After a summer pause, a new MintsLoader campaign was observed using PEC-compromised accounts to send invoice-themed emails with ZIP attachments containing obfuscated JavaScript that launches an infection chain. Targets are Windows 10+ systems where cURL is abused to retrieve and install information-stealing malware; IoCs and mitigations were distributed via CERT-AGID feeds to PEC providers. #MintsLoader #CERT-AGID
Keypoints
- The MintsLoader campaign resumed after a summer break, first seen yesterday following the previous wave in June.
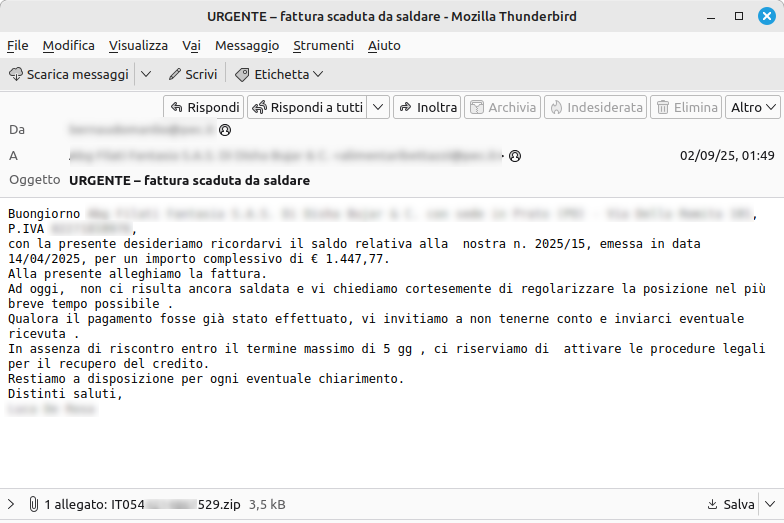
- Email template was slightly modified: a ZIP attachment replaced the prior “Invoice” hyperlink while keeping the same social-engineering theme.
- The ZIP contains an obfuscated JavaScript file that initiates the compromise chain on the victim host.
- Attackers abuse compromised PEC (certified email) accounts to send malicious messages, increasing credibility and delivery success.
- Primary targets are Windows systems (Windows 10 and later), where available cURL is used to fetch and deploy info-stealer malware.
- Countermeasures have been enacted with PEC providers and IoCs were shared via the CERT-AGID IoC feed to providers and accredited entities.
- Users are advised not to extract ZIP attachments from suspicious invoice emails and to forward suspected emails to [email protected].
MITRE Techniques
- [T1204] User Execution – Malicious ZIP attachment containing obfuscated JavaScript is delivered in an email to induce the user to open or extract the archive (“…the email now features a ZIP attachment; inside the compressed archive is an obfuscated JavaScript file that initiates the compromise chain.”).
- [T1566] Phishing – Use of credentialed PEC accounts and invoice-themed messages to socially engineer recipients (“…messages are sent from compromised PEC accounts to recipients’ PEC accounts, thereby exploiting the certified channel to increase the credibility and effectiveness of the attack.”).
- [T1105] Ingress Tool Transfer – Use of cURL on Windows hosts to download additional payloads and install info-stealer malware (“…the availability of the cURL command is exploited to initiate the infection chain and install malware, typically belonging to the info-stealer category.”).
Indicators of Compromise
- [Email/Accounts] Compromised PEC mailboxes – used as sender accounts to distribute invoice-themed malicious emails (specific addresses not listed in article).
- [File] Malicious attachment (ZIP) – contains an obfuscated JavaScript file that starts the compromise chain (example: “invoice.zip” containing “script.js” implied; full names not provided).
- [Hashes/IoC Feed] IoC feed distributed by CERT-AGID – IoCs made available via the CERT-AGID Feed IoC to PEC providers (link referenced as “Download IoC”).
Read more: https://cert-agid.gov.it/news/riprende-la-campagna-mintsloader/