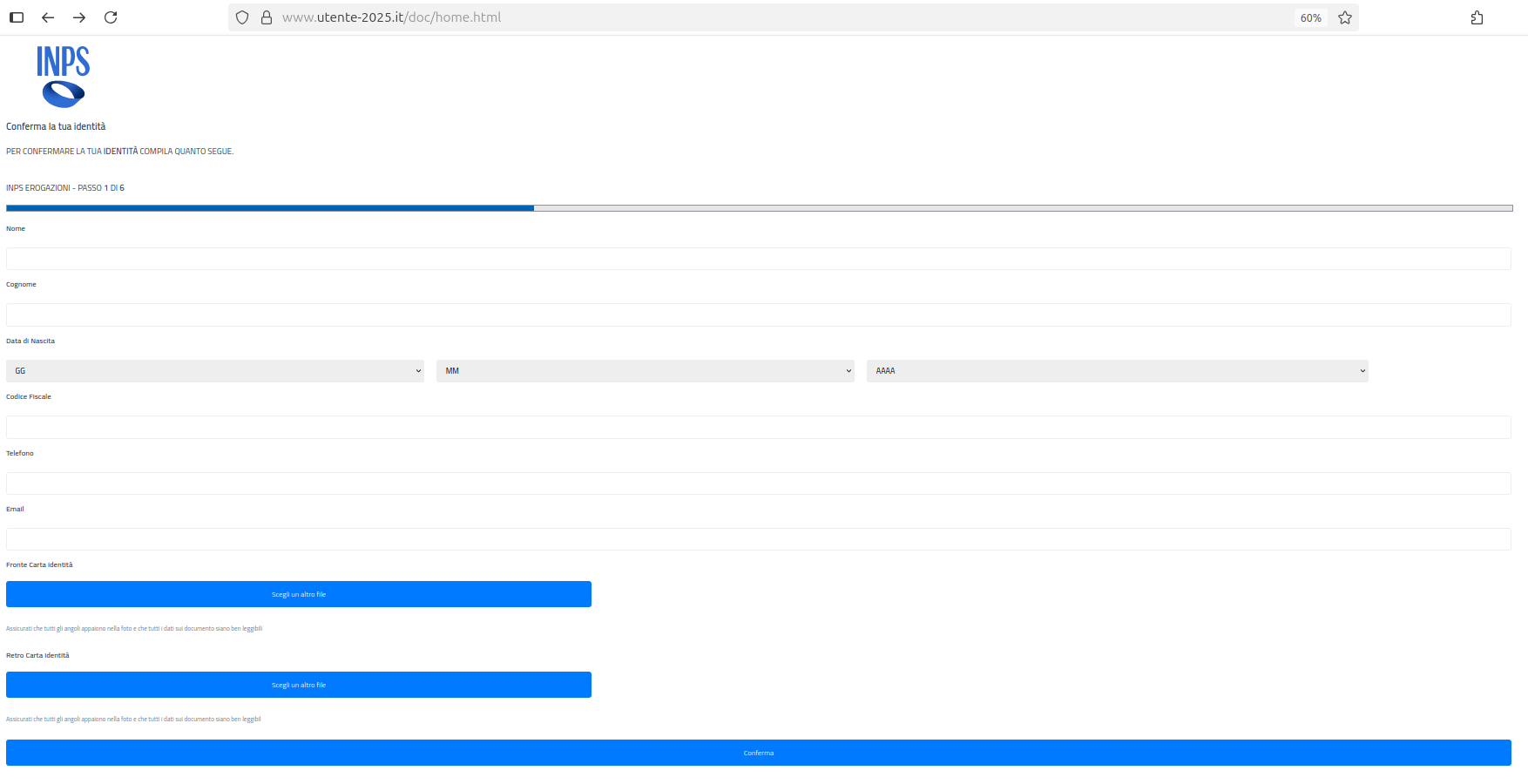
A phishing campaign impersonating INPS uses smishing SMS (sometimes followed by phishing emails) to direct victims to a fake website that harvests personal and financial documents, including ID cards, health cards, driving licenses, payslips, bank details, and selfies. Stolen data are used to create SPID accounts, hijack state disbursements by changing IBANs, resell documents on the dark web, and commit further financial fraud. #INPS #CERT-AGID
Keypoints
- The campaign resumed after about a month-long pause, using INPS branding and logo to deceive users toward a counterfeit portal.
- Delivery method: smishing via fraudulent SMS links, sometimes followed by phishing emails urging victims to “update” personal information to receive state payments.
- The fake site requests extensive sensitive documents: ID card (front/back), health card (front/back), driver’s license (front/back), last three payslips, IBAN, and a selfie with an ID.
- Stolen data are used to create SPID identities in victims’ names and to change IBANs to divert pensions, salaries, and other state disbursements to attacker-controlled accounts.
- Collected documents may be sold on the dark web, used to build synthetic identities, or leveraged for additional financial fraud.
- CERT-AGID and INPS monitored the campaign; CERT-AGID coordinated takedown actions and removed the malicious domain; IoCs were shared with accredited organizations.
- Advice: verify message origin, check the browser URL matches the official domain, and report suspicious messages to [email protected]; CERT-AGID published a guide on recognizing and responding to these scams.
MITRE Techniques
- [T1566] Phishing – Fraudulent SMS and emails were used to lure victims to a fake INPS portal: ‘SMS … invitano le potenziali vittime a seguire un link per aggiornare le proprie informazioni personali’ (‘SMS … invite potential victims to follow a link to update their personal information’).
- [T1446] Steal or Forge Credentials – Attackers collect identity documents and selfies to create SPID accounts in victims’ names: ‘I dati sottratti vengono sfruttati … creazione di un’identità digitale SPID intestata alla vittima’ (‘Stolen data are used … to create a digital SPID identity in the victim’s name’).
- [T1005] Data from Local System / [T1530] Data from Information Repositories – Collection of documents and payslips uploaded by victims (IDs, health cards, licenses, payslips, IBANs): ‘il sito malevolo richiede … carta d’identità, tessera sanitaria, patente, ultime tre buste paga, selfie’ (‘the malicious site requests … ID card, health card, driving license, last three payslips, selfie’).
- [T1587] Compromise Infrastructure – Use of a malicious domain hosting the counterfeit INPS portal which was later removed by CERT-AGID: ‘Le attività di contrasto … hanno condotto alla dismissione del dominio malevolo’ (‘Countermeasures … led to the takedown of the malicious domain’).
- [T1609] Data Encrypted for Impact / [T1531] Account Access Removal or Manipulation – Modification of IBANs associated with state disbursements to redirect funds (financial account manipulation): ‘possono … effettuare operazioni illecite, come la modifica dell’IBAN associato alle erogazioni statali’ (‘they can … perform illicit operations, such as changing the IBAN associated with state disbursements’).
Indicators of Compromise
- [Domain] malicious impersonation site – the counterfeit INPS domain used in the campaign (domain removed by CERT-AGID); specific domain name not published, IoCs shared with accredited organizations.
- [Email address] reporting contact – users are instructed to forward suspicious messages to [email protected] for analysis and reporting.
- [File types] requested/uploaded documents – examples: ID card images (front/back), health card images (front/back), driver’s license images, payslip PDFs (last three), selfies with ID.
- [Other] banking account details (IBAN) – victims are asked to provide IBANs which are subsequently targeted for unauthorized modification and fund diversion.
Read more: https://cert-agid.gov.it/news/torna-lo-smishing-ai-danni-di-utenti-inps/