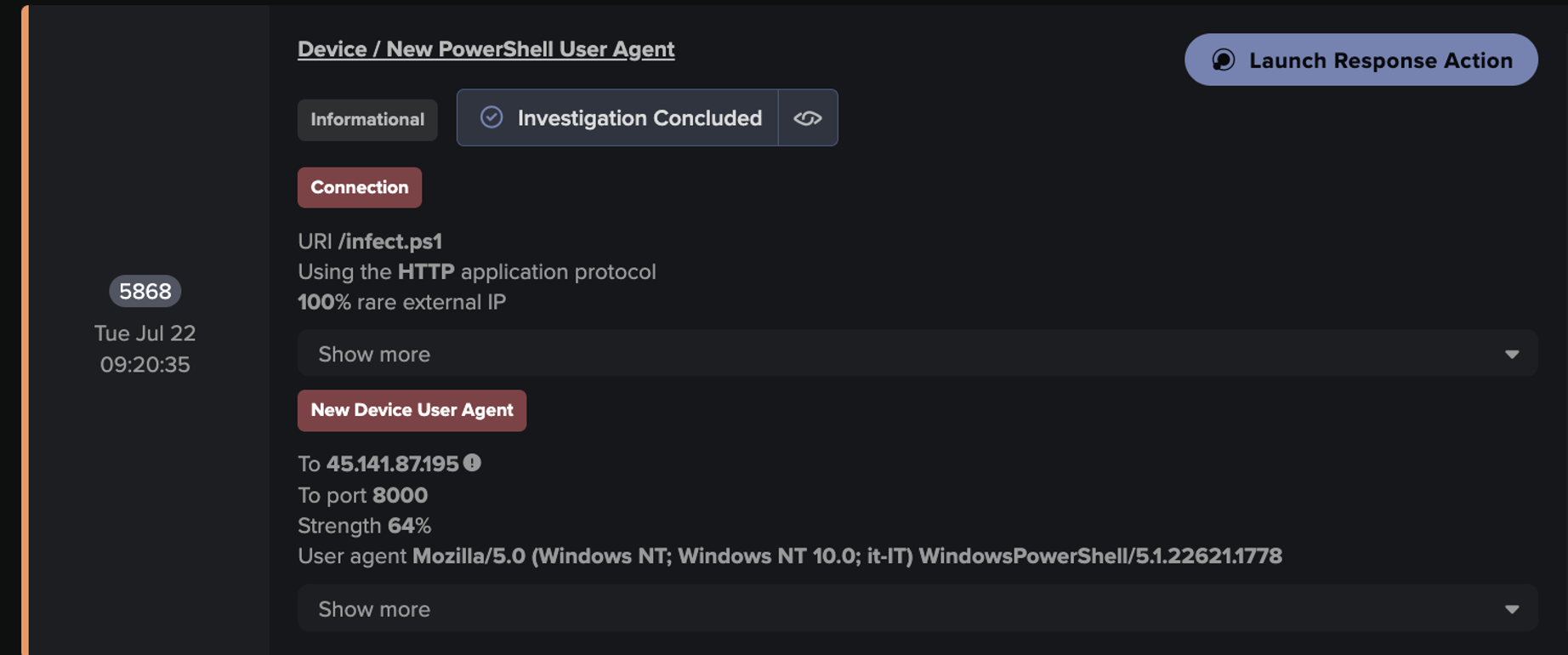
Darktrace detected and autonomously contained a PowerShell-based cryptojacking campaign that downloaded an AutoIt loader which injected the NBMiner payload into a legitimate process to mine Monero. Key artifacts include the malicious script 45.141.87[.]195:8000/infect.ps1, NBMiner retrieved from api[.]chimera-hosting[.]zip, and connections to monerooceans[.]stream / 152.53.121[.]6; #NBMiner #monerooceans.stream
Since March 2025, attackers have increasingly abused trojanized ConnectWise ScreenConnect ClickOnce installers to gain initial access to mainly U.S.-based organizations and rapidly deploy multiple RATs, including AsyncRAT, a custom PowerShell RAT, and later PureHVNC. The campaigns use evasive installers that fetch components at runtime, reuse preconfigured Windows Server 2022 VMs, and distribute malicious installers via social engineering with filenames impersonating official documents. #ScreenConnect #AsyncRAT #PureHVNC

