Two Unit 42 interns, a Threat Research Intern and a Malware Reverse Engineering Intern, describe hands-on projects and mentorship that deepened their technical skills in threat intelligence, automation, and malware analysis. They highlight projects like automating data ingestion, building a fidelity scoring framework, creating dashboards, and developing tools to auto-identify malware…
Category: Threat Research

VShell is a Go-based, memory-resident Linux backdoor delivered via RAR archives that weaponize filenames to trigger Bash execution and load architecture-specific ELF payloads which decrypt and run in memory. Observed actors using VShell include UNC5174, Earth Lamia, CL-STA-0048, and UNC5221. #VShell #UNC5174

An LLM role-playing community was targeted with a backdoor disguised as an “AI Waifu” feature that provides arbitrary code execution and file access via a local agent listening on 127.0.0.1:9999 and 127.0.0.1:4444, enabling remote command execution, file exfiltration, and staged payload delivery. Publicly disclosed IoCs include SHA256 hashes, filenames, local HTTP endpoints, registry persistence key FakeUpdater, and hosting URLs linked to actors using aliases such as KazePsi/PsionicZephyr and Enclave0775. #AIWaifuRAT #PsionicZephyr
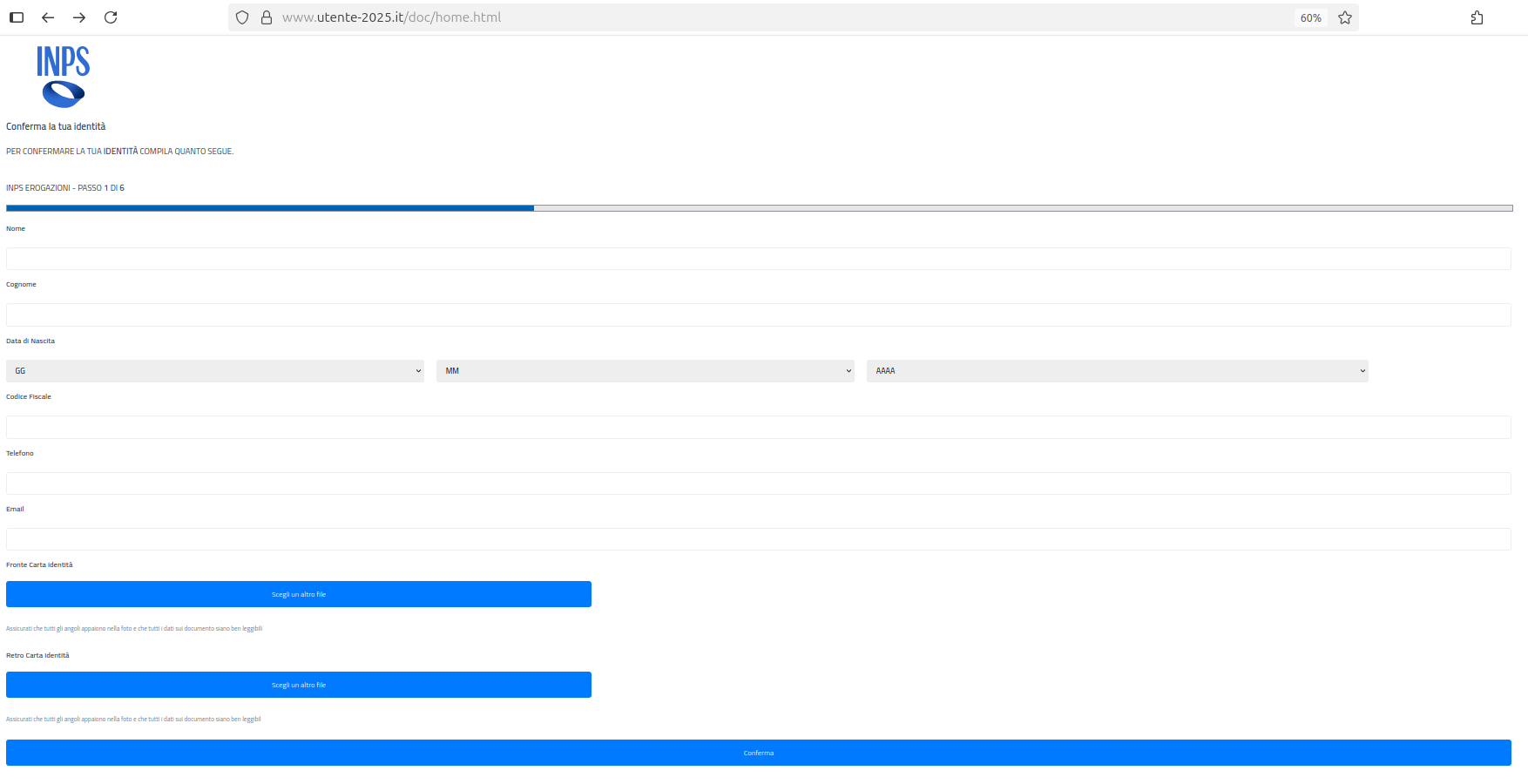
A phishing campaign impersonating INPS uses smishing SMS (sometimes followed by phishing emails) to direct victims to a fake website that harvests personal and financial documents, including ID cards, health cards, driving licenses, payslips, bank details, and selfies. Stolen data are used to create SPID accounts, hijack state disbursements by changing IBANs, resell documents on the dark web, and commit further financial fraud. #INPS #CERT-AGID

Elastic Security Labs diagnosed a Windows signature validation failure caused by an internal heuristic that flags certain byte-pattern “invalid markers” inside PE signature blocks, which in their case produced a false positive due to an EGGA marker collision. Re-signing with signtool.exe /rmc fixed validation, and the root cause was traced to imagehlp.dll’s ImageGetCertificateDataEx using IsBufferCleanOfInvalidMarkers and a hardcoded marker list (registry override at PECertInvalidMarkers). #ImageGetCertificateDataEx #PECertInvalidMarkers
Between 2010 and 2025 commercial surveillance vendors (CSVs) evolved from niche suppliers into a lucrative, consolidated ecosystem selling sophisticated spyware—often exploited for repression and human-rights abuses despite public exposures and sanctions. The report highlights repeated reuse of advanced exploits (including zero-click techniques) by state-linked actors and emphasizes detection, mitigation, and regulatory challenges. #Predator #Pegasus
Between August 8–18, 2025, a threat actor used compromised OAuth credentials in the Salesloft-Drift integration to exfiltrate large volumes of Salesforce data (Account, Contact, Case, Opportunity) and scanned that data for credentials. Salesloft revoked active Drift tokens and notified impacted customers while Palo Alto Networks Unit 42 urges urgent investigation, credential…
Attackers used a fake AnyDesk installer that leverages a Cloudflare Turnstile lure, the Windows search-ms protocol, and an SMB-hosted LNK disguised as a PDF to deliver an MSI that installs MetaStealer. The campaign collects victim hostnames via %COMPUTERNAME% subdomains and uses a Private EXE Protector-protected dropper (ls26.exe) connecting to multiple C2 domains and an IP. #MetaStealer #anydeesk[.]ink
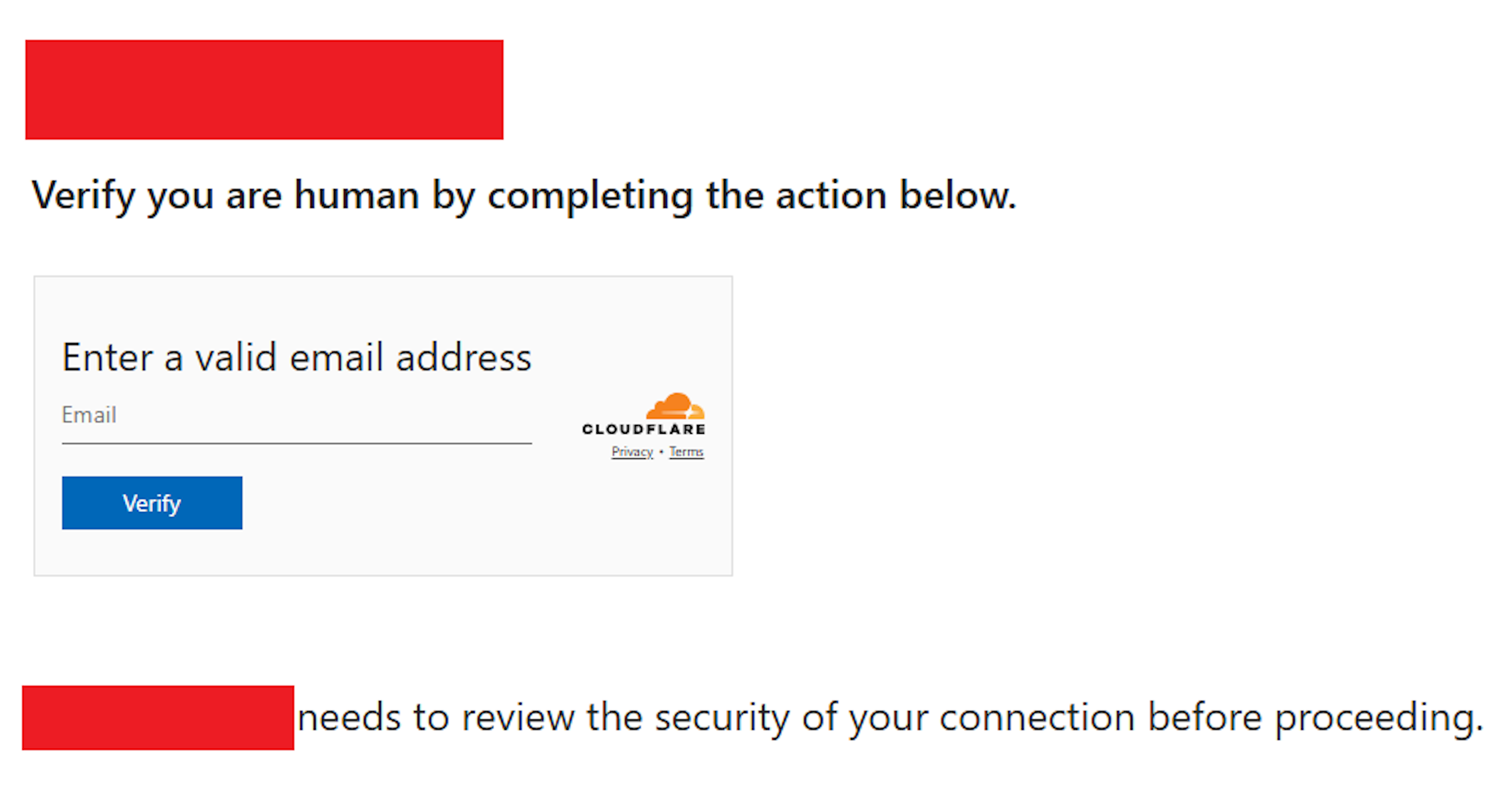
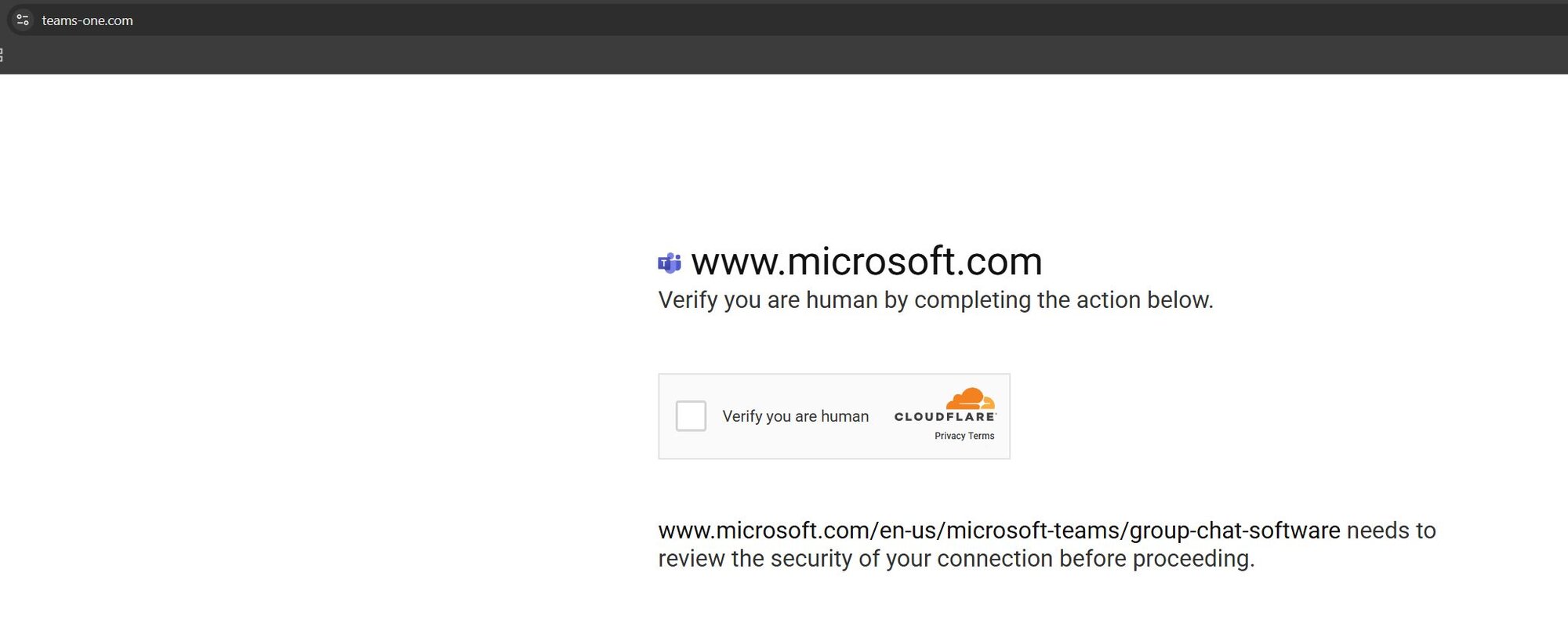
Amazon disrupted a watering hole campaign by APT29 that injected obfuscated JavaScript into legitimate websites to redirect a subset of visitors to actor-controlled domains mimicking Cloudflare verification pages and tricking users into authorizing attacker-controlled devices via Microsoft’s device code authentication flow. The actor used evasion tactics (randomized redirects, base64 encoding, cookies) and pivoted infrastructure after disruptions, with identified domains including findcloudflare[.]com and cloudflare[.]redirectpartners[.]com. #APT29 #findcloudflare[.]com
ESET researchers discovered PromptLock, the first known AI-powered ransomware proof-of-concept that uses a local gpt-oss-20b model via the Ollama API to generate and execute malicious Lua scripts for enumeration, exfiltration and encryption. The malware is written in Golang with both Windows and Linux samples uploaded to VirusTotal, highlighting how publicly available AI tools can automate and scale ransomware activities. #PromptLock #gpt-oss-20b