Multiple Russia-linked influence operations (Operation Overload, Operation Undercut, Foundation to Battle Injustice, Portal Kombat/Pravda MD, MD24, and Ilan Shor–linked Evrazia) are actively pushing anti‑Sandu, anti‑PAS, and anti‑EU narratives ahead of Moldova’s September 28, 2025 parliamentary elections to undermine public trust and discourage pro‑European voting. Insikt Group assesses these IOs have limited evidence of electoral impact so far but pose significant risks to media integrity, diaspora turnout, and information ecosystems via impersonation, deepfakes, inauthentic networks, and coordinated amplification. #OperationOverload #OperationUndercut #PravdaMD
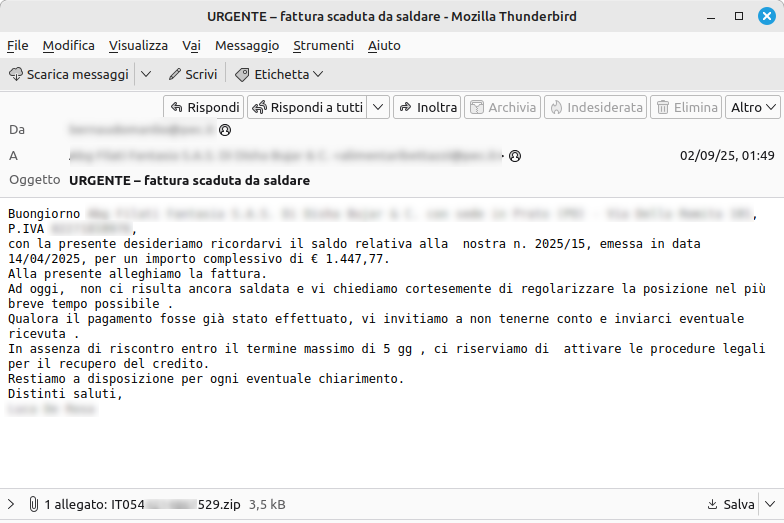
After a summer pause, a new MintsLoader campaign was observed using PEC-compromised accounts to send invoice-themed emails with ZIP attachments containing obfuscated JavaScript that launches an infection chain. Targets are Windows 10+ systems where cURL is abused to retrieve and install information-stealing malware; IoCs and mitigations were distributed via CERT-AGID feeds to PEC providers. #MintsLoader #CERT-AGID
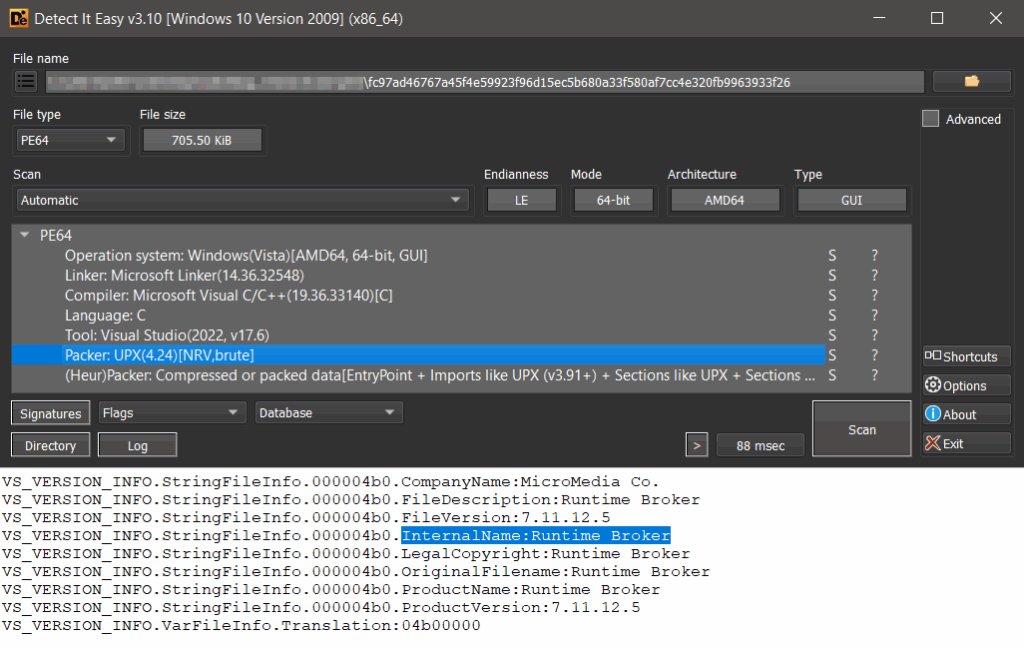
Check Point Research uncovered a Silver Fox APT campaign abusing a previously unknown Microsoft-signed vulnerable driver (amsdk.sys WatchDog Antimalware v1.0.600) to terminate protected processes and disable endpoint protections, enabling deployment of the ValleyRAT backdoor. Attackers used dual-driver loaders, flipped a single byte in the patched driver’s unauthenticated timestamp to preserve signature…

DireWolf is a newly emerged ransomware group (first seen May 2025) using double extortion and contacting victims via Tox, with at least 16 victims across multiple countries and industries. Their ransomware uses Curve25519 key exchange with ChaCha20 encryption, applies extensive anti-recovery/anti-analysis actions, and appends the .direwolf extension to encrypted files. #DireWolf…
ReversingLabs researchers discovered two npm packages (colortoolsv2 and mimelib2) that used Ethereum smart contracts to conceal C2 commands which downloaded second-stage malware, forming part of a larger supply-chain campaign that inflated GitHub popularity metrics to trick developers. The campaign employed fake GitHub accounts, automated commits, and replicated malicious packages across npm and GitHub to evade detection and distribute downloaders. #colortoolsv2 #mimelib2

A North Korean state-sponsored group identified as Kimsuky conducted a covert multi-stage campaign using Facebook, email, and Telegram to target defense and North Korea–related activists, delivering password-protected EGG archives containing obfuscated JSE scripts and VMProtect-packed DLLs that establish persistent RATs. The campaign used Korea-specific compressed formats, double Base64/encoded payloads, and Telegram-based C2 communications (woana.n-e[.]kr) to evade detection and maintain long-term access. #Kimsuky #AppleSeed #woana.n-e.kr