WhoisXML API launched a free MCP server that lets large language models query 17 WhoisXML APIs so users can retrieve internet infrastructure intelligence and run bulk or complex research via natural language. The server supports tools like Claude and Gemini and enables investigations such as historical WHOIS/DNS lookups and reverse lookups for IoCs. #WhoisXMLAPI #MCPServer

Mosyle discovered a new Mac malware strain named JSCoreRunner that spreads via a fake file-conversion site (fileripple[.]com) and evaded VirusTotal detections at discovery, using a two-stage installer to disable macOS quarantine and deliver a second unsigned payload. The malware hijacks Google Chrome search settings to redirect users to a fraudulent search engine, enabling keylogging, phishing, and potential data/financial theft. #JSCoreRunner #FileRipple #fileripple

Threat actors are increasingly abusing Microsoft Teams to socially engineer targets into installing remote access tools (QuickAssist, AnyDesk) and executing a PowerShell-based multi-stage payload that performs credential theft, persistence, and encrypted C2 communication. Campaigns have delivered DarkGate and Matanbuchus loader variants, reused static AES parameters linked to EncryptHub/LARVA-208 (Water Gamayun), and hosted payloads at domains such as audiorealteak.com and cjhsbam.com. #DarkGate #Matanbuchus

Cybercriminals are exploiting Formula 1’s expanding digital ecosystem with sophisticated attacks including deepfake CEO impersonations, malicious mobile apps, hospitality fraud rings, NFT/crypto scams, telemetry data interception, and supply-chain compromises ahead of the Dutch Grand Prix. Protective measures recommended include deepfake detection, external digital risk monitoring, strict vendor vetting, and fan guidance to only use verified sellers and official apps. #CloudSEK #Ferrari
Researchers chained a pre-auth HTML cache poisoning vulnerability in Sitecore Experience Platform with a post-auth insecure deserialization flaw to achieve full compromise of a patched instance. They also showed how exposing the ItemService API (or leveraging search behavior) lets attackers enumerate cache keys and reliably exploit the cache poisoning to inject…